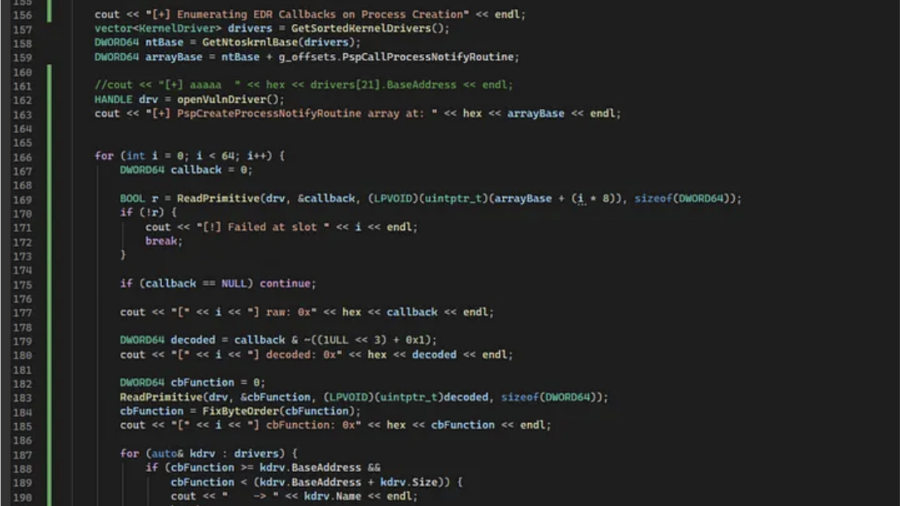
The article shows how to enumerate Windows process creation callbacks by reading PspCreateProcessNotifyRoutine from kernel memory using a BYOVD read primitive and mapping callbacks to drivers.
EDR/XDR Bypass and Detection Evasion Techniques: An Investigation of Advanced Evasion Strategies from a Red Team Perspective
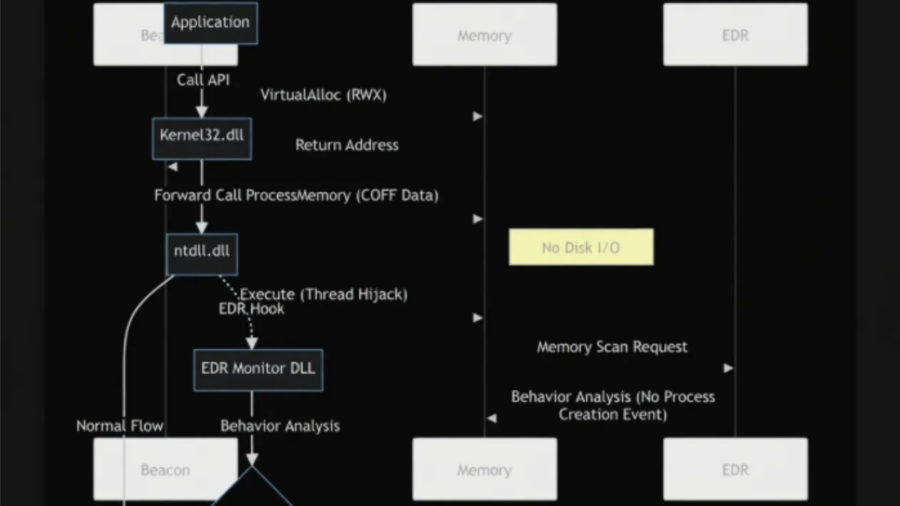
The article analyzes advanced techniques used to bypass EDR/XDR systems, showing how attackers combine evasion methods—such as indirect syscalls, ETW tampering, API unhooking, and in-memory execution—to evade detection and extend stealth during attacks.
Tutorial: Adaptix C2 with ShellcodePack and MacroPack
This tutorial shows how to weaponize Adaptix C2 agents using ShellcodePack and MacroPack, converting payloads into shellcode and packaging them in evasive loaders to improve stealth and bypass EDR during red-team operations.
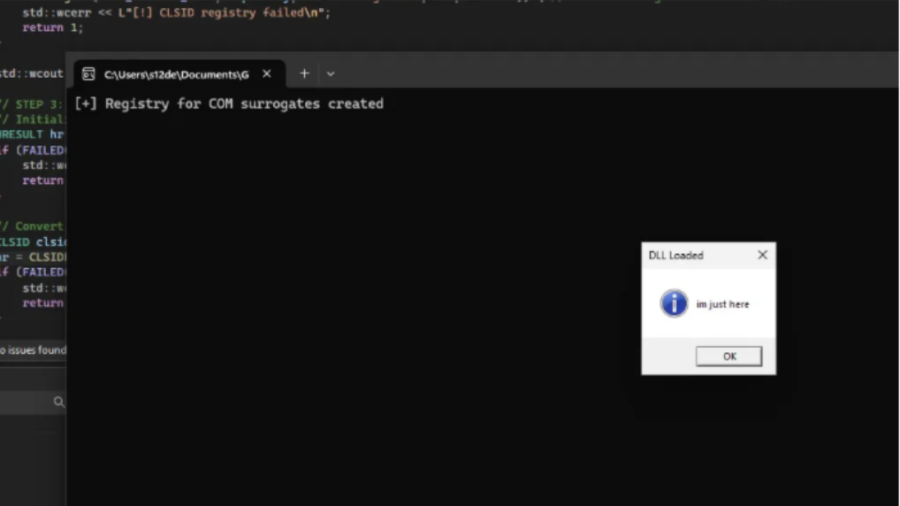
COMouflage: Stealthy DLL Surrogate Injection for Process Tree Evasion
COMouflage is a stealthy Windows injection technique that abuses COM DLL Surrogates to execute malicious DLLs inside dllhost.exe, making svchost.exe appear as the parent process and hiding the attacker’s process from detection.
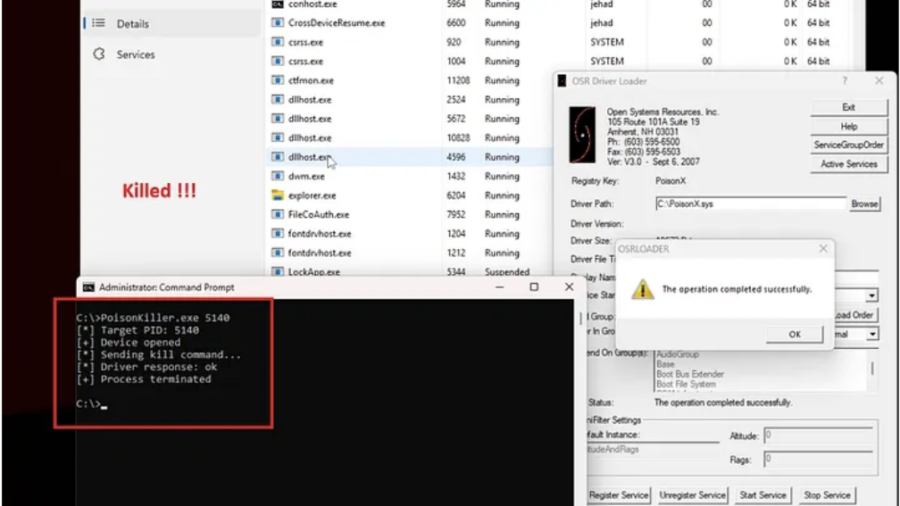
Signed to Kill: Reverse Engineering a 0-Day Used to Disable CrowdStrike EDR
The article analyzes a Microsoft-signed vulnerable driver used in a BYOVD attack to kill security processes. By sending crafted IOCTL requests with a target PID, attackers can terminate EDR services such as CrowdStrike Falcon.
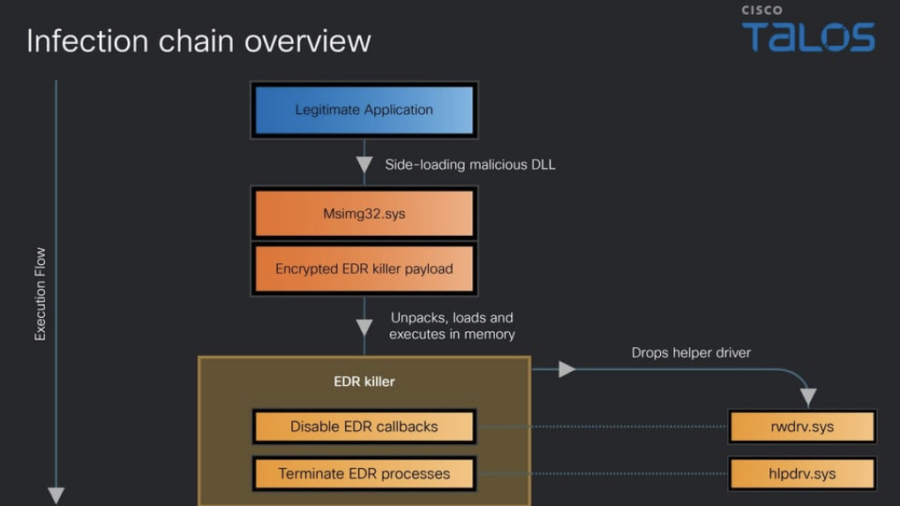
Blinding the Defenders: Inside Qilin’s EDR-Killer Malware
Cisco Talos analyzes a Qilin ransomware EDR-killer that disables over 300 security drivers. The multi-stage malware uses obfuscation and kernel-level techniques to bypass endpoint defenses and hide attacker activity.
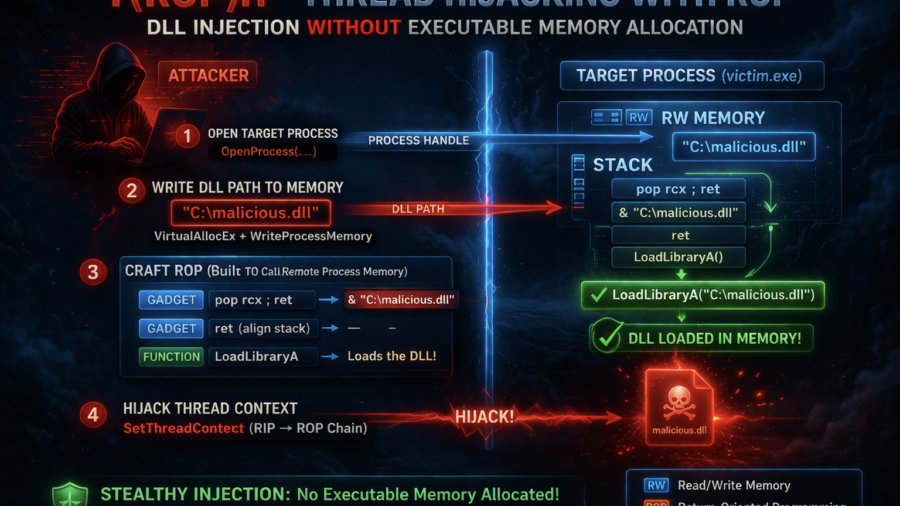
Stealth Injection with ROP: Thread Hijacking Without Executable Memory
The article presents T(ROP)H, a process injection technique that hijacks threads and uses a ROP chain to load a DLL without allocating executable memory, reducing common detection indicators used by EDR systems.
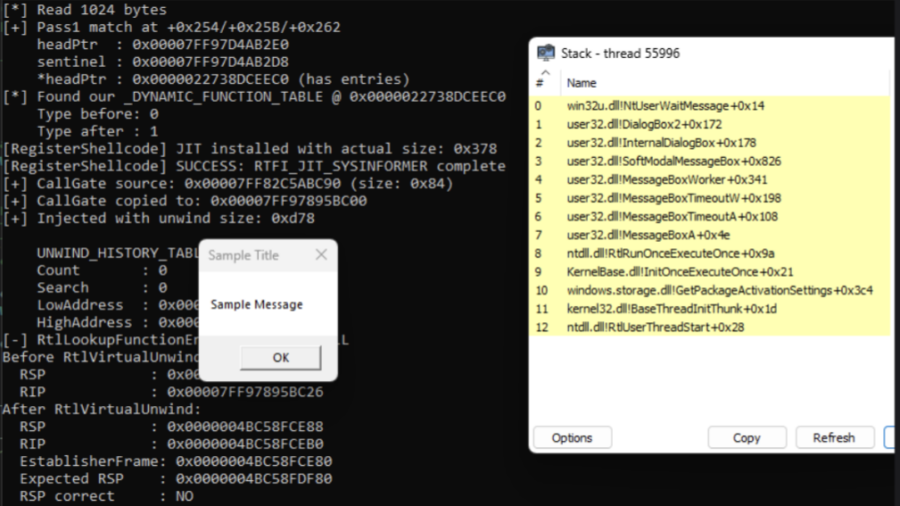
Invisible Execution: Hiding Malware with Unwind Metadata Manipulation
The article introduces BYOUD, a Windows evasion technique that manipulates unwind metadata to spoof call stacks without altering return addresses, allowing malware to bypass EDR stack inspection and appear as legitimate execution.
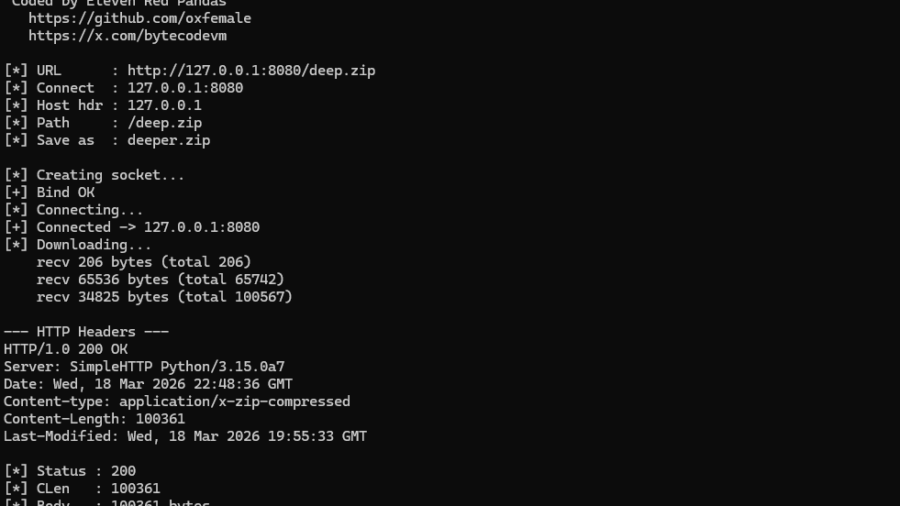
NT AFD.SYS HTTP Downloader: From First Syscall to bypass the majority of usermode EDR hooks
The article demonstrates how to bypass the Winsock layer by communicating directly with the Windows AFD driver using Native API calls. It explains how socket operations can be replicated via IOCTLs and how this reduces reliance on standard networking APIs.
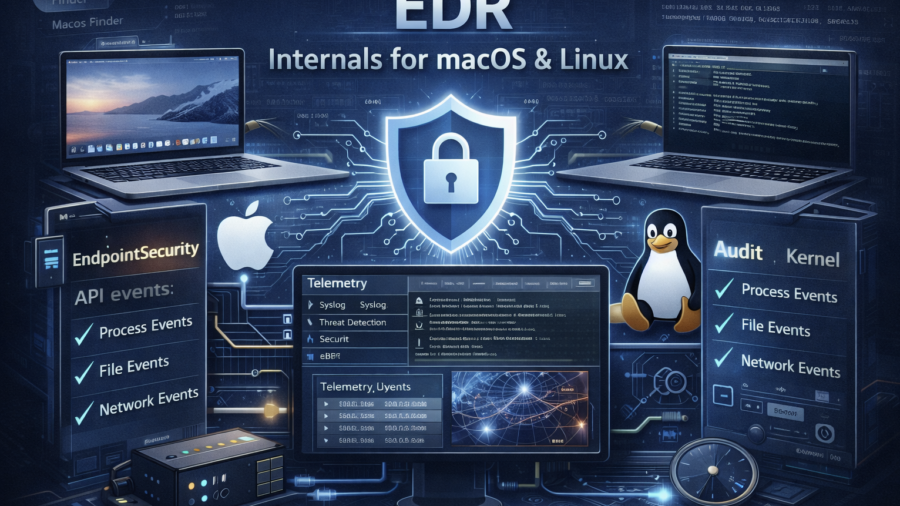
EDR Internals for macOS and Linux
The article examines how EDR agents monitor macOS and Linux systems by collecting telemetry from OS security frameworks, kernel interfaces, and tools like eBPF. Understanding these data sources reveals detection capabilities and potential blind spots.