The article shows how Claude Code plus MCP can automate vulnerability hunting with RE, fuzzing, RAG, bounty scoring, and strict validation gates to reduce LLM hallucinations and confirm real bugs.
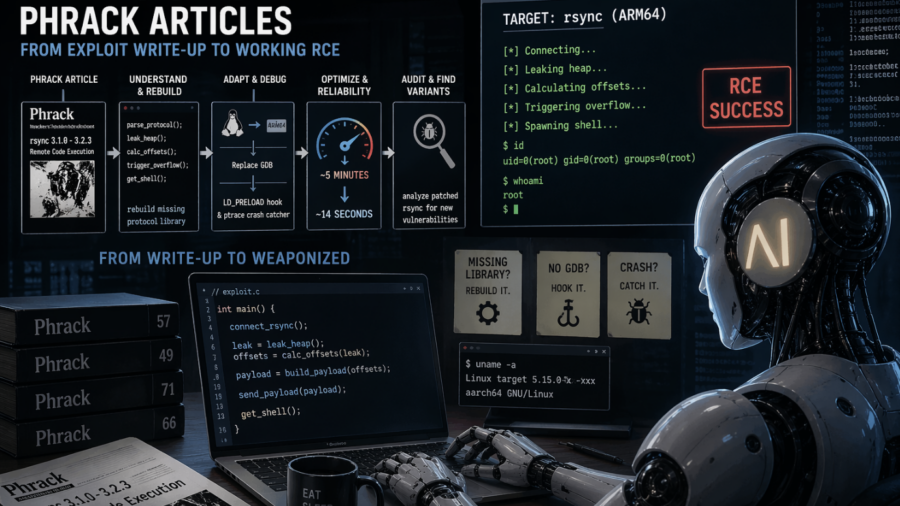
MAD Bugs: Feeding Claude Phrack Articles for Fun and Profit
The article shows Claude turning a Phrack rsync exploit write-up into a faster working ARM64 RCE, rebuilding missing pieces, debugging without GDB, and even helping audit patched code for variants.
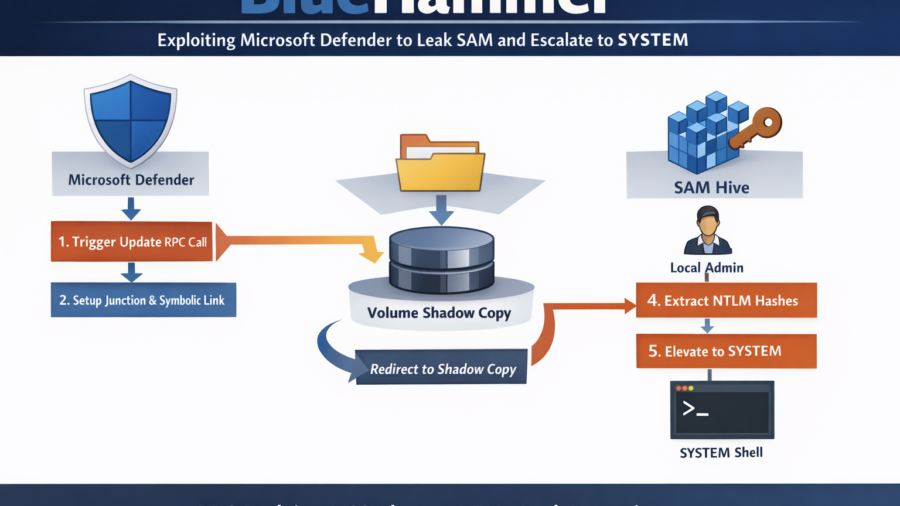
BlueHammer: Exploiting Microsoft Defender Update Workflow to Leak SAM and Escalate to SYSTEM
BlueHammer shows how Microsoft Defender’s update workflow can be abused to redirect privileged file access to a Volume Shadow Copy. By exploiting filesystem races and NT namespace tricks, the technique leaks the SAM hive, extracts NTLM hashes, and enables privilege escalation to SYSTEM.
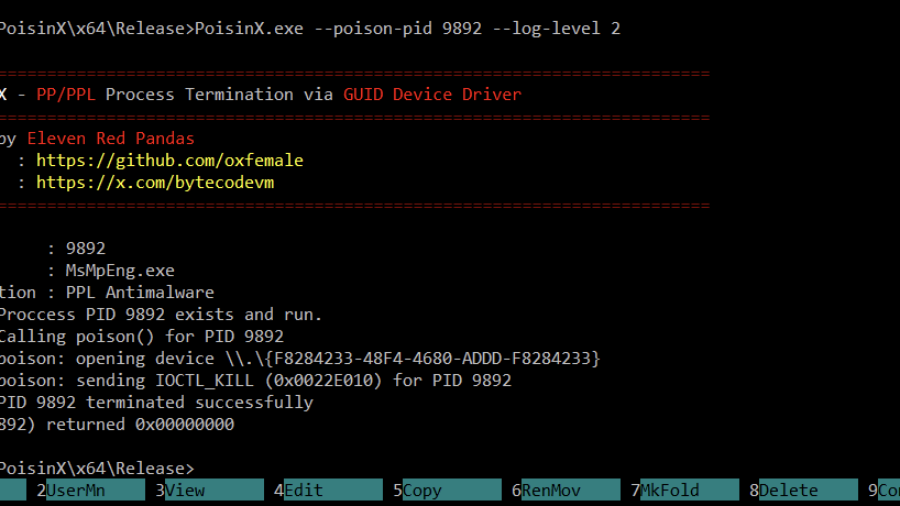
PoisonX: Terminating Protected Windows Processes via BYOVD
PoisonX is a Bring Your Own Vulnerable Driver (BYOVD) research tool that leverages a signed Microsoft kernel driver to terminate any Windows process — including PP (Protected Processes) and PPL (Protected Process Light) processes such as EDR/AV services.
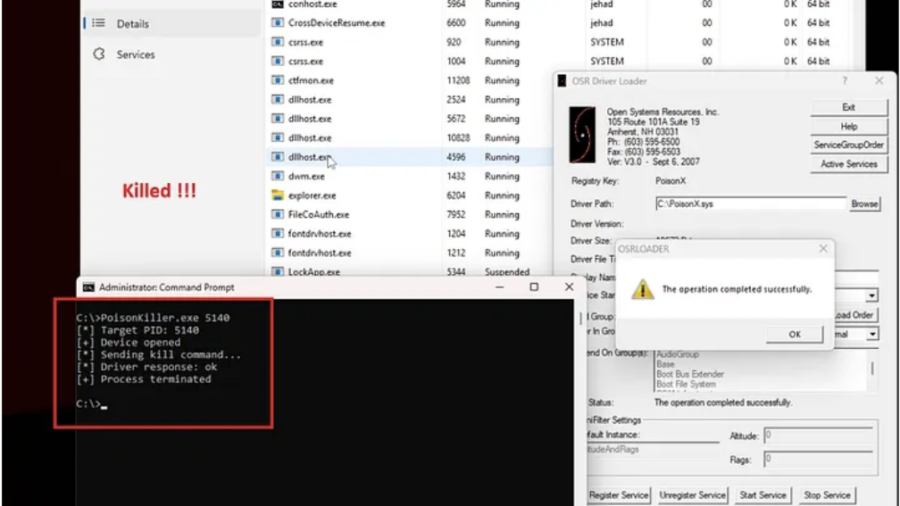
Signed to Kill: Reverse Engineering a 0-Day Used to Disable CrowdStrike EDR
The article analyzes a Microsoft-signed vulnerable driver used in a BYOVD attack to kill security processes. By sending crafted IOCTL requests with a target PID, attackers can terminate EDR services such as CrowdStrike Falcon.
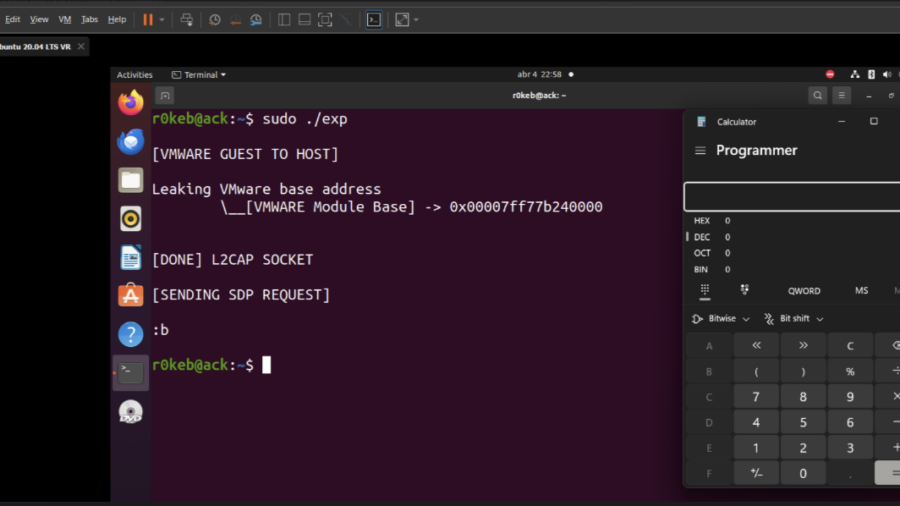
Escaping the VM: From Guest Code to Host Compromise in VMware Workstation
The article explains how vulnerabilities in VMware Workstation can enable a guest-to-host escape, allowing malicious code running inside a VM to exploit virtual device bugs and execute code on the host system.
MAD Bugs: Claude Wrote a Full FreeBSD Remote Kernel RCE with Root Shell (CVE-2026-4747)
Researchers showed that the Claude AI model could generate a working exploit for a FreeBSD kernel vulnerability (CVE-2026-4747), producing a remote root shell by building a stack overflow and ROP chain with minimal human guidance.
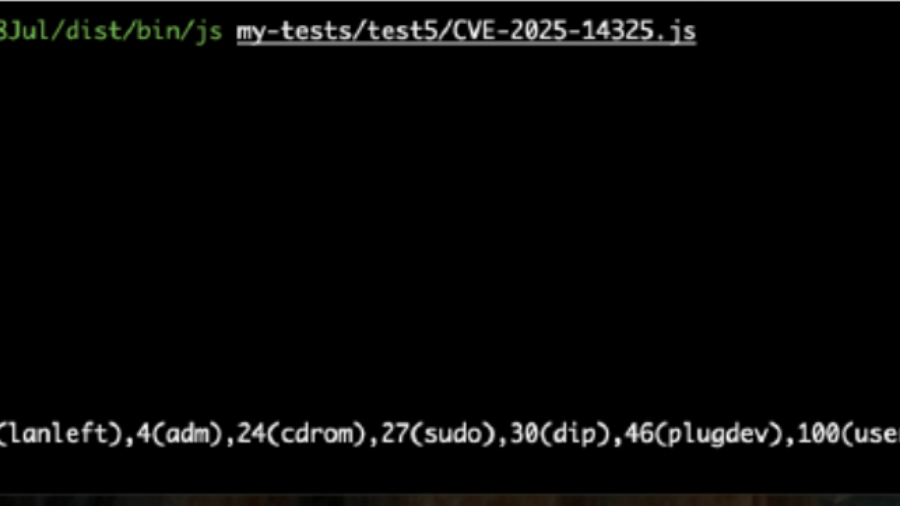
Breaking the JIT: Exploiting a SpiderMonkey Type Confusion Bug
The article analyzes CVE-2025-14325, a SpiderMonkey Baseline JIT bug causing type confusion in inline caches. Incorrect assumptions about object shapes can lead to memory corruption and possible code execution in Firefox.
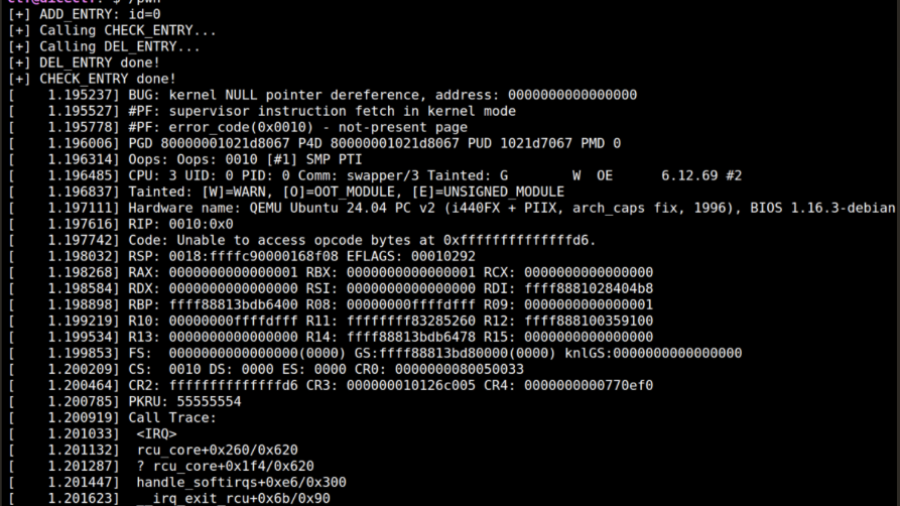
From RCU Double Free to Root: Exploiting a Linux Kernel Race in cornelslop
A DiceCTF write-up showing how an RCU double-free race in a Linux kernel module can be turned into a cross-cache exploit by manipulating SLUB allocator behavior and overlapping page-table entries.
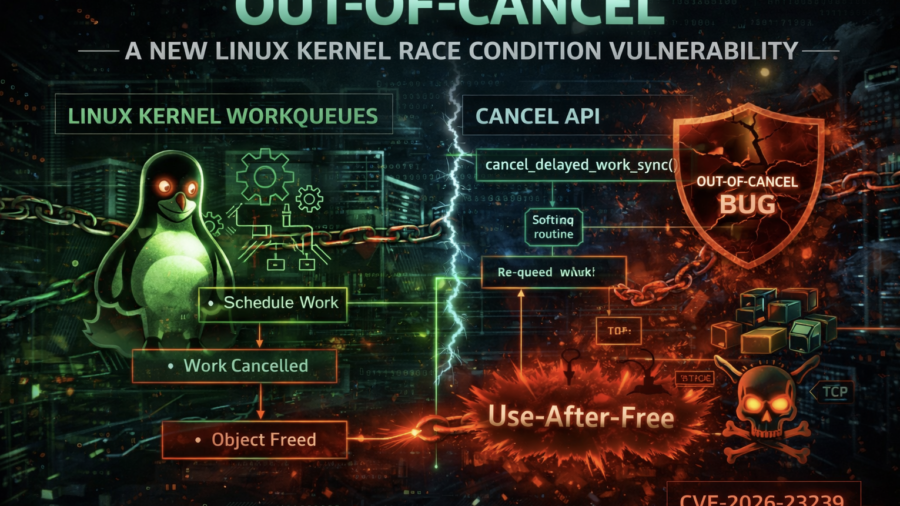
Out-of-Cancel: A New Linux Kernel Race Condition Bug Class
The article introduces the Out-of-Cancel vulnerability class in the Linux kernel, where workqueue cancellation APIs fail to guarantee object lifetime. This race can lead to Use-After-Free bugs, demonstrated using espintcp (CVE-2026-23239).