A bug in macOS’s TCP stack causes networking to fail after about 49.7 days of uptime. A 32-bit timer overflow freezes the TCP clock, preventing cleanup of closed connections and eventually exhausting ephemeral ports.
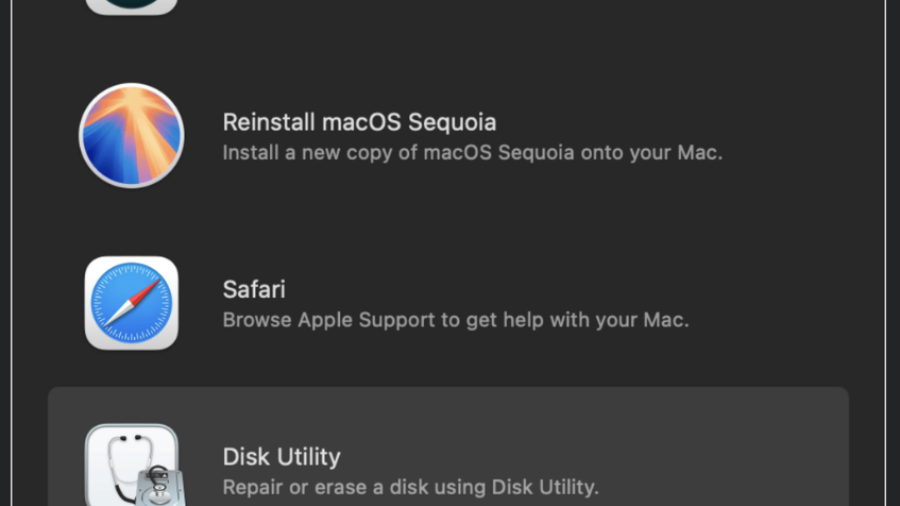
Recovery Mode Breakdown: Turning macOS Recovery Safari into Root Persistence
A macOS Recovery Mode Safari flaw allowed attackers to write arbitrary files to system partitions. By placing a malicious LaunchDaemon in /Library/LaunchDaemons, an attacker could achieve persistent root execution after reboot.
Booting into Trust: Reverse Engineering macOS Secure Boot Internals
The article analyzes the macOS secure boot chain on Apple Silicon, showing how Boot ROM, cryptographic verification, Secure Enclave, and staged bootloaders create a hardware-anchored chain-of-trust that protects the OS from power-on to kernel startup.
EDR Internals for macOS and Linux
The article examines how EDR agents monitor macOS and Linux systems by collecting telemetry from OS security frameworks, kernel interfaces, and tools like eBPF. Understanding these data sources reveals detection capabilities and potential blind spots.