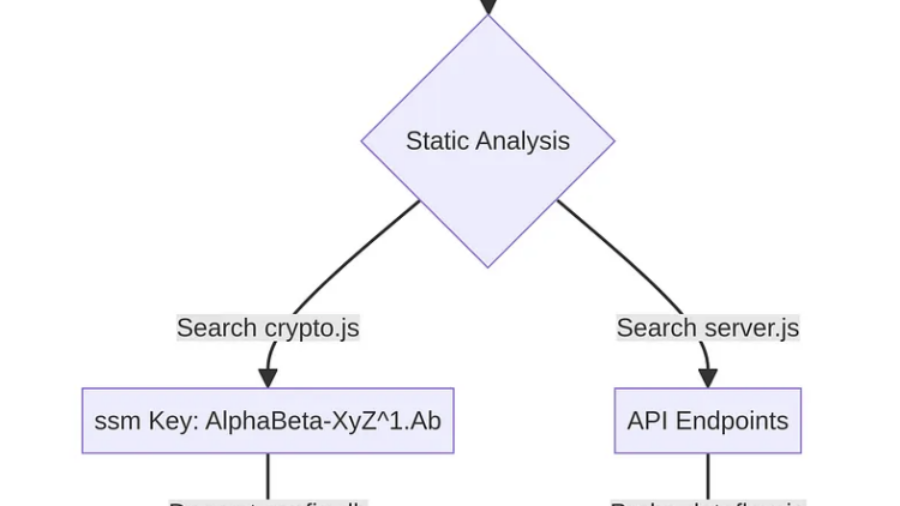
The article shows how APK decompilation with Jadx exposed Cordova JavaScript code, hardcoded database keys, CryptoJS-derived secrets, backend endpoints, and a critical LFI flaw.
Jenny was a Friend of Mine – MCPs and Friends
The article shows how Claude Code plus MCP can automate vulnerability hunting with RE, fuzzing, RAG, bounty scoring, and strict validation gates to reduce LLM hallucinations and confirm real bugs.
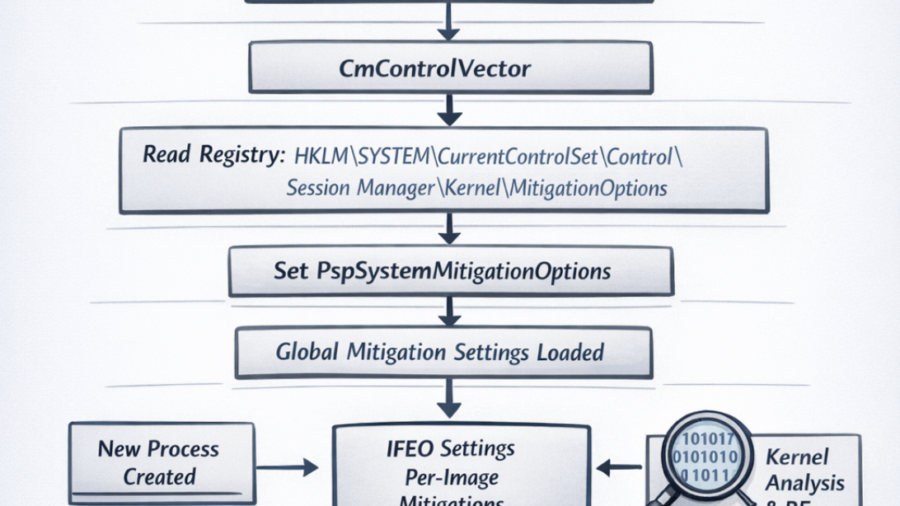
Windows Early Boot Configuration: The CmControlVector and PspSystemMitigationOptions
The article explores how Windows loads system-wide exploit mitigation settings during early boot via CmControlVector, populating PspSystemMitigationOptions, which later influences process security flags and mitigation behavior.
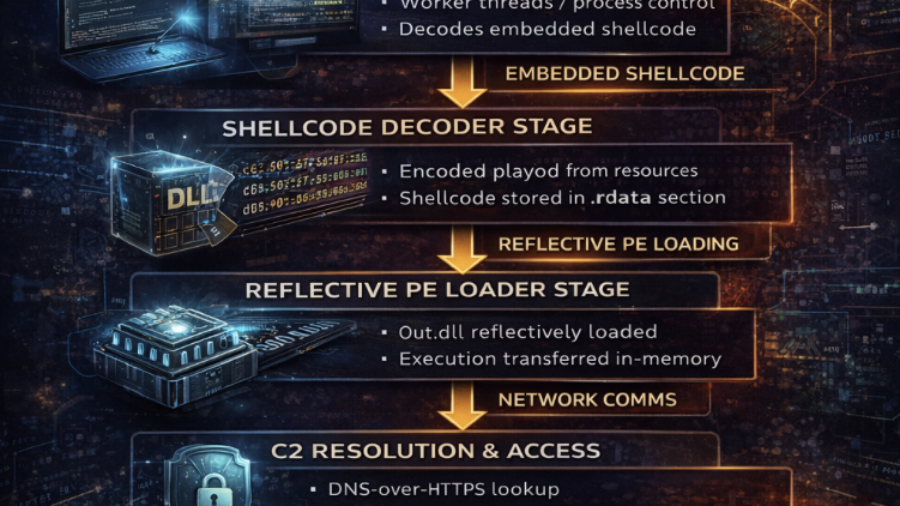
Inside the Trojanized CPU-Z Campaign: DLL Sideloading, Zig Malware, and Multi-Layer Persistence
A trojanized CPU-Z package installs malware through CRYPTBASE.dll sideloading. The Zig-compiled DLL decodes an embedded payload, loads a reflective backdoor, connects to C2, and establishes persistence using PowerShell, COM hijacking, and scheduled tasks.
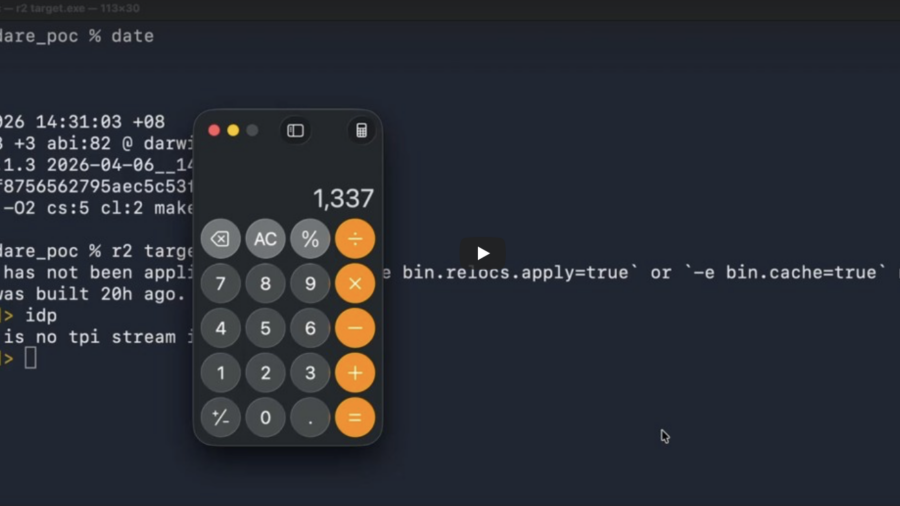
AI vs Reverse Engineering: How Claude Helped Find a radare2 0-Day
Researchers used Claude AI to discover a command-injection 0-day in radare2. A crafted PDB symbol name allowed arbitrary command execution when a binary was analyzed, showing the power of AI-assisted vulnerability discovery.
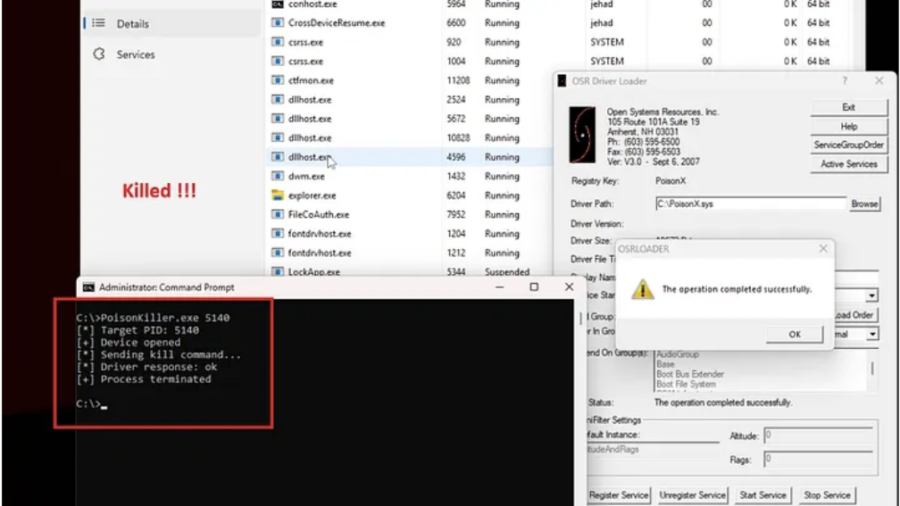
Signed to Kill: Reverse Engineering a 0-Day Used to Disable CrowdStrike EDR
The article analyzes a Microsoft-signed vulnerable driver used in a BYOVD attack to kill security processes. By sending crafted IOCTL requests with a target PID, attackers can terminate EDR services such as CrowdStrike Falcon.
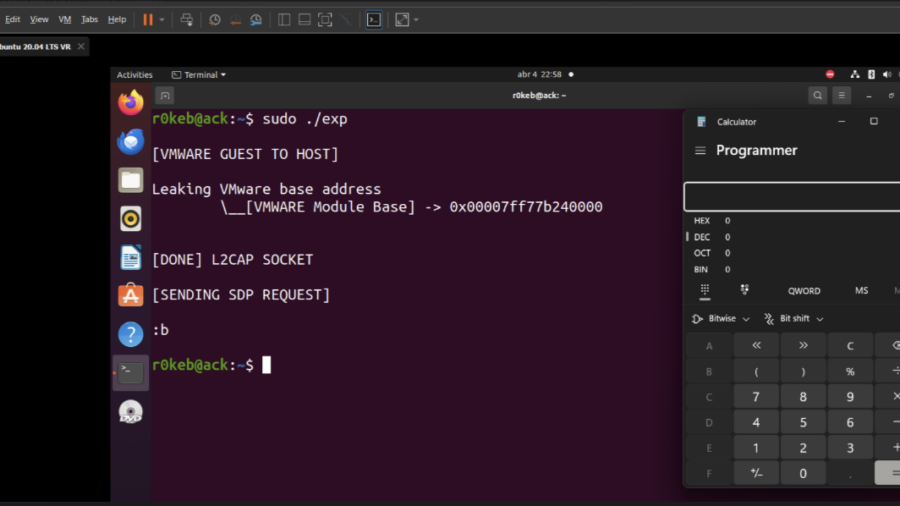
Escaping the VM: From Guest Code to Host Compromise in VMware Workstation
The article explains how vulnerabilities in VMware Workstation can enable a guest-to-host escape, allowing malicious code running inside a VM to exploit virtual device bugs and execute code on the host system.
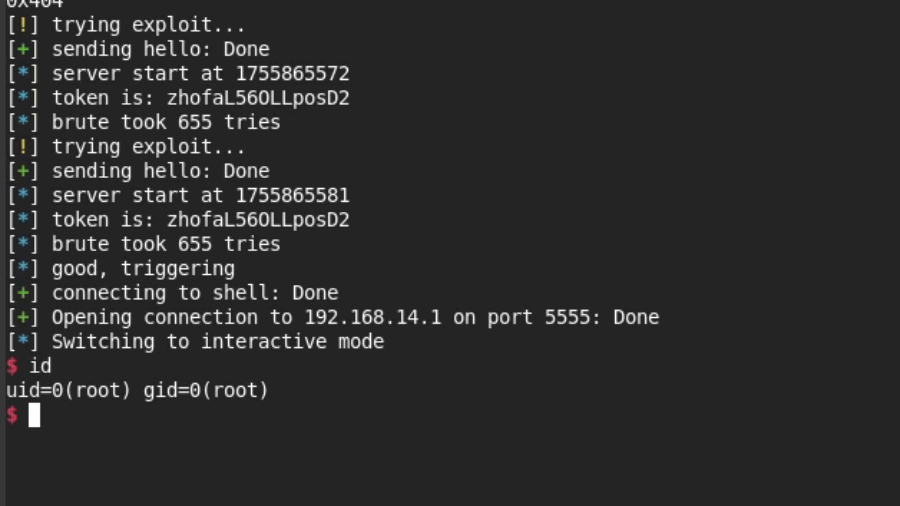
Now You See mi: Hacking the Xiaomi C400 Camera
Researchers exploited weaknesses in Xiaomi’s miIO protocol to bypass authentication, predict cryptographic values, and trigger memory corruption, ultimately achieving remote code execution and a cloud-independent jailbreak on a Xiaomi C400 camera.
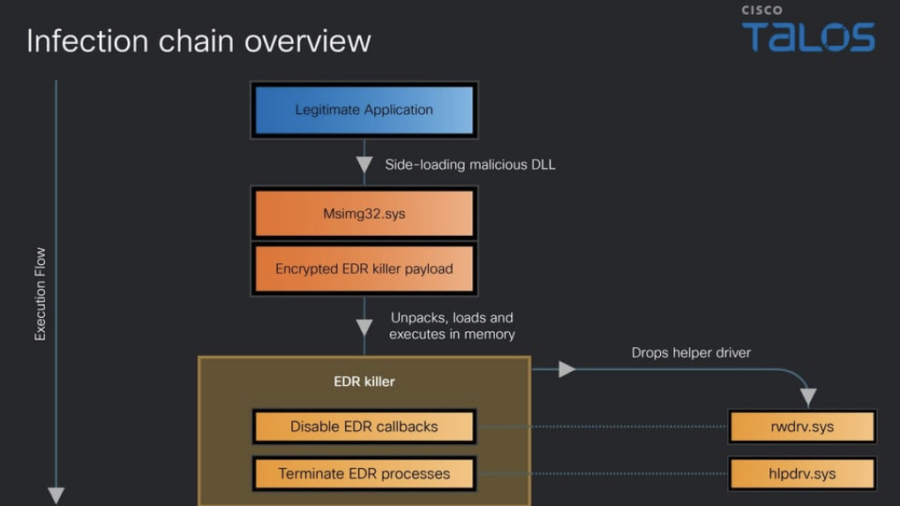
Blinding the Defenders: Inside Qilin’s EDR-Killer Malware
Cisco Talos analyzes a Qilin ransomware EDR-killer that disables over 300 security drivers. The multi-stage malware uses obfuscation and kernel-level techniques to bypass endpoint defenses and hide attacker activity.
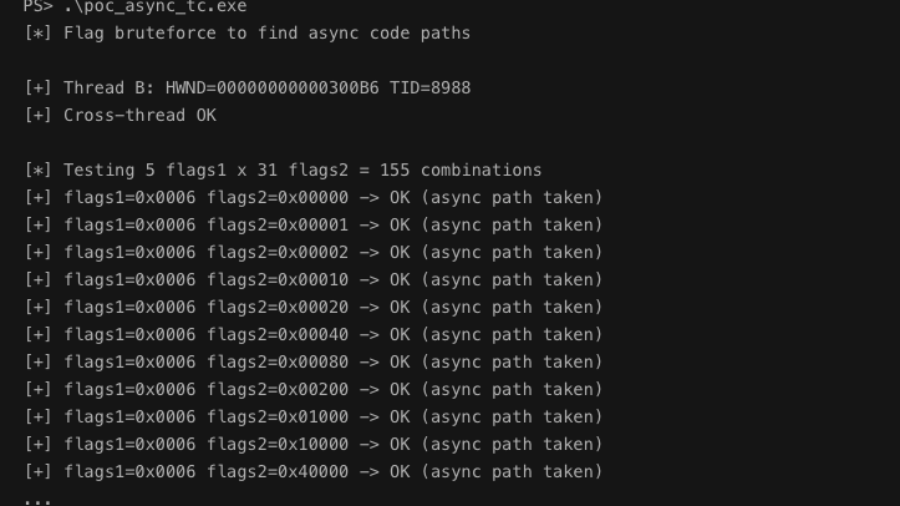
Async Windows Gone Wrong: Exploiting a Win32k Type Confusion Bug
The article analyzes a Win32k type confusion vulnerability in the async window action path of win32kfull.sys. Improper handling of window objects can corrupt kernel structures and potentially enable local privilege escalation.