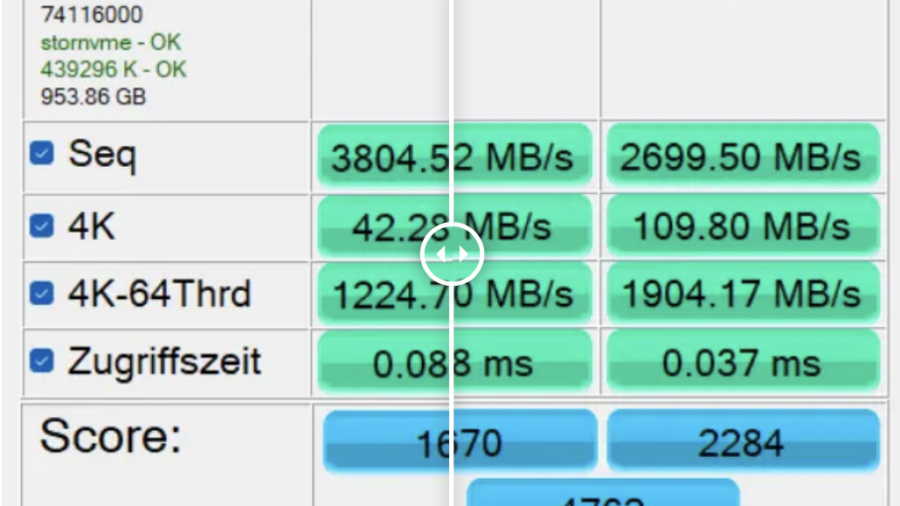
Microsoft has disabled a registry hack that enabled a hidden native NVMe driver in Windows 11 24H2/25H2. The tweak previously delivered major SSD performance gains but was likely blocked due to stability and compatibility concerns.
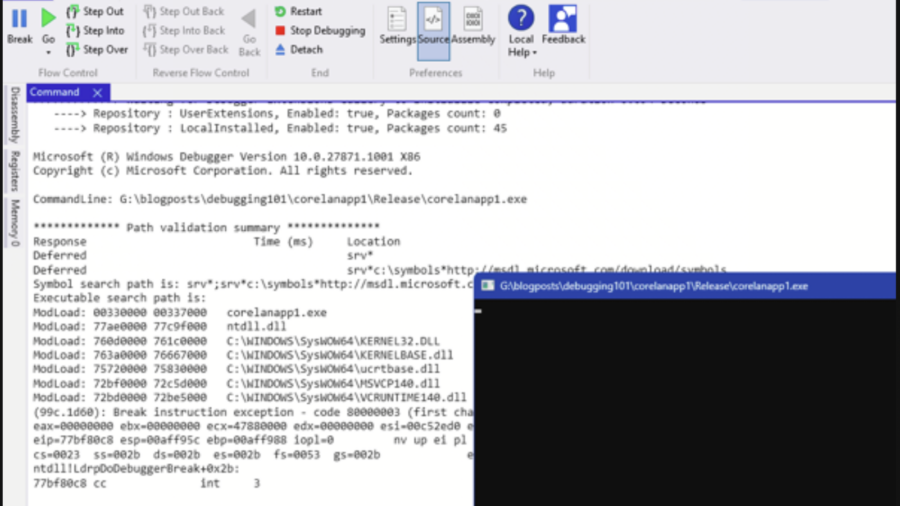
Debugging – WinDBG & WinDBGX Fundamentals
A beginner-friendly guide to debugging Windows programs using WinDbg and WinDbgX. It explains debugger basics, breakpoints, symbols, memory inspection, and execution control—key skills for reverse engineering and vulnerability research.
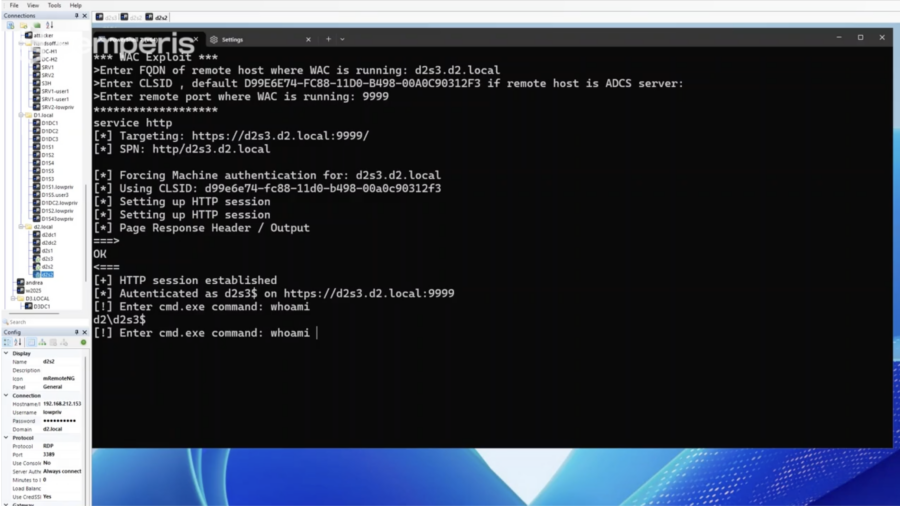
What You Need to Know: Windows Admin Center Remote Privilege Escalation (CVE-2026-26119)
CVE-2026-26119 is a high-severity privilege-escalation flaw in Windows Admin Center caused by improper authentication. Attackers with low-privileged access could gain admin rights and potentially compromise entire domains.
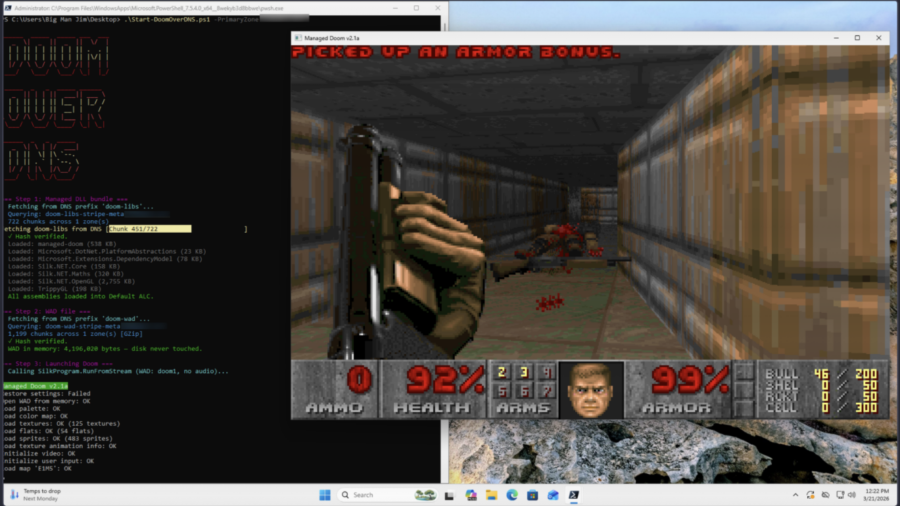
Can it Resolve DOOM? Game Engine in 2,000 DNS Records
The article shows a proof-of-concept where DOOM is stored across ~2,000 DNS TXT records and executed directly from memory. A PowerShell loader reconstructs the binary via DNS queries, illustrating how DNS can act as a covert payload delivery system.
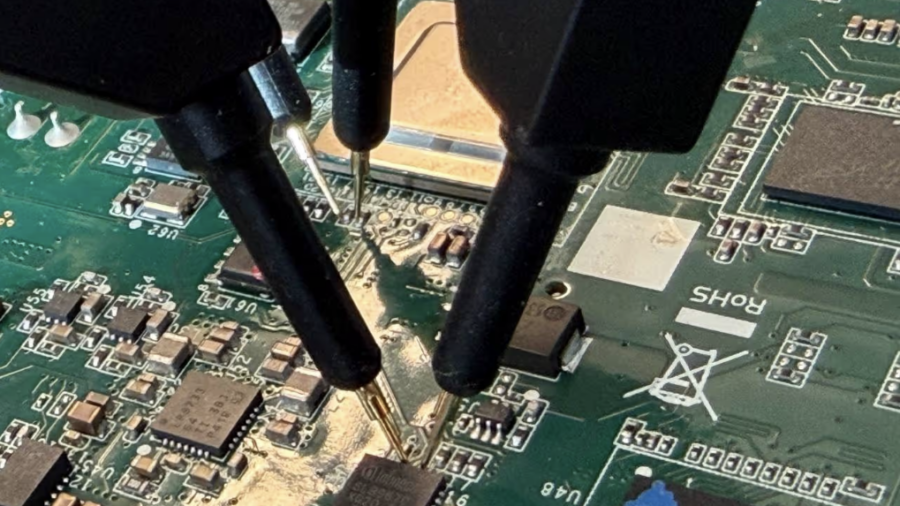
(CVE-2026-0714) TPM-sniffing LUKS Keys on an Embedded Device
Researchers discovered CVE-2026-0714 where a Moxa embedded device leaks its LUKS disk key in plaintext over the TPM SPI bus during boot. By sniffing TPM communication with a logic analyzer, attackers with physical access can recover the encryption key.
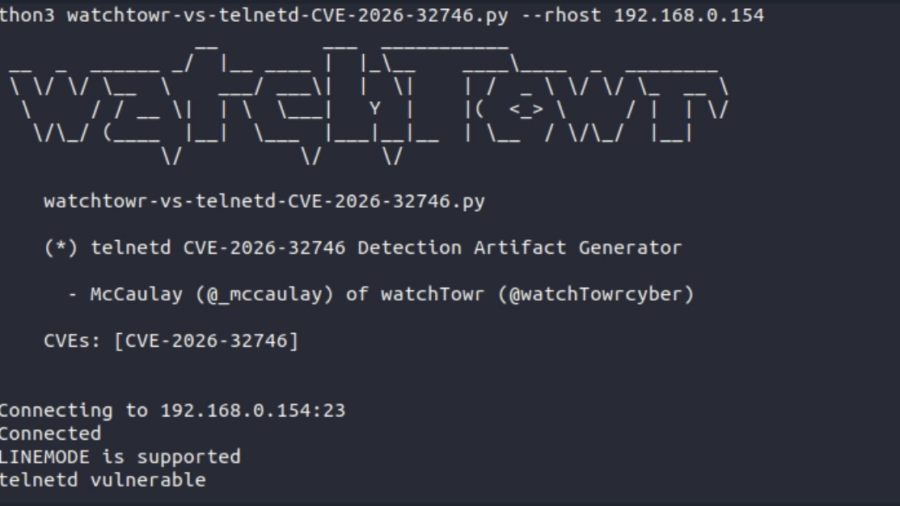
A 32-Year-Old Bug Walks Into A Telnet Server (GNU inetutils Telnetd CVE-2026-32746 Pre-Auth RCE)
The article analyzes CVE-2026-32746, a decades-old vulnerability in GNU Inetutils telnetd where a malformed LINEMODE SLC option triggers an out-of-bounds write, enabling unauthenticated remote exploitation.
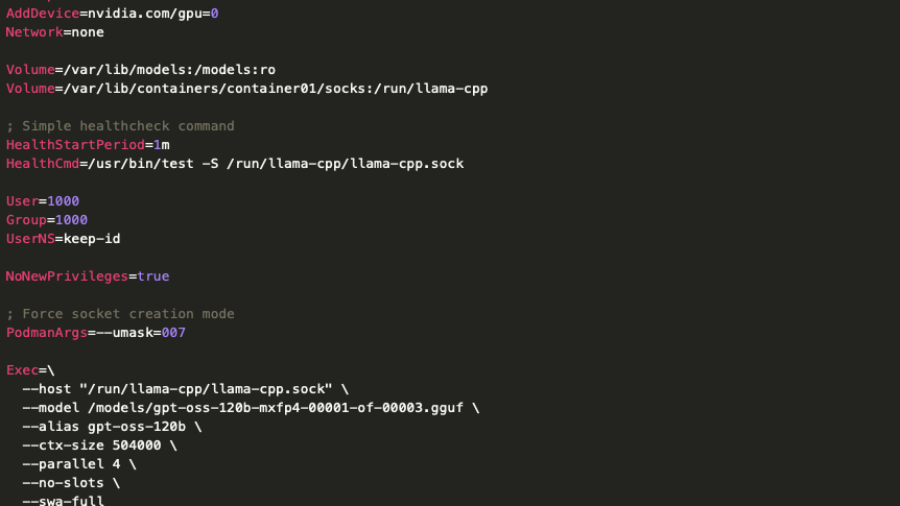
When Local AI Becomes an Attack Vector: A Deep Dive into LLM Infrastructure Security
The article analyzes a real deployment of a low-privileged on-prem LLM server and shows that even restricted models can expose internal systems through APIs, RAG pipelines, and data access, creating new enterprise attack surfaces.
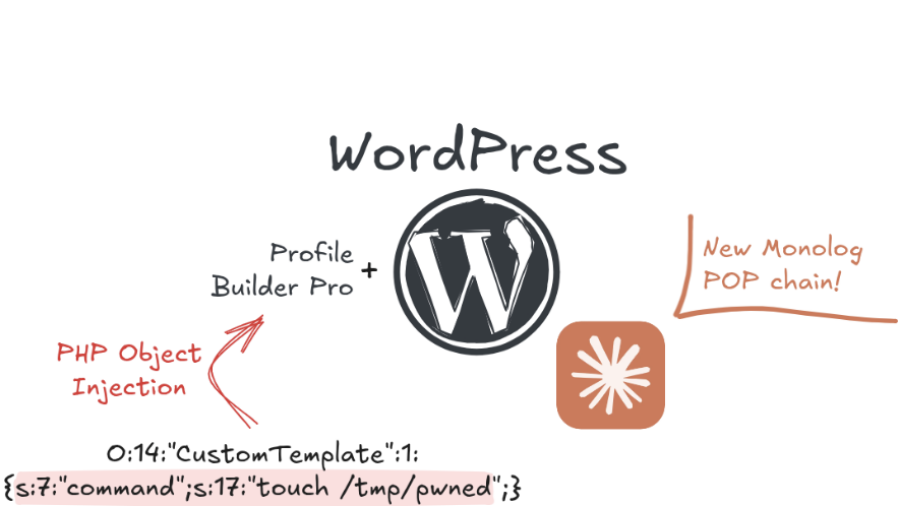
Exploiting a PHP Object Injection in Profile Builder Pro in the era of AI
The article explains how researchers exploited an unauthenticated PHP Object Injection in the WordPress plugin Profile Builder Pro, showing how AI tools can accelerate vulnerability discovery and exploit development in modern web applications.
TP-Link Tapo C200: Hardcoded Keys, Buffer Overflows and Privacy in the Era of AI Assisted Reverse Engineering
The article shows how AI-assisted reverse engineering of the TP-Link Tapo C200 firmware uncovered hardcoded keys, buffer overflows, and insecure APIs, demonstrating how IoT devices can expose users to remote compromise and privacy risks.
Booting into Trust: Reverse Engineering macOS Secure Boot Internals
The article analyzes the macOS secure boot chain on Apple Silicon, showing how Boot ROM, cryptographic verification, Secure Enclave, and staged bootloaders create a hardware-anchored chain-of-trust that protects the OS from power-on to kernel startup.