A parsing flaw in BullFrog’s DNS-over-TCP handling allows attackers to bypass CI/CD egress filtering by pipelining DNS queries. The filter validates only the first query, letting malicious queries slip through.
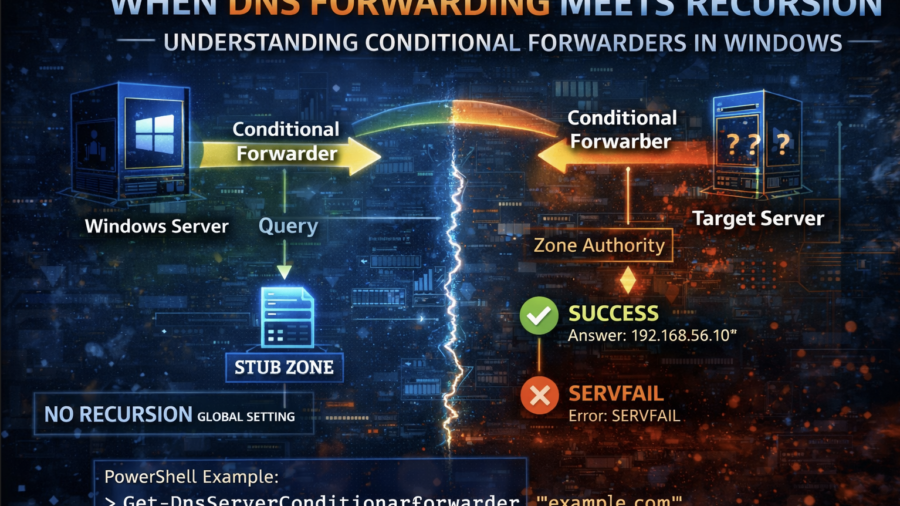
When DNS Forwarding Meets Recursion: Understanding Conditional Forwarders in Windows
The article explains how Windows DNS conditional forwarders interact with recursion. It shows that recursion settings can be overridden per zone and demonstrates how different DNS configurations affect query resolution.
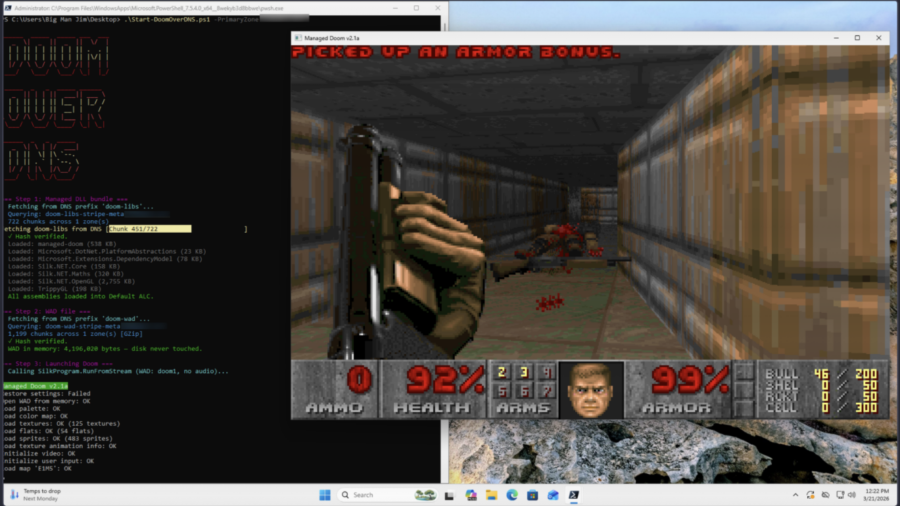
Can it Resolve DOOM? Game Engine in 2,000 DNS Records
The article shows a proof-of-concept where DOOM is stored across ~2,000 DNS TXT records and executed directly from memory. A PowerShell loader reconstructs the binary via DNS queries, illustrating how DNS can act as a covert payload delivery system.