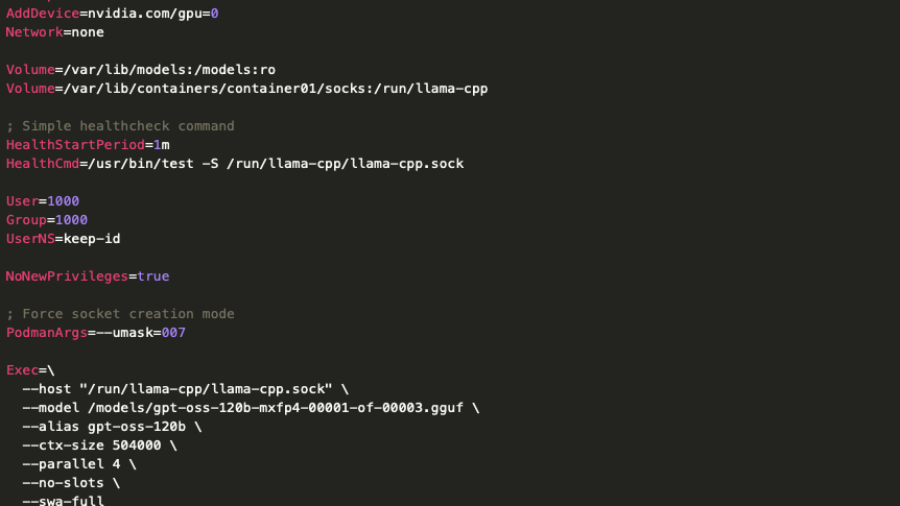
The article analyzes a real deployment of a low-privileged on-prem LLM server and shows that even restricted models can expose internal systems through APIs, RAG pipelines, and data access, creating new enterprise attack surfaces.
Exploiting a PHP Object Injection in Profile Builder Pro in the era of AI
The article explains how researchers exploited an unauthenticated PHP Object Injection in the WordPress plugin Profile Builder Pro, showing how AI tools can accelerate vulnerability discovery and exploit development in modern web applications.
TP-Link Tapo C200: Hardcoded Keys, Buffer Overflows and Privacy in the Era of AI Assisted Reverse Engineering
The article shows how AI-assisted reverse engineering of the TP-Link Tapo C200 firmware uncovered hardcoded keys, buffer overflows, and insecure APIs, demonstrating how IoT devices can expose users to remote compromise and privacy risks.
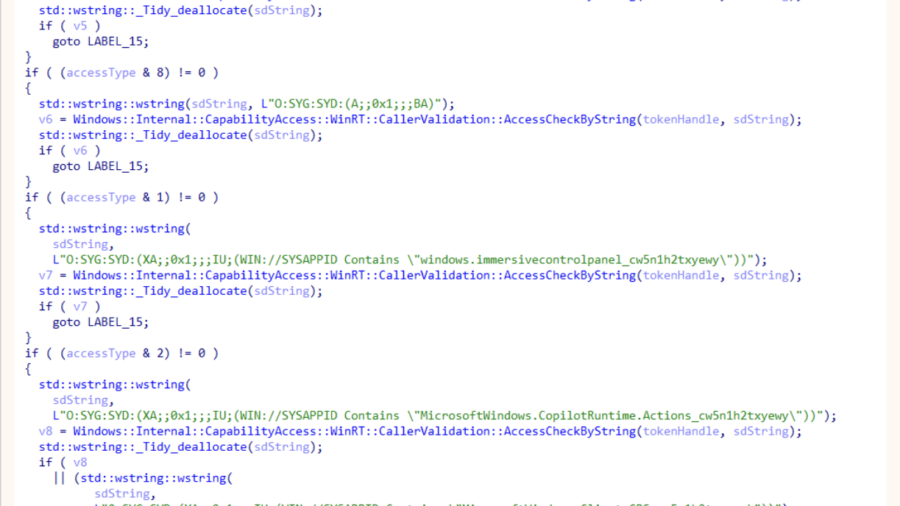
ODR: Internals of Microsoft’s New Native MCP Registration
The article explains Microsoft’s ODR mechanism for native MCP registration, enabling AI agents to discover and invoke system tools through the Model Context Protocol, preparing Windows for secure agent-driven workflows and integrations.