Researchers showed that the Claude AI model could generate a working exploit for a FreeBSD kernel vulnerability (CVE-2026-4747), producing a remote root shell by building a stack overflow and ROP chain with minimal human guidance.
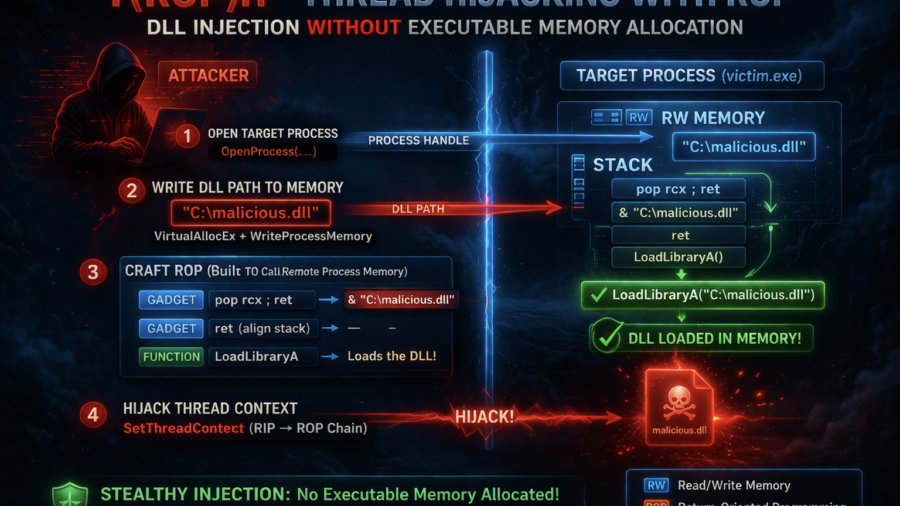
Stealth Injection with ROP: Thread Hijacking Without Executable Memory
The article presents T(ROP)H, a process injection technique that hijacks threads and uses a ROP chain to load a DLL without allocating executable memory, reducing common detection indicators used by EDR systems.
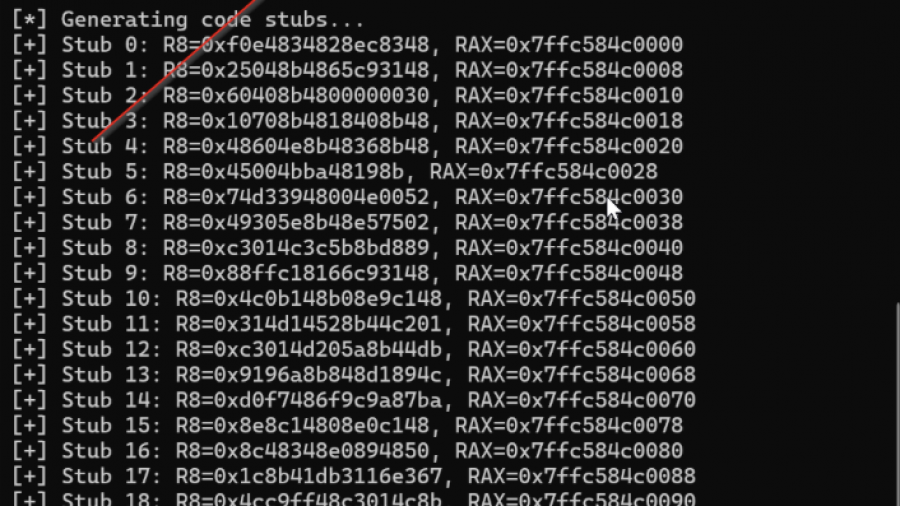
Defeating Windows DEP Using ROP Chains Leveraging VirtualAlloc
Uses manual Return-Oriented Programming (ROP) to chain existing code fragments and call VirtualAlloc, changing memory permissions to bypass Windows DEP and then execute shellcode in exploited process memory.
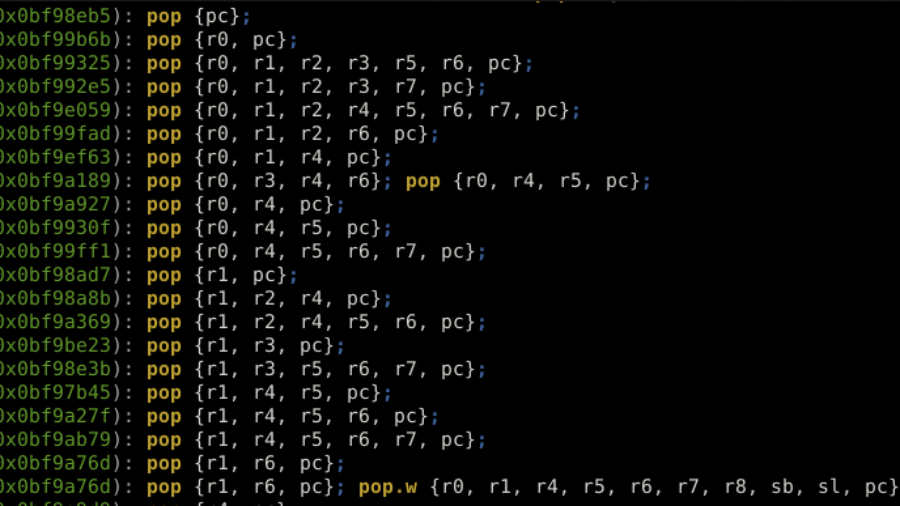
ROP the ROM: Exploiting a Stack Buffer Overflow on STM32H5 in Multiple Ways
Article details exploiting a stack buffer overflow on an STM32H5. It demonstrates basic shellcode injection, then bypassing a non-executable stack (XN/MPU) using Return-Oriented Programming (ROP) with gadgets from the chip’s ROM code to dump firmware, showcasing advanced embedded exploitation techniques.
Mastering Living off the Process in Offensive Security
No need for overusing WriteProcessMemory, VirtualAlloc, injecting a DLL, etc. This way, everything you need to manipulate the remote process is self-contained and already available to the process.