Bloodied (but not broken) by the ordeal, I achieved my goals and stretch goals. And given that there are no public descriptions of how Realtek Bluetooth chips work, I look forward to sharing hitherto-unknown information about how to navigate and understand these mostly-16-bit-MIPS-code systems. And I’ll discuss how their ROM-“patch”ing firmware update mechanism works, how you can patch it to change its code too, and the security implications thereof.
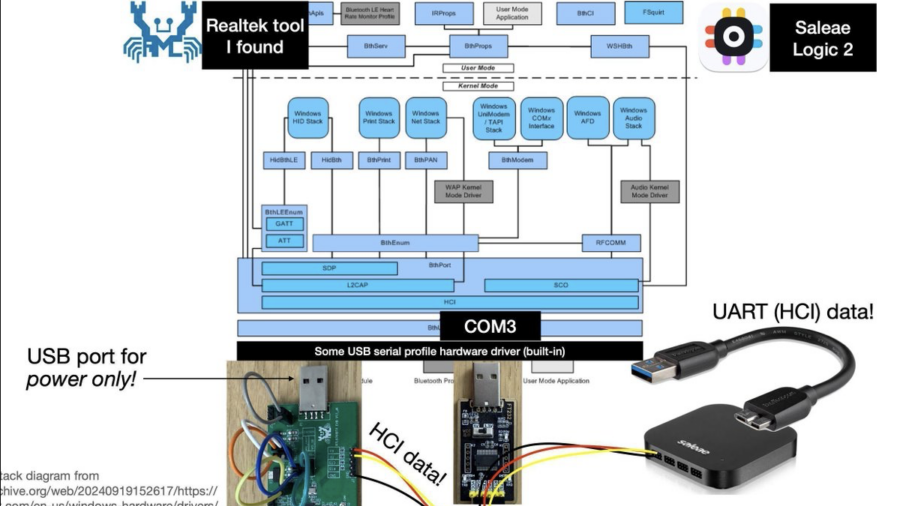
Hacking a Bluetooth Printer Server: GATT to UART Adapter?
Reverse engineering a Bluetooth printer server reveals multiple security flaws, including exposed debug interfaces and insecure GATT services, enabling unauthenticated remote code execution with root privileges via Bluetooth or network access.
Blinkenlights 2.0: Reverse Engineering a Smartwatch via Screen Signals
Reverse engineering a cheap smartwatch and reviving the classic “blinkenlights” attack to extract firmware through screen update patterns, revealing weaknesses in OTA update mechanisms, BLE communication, and embedded device security design.