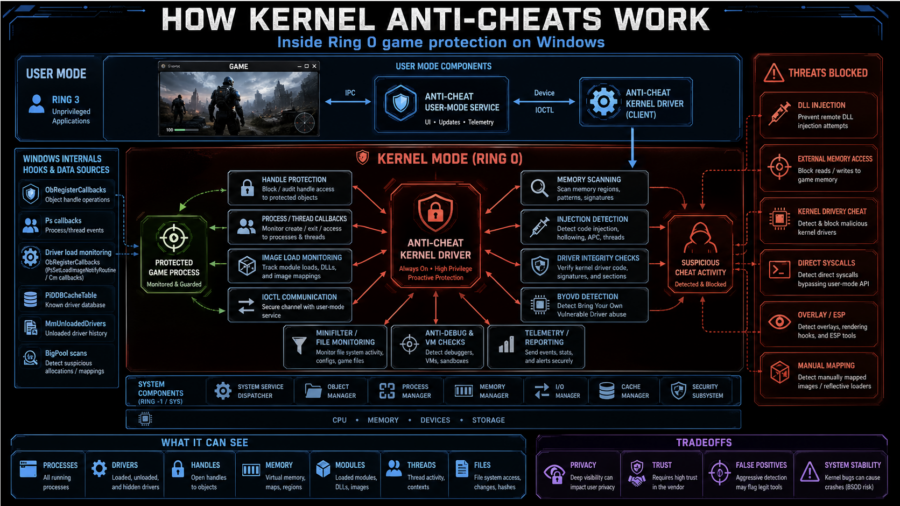
The article explains how kernel anti-cheats monitor games from Ring 0 using callbacks, handle filtering, memory scans, driver checks, anti-debugging, VM detection, and hardware fingerprinting.
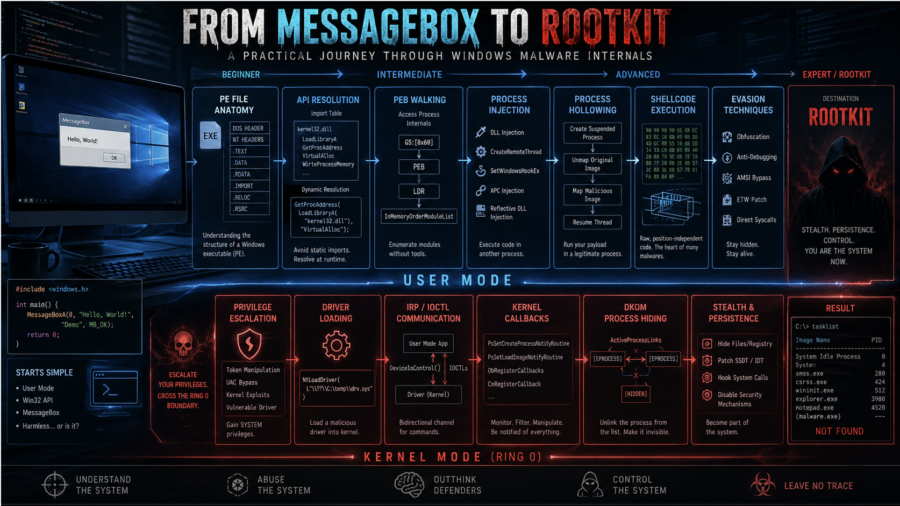
From MessageBox to Rootkit: A Practical Journey Through Windows Malware Internals
The article walks through Windows malware development from dynamic API resolution and PEB walking to injection, APC execution, driver basics, DKOM process hiding, and kernel callback abuse.
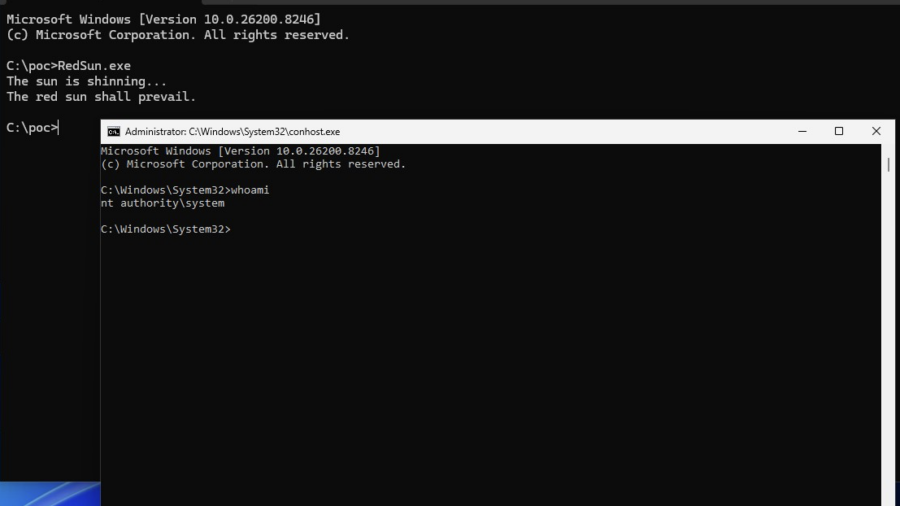
Vulnerability: When Microsoft Defender Becomes the Primitive – RedSun PoC.
This vulnerability shows how Windows Defender file handling can be abused through filesystem races, Cloud Files APIs, and reparse points to redirect privileged writes and escalate from a low-privileged user to SYSTEM.
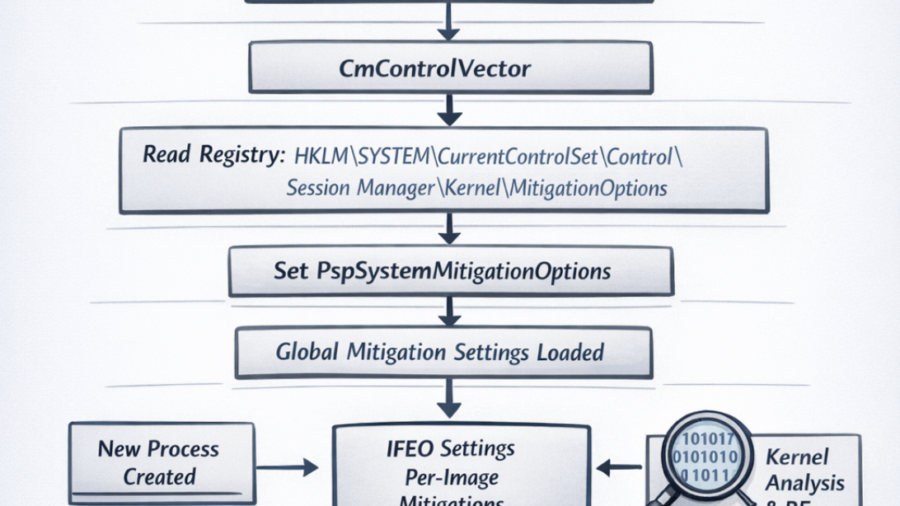
Windows Early Boot Configuration: The CmControlVector and PspSystemMitigationOptions
The article explores how Windows loads system-wide exploit mitigation settings during early boot via CmControlVector, populating PspSystemMitigationOptions, which later influences process security flags and mitigation behavior.
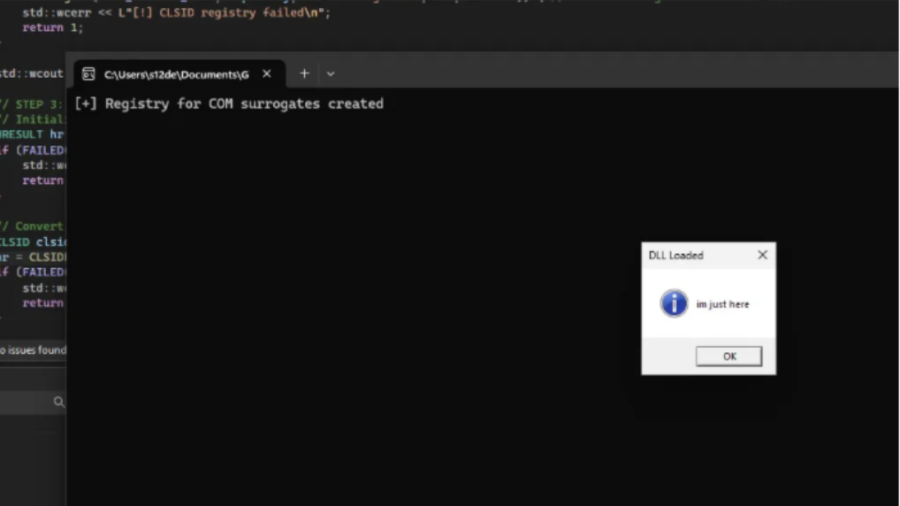
COMouflage: Stealthy DLL Surrogate Injection for Process Tree Evasion
COMouflage is a stealthy Windows injection technique that abuses COM DLL Surrogates to execute malicious DLLs inside dllhost.exe, making svchost.exe appear as the parent process and hiding the attacker’s process from detection.
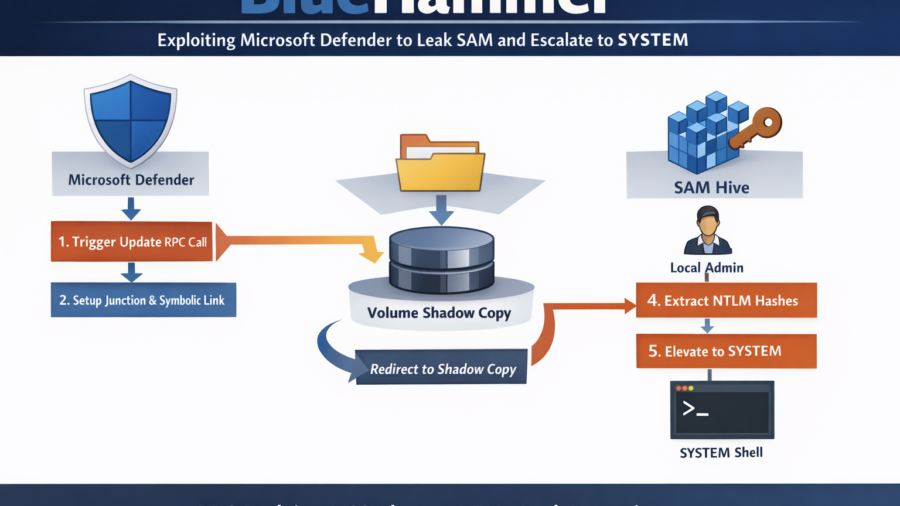
BlueHammer: Exploiting Microsoft Defender Update Workflow to Leak SAM and Escalate to SYSTEM
BlueHammer shows how Microsoft Defender’s update workflow can be abused to redirect privileged file access to a Volume Shadow Copy. By exploiting filesystem races and NT namespace tricks, the technique leaks the SAM hive, extracts NTLM hashes, and enables privilege escalation to SYSTEM.
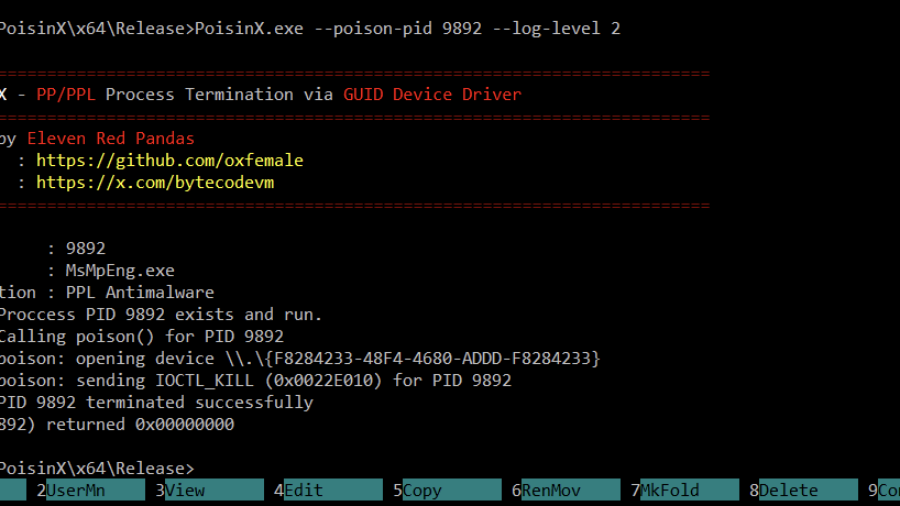
PoisonX: Terminating Protected Windows Processes via BYOVD
PoisonX is a Bring Your Own Vulnerable Driver (BYOVD) research tool that leverages a signed Microsoft kernel driver to terminate any Windows process — including PP (Protected Processes) and PPL (Protected Process Light) processes such as EDR/AV services.
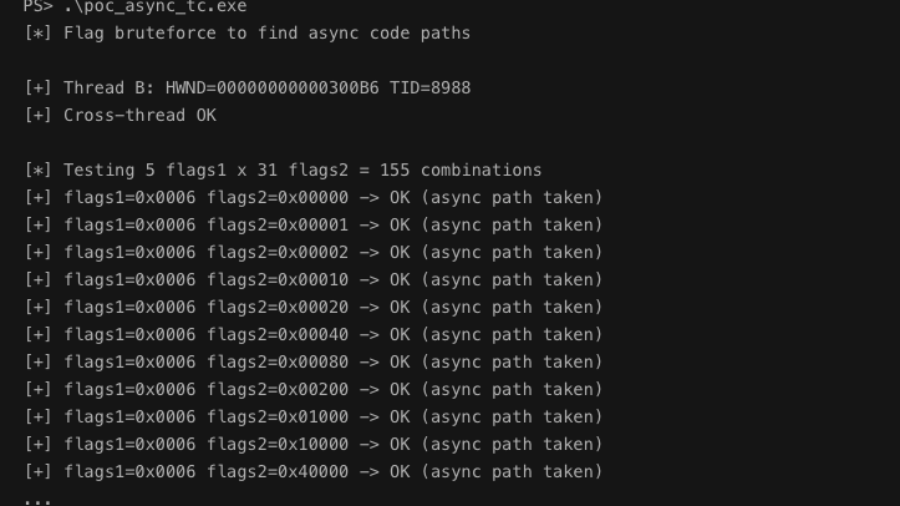
Async Windows Gone Wrong: Exploiting a Win32k Type Confusion Bug
The article analyzes a Win32k type confusion vulnerability in the async window action path of win32kfull.sys. Improper handling of window objects can corrupt kernel structures and potentially enable local privilege escalation.
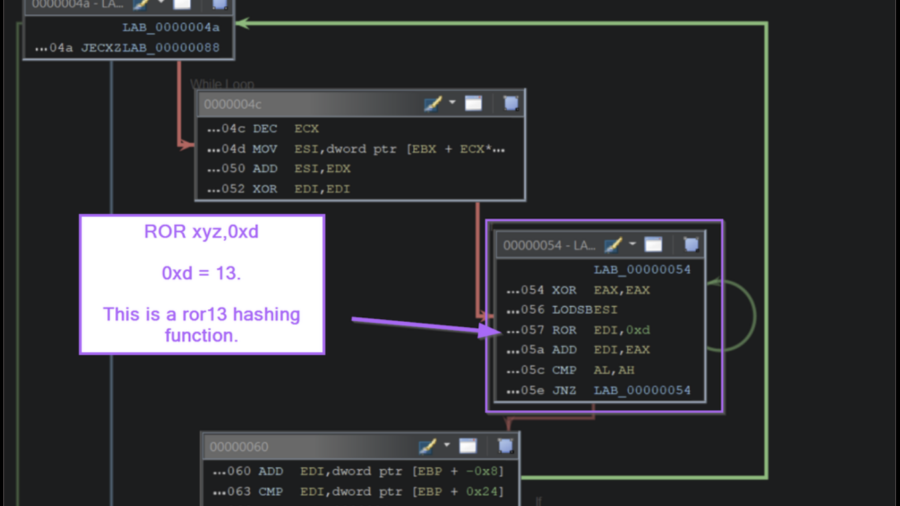
Inside the Payload: Manual Shellcode Analysis with Ghidra
The article demonstrates how to analyze Windows shellcode in Ghidra by identifying API-hashing routines, resolving hidden Windows API calls, and extracting C2 infrastructure without relying on automated emulation tools.
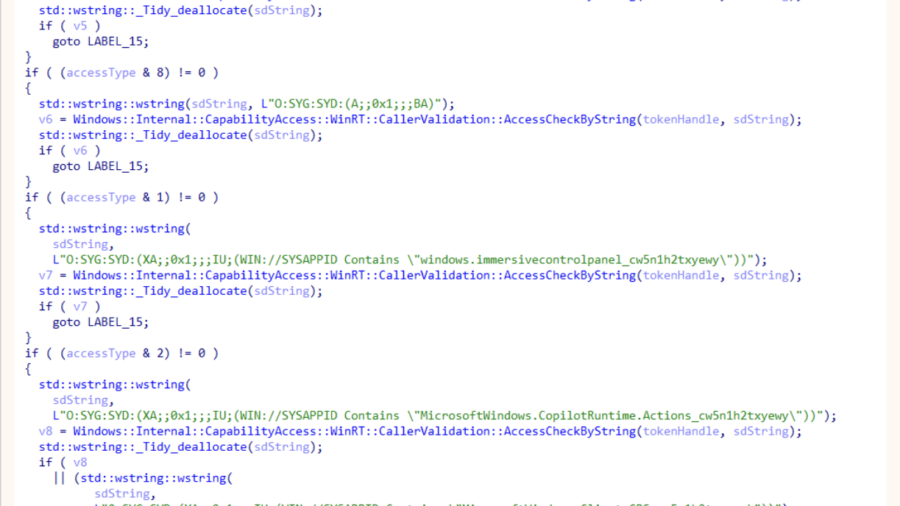
ODR: Internals of Microsoft’s New Native MCP Registration
The article explains Microsoft’s ODR mechanism for native MCP registration, enabling AI agents to discover and invoke system tools through the Model Context Protocol, preparing Windows for secure agent-driven workflows and integrations.