The article explains out-of-bounds vulnerabilities in Windows kernel drivers, showing how unchecked indexes, user-controlled offsets, and unsafe memory copies can cause kernel memory leaks, corruption, privilege escalation, or system crashes.
MAD Bugs: Claude Wrote a Full FreeBSD Remote Kernel RCE with Root Shell (CVE-2026-4747)
Researchers showed that the Claude AI model could generate a working exploit for a FreeBSD kernel vulnerability (CVE-2026-4747), producing a remote root shell by building a stack overflow and ROP chain with minimal human guidance.
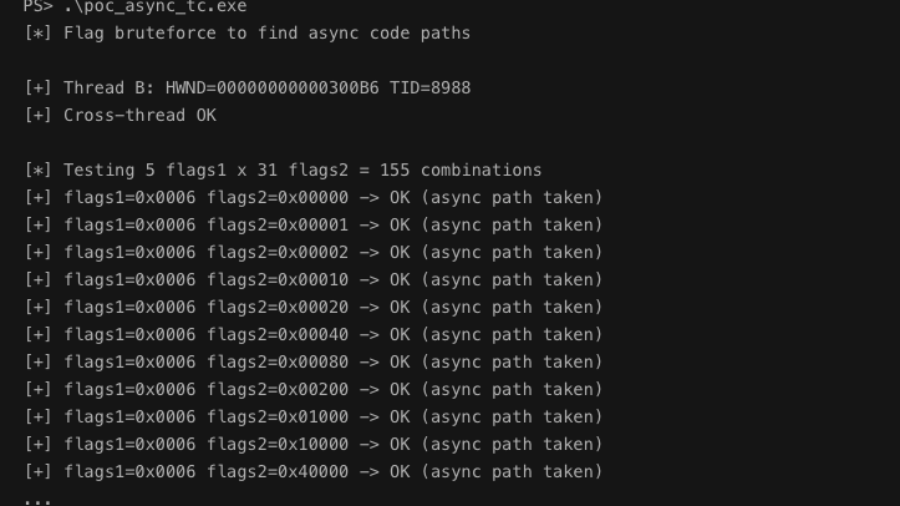
Async Windows Gone Wrong: Exploiting a Win32k Type Confusion Bug
The article analyzes a Win32k type confusion vulnerability in the async window action path of win32kfull.sys. Improper handling of window objects can corrupt kernel structures and potentially enable local privilege escalation.
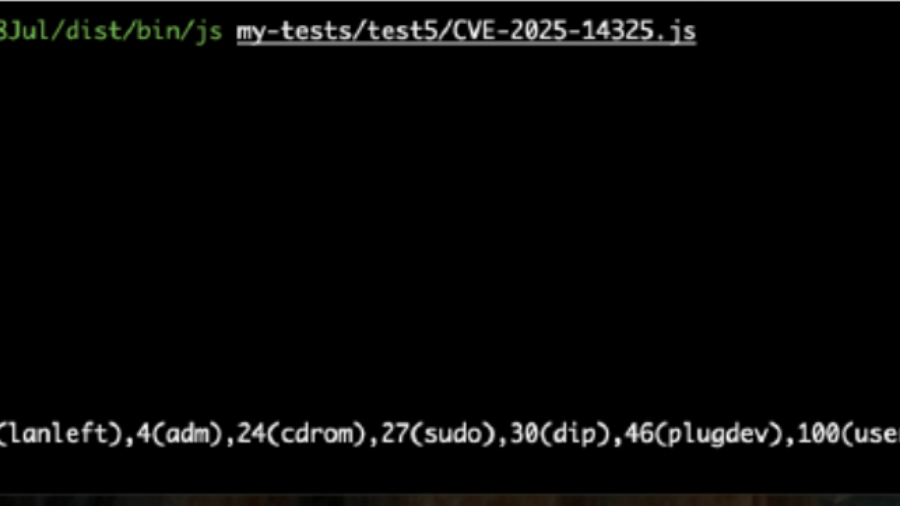
Breaking the JIT: Exploiting a SpiderMonkey Type Confusion Bug
The article analyzes CVE-2025-14325, a SpiderMonkey Baseline JIT bug causing type confusion in inline caches. Incorrect assumptions about object shapes can lead to memory corruption and possible code execution in Firefox.
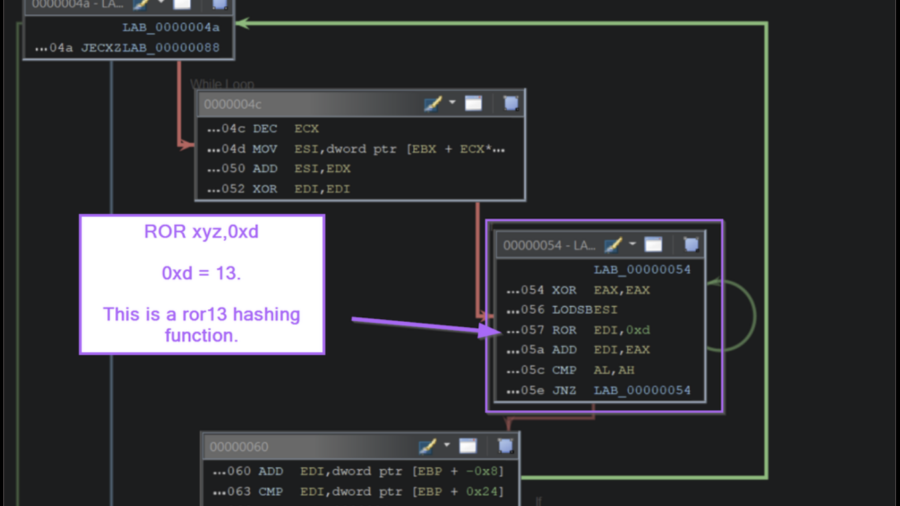
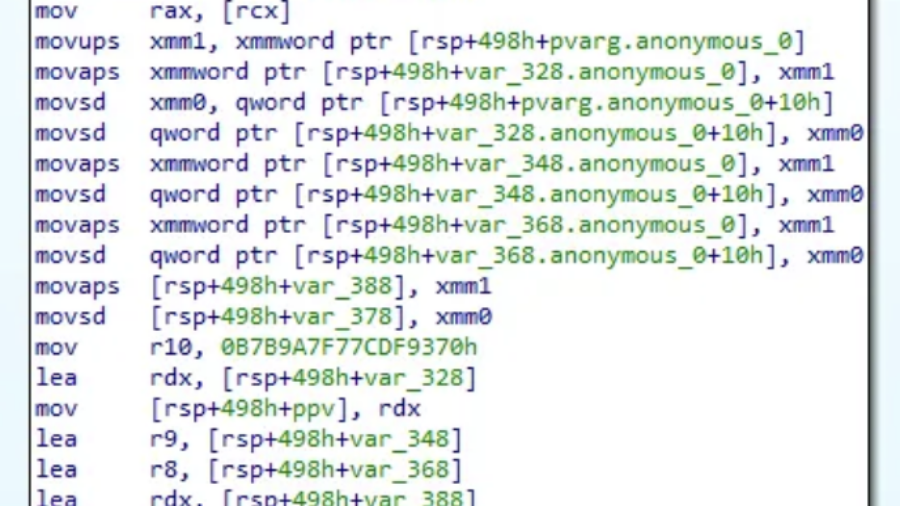
Inside the Payload: Manual Shellcode Analysis with Ghidra
The article demonstrates how to analyze Windows shellcode in Ghidra by identifying API-hashing routines, resolving hidden Windows API calls, and extracting C2 infrastructure without relying on automated emulation tools.
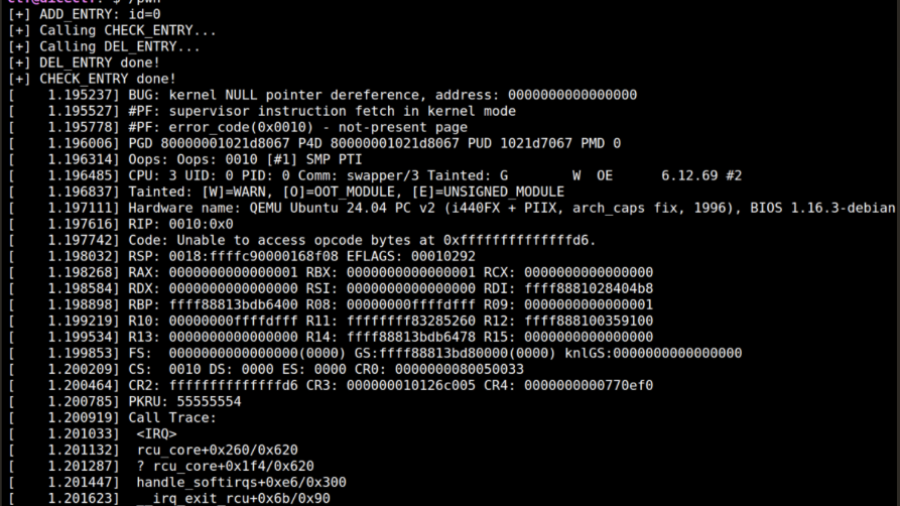
From RCU Double Free to Root: Exploiting a Linux Kernel Race in cornelslop
A DiceCTF write-up showing how an RCU double-free race in a Linux kernel module can be turned into a cross-cache exploit by manipulating SLUB allocator behavior and overlapping page-table entries.
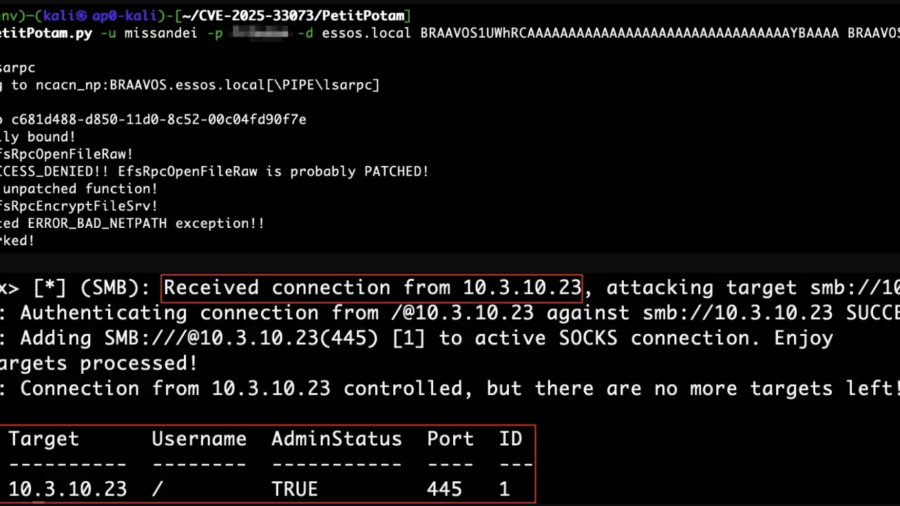
Reflecting on Your Tier Model: CVE-2025-33073 and the One-Hop Problem
CVE-2025-33073 enables NTLM reflection attacks that give attackers SYSTEM access on vulnerable Windows hosts. When combined with unconstrained delegation, a single compromised server can lead to full Active Directory domain compromise.
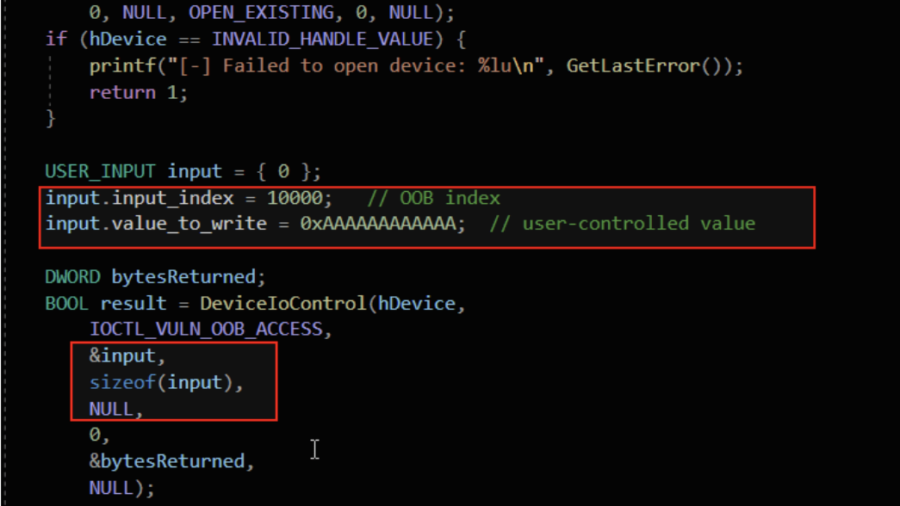
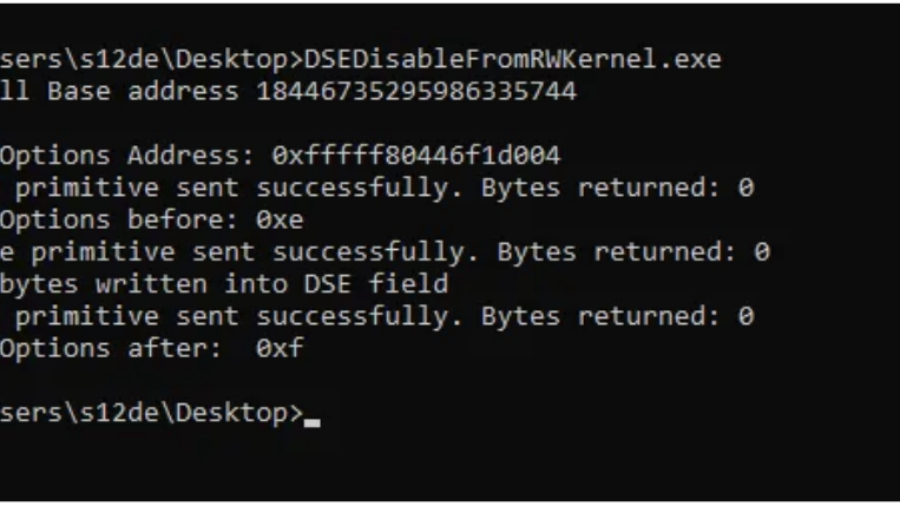
Bypassing Code Integrity Using BYOVD for Kernel R/W Primitives
The article shows how BYOVD techniques bypass Windows Code Integrity by loading a vulnerable signed driver and exploiting its IOCTL interface to gain arbitrary kernel read/write access and manipulate protected kernel memory.
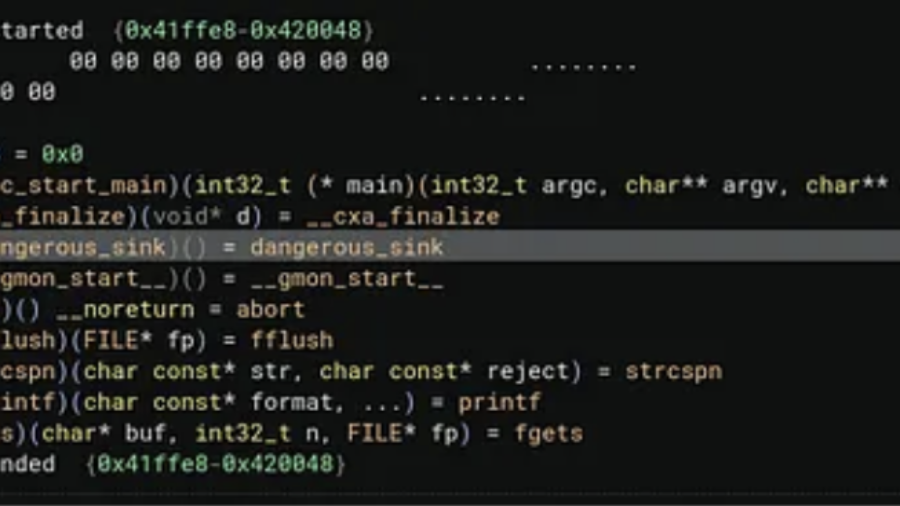
Hidden Bugs in Plain Sight: Hunting Vulnerabilities Inside Shared Libraries
The article explains how cross-binary analysis can uncover vulnerabilities hidden inside shared libraries. By tracing data flows from applications into library functions, researchers can detect security bugs often missed in traditional audits.
Inside WMI: Tracing Windows Management from Consumers to COM Providers
The article explains WMI internals, showing how Windows management queries travel from applications to the WMI service, repository, and provider hosts, and how COM/DCOM mechanisms execute underlying system operations.