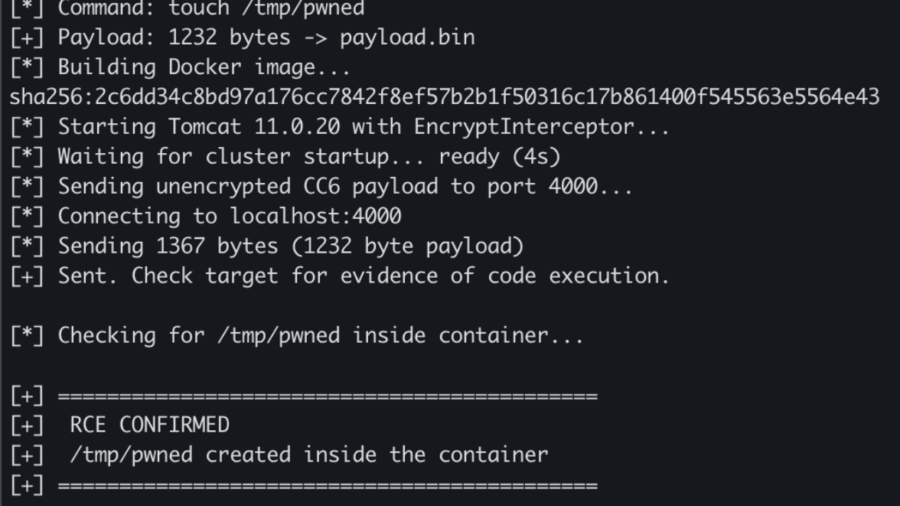
A flaw in Apache Tomcat Tribes clustering allows attackers to send crafted cluster messages that bypass authentication and trigger unsafe deserialization, leading to unauthenticated remote code execution on exposed servers.
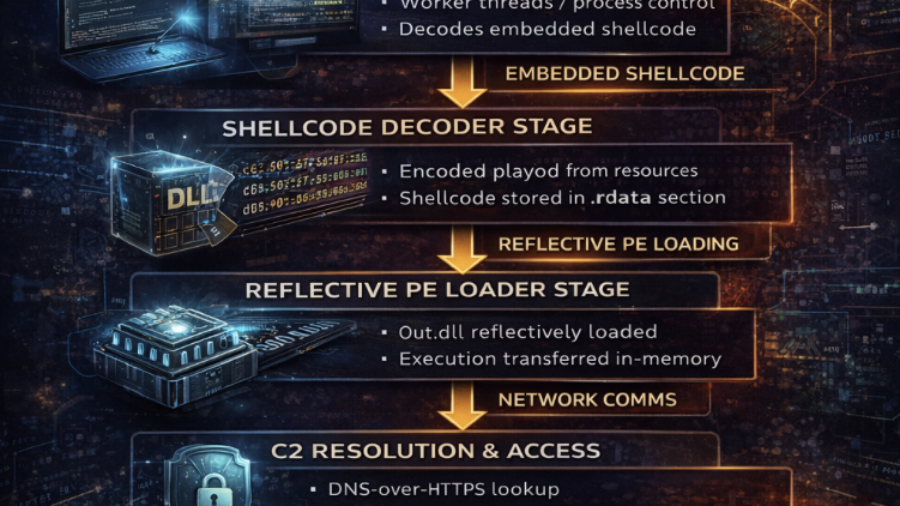
Inside the Trojanized CPU-Z Campaign: DLL Sideloading, Zig Malware, and Multi-Layer Persistence
A trojanized CPU-Z package installs malware through CRYPTBASE.dll sideloading. The Zig-compiled DLL decodes an embedded payload, loads a reflective backdoor, connects to C2, and establishes persistence using PowerShell, COM hijacking, and scheduled tasks.
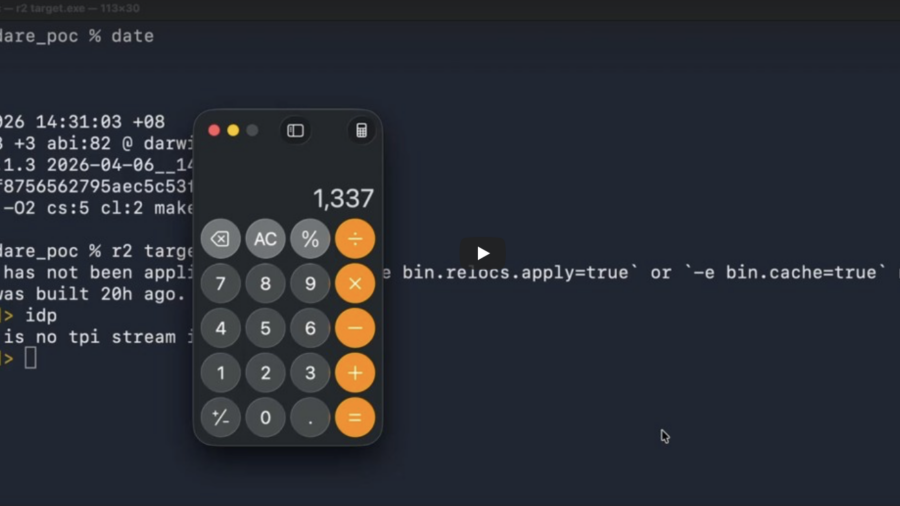
AI vs Reverse Engineering: How Claude Helped Find a radare2 0-Day
Researchers used Claude AI to discover a command-injection 0-day in radare2. A crafted PDB symbol name allowed arbitrary command execution when a binary was analyzed, showing the power of AI-assisted vulnerability discovery.
BullFrog DNS Pipelining: Smuggling Data Past CI/CD Egress Filters
A parsing flaw in BullFrog’s DNS-over-TCP handling allows attackers to bypass CI/CD egress filtering by pipelining DNS queries. The filter validates only the first query, letting malicious queries slip through.
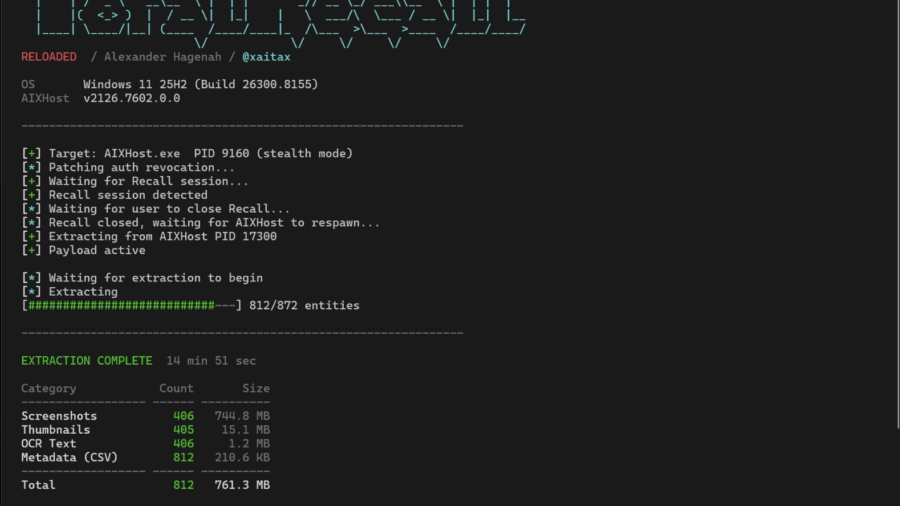
Windows Recall: A Perfect Memory or a Perfect Data Leak?
An in-depth look at Windows Recall on Copilot+ PCs, how its SQLite and embedding databases store screen history, and how the TotalRecall tool can extract that data—revealing serious security and privacy implications.
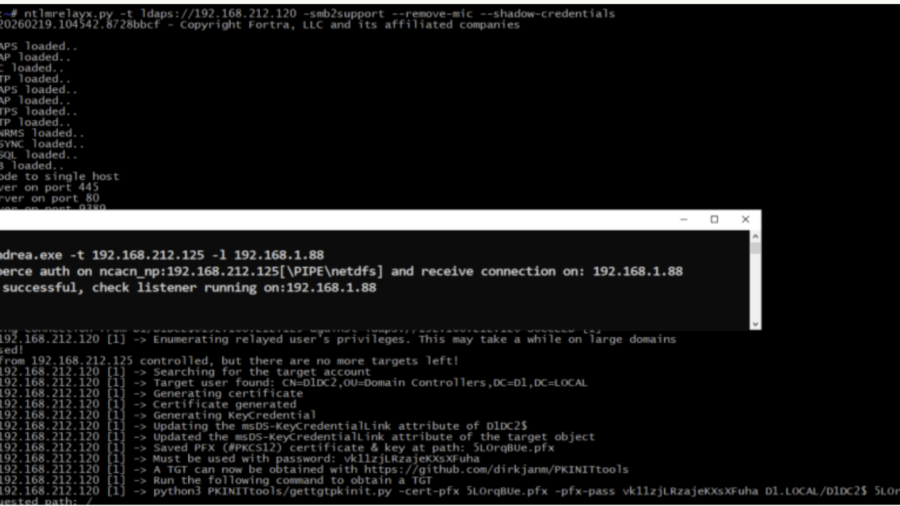
What Windows Server 2025 Quietly Did to Your NTLM Relay
Windows Server 2025 quietly breaks a classic NTLM relay technique by enforcing changes inside msv1_0.dll. The update prevents attackers from abusing NTLMv1 and stripping MIC to relay authentication to LDAPS.
The 49-Day macOS Time Bomb: How a TCP Timer Overflow Breaks the Network Stack
A bug in macOS’s TCP stack causes networking to fail after about 49.7 days of uptime. A 32-bit timer overflow freezes the TCP clock, preventing cleanup of closed connections and eventually exhausting ephemeral ports.
Tutorial: Adaptix C2 with ShellcodePack and MacroPack
This tutorial shows how to weaponize Adaptix C2 agents using ShellcodePack and MacroPack, converting payloads into shellcode and packaging them in evasive loaders to improve stealth and bypass EDR during red-team operations.
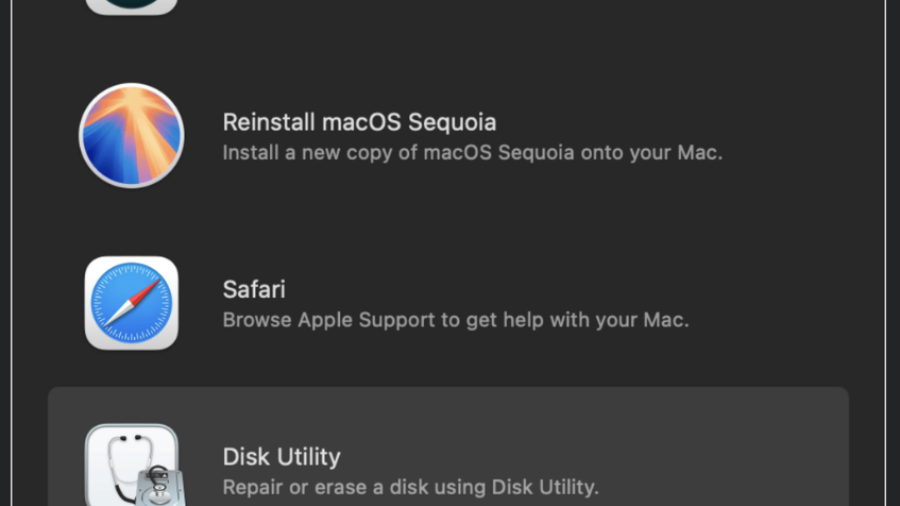
Recovery Mode Breakdown: Turning macOS Recovery Safari into Root Persistence
A macOS Recovery Mode Safari flaw allowed attackers to write arbitrary files to system partitions. By placing a malicious LaunchDaemon in /Library/LaunchDaemons, an attacker could achieve persistent root execution after reboot.
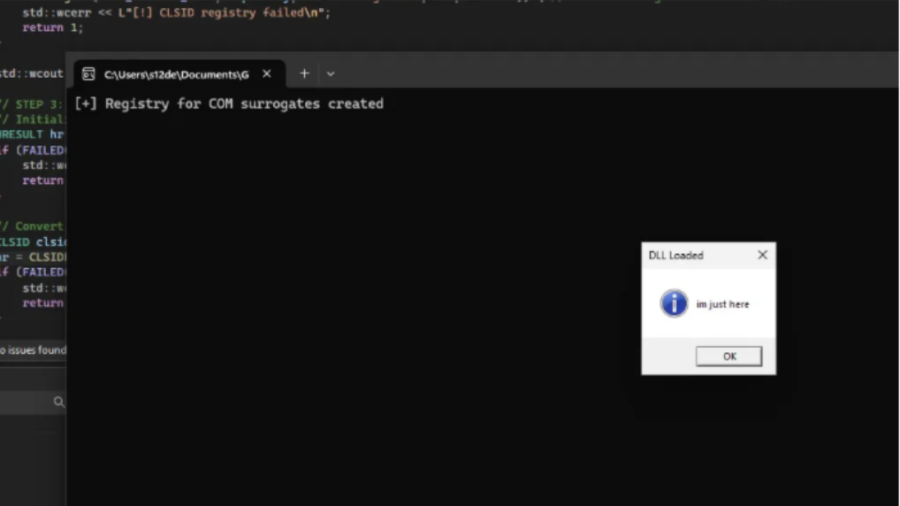
COMouflage: Stealthy DLL Surrogate Injection for Process Tree Evasion
COMouflage is a stealthy Windows injection technique that abuses COM DLL Surrogates to execute malicious DLLs inside dllhost.exe, making svchost.exe appear as the parent process and hiding the attacker’s process from detection.