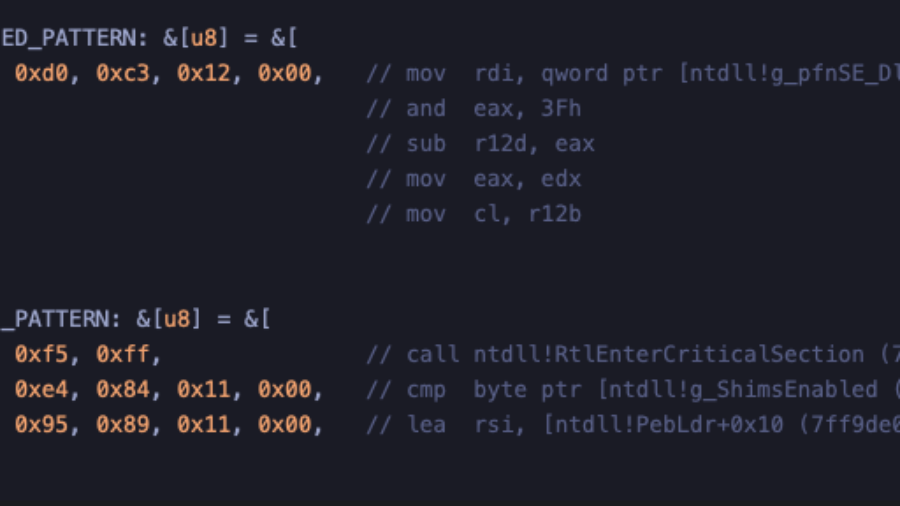
How to implement Early Cascade Injection in Rust, a stealthy Windows process injection technique that hijacks shim engine callbacks in ntdll to execute shellcode during early process initialization, before many EDR hooks activate.
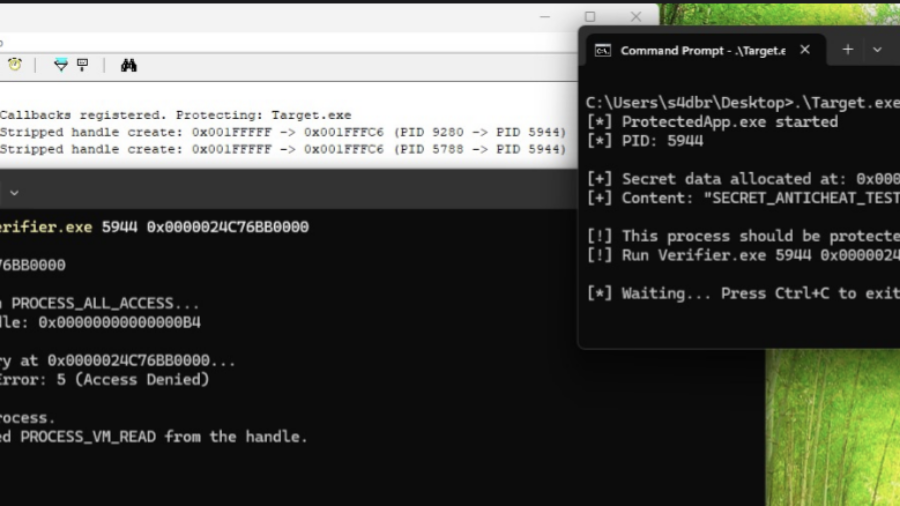
How Kernel Anti-Cheats Work: A Deep Dive into Modern Game Protection
The article explains how modern kernel-level anti-cheat systems work, describing their driver architecture, callbacks, memory monitoring, and detection methods used to identify cheats that operate at the same privilege level as the operating system kernel.
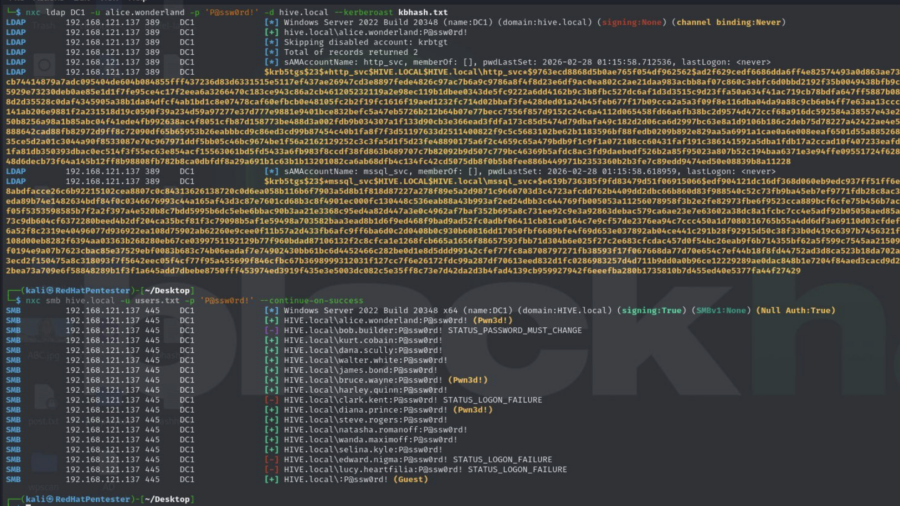
Active Directory Security Assessment: Password Spraying, Privilege Escalation, and Kerberoasting
This article analyzes an Active Directory attack chain where password spraying reveals valid credentials, privileged accounts enable escalation, and Kerberoasting exposes service account hashes, demonstrating how weak credential management can lead to full domain compromise.
Reverse engineering undocumented Windows Kernel features to work with the EDR
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.
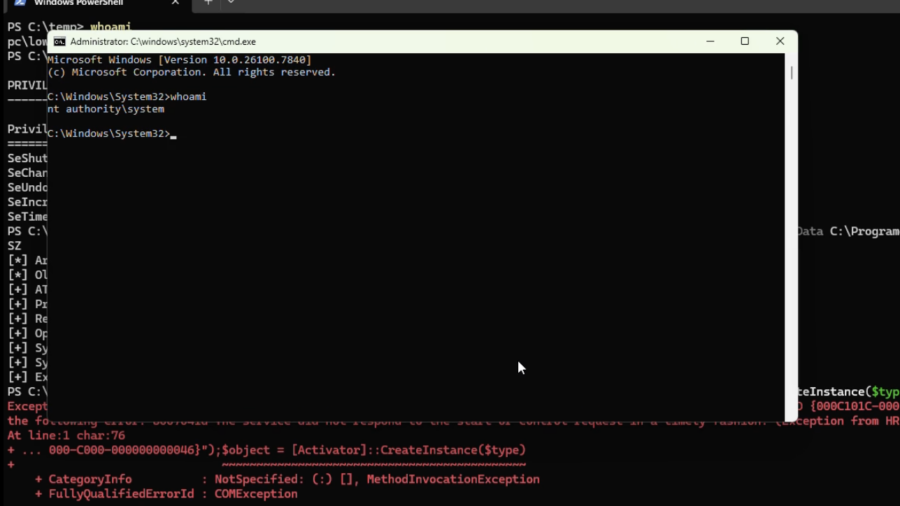
Silent Harvest: Extracting Windows Secrets Under the Radar
“Silent Harvest” explains how attackers can quietly extract sensitive Windows secrets such as credentials and security keys by abusing legitimate registry and system mechanisms, avoiding LSASS dumping and bypassing many common EDR detections.
RIP RegPwn: The Rise and Fall of a Windows Registry Exploitation Technique
The article explores a red-team research project called “RegPwn,” showing how weaknesses in Windows registry handling can be abused to achieve privilege escalation or persistence, and discusses why the technique has now been mitigated or rendered ineffective.
Our Telegram channel
It’s great to see that our website now has its own Telegram channel! Follow us at @core-jmp.org to stay updated with the latest posts, security research, and new articles published on core-jmp.org.
Hacking a Bluetooth Printer Server: GATT to UART Adapter?
Reverse engineering a Bluetooth printer server reveals multiple security flaws, including exposed debug interfaces and insecure GATT services, enabling unauthenticated remote code execution with root privileges via Bluetooth or network access.
Blinkenlights 2.0: Reverse Engineering a Smartwatch via Screen Signals
Reverse engineering a cheap smartwatch and reviving the classic “blinkenlights” attack to extract firmware through screen update patterns, revealing weaknesses in OTA update mechanisms, BLE communication, and embedded device security design.
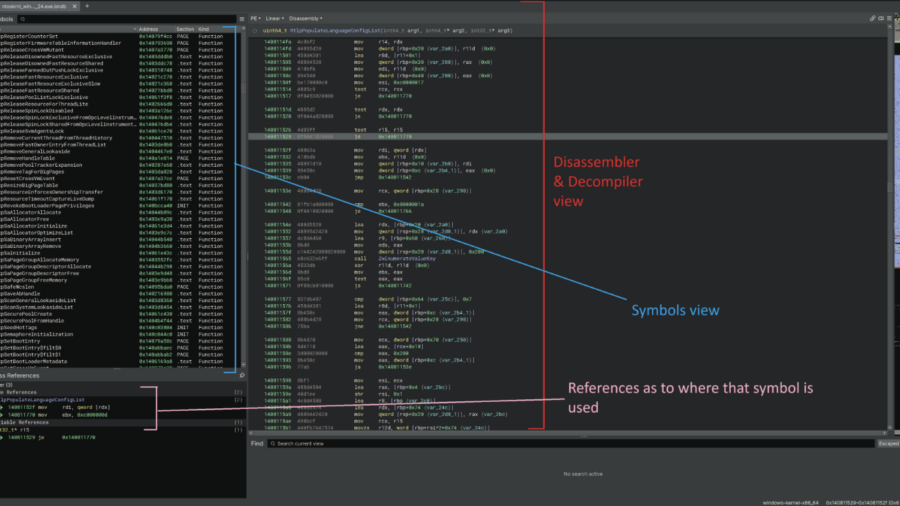
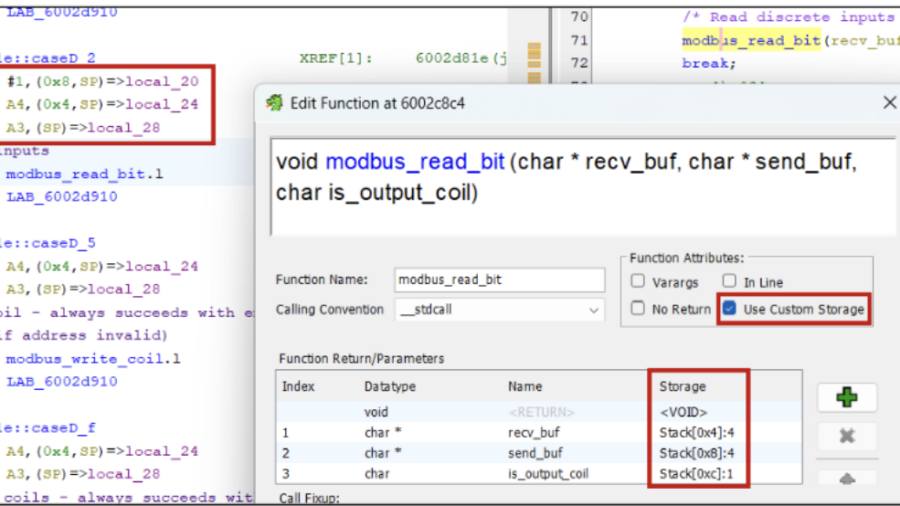
Taming the dragon: reverse engineering firmware with Ghidra
The article explains how to reverse engineer embedded firmware using Ghidra, covering techniques for loading firmware, identifying CPU architectures, analyzing functions, and using scripts/plugins to understand device logic and discover vulnerabilities.