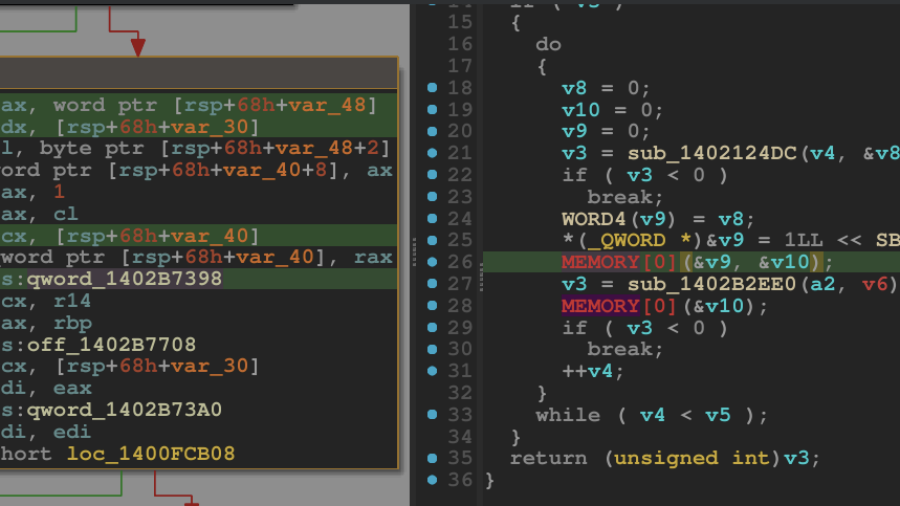
A technical walkthrough showing how to unpack a VMProtected Windows kernel driver using WinDbg and dynamic analysis. The guide demonstrates restoring the hidden Import Address Table and dumping a clean driver for reverse engineering.
Reverse Engineering the Tapo C260 and Tapo Discovery Protocol v2
The research reverse-engineers the TP-Link Tapo C260 camera firmware and analyzes Tapo Discovery Protocol v2. By dumping and decrypting the filesystem, the author reconstructs protocol logic and maps the device’s network attack surface.