ENKI analyzes CVE-2026-32223, a heap overflow in Windows usbprint.sys triggered by malformed USB printer descriptors, leading to SYSTEM privilege escalation via crafted USB device.
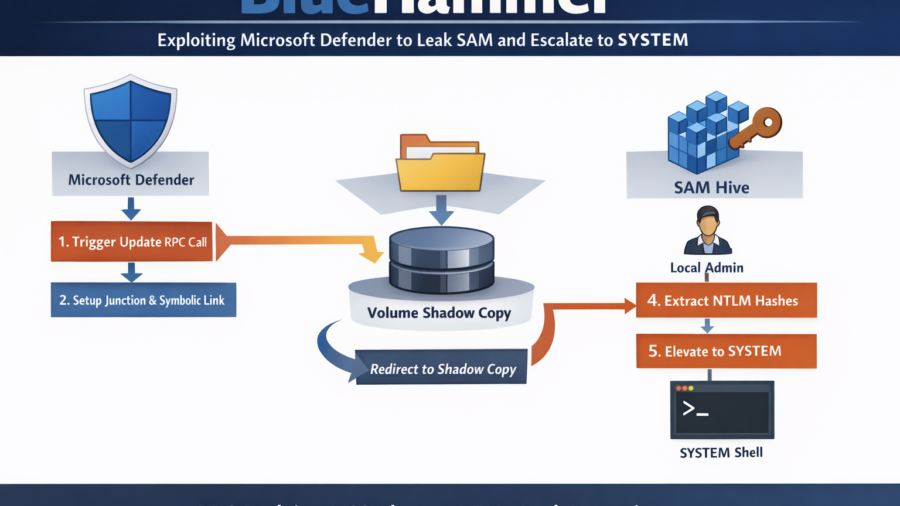
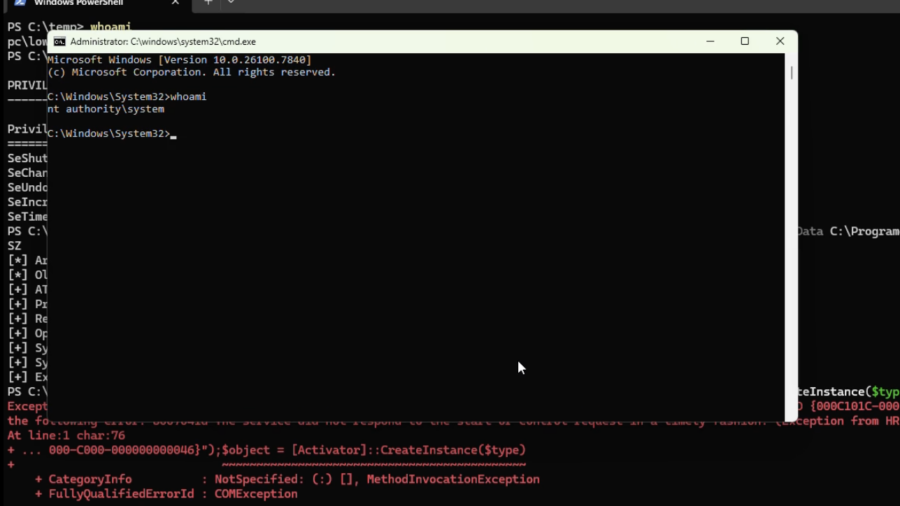
BlueHammer: Exploiting Microsoft Defender Update Workflow to Leak SAM and Escalate to SYSTEM
BlueHammer shows how Microsoft Defender’s update workflow can be abused to redirect privileged file access to a Volume Shadow Copy. By exploiting filesystem races and NT namespace tricks, the technique leaks the SAM hive, extracts NTLM hashes, and enables privilege escalation to SYSTEM.
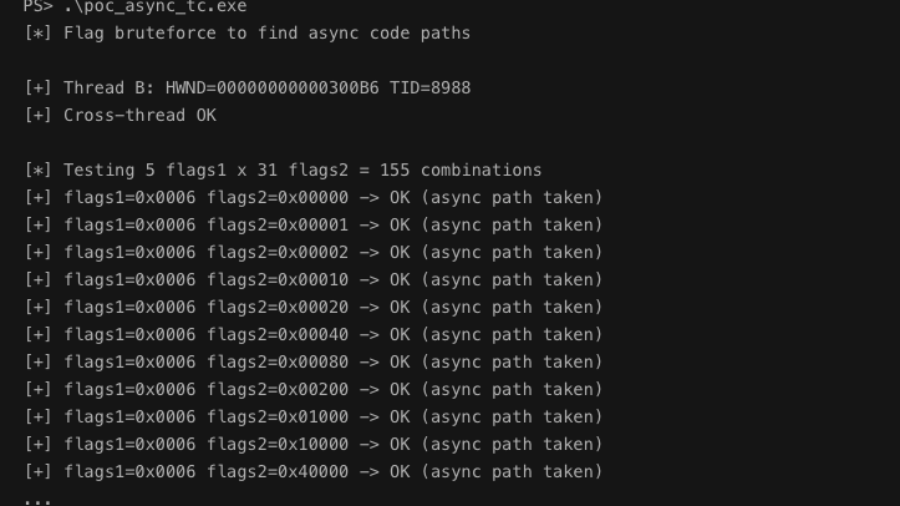
Async Windows Gone Wrong: Exploiting a Win32k Type Confusion Bug
The article analyzes a Win32k type confusion vulnerability in the async window action path of win32kfull.sys. Improper handling of window objects can corrupt kernel structures and potentially enable local privilege escalation.
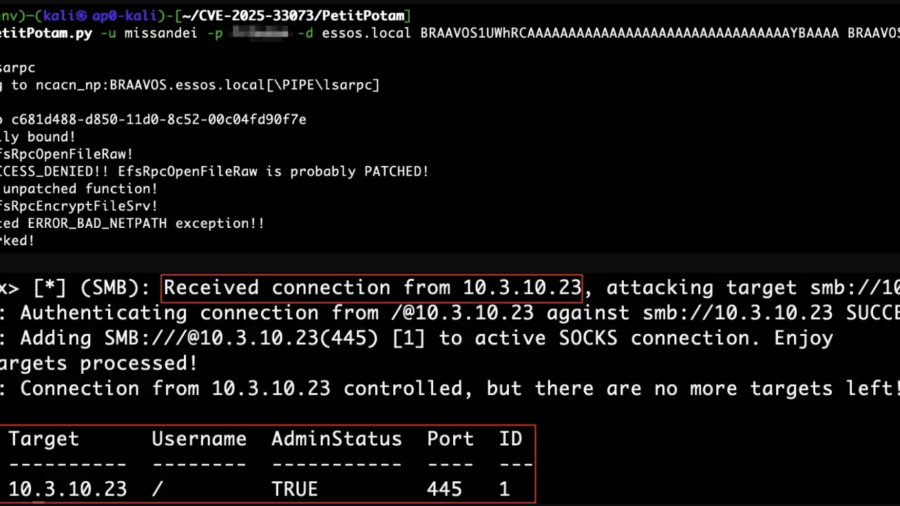
Reflecting on Your Tier Model: CVE-2025-33073 and the One-Hop Problem
CVE-2025-33073 enables NTLM reflection attacks that give attackers SYSTEM access on vulnerable Windows hosts. When combined with unconstrained delegation, a single compromised server can lead to full Active Directory domain compromise.
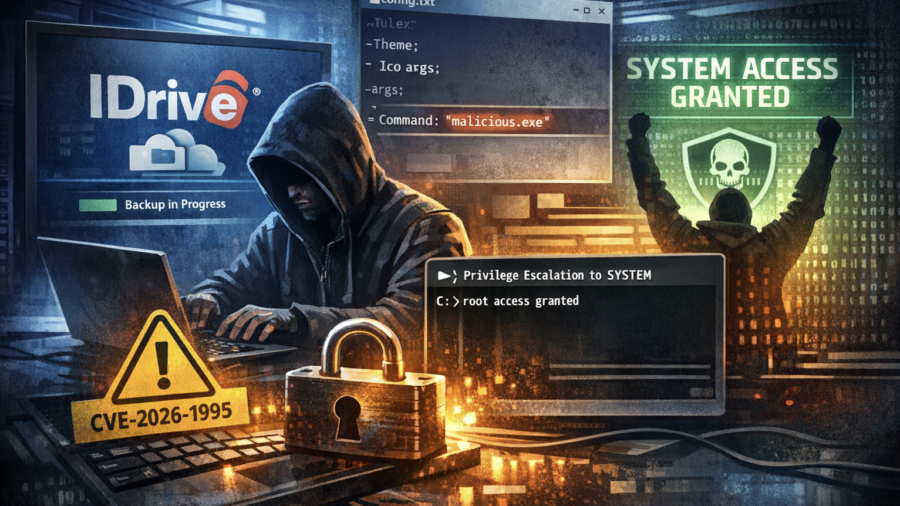
Backup to SYSTEM: Exploiting the IDrive Client Privilege Escalation Flaw
CVE-2026-1995 is a privilege escalation flaw in the IDrive Windows backup client. Weak file permissions allow low-privileged users to modify service arguments and execute arbitrary code as SYSTEM.
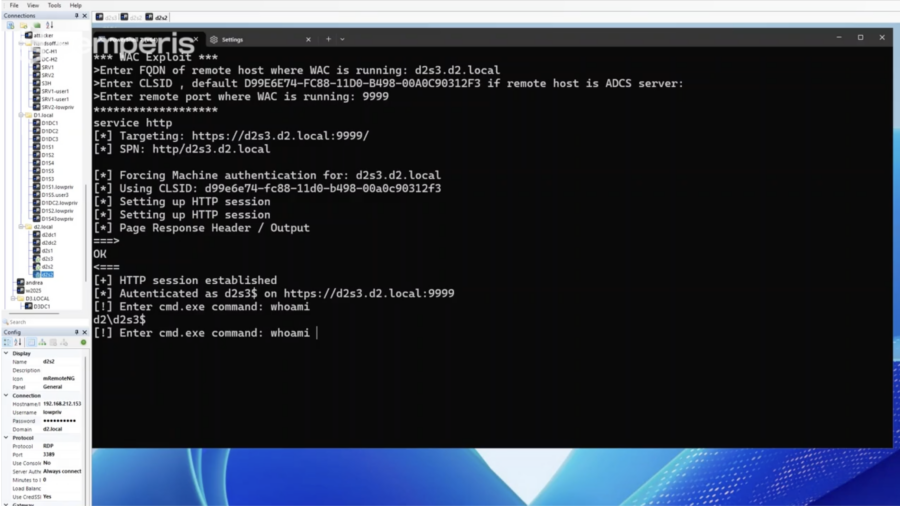
What You Need to Know: Windows Admin Center Remote Privilege Escalation (CVE-2026-26119)
CVE-2026-26119 is a high-severity privilege-escalation flaw in Windows Admin Center caused by improper authentication. Attackers with low-privileged access could gain admin rights and potentially compromise entire domains.
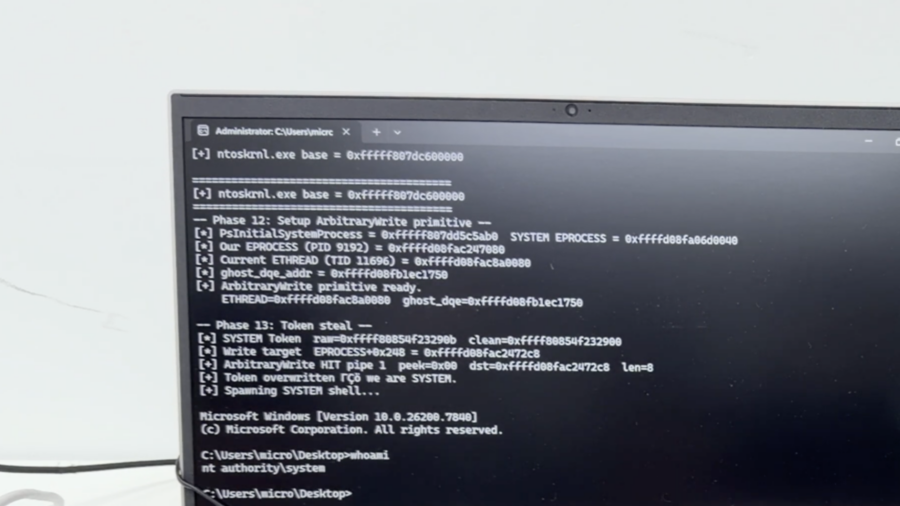
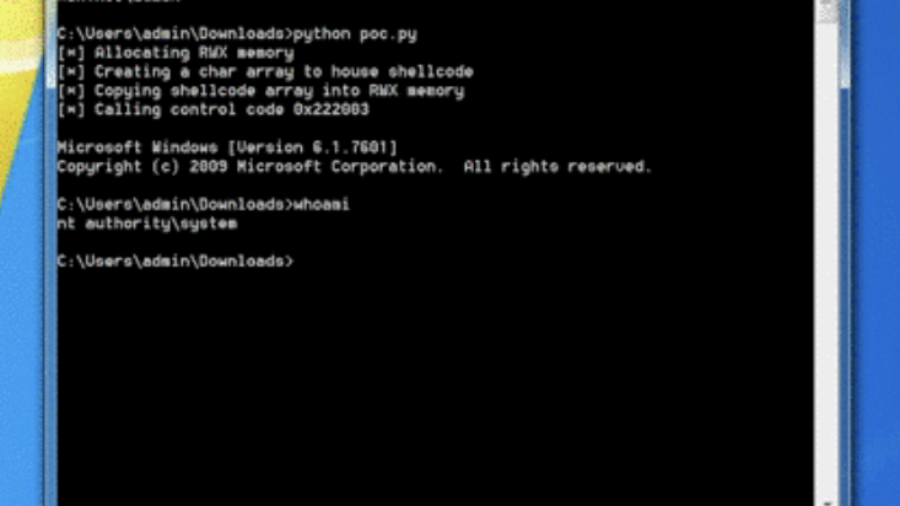
0x00 – Introduction to Windows Kernel Exploitation
The article introduces Windows kernel exploitation and explains how to build a research lab using tools like WinDbg and the HackSys Extreme Vulnerable Driver (HEVD) to study kernel vulnerabilities and exploit development.
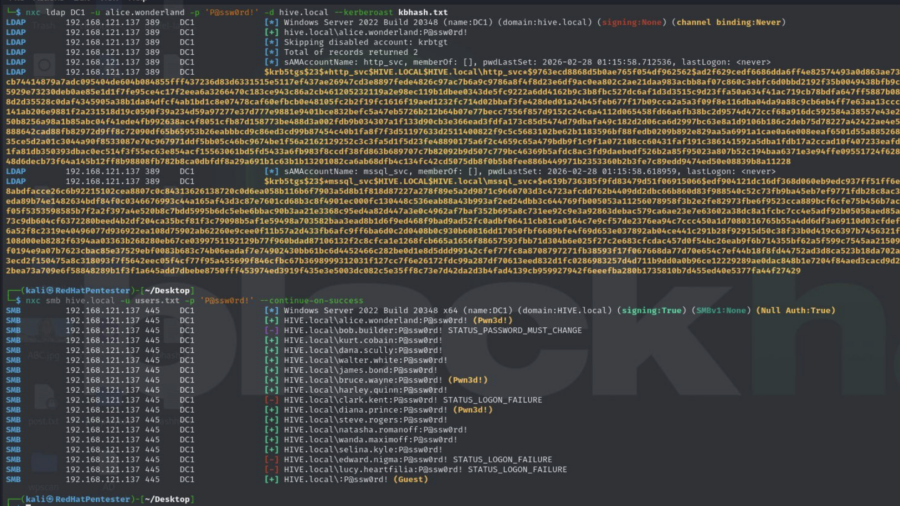
Active Directory Security Assessment: Password Spraying, Privilege Escalation, and Kerberoasting
This article analyzes an Active Directory attack chain where password spraying reveals valid credentials, privileged accounts enable escalation, and Kerberoasting exposes service account hashes, demonstrating how weak credential management can lead to full domain compromise.
RIP RegPwn: The Rise and Fall of a Windows Registry Exploitation Technique
The article explores a red-team research project called “RegPwn,” showing how weaknesses in Windows registry handling can be abused to achieve privilege escalation or persistence, and discusses why the technique has now been mitigated or rendered ineffective.
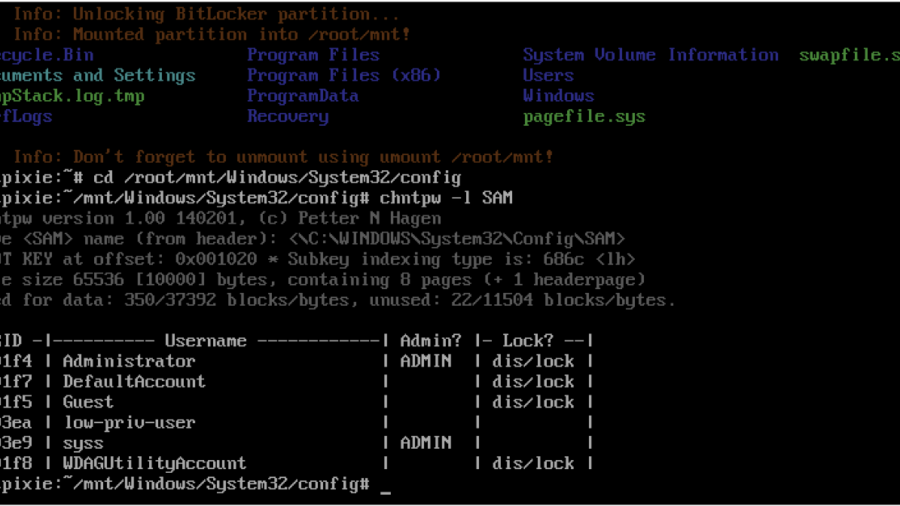
Windows Local Privilege Escalation through the bitpixie Vulnerability
The article explains the Bitpixie vulnerability in Windows Boot Manager that allows attackers to bypass BitLocker encryption. By abusing a PXE soft reboot flaw, the BitLocker key remains in memory, enabling extraction of the VMK and potential privilege escalation.