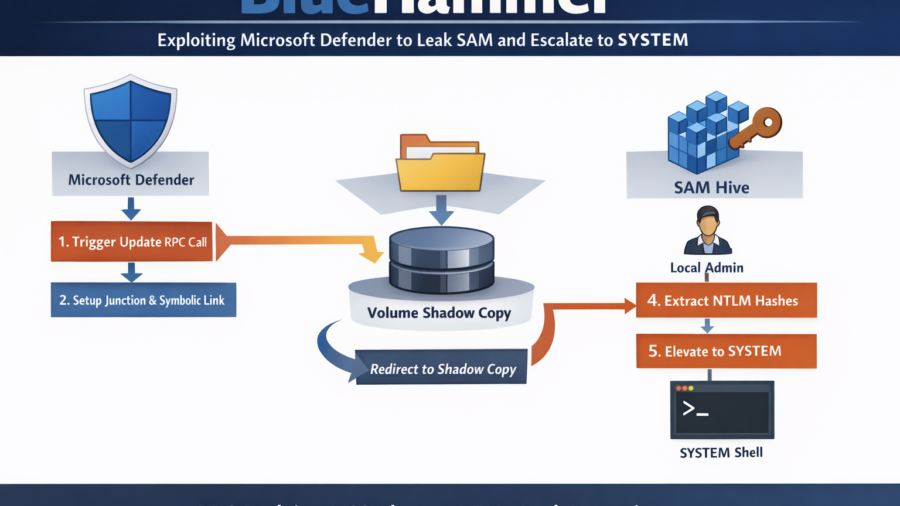
BlueHammer shows how Microsoft Defender’s update workflow can be abused to redirect privileged file access to a Volume Shadow Copy. By exploiting filesystem races and NT namespace tricks, the technique leaks the SAM hive, extracts NTLM hashes, and enables privilege escalation to SYSTEM.
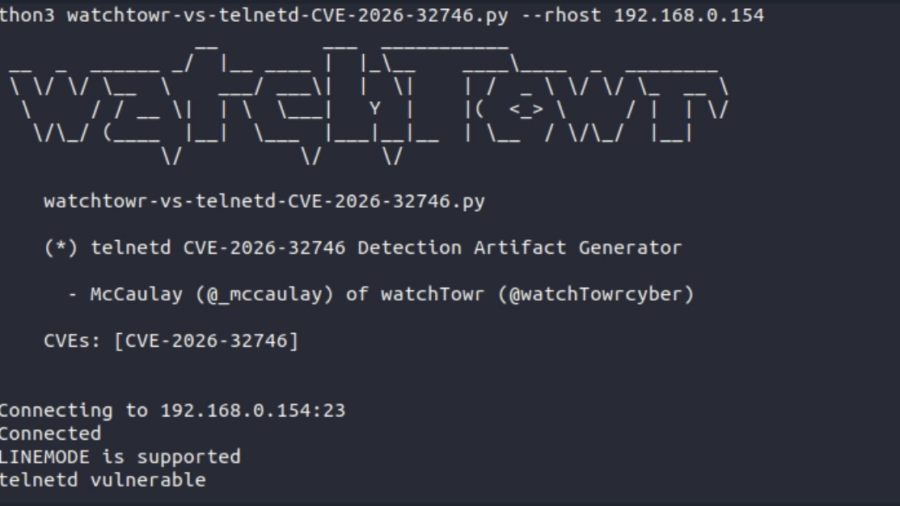
A 32-Year-Old Bug Walks Into A Telnet Server (GNU inetutils Telnetd CVE-2026-32746 Pre-Auth RCE)
The article analyzes CVE-2026-32746, a decades-old vulnerability in GNU Inetutils telnetd where a malformed LINEMODE SLC option triggers an out-of-bounds write, enabling unauthenticated remote exploitation.
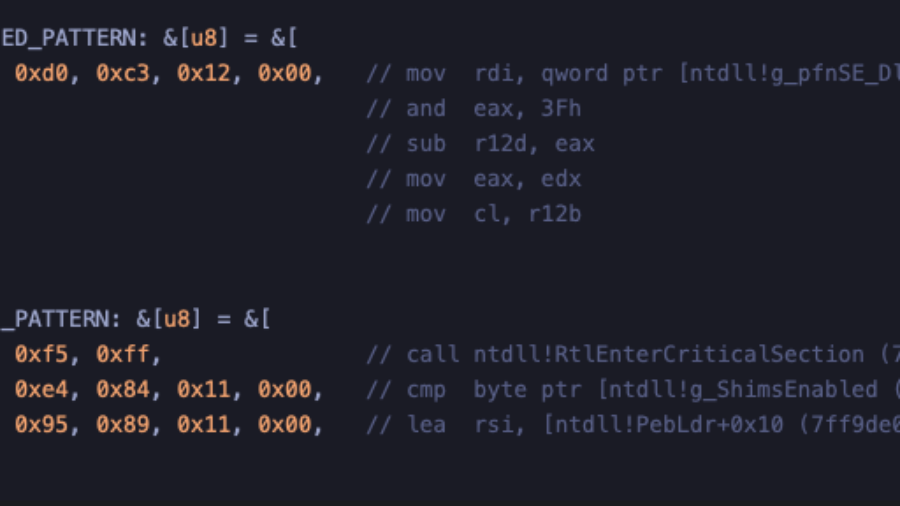
Crimes against NTDLL – Implementing Early Cascade Injection
How to implement Early Cascade Injection in Rust, a stealthy Windows process injection technique that hijacks shim engine callbacks in ntdll to execute shellcode during early process initialization, before many EDR hooks activate.
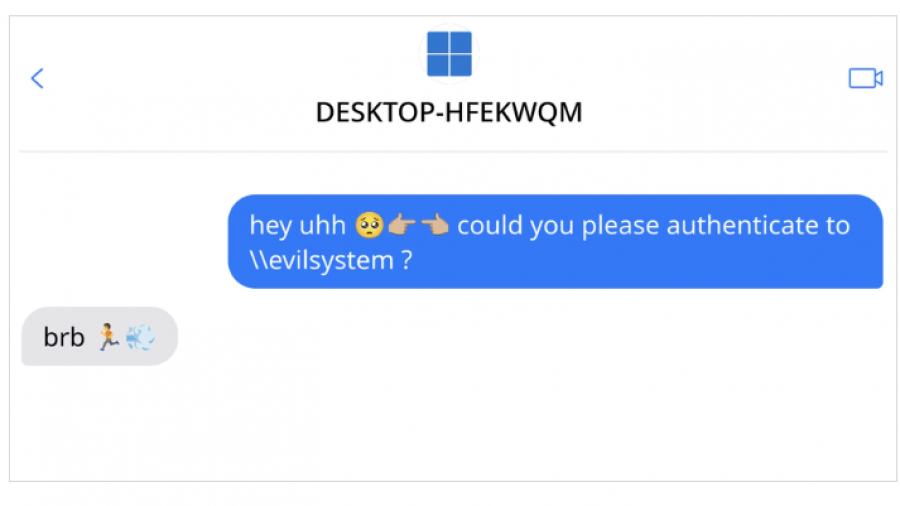
THE ULTIMATE GUIDE TO WINDOWS COERCION TECHNIQUES IN 2025
Windows authentication coercion is still a powerful AD primitive: it forces predictable auth flows and enables relay chains. Modern mitigations reduce easy abuse, but when combined with AD CS o