The article introduces LOLExfil, a Living-Off-the-Land data exfiltration technique that abuses legitimate system tools and trusted services to stealthily extract data, blending malicious activity with normal system behavior.
Reverse Engineering the Tapo C260 and Tapo Discovery Protocol v2
The research reverse-engineers the TP-Link Tapo C260 camera firmware and analyzes Tapo Discovery Protocol v2. By dumping and decrypting the filesystem, the author reconstructs protocol logic and maps the device’s network attack surface.
Decrypting and Abusing Predefined BIOCs in Palo Alto Cortex XDR
Research shows how Palo Alto Cortex XDR predefined BIOC behavioral rules can be decrypted and analyzed. By understanding rule logic and built-in exceptions, attackers can adapt techniques to evade detection and bypass behavioral protections.
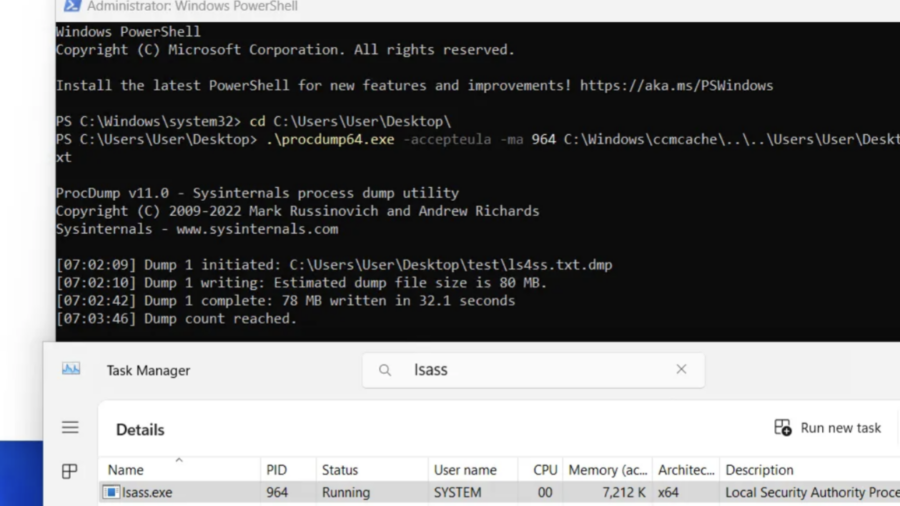
Ghost in the PPL – LSASS Memory Dump
The article explains a technique for dumping memory from the protected LSASS process (PPL). It analyzes limitations of PPL protection and demonstrates how MiniDumpWriteDump and existing process handles can be used to extract credential data.
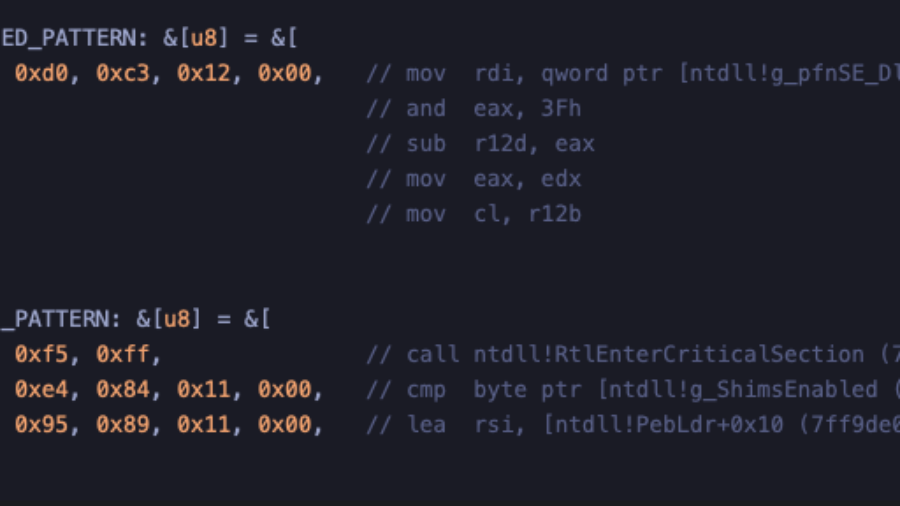
Crimes against NTDLL – Implementing Early Cascade Injection
How to implement Early Cascade Injection in Rust, a stealthy Windows process injection technique that hijacks shim engine callbacks in ntdll to execute shellcode during early process initialization, before many EDR hooks activate.
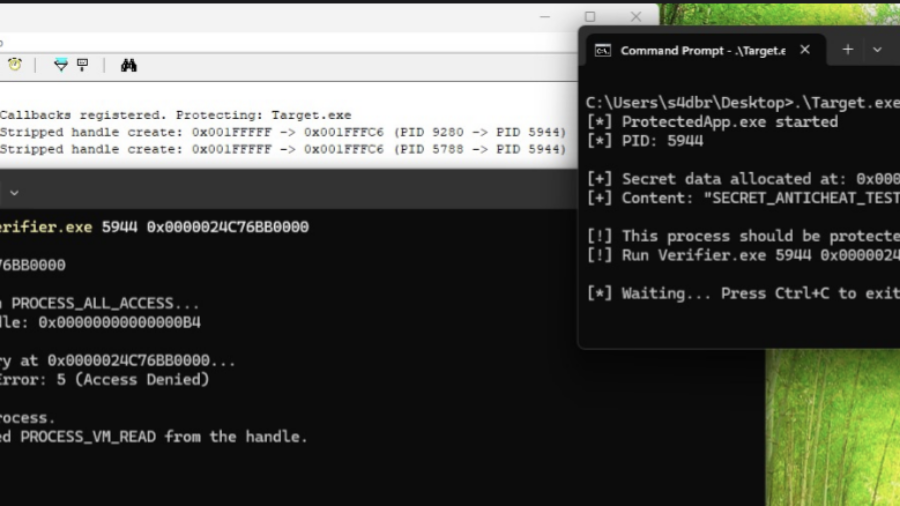
How Kernel Anti-Cheats Work: A Deep Dive into Modern Game Protection
The article explains how modern kernel-level anti-cheat systems work, describing their driver architecture, callbacks, memory monitoring, and detection methods used to identify cheats that operate at the same privilege level as the operating system kernel.
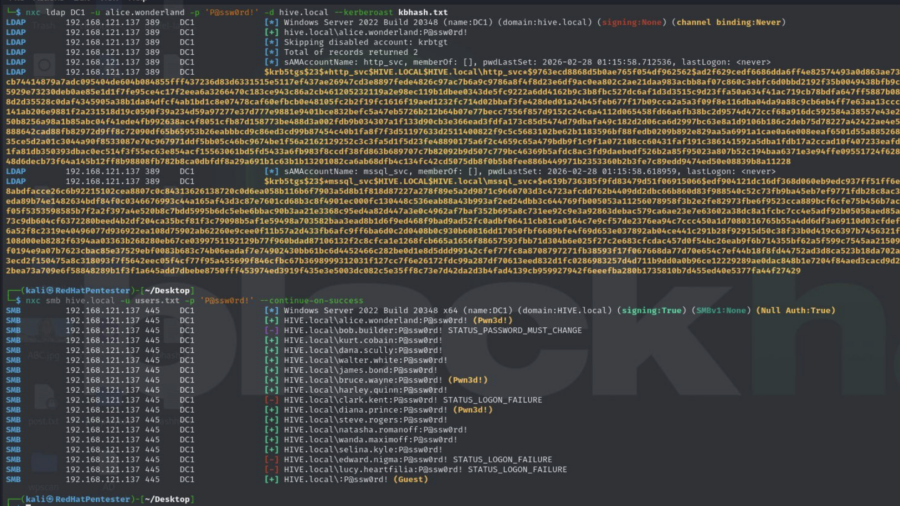
Active Directory Security Assessment: Password Spraying, Privilege Escalation, and Kerberoasting
This article analyzes an Active Directory attack chain where password spraying reveals valid credentials, privileged accounts enable escalation, and Kerberoasting exposes service account hashes, demonstrating how weak credential management can lead to full domain compromise.
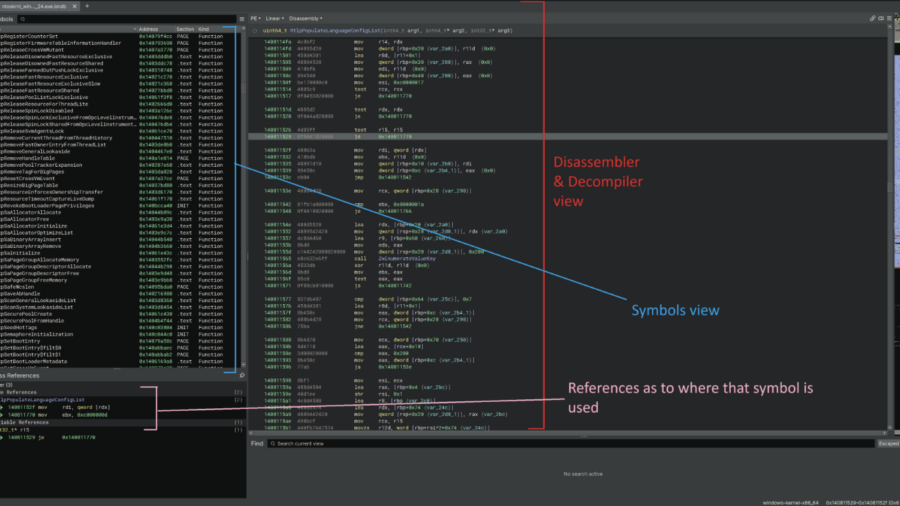
Reverse engineering undocumented Windows Kernel features to work with the EDR
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.
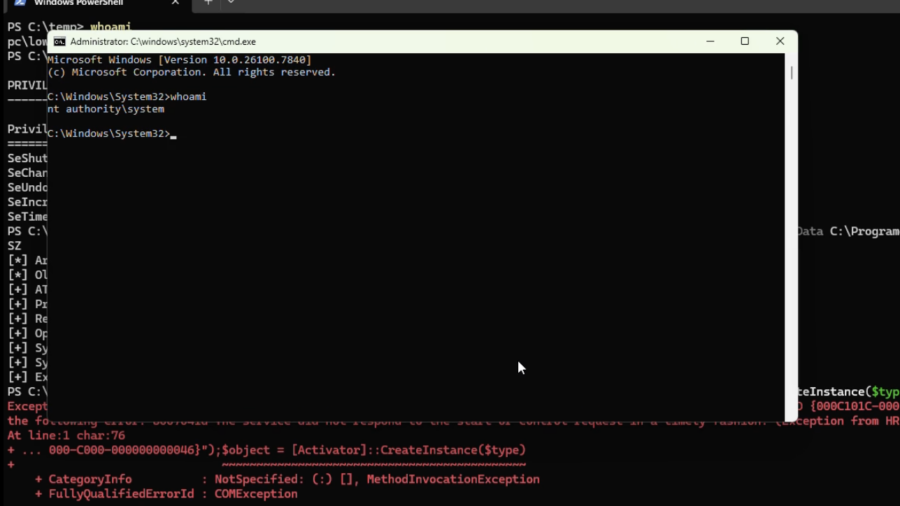
Silent Harvest: Extracting Windows Secrets Under the Radar
“Silent Harvest” explains how attackers can quietly extract sensitive Windows secrets such as credentials and security keys by abusing legitimate registry and system mechanisms, avoiding LSASS dumping and bypassing many common EDR detections.
RIP RegPwn: The Rise and Fall of a Windows Registry Exploitation Technique
The article explores a red-team research project called “RegPwn,” showing how weaknesses in Windows registry handling can be abused to achieve privilege escalation or persistence, and discusses why the technique has now been mitigated or rendered ineffective.