A bug in macOS’s TCP stack causes networking to fail after about 49.7 days of uptime. A 32-bit timer overflow freezes the TCP clock, preventing cleanup of closed connections and eventually exhausting ephemeral ports.
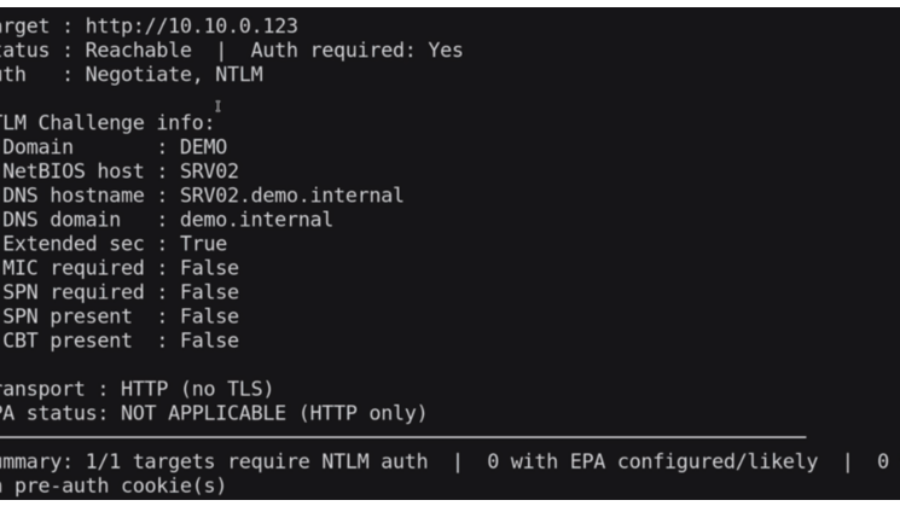
Relaying Trust: Exploiting NTLM Authentication to Compromise Active Directory
he article demonstrates an NTLM relay attack against Active Directory using tools like ntlmrelayx and PetitPotam. By relaying authentication to LDAP, attackers can create accounts, abuse delegation, and gain administrative access.
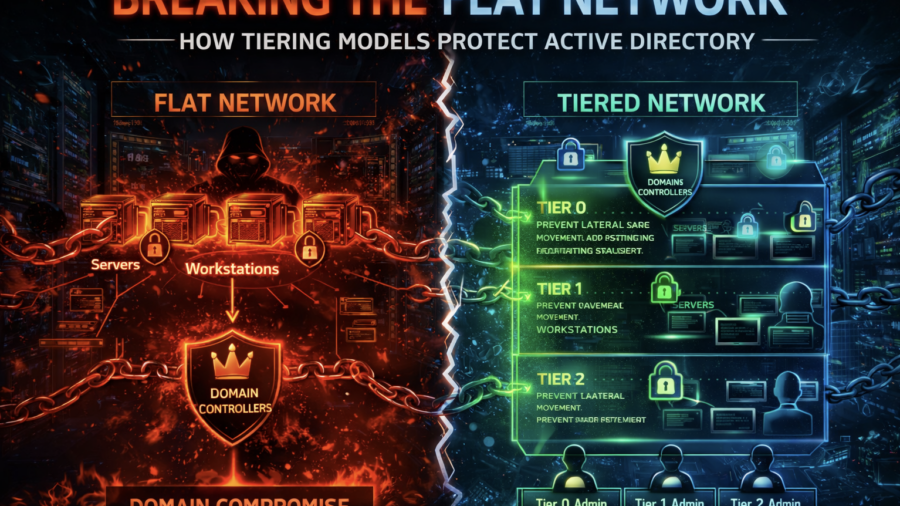
Breaking the Flat Network: How Tiering Models Protect Active Directory
The article explains how flat enterprise networks enable easy lateral movement and domain compromise. It shows how Active Directory tiering models segment privileges and systems to prevent attackers from escalating access.
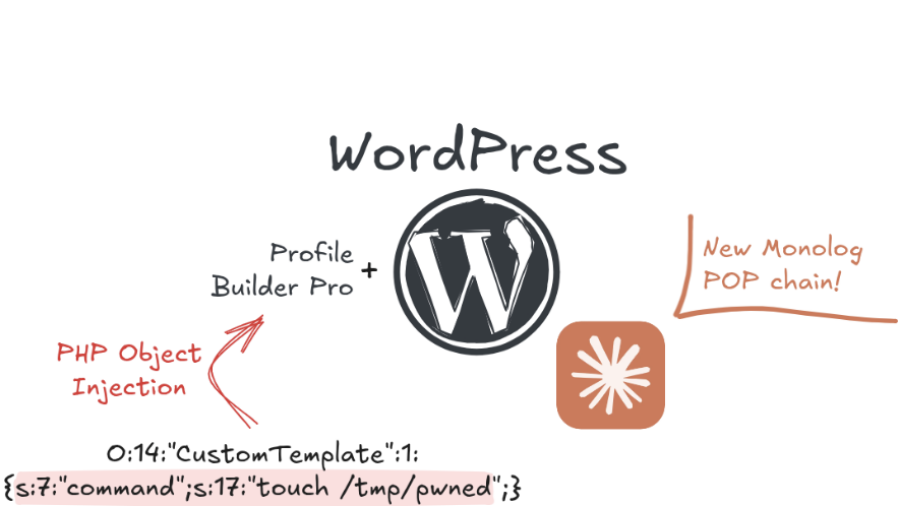
Exploiting a PHP Object Injection in Profile Builder Pro in the era of AI
The article explains how researchers exploited an unauthenticated PHP Object Injection in the WordPress plugin Profile Builder Pro, showing how AI tools can accelerate vulnerability discovery and exploit development in modern web applications.
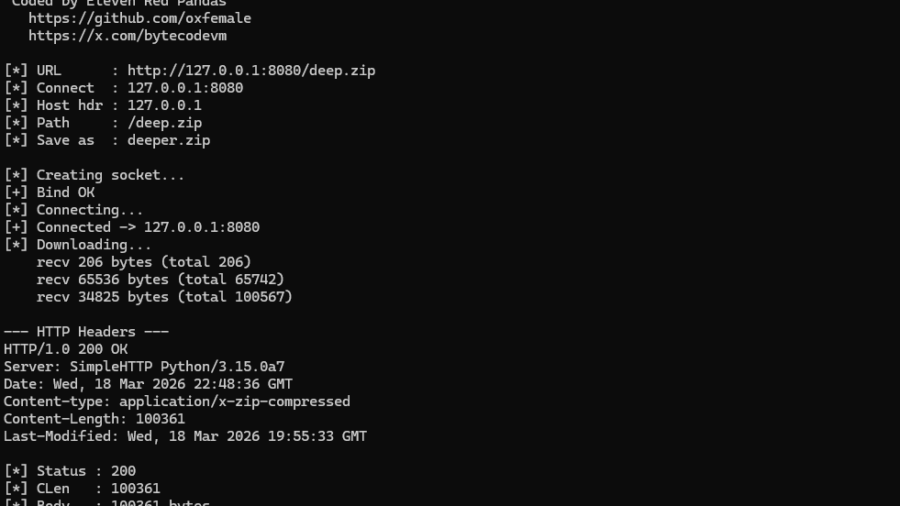
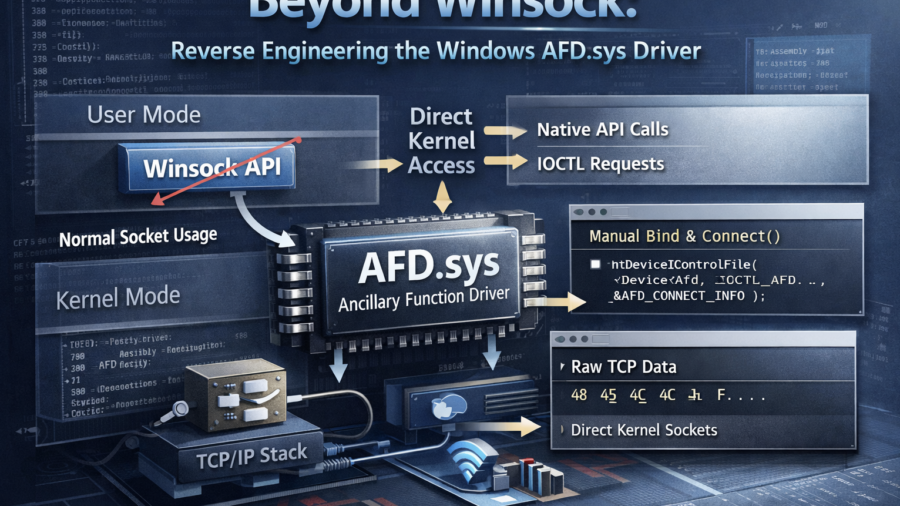
NT AFD.SYS HTTP Downloader: From First Syscall to bypass the majority of usermode EDR hooks
The article demonstrates how to bypass the Winsock layer by communicating directly with the Windows AFD driver using Native API calls. It explains how socket operations can be replicated via IOCTLs and how this reduces reliance on standard networking APIs.
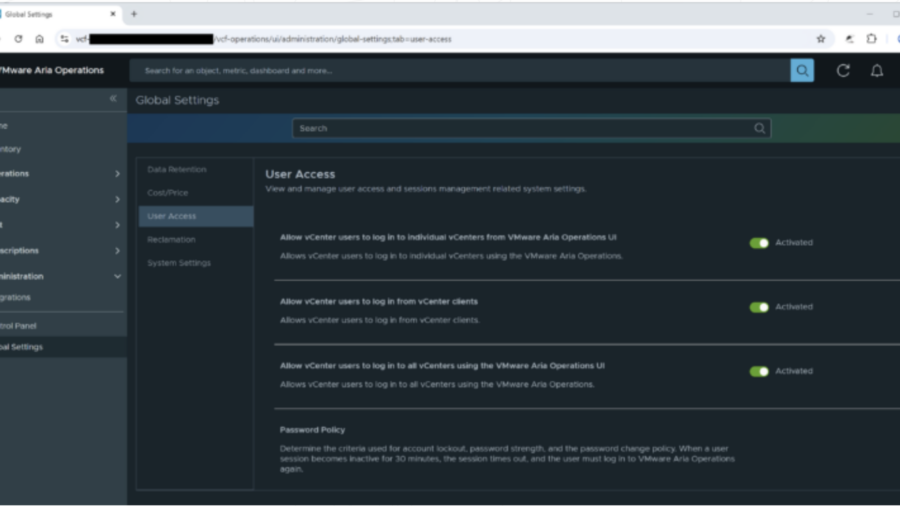
Vulnerabilities in Broadcom VMware Aria Operations: Privilege Escalation (CVE-2025-41245 / CVE-2026-22721)
The article examines vulnerabilities in VMware Aria Operations that enable credential disclosure and privilege escalation. Attackers with limited access can escalate privileges and gain administrative control over the infrastructure monitoring platform.
Peeling Back the Socket Layer: Reverse Engineering Windows AFD.sys
The research reverse-engineers Windows AFD.sys, showing how TCP sockets can be created, connected, and used by sending handcrafted IOCTL requests directly to the kernel driver—completely bypassing the Winsock networking API.
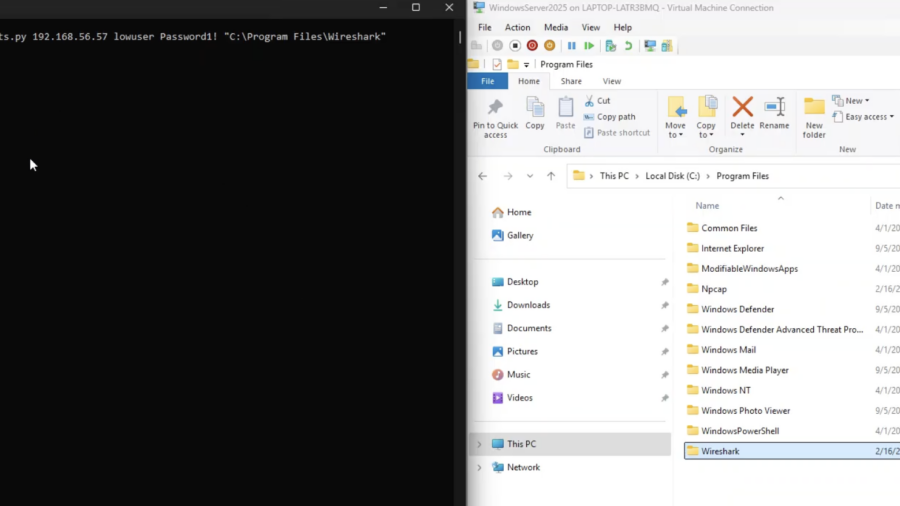
Physical Network Sniffing: Capturing Ethernet Traffic with Simple Alligator Clips
The article demonstrates how Ethernet traffic can be passively intercepted at the physical layer using simple tools like alligator clips attached to network cables. It highlights risks of exposed wiring and shows how attackers can capture unencrypted traffic.
Windows Kernel Debugging
The article explains how to set up Windows kernel debugging over a network using WinDBG and a host/target configuration. It covers enabling debug mode, connecting WinDBG to a remote VM, and using kernel debug infrastructure for low-level inspection and manipulation.
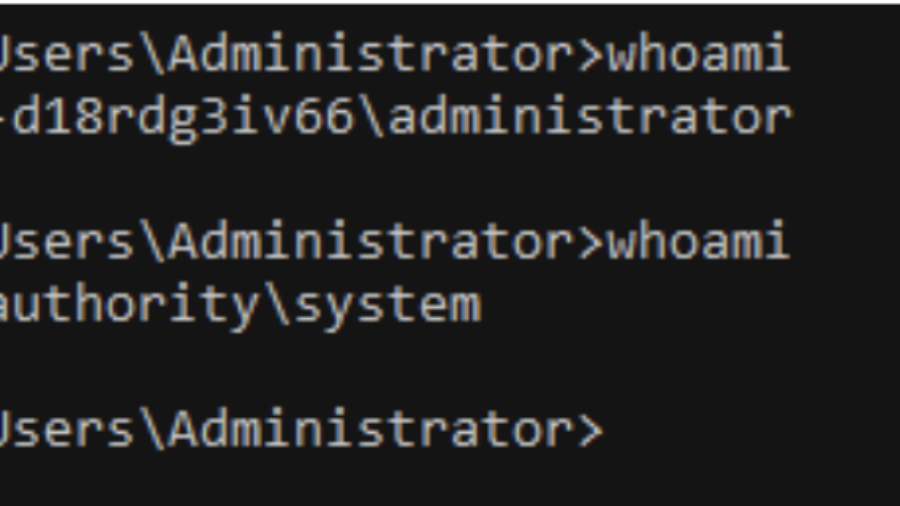
EventLog-in: Propagating With Weak Credentials Using the Eventlog Service in Microsoft Windows (CVE-2025-29969)
SafeBreach Labs disclosed a critical RCE in the MS-EVEN RPC service (CVE-2025-29969) that lets low-privilege users write arbitrary files remotely on Windows 11/Server 2025, bypassing share limits. Patched May 2025.