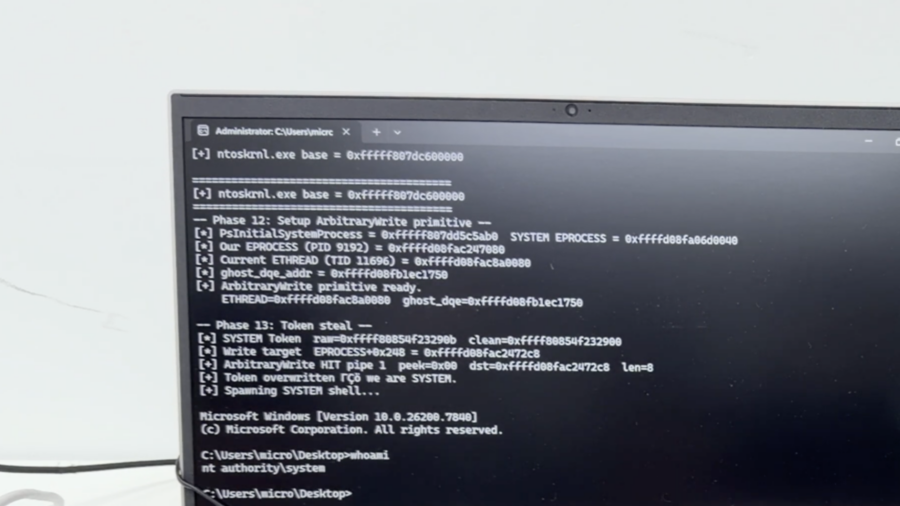
ENKI analyzes CVE-2026-32223, a heap overflow in Windows usbprint.sys triggered by malformed USB printer descriptors, leading to SYSTEM privilege escalation via crafted USB device.
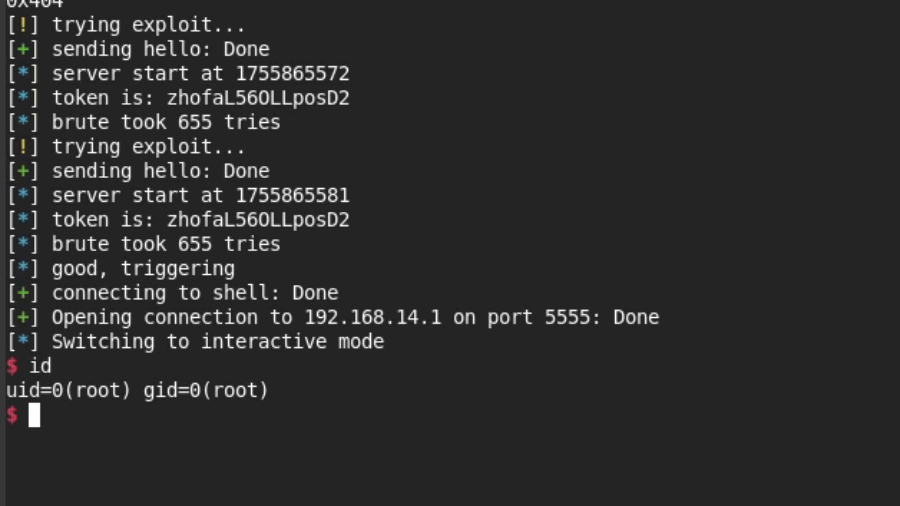
Now You See mi: Hacking the Xiaomi C400 Camera
Researchers exploited weaknesses in Xiaomi’s miIO protocol to bypass authentication, predict cryptographic values, and trigger memory corruption, ultimately achieving remote code execution and a cloud-independent jailbreak on a Xiaomi C400 camera.
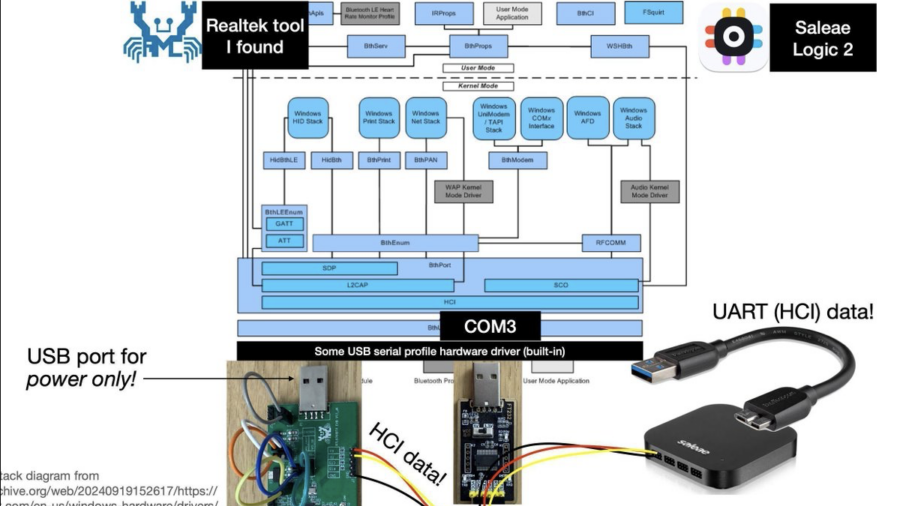
Reverse engineering Realtek RTL8761B* Bluetooth chips, to make better Bluetooth security tools & classes
Bloodied (but not broken) by the ordeal, I achieved my goals and stretch goals. And given that there are no public descriptions of how Realtek Bluetooth chips work, I look forward to sharing hitherto-unknown information about how to navigate and understand these mostly-16-bit-MIPS-code systems. And I’ll discuss how their ROM-“patch”ing firmware update mechanism works, how you can patch it to change its code too, and the security implications thereof.
Breaking the Firmware Trust: Disabling Security in a Locked BIOS
The article shows how modifying UEFI firmware at the flash level can disable BIOS security features even when the interface is locked, enabling DMA attacks that bypass protections and lead to SYSTEM-level access.
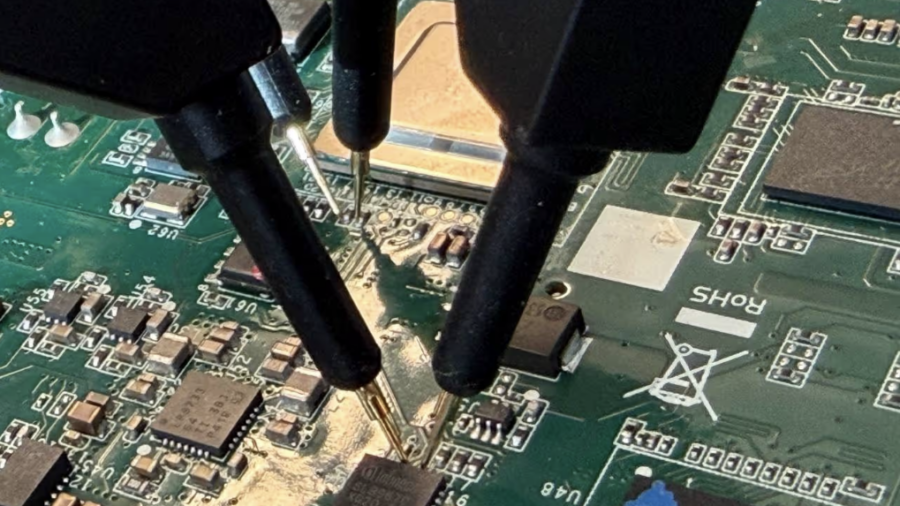
(CVE-2026-0714) TPM-sniffing LUKS Keys on an Embedded Device
Researchers discovered CVE-2026-0714 where a Moxa embedded device leaks its LUKS disk key in plaintext over the TPM SPI bus during boot. By sniffing TPM communication with a logic analyzer, attackers with physical access can recover the encryption key.
TP-Link Tapo C200: Hardcoded Keys, Buffer Overflows and Privacy in the Era of AI Assisted Reverse Engineering
The article shows how AI-assisted reverse engineering of the TP-Link Tapo C200 firmware uncovered hardcoded keys, buffer overflows, and insecure APIs, demonstrating how IoT devices can expose users to remote compromise and privacy risks.
Booting into Trust: Reverse Engineering macOS Secure Boot Internals
The article analyzes the macOS secure boot chain on Apple Silicon, showing how Boot ROM, cryptographic verification, Secure Enclave, and staged bootloaders create a hardware-anchored chain-of-trust that protects the OS from power-on to kernel startup.
Reverse Engineering the Tapo C260 and Tapo Discovery Protocol v2
The research reverse-engineers the TP-Link Tapo C260 camera firmware and analyzes Tapo Discovery Protocol v2. By dumping and decrypting the filesystem, the author reconstructs protocol logic and maps the device’s network attack surface.
Hacking a Bluetooth Printer Server: GATT to UART Adapter?
Reverse engineering a Bluetooth printer server reveals multiple security flaws, including exposed debug interfaces and insecure GATT services, enabling unauthenticated remote code execution with root privileges via Bluetooth or network access.
Blinkenlights 2.0: Reverse Engineering a Smartwatch via Screen Signals
Reverse engineering a cheap smartwatch and reviving the classic “blinkenlights” attack to extract firmware through screen update patterns, revealing weaknesses in OTA update mechanisms, BLE communication, and embedded device security design.