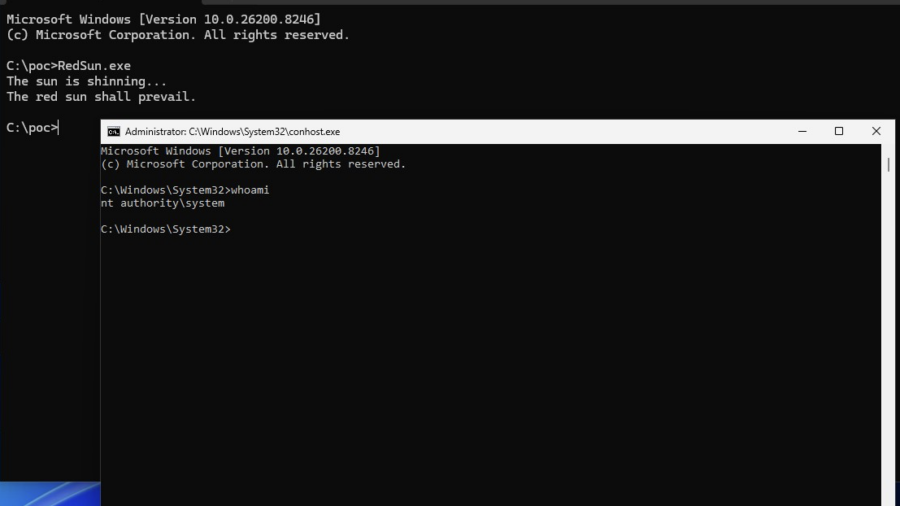
This vulnerability shows how Windows Defender file handling can be abused through filesystem races, Cloud Files APIs, and reparse points to redirect privileged writes and escalate from a low-privileged user to SYSTEM.
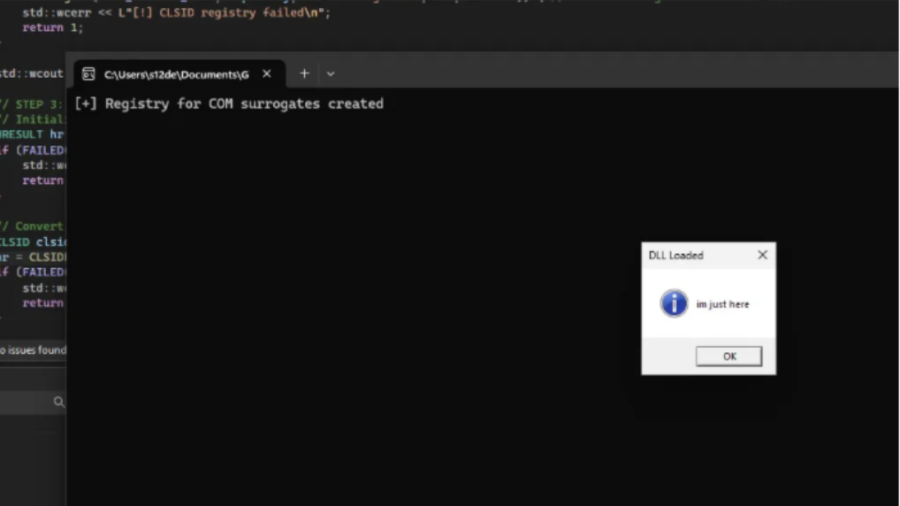
COMouflage: Stealthy DLL Surrogate Injection for Process Tree Evasion
COMouflage is a stealthy Windows injection technique that abuses COM DLL Surrogates to execute malicious DLLs inside dllhost.exe, making svchost.exe appear as the parent process and hiding the attacker’s process from detection.
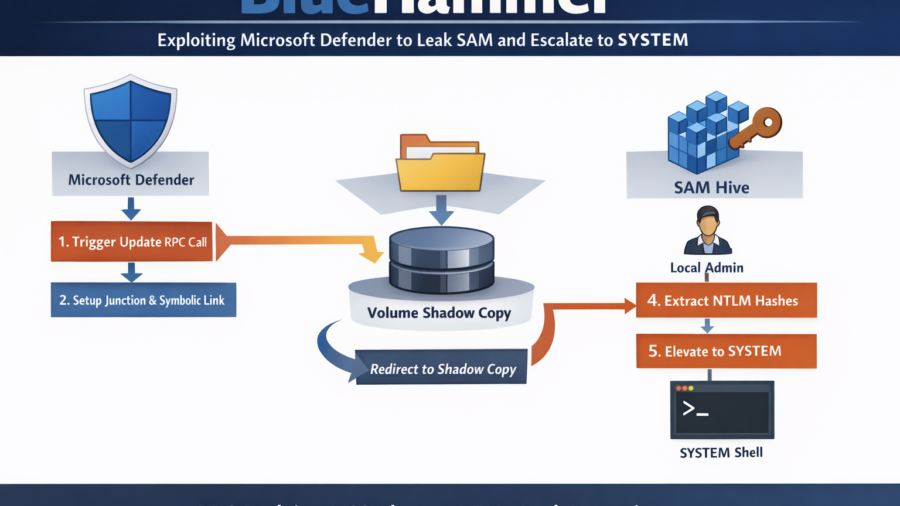
BlueHammer: Exploiting Microsoft Defender Update Workflow to Leak SAM and Escalate to SYSTEM
BlueHammer shows how Microsoft Defender’s update workflow can be abused to redirect privileged file access to a Volume Shadow Copy. By exploiting filesystem races and NT namespace tricks, the technique leaks the SAM hive, extracts NTLM hashes, and enables privilege escalation to SYSTEM.
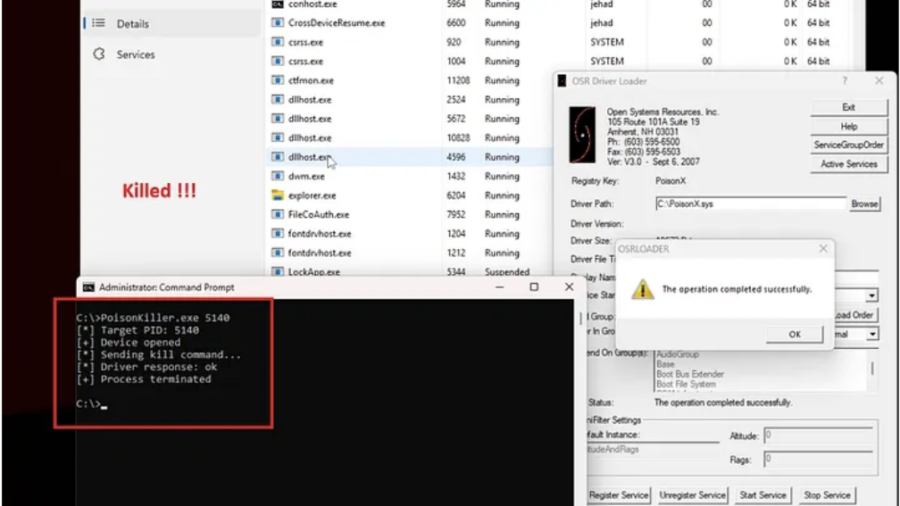
Signed to Kill: Reverse Engineering a 0-Day Used to Disable CrowdStrike EDR
The article analyzes a Microsoft-signed vulnerable driver used in a BYOVD attack to kill security processes. By sending crafted IOCTL requests with a target PID, attackers can terminate EDR services such as CrowdStrike Falcon.
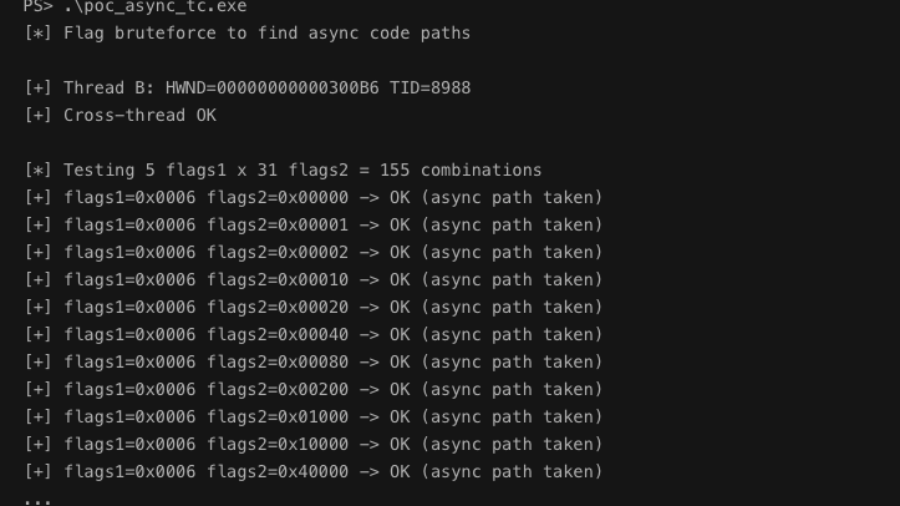
Async Windows Gone Wrong: Exploiting a Win32k Type Confusion Bug
The article analyzes a Win32k type confusion vulnerability in the async window action path of win32kfull.sys. Improper handling of window objects can corrupt kernel structures and potentially enable local privilege escalation.
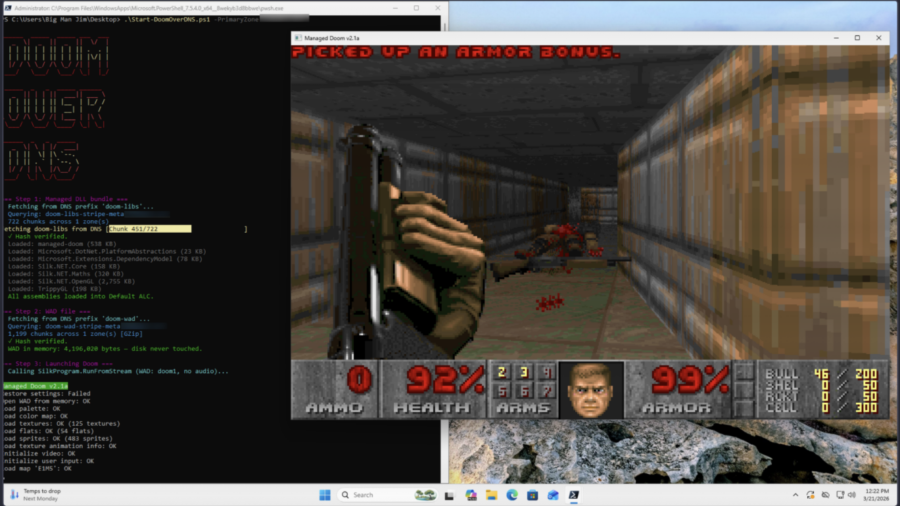
Can it Resolve DOOM? Game Engine in 2,000 DNS Records
The article shows a proof-of-concept where DOOM is stored across ~2,000 DNS TXT records and executed directly from memory. A PowerShell loader reconstructs the binary via DNS queries, illustrating how DNS can act as a covert payload delivery system.
TP-Link Tapo C200: Hardcoded Keys, Buffer Overflows and Privacy in the Era of AI Assisted Reverse Engineering
The article shows how AI-assisted reverse engineering of the TP-Link Tapo C200 firmware uncovered hardcoded keys, buffer overflows, and insecure APIs, demonstrating how IoT devices can expose users to remote compromise and privacy risks.
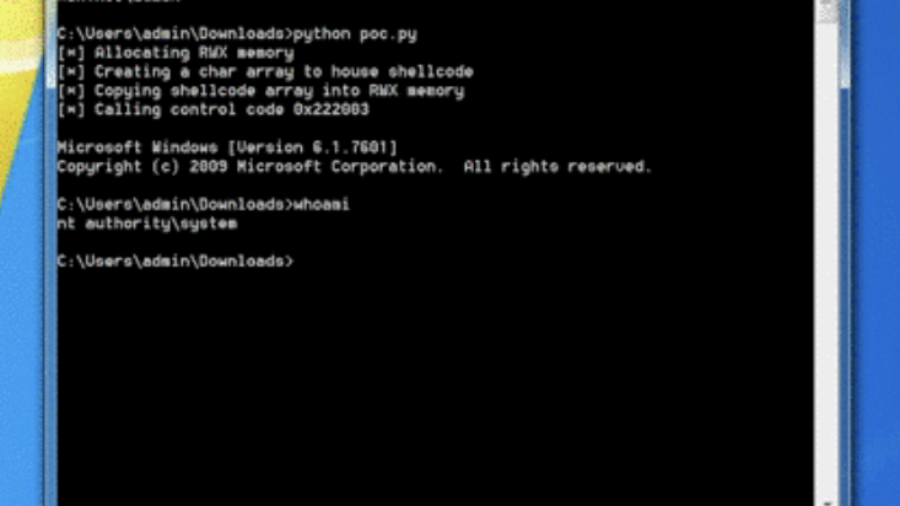
0x00 – Introduction to Windows Kernel Exploitation
The article introduces Windows kernel exploitation and explains how to build a research lab using tools like WinDbg and the HackSys Extreme Vulnerable Driver (HEVD) to study kernel vulnerabilities and exploit development.
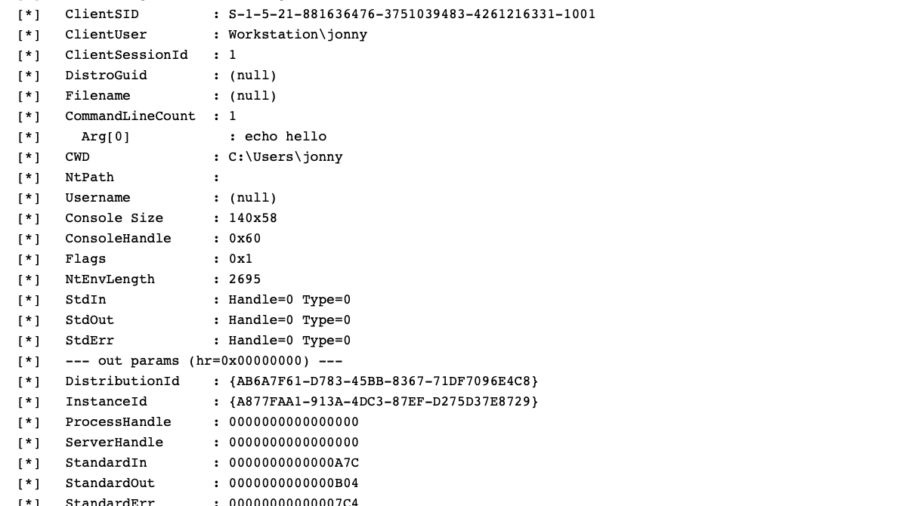
WSL, COM Hooking, & RTTI
The article demonstrates how to hook COM methods in Windows Subsystem for Linux by leveraging C++ RTTI metadata to reconstruct class layouts and locate virtual methods, enabling precise COM instrumentation without symbols.
Ghost in the PPL – LSASS Memory Dump
The article explains a technique for dumping memory from the protected LSASS process (PPL). It analyzes limitations of PPL protection and demonstrates how MiniDumpWriteDump and existing process handles can be used to extract credential data.