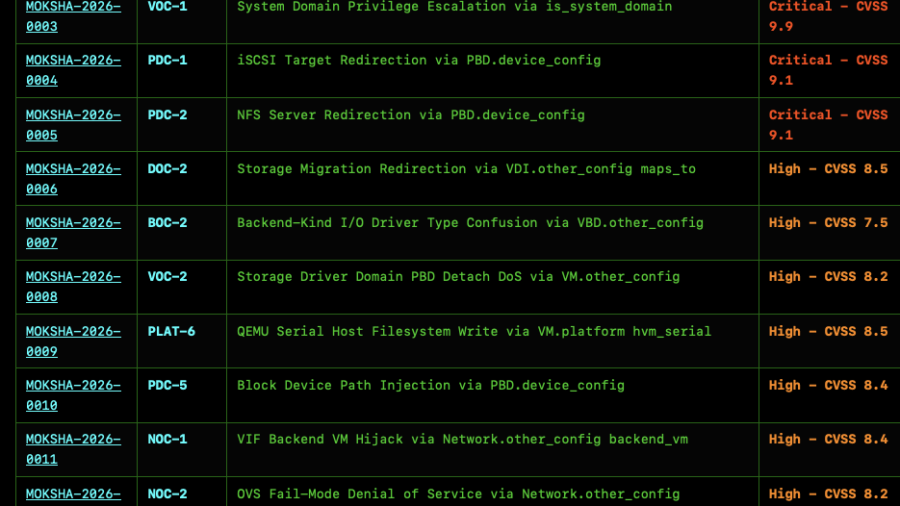
Shittrix discloses 89 XAPI/Citrix XenServer flaws caused by unvalidated metadata fields, enabling low-privileged users to mount host disks, inject storage commands, redirect storage, and compromise pools.
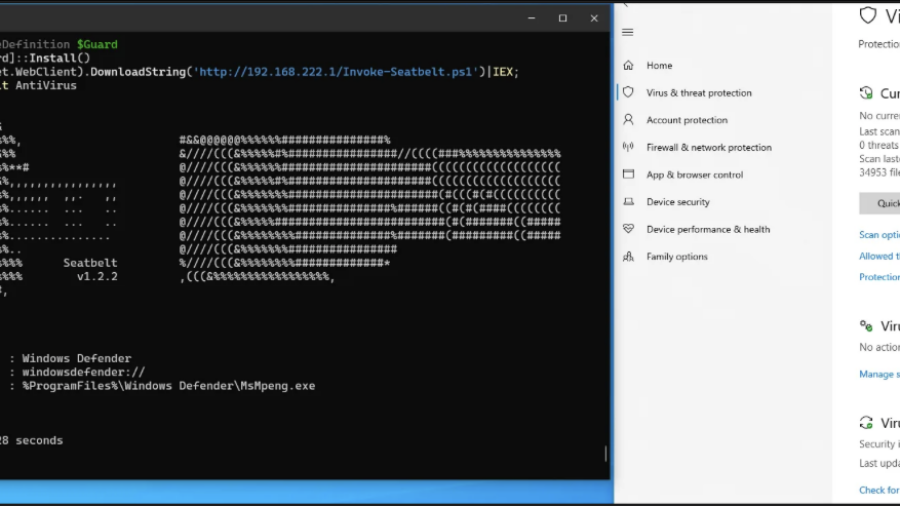
Patchless AMSI Bypass via Page Guard Exceptions
The article shows a patchless AMSI bypass using Page Guard exceptions and VEH to intercept AmsiScanBuffer, force an early clean return, and avoid direct code patching.
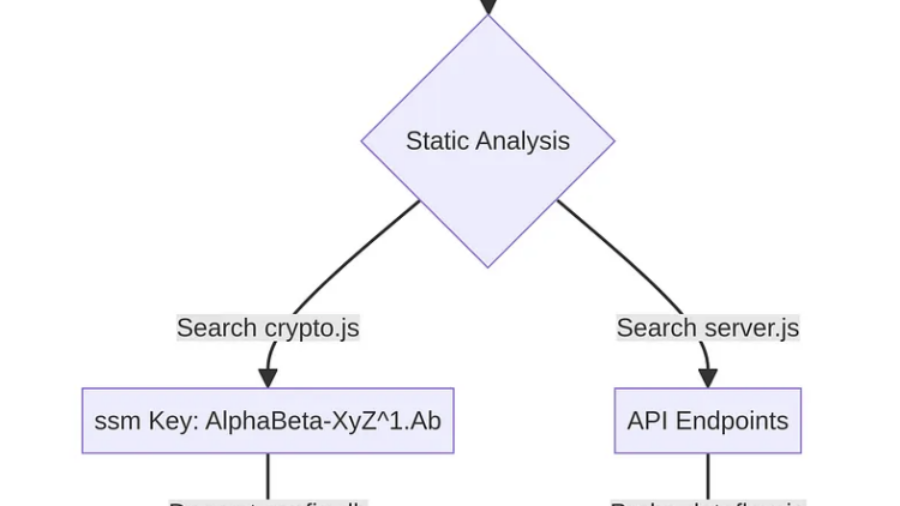
A Step-by-Step Guide to Uncovering Vulnerabilities in a Mobile App
The article shows how APK decompilation with Jadx exposed Cordova JavaScript code, hardcoded database keys, CryptoJS-derived secrets, backend endpoints, and a critical LFI flaw.
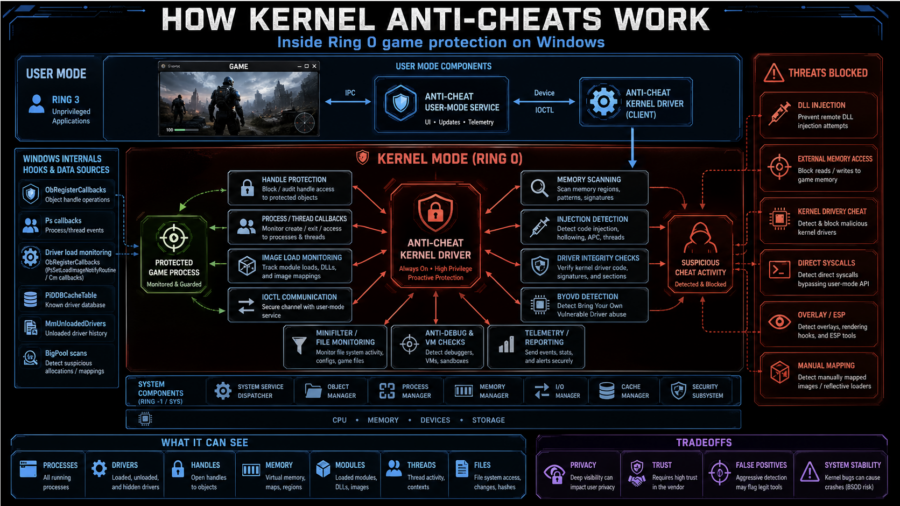
How Kernel Anti-Cheats Work: A Deep Dive into Modern Game Protection
The article explains how kernel anti-cheats monitor games from Ring 0 using callbacks, handle filtering, memory scans, driver checks, anti-debugging, VM detection, and hardware fingerprinting.
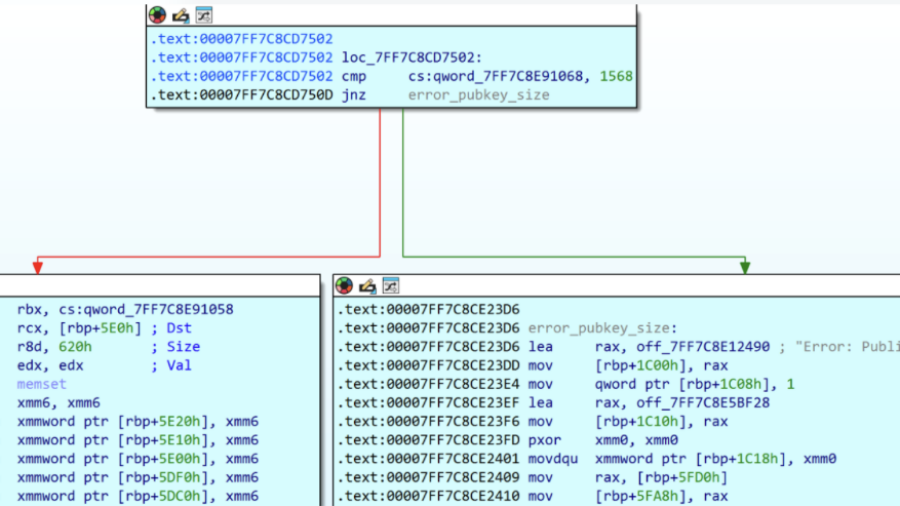
A Shortcut to Coercion: Incomplete Patch of APT28’s Zero-Day Leads to CVE-2026-32202
Akamai shows how Microsoft’s incomplete fix for an APT28 LNK exploit left CVE-2026-32202: a zero-click UNC path issue that coerces SMB/NTLM authentication via Explorer icon parsing.
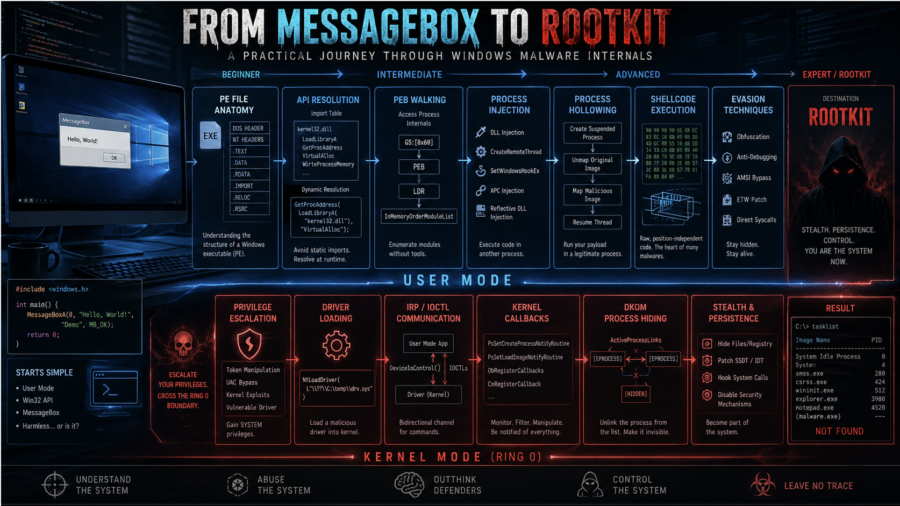
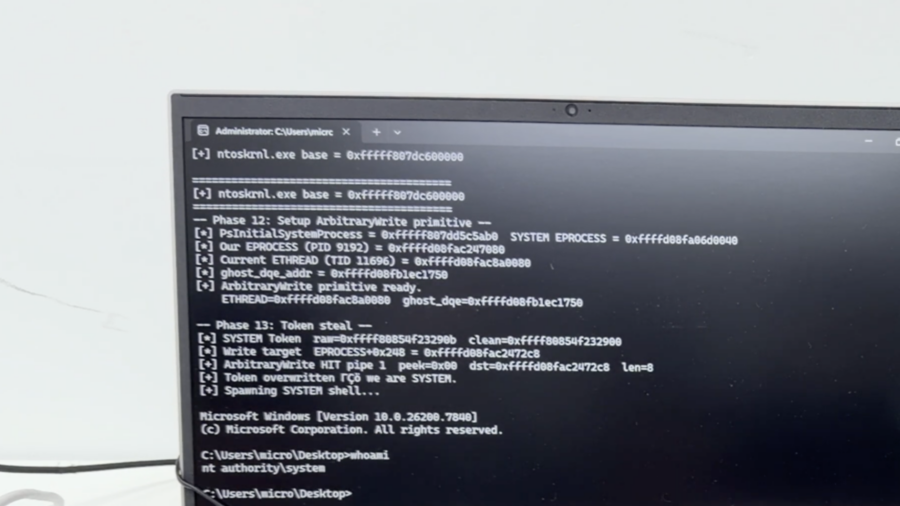
From MessageBox to Rootkit: A Practical Journey Through Windows Malware Internals
The article walks through Windows malware development from dynamic API resolution and PEB walking to injection, APC execution, driver basics, DKOM process hiding, and kernel callback abuse.
Plug me If you can : Exploiting USB Printer Drivers in Windows
ENKI analyzes CVE-2026-32223, a heap overflow in Windows usbprint.sys triggered by malformed USB printer descriptors, leading to SYSTEM privilege escalation via crafted USB device.
Kyber Ransomware Double Trouble: Windows and ESXi Attacks Explained
Rapid7 analyzes Kyber ransomware’s Windows and ESXi variants, showing coordinated attacks on VM infrastructure, file systems, backups, recovery tools, and cryptographic claims.
JWT, Part 13: XSS + JWT = Full Account Takeover
The article shows how XSS can steal or abuse JWTs from localStorage, sessionStorage, cookies, or memory, and recommends HttpOnly cookies, DPoP, BFF, rotation, and Token Sidejacking.
Secure Code Review: Finding XML vulnerabilities in Code
The article explains how to spot XXE risks during C++ secure code review by checking XML parser configuration, especially Xerces-C++ entity handling and DTD resolution settings.