Dirty Frag is a Linux kernel local privilege escalation class abusing zero-copy networking, skb fragments, and in-place crypto to corrupt page cache memory and gain root privileges.
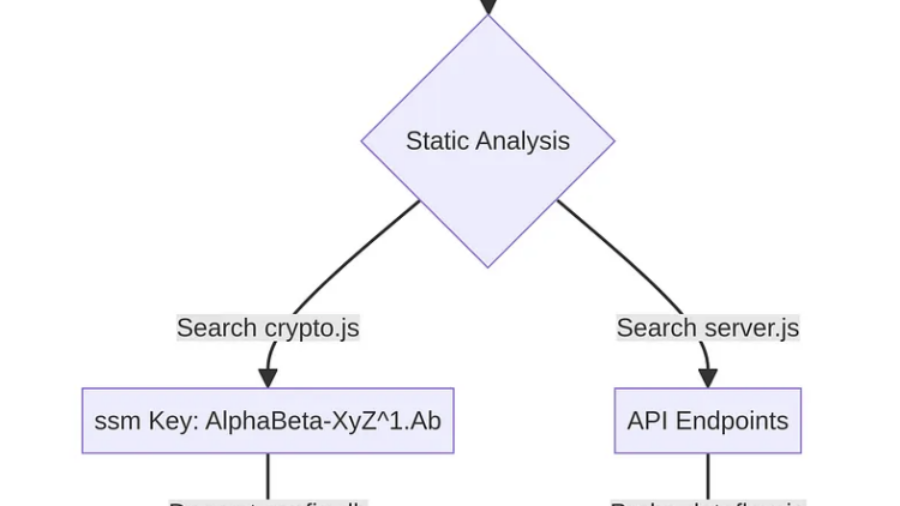
A Step-by-Step Guide to Uncovering Vulnerabilities in a Mobile App
The article shows how APK decompilation with Jadx exposed Cordova JavaScript code, hardcoded database keys, CryptoJS-derived secrets, backend endpoints, and a critical LFI flaw.
BullFrog DNS Pipelining: Smuggling Data Past CI/CD Egress Filters
A parsing flaw in BullFrog’s DNS-over-TCP handling allows attackers to bypass CI/CD egress filtering by pipelining DNS queries. The filter validates only the first query, letting malicious queries slip through.
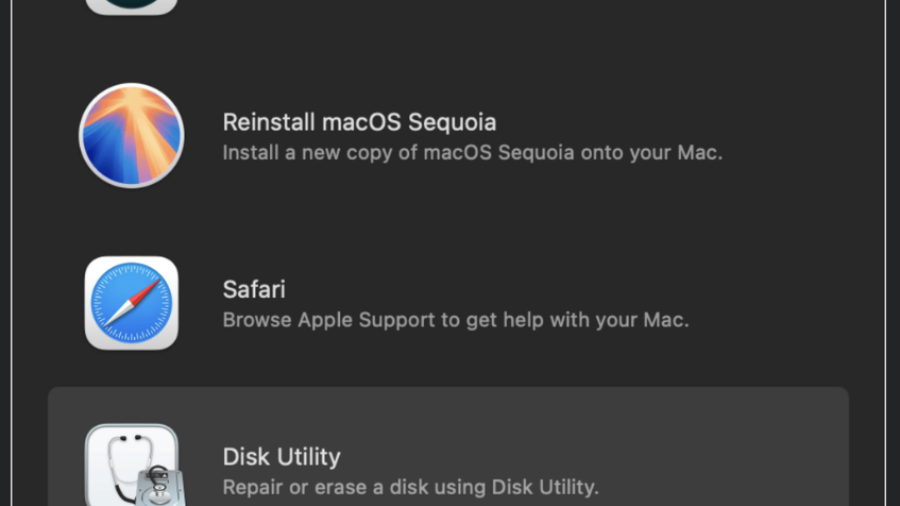
Recovery Mode Breakdown: Turning macOS Recovery Safari into Root Persistence
A macOS Recovery Mode Safari flaw allowed attackers to write arbitrary files to system partitions. By placing a malicious LaunchDaemon in /Library/LaunchDaemons, an attacker could achieve persistent root execution after reboot.
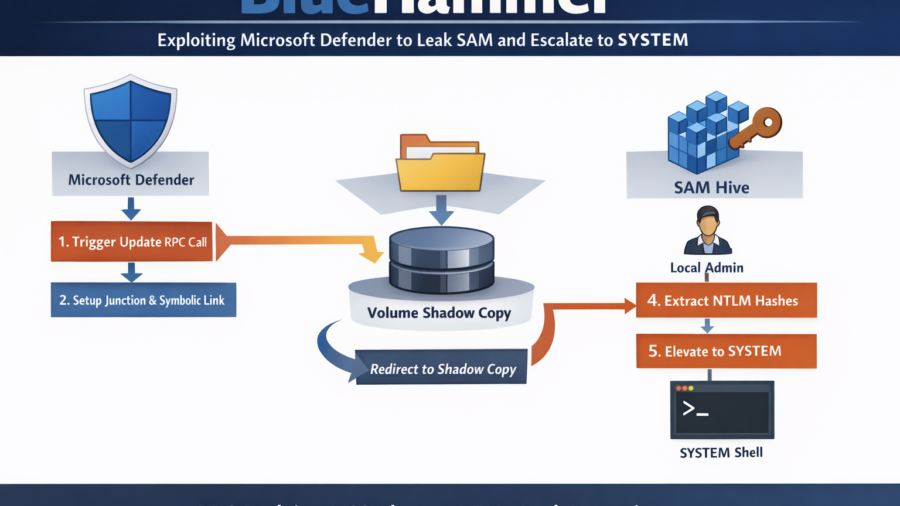
BlueHammer: Exploiting Microsoft Defender Update Workflow to Leak SAM and Escalate to SYSTEM
BlueHammer shows how Microsoft Defender’s update workflow can be abused to redirect privileged file access to a Volume Shadow Copy. By exploiting filesystem races and NT namespace tricks, the technique leaks the SAM hive, extracts NTLM hashes, and enables privilege escalation to SYSTEM.
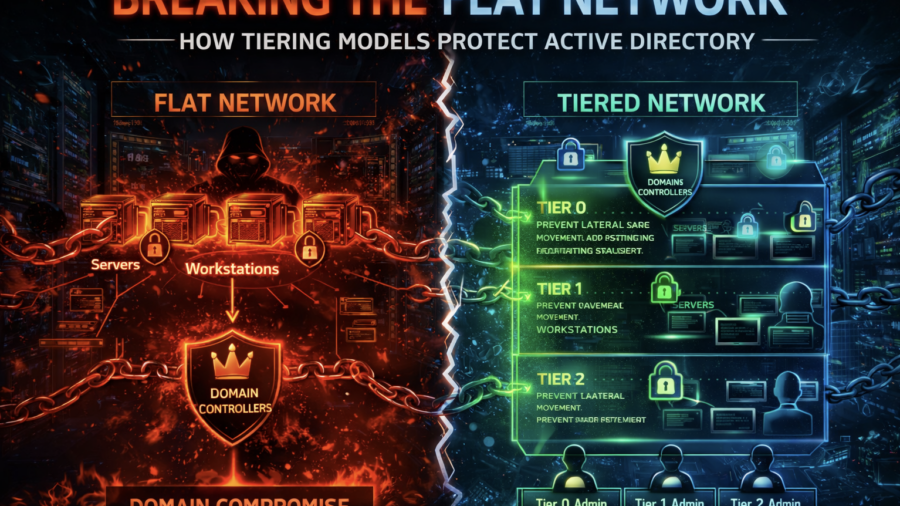
Breaking the Flat Network: How Tiering Models Protect Active Directory
The article explains how flat enterprise networks enable easy lateral movement and domain compromise. It shows how Active Directory tiering models segment privileges and systems to prevent attackers from escalating access.
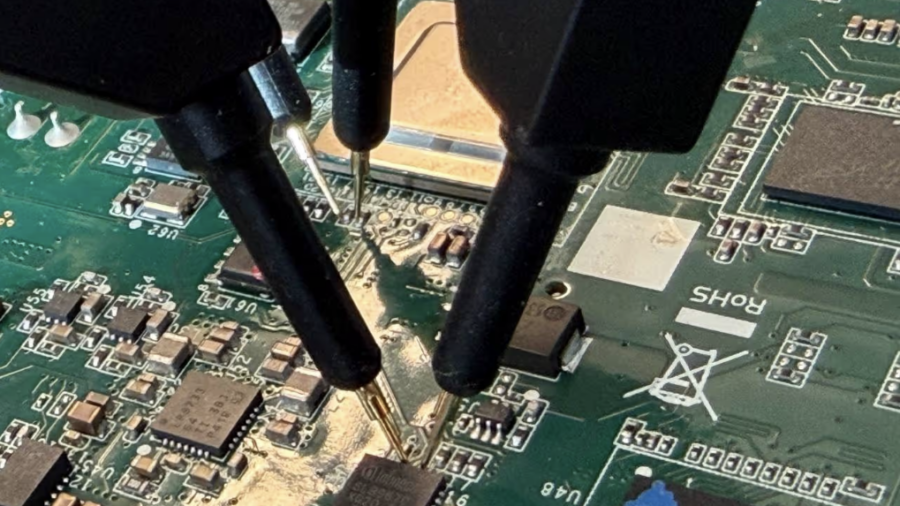
(CVE-2026-0714) TPM-sniffing LUKS Keys on an Embedded Device
Researchers discovered CVE-2026-0714 where a Moxa embedded device leaks its LUKS disk key in plaintext over the TPM SPI bus during boot. By sniffing TPM communication with a logic analyzer, attackers with physical access can recover the encryption key.
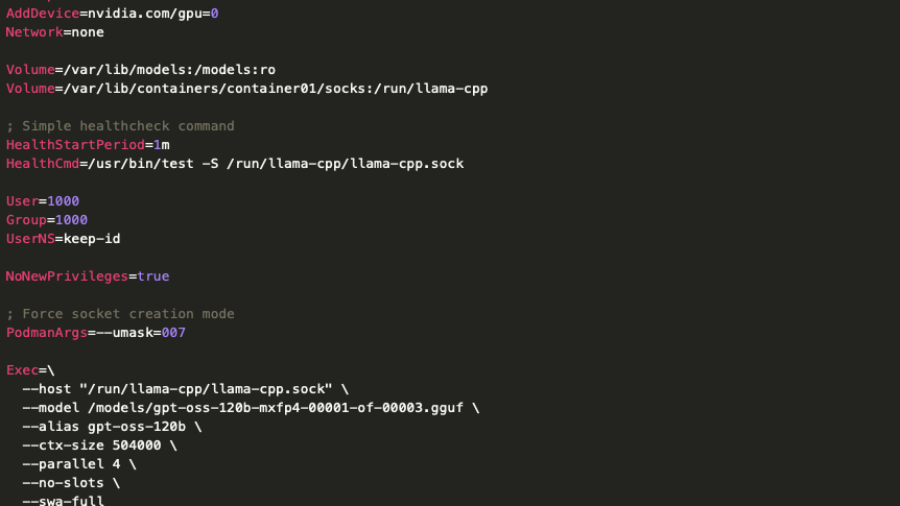
When Local AI Becomes an Attack Vector: A Deep Dive into LLM Infrastructure Security
The article analyzes a real deployment of a low-privileged on-prem LLM server and shows that even restricted models can expose internal systems through APIs, RAG pipelines, and data access, creating new enterprise attack surfaces.