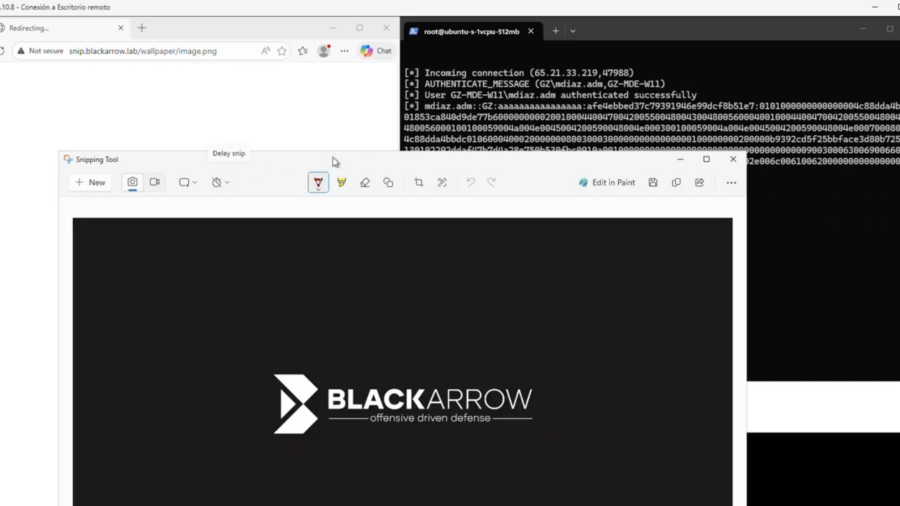
This vulnerability in the Windows Snipping Tool allows attackers to trigger NTLM authentication through the ms-screensketch protocol, forcing a connection to a remote SMB server and leaking the user’s Net-NTLM hash via a crafted link.
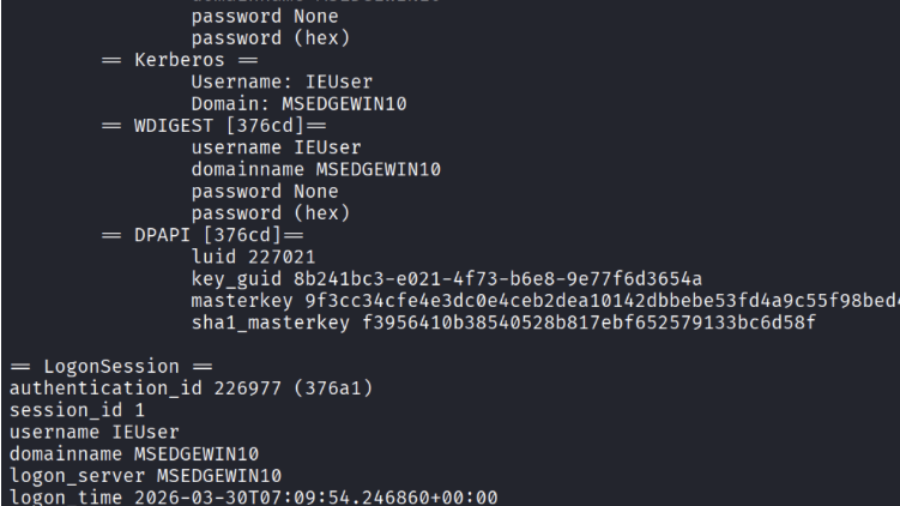
Credential Dumping from LSASS (Windows Authentication Secrets)
The article explains how attackers dump credentials from the Windows LSASS process using tools like Mimikatz and ProcDump, extracting password hashes and Kerberos tickets that enable privilege escalation and lateral movement.
From PCAP to Passwords: Automating Kerberos Roast Extraction
Krb5RoastParser is a Python tool that extracts Kerberos authentication hashes from PCAP traffic and converts them into Hashcat-compatible formats, simplifying Kerberoasting and Kerberos password-cracking workflows.
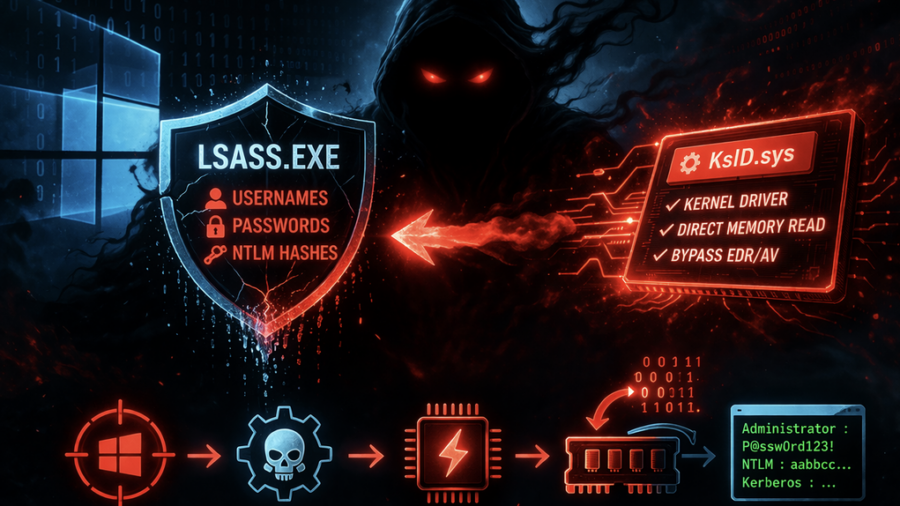
Ghost in LSASS: Inside the KslKatz Credential Dumping Framework
KslKatz is a Windows credential-dumping tool that reads LSASS memory using a kernel driver to bypass user-mode protections. It merges techniques from KslDump and GhostKatz to extract authentication secrets with improved stealth.
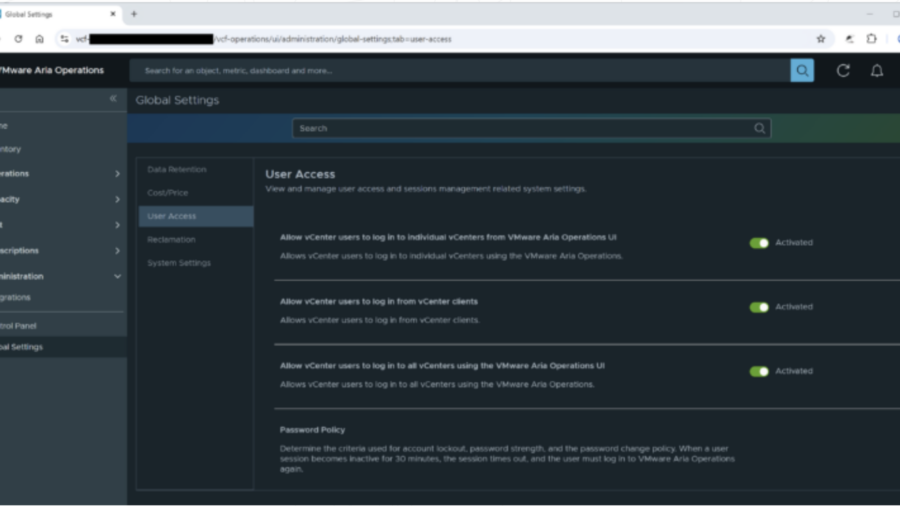
Vulnerabilities in Broadcom VMware Aria Operations: Privilege Escalation (CVE-2025-41245 / CVE-2026-22721)
The article examines vulnerabilities in VMware Aria Operations that enable credential disclosure and privilege escalation. Attackers with limited access can escalate privileges and gain administrative control over the infrastructure monitoring platform.
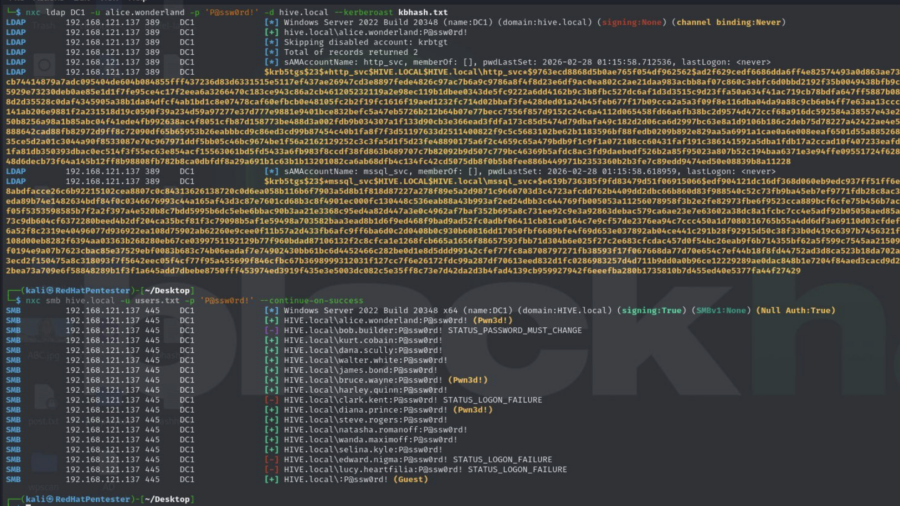
Active Directory Security Assessment: Password Spraying, Privilege Escalation, and Kerberoasting
This article analyzes an Active Directory attack chain where password spraying reveals valid credentials, privileged accounts enable escalation, and Kerberoasting exposes service account hashes, demonstrating how weak credential management can lead to full domain compromise.