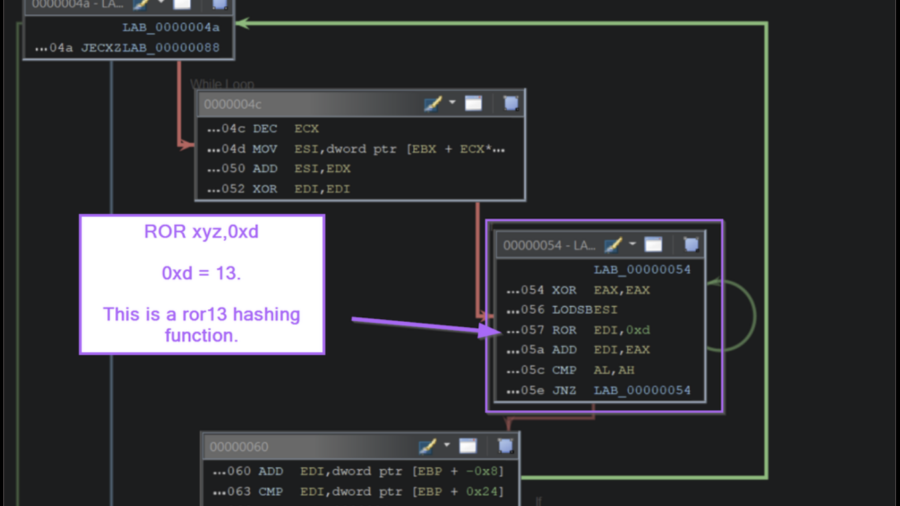
The article demonstrates how to analyze Windows shellcode in Ghidra by identifying API-hashing routines, resolving hidden Windows API calls, and extracting C2 infrastructure without relying on automated emulation tools.
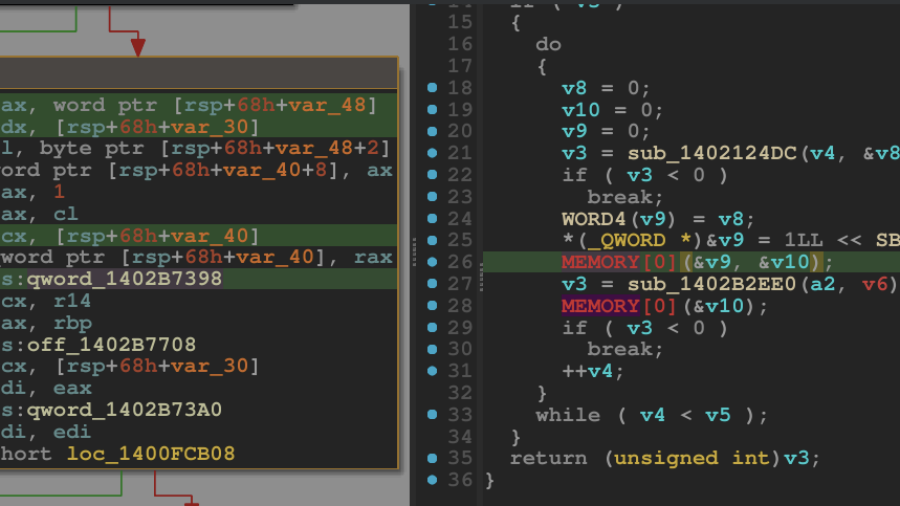
Breaking the Shield: Unpacking a VMProtected Windows Kernel Driver
A technical walkthrough showing how to unpack a VMProtected Windows kernel driver using WinDbg and dynamic analysis. The guide demonstrates restoring the hidden Import Address Table and dumping a clean driver for reverse engineering.
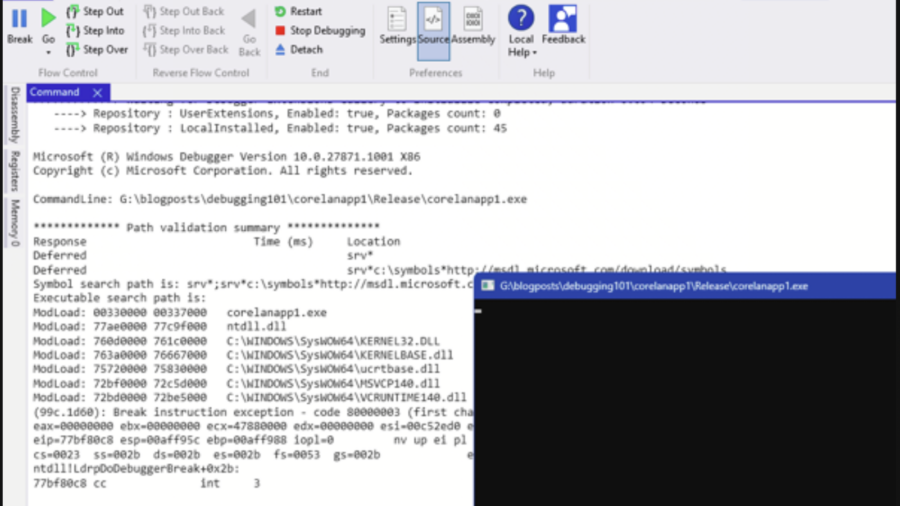
Debugging – WinDBG & WinDBGX Fundamentals
A beginner-friendly guide to debugging Windows programs using WinDbg and WinDbgX. It explains debugger basics, breakpoints, symbols, memory inspection, and execution control—key skills for reverse engineering and vulnerability research.
0x00 – Introduction to Windows Kernel Exploitation
The article introduces Windows kernel exploitation and explains how to build a research lab using tools like WinDbg and the HackSys Extreme Vulnerable Driver (HEVD) to study kernel vulnerabilities and exploit development.
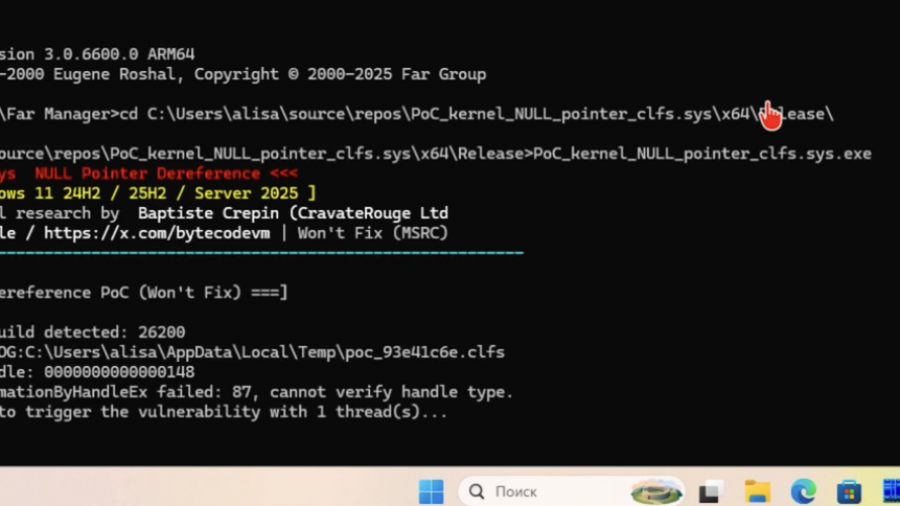
Won’t Fix: Kernel DoS in clfs.sys via NULL FastMutex Dereference
The article examines a Windows kernel bug in clfs.sys where a NULL pointer is dereferenced during fast mutex acquisition, causing a kernel crash and denial of service due to improper validation of a FAST_MUTEX pointer.
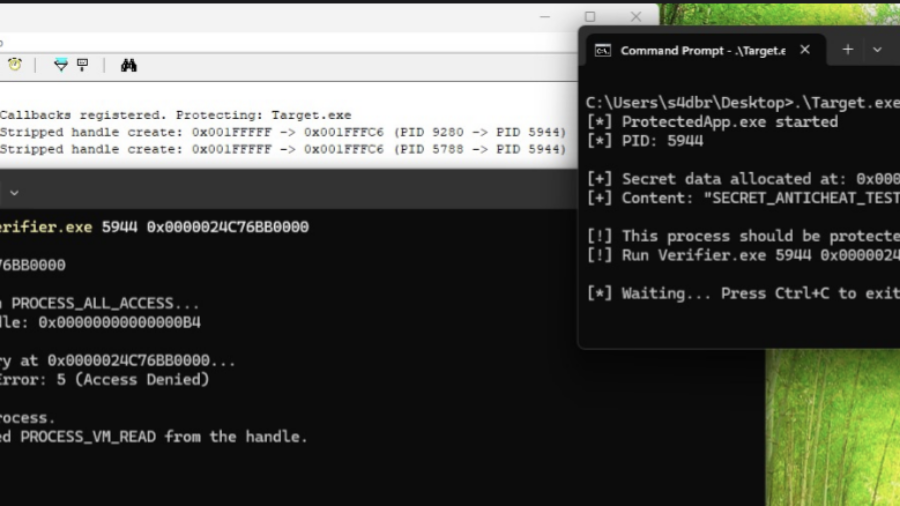
Ghost in the PPL – LSASS Memory Dump
The article explains a technique for dumping memory from the protected LSASS process (PPL). It analyzes limitations of PPL protection and demonstrates how MiniDumpWriteDump and existing process handles can be used to extract credential data.
How Kernel Anti-Cheats Work: A Deep Dive into Modern Game Protection
The article explains how modern kernel-level anti-cheat systems work, describing their driver architecture, callbacks, memory monitoring, and detection methods used to identify cheats that operate at the same privilege level as the operating system kernel.
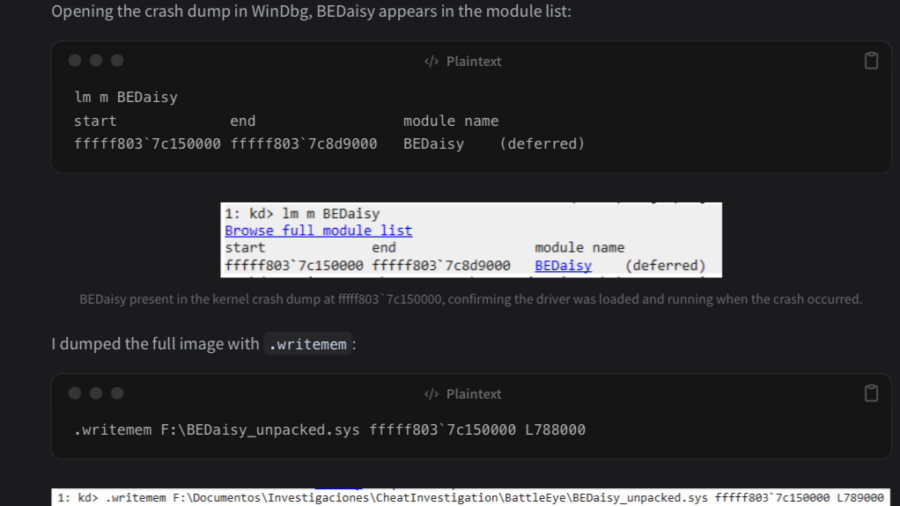
Reversing BEDaisy.sys: Static Analysis of BattlEye’s Kernel Anti-Cheat Driver
The article analyzes the Windows kernel driver BEDaisy.sys, used by BattlEye anti-cheat. Through static reverse engineering, it explores driver architecture, APC usage, hardware fingerprinting, import handling, and detection mechanisms used to monitor system activity.
Defeating Windows DEP Using ROP Chains Leveraging VirtualAlloc
Uses manual Return-Oriented Programming (ROP) to chain existing code fragments and call VirtualAlloc, changing memory permissions to bypass Windows DEP and then execute shellcode in exploited process memory.
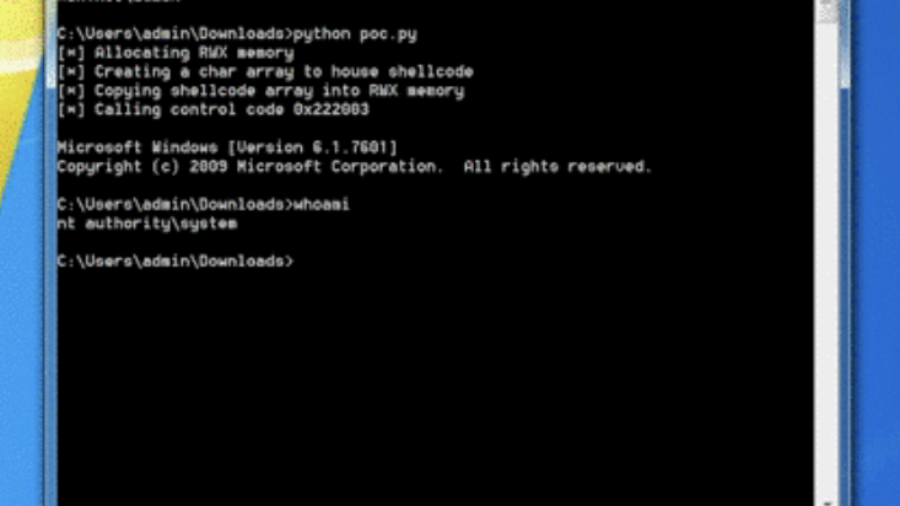
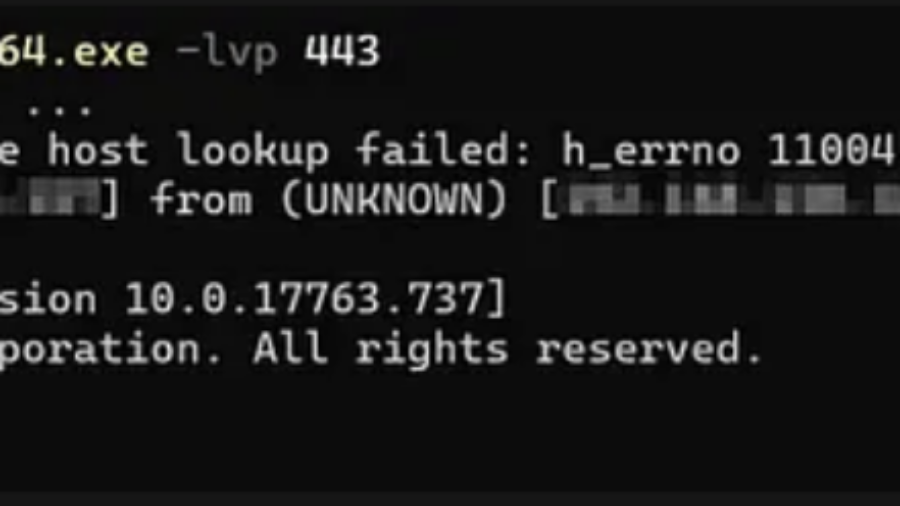
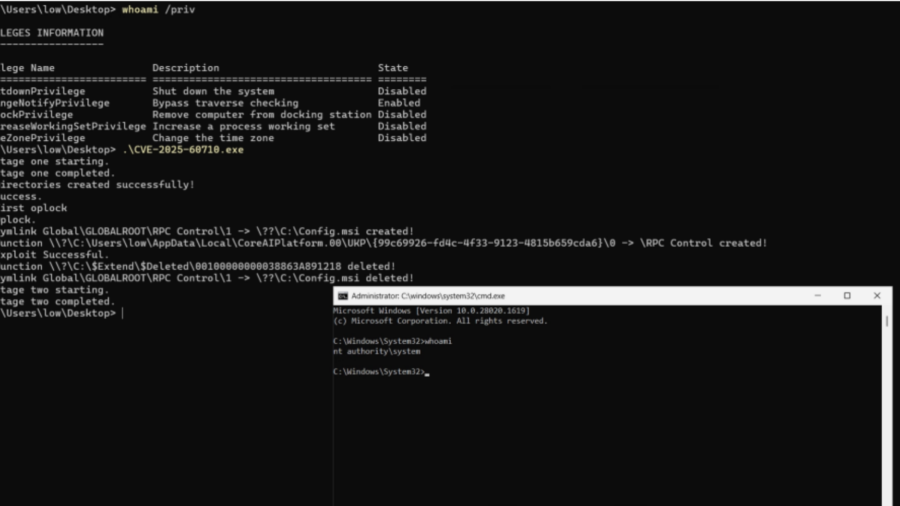
Total Recall – Retracing Your Steps Back to NT AUTHORITY\SYSTEM
A Windows elevation-of-privilege flaw in the Recall scheduled task let low-privileged users trigger it via WNF and abuse unsafe directory cleanup to execute arbitrary actions as NT AUTHORITY\SYSTEM.