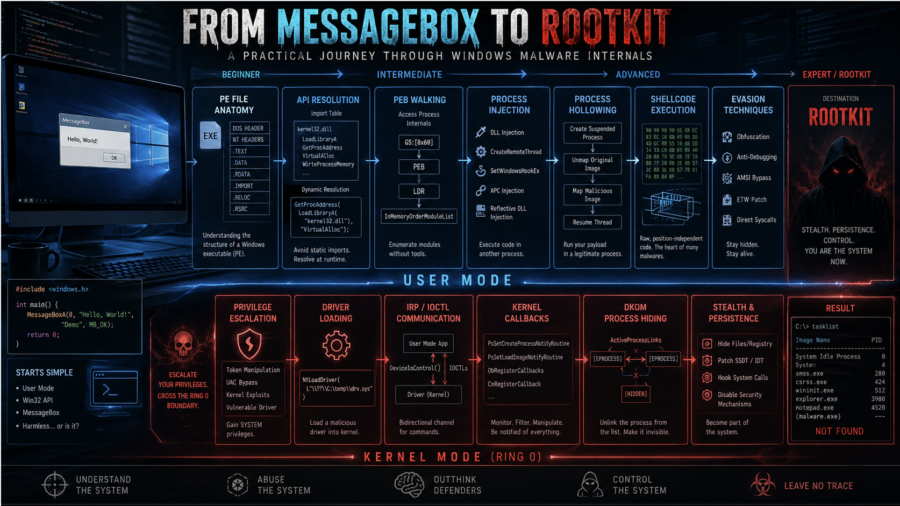
The article walks through Windows malware development from dynamic API resolution and PEB walking to injection, APC execution, driver basics, DKOM process hiding, and kernel callback abuse.
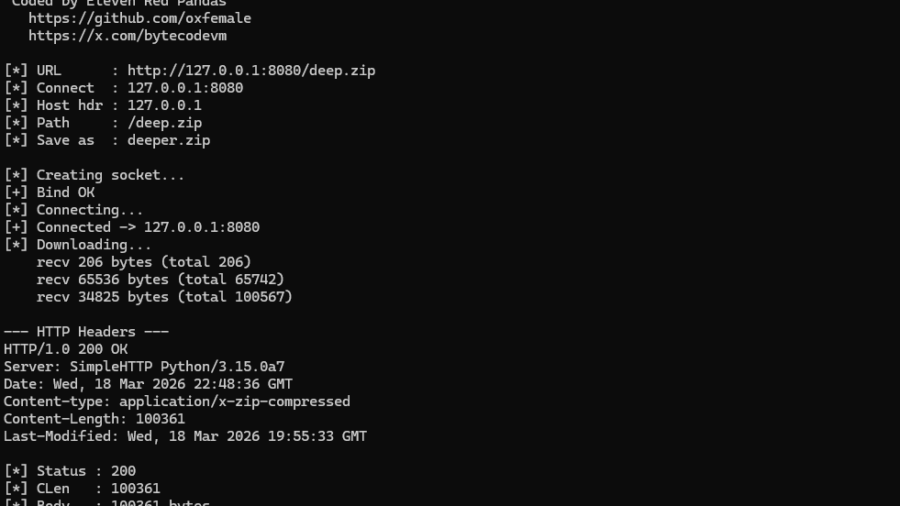
NT AFD.SYS HTTP Downloader: From First Syscall to bypass the majority of usermode EDR hooks
The article demonstrates how to bypass the Winsock layer by communicating directly with the Windows AFD driver using Native API calls. It explains how socket operations can be replicated via IOCTLs and how this reduces reliance on standard networking APIs.
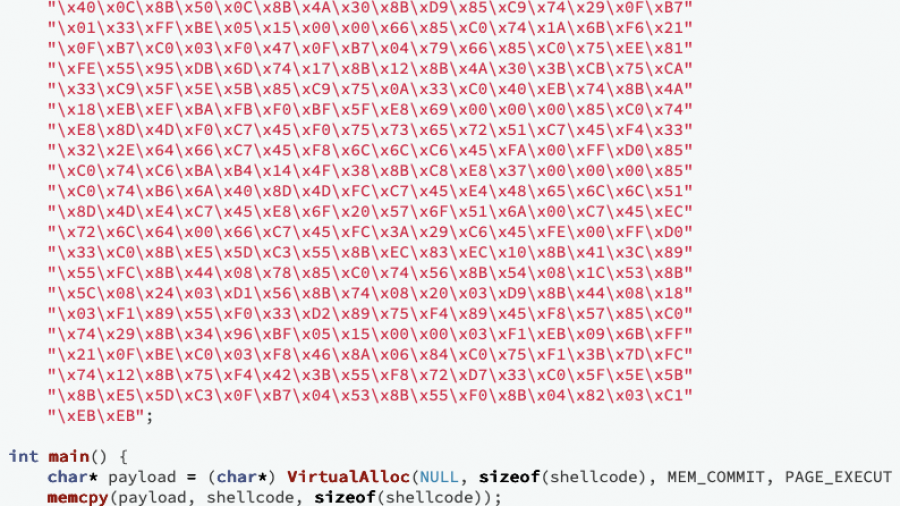
Writing Optimized Windows Shellcode (old but gold)
A deep dive into crafting ultra-compact Windows shellcode that walks the PEB, resolves APIs via export hashing, and runs fully self-contained without imports — showing how C can build stealthy, position-independent payloads.