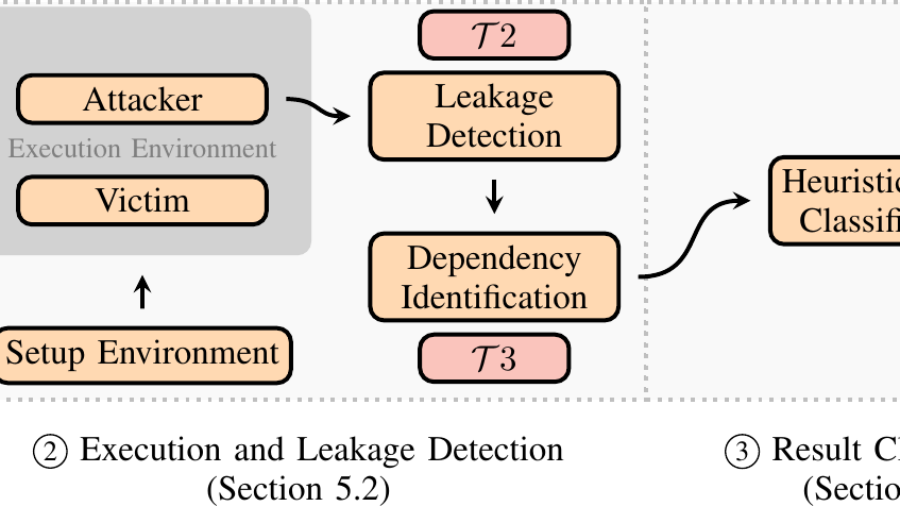
TREVEX is a post-silicon black-box CPU fuzzer from CISPA designed to discover data-flow transient execution vulnerabilities without needing RTL access, an ISA emulator, or a leakage contract. The framework runs across 20 microarchitectures from Intel, AMD, and Zhaoxin and uncovers a new TEA — Floating Point Divider State Sampling (FP-DSS, CVE-2025-54505) — on AMD Zen and Zen+, a new FPVI variant on AMD that does not need denormal inputs, three instances of Zero-at-ret on Intel, and FPVI on Zhaoxin. The authors weaponise FP-DSS from native code, the Linux kernel, and a Chrome JavaScript exploit.
{“_yoast_wpseo_title”: “TREVEX: Black-Box CPU Fuzzer Finds FP-DSS (CVE-2025-54505)”, “_yoast_wpseo_metadesc”: “TREVEX black-box CPU fuzzer (CISPA, S&P 2026) finds FP-DSS (CVE-2025-54505), new FPVI variants, and Zero-at-ret across 20 Intel, AMD, Zhaoxin microarchitectures.”, “rank_math_title”: “TREVEX: Black-Box CPU Fuzzer Finds FP-DSS (CVE-2025-54505)”, “rank_math_description”: “TREVEX black-box CPU fuzzer (CISPA, S&P 2026) finds FP-DSS (CVE-2025-54505), new FPVI variants, and Zero-at-ret across 20 Intel, AMD, Zhaoxin microarchitectures.”}
CVE-2025-54539: Apache.NMS.AMQP Deserialization Policy Bypass to Unauthenticated RCE in .NET
CVE-2025-54539 is a deserialization policy bypass in Apache.NMS.AMQP (≤ 2.3.0) that lets a single 290-byte AMQP message reach BinaryFormatter inside an unsuspecting .NET client and execute arbitrary commands.
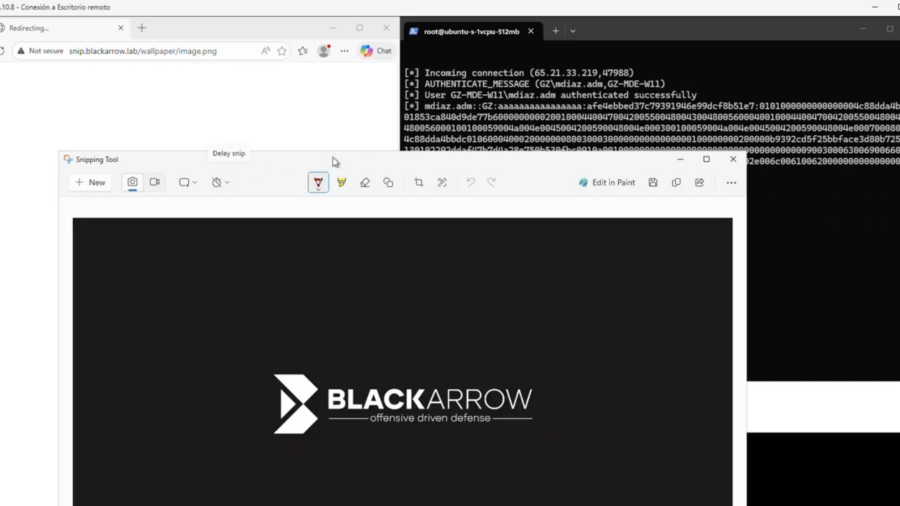
CVE-2026-33829: How a Deep Link in Windows Can Expose Net-NTLM Credentials
This vulnerability in the Windows Snipping Tool allows attackers to trigger NTLM authentication through the ms-screensketch protocol, forcing a connection to a remote SMB server and leaking the user’s Net-NTLM hash via a crafted link.
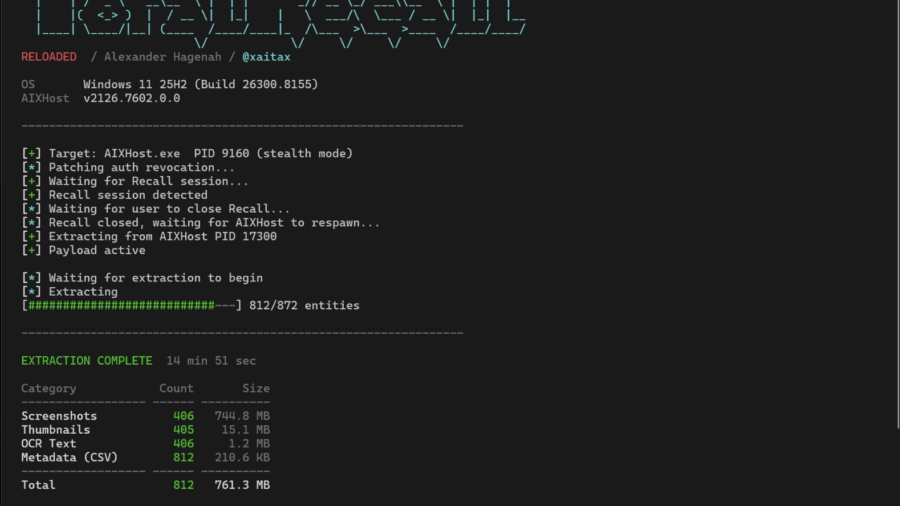
Windows Recall: A Perfect Memory or a Perfect Data Leak?
An in-depth look at Windows Recall on Copilot+ PCs, how its SQLite and embedding databases store screen history, and how the TotalRecall tool can extract that data—revealing serious security and privacy implications.
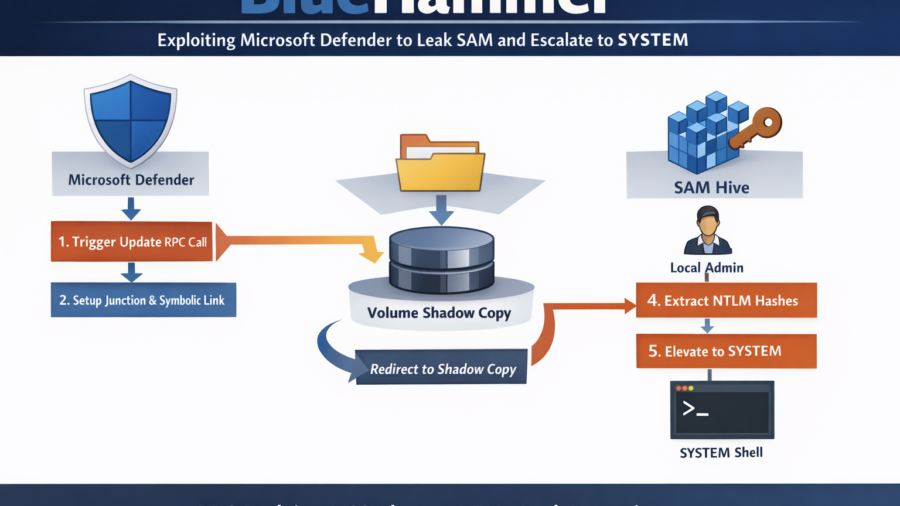
BlueHammer: Exploiting Microsoft Defender Update Workflow to Leak SAM and Escalate to SYSTEM
BlueHammer shows how Microsoft Defender’s update workflow can be abused to redirect privileged file access to a Volume Shadow Copy. By exploiting filesystem races and NT namespace tricks, the technique leaks the SAM hive, extracts NTLM hashes, and enables privilege escalation to SYSTEM.
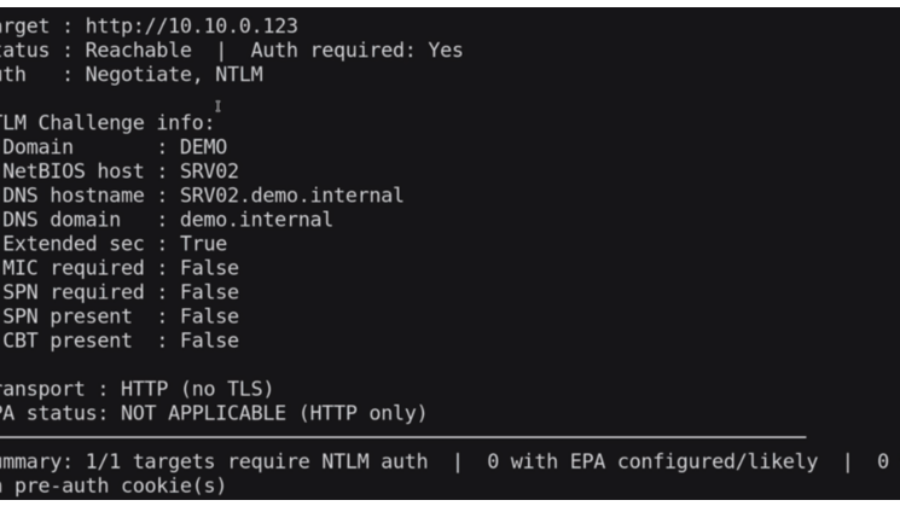
Relaying Trust: Exploiting NTLM Authentication to Compromise Active Directory
he article demonstrates an NTLM relay attack against Active Directory using tools like ntlmrelayx and PetitPotam. By relaying authentication to LDAP, attackers can create accounts, abuse delegation, and gain administrative access.
LOLExfil: Stealthy Data Exfiltration Using Living-Off-the-Land Techniques
The article introduces LOLExfil, a Living-Off-the-Land data exfiltration technique that abuses legitimate system tools and trusted services to stealthily extract data, blending malicious activity with normal system behavior.
Ghost in the PPL – LSASS Memory Dump
The article explains a technique for dumping memory from the protected LSASS process (PPL). It analyzes limitations of PPL protection and demonstrates how MiniDumpWriteDump and existing process handles can be used to extract credential data.
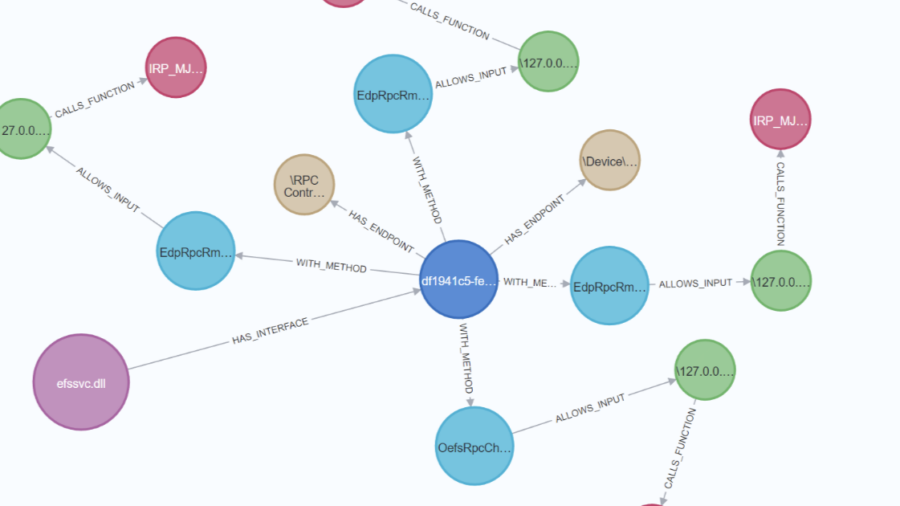
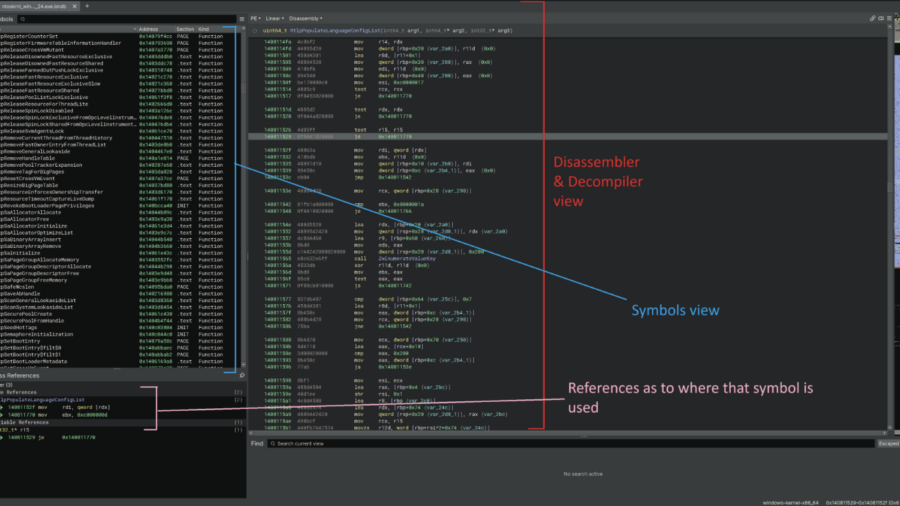
Reverse engineering undocumented Windows Kernel features to work with the EDR
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.