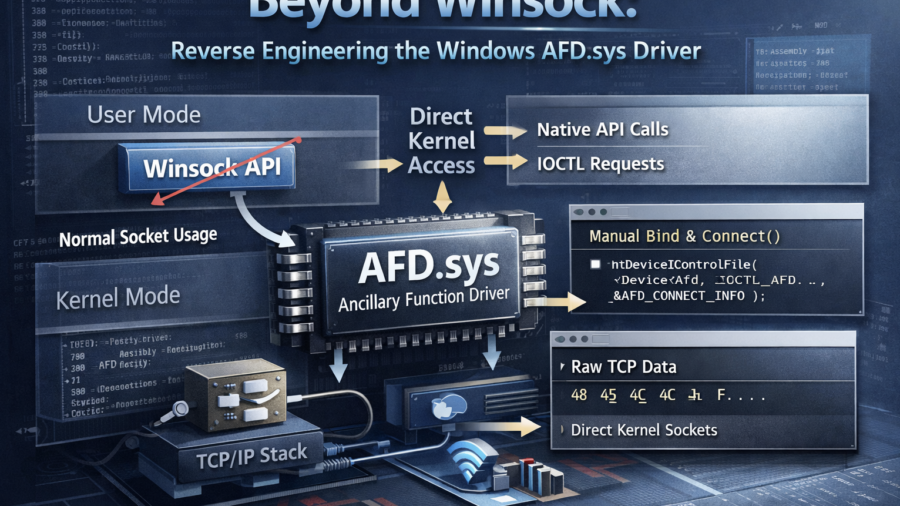
The article demonstrates how to bypass the Winsock layer by communicating directly with the Windows AFD driver using Native API calls. It explains how socket operations can be replicated via IOCTLs and how this reduces reliance on standard networking APIs.
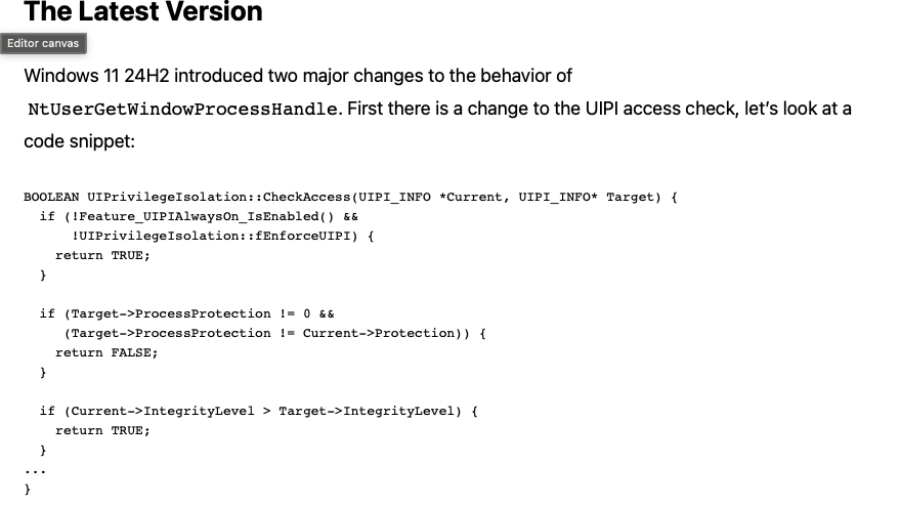
A Deep Dive into the GetProcessHandleFromHwnd API
The article analyzes the Windows GetProcessHandleFromHwnd API and its evolution from a hook-based implementation to a kernel Win32k function that could open powerful process handles, enabling security bypasses such as CVE-2023-41772.
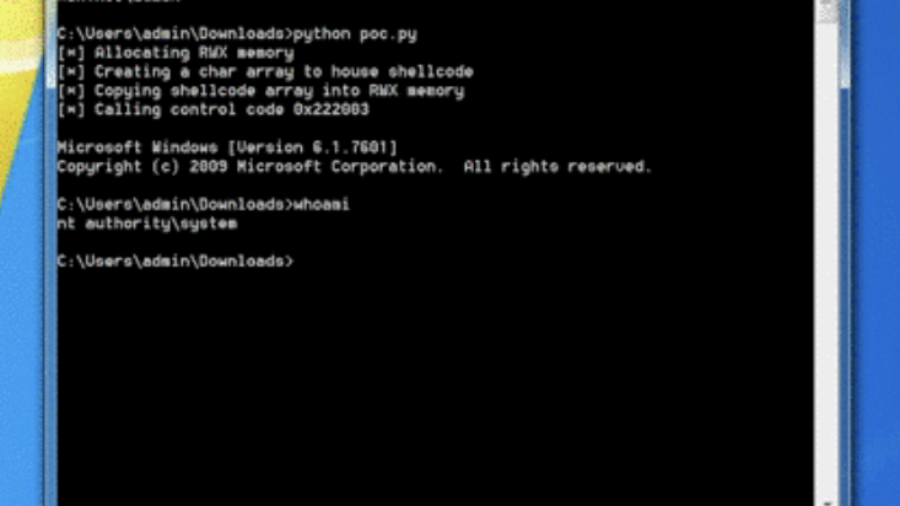
0x00 – Introduction to Windows Kernel Exploitation
The article introduces Windows kernel exploitation and explains how to build a research lab using tools like WinDbg and the HackSys Extreme Vulnerable Driver (HEVD) to study kernel vulnerabilities and exploit development.
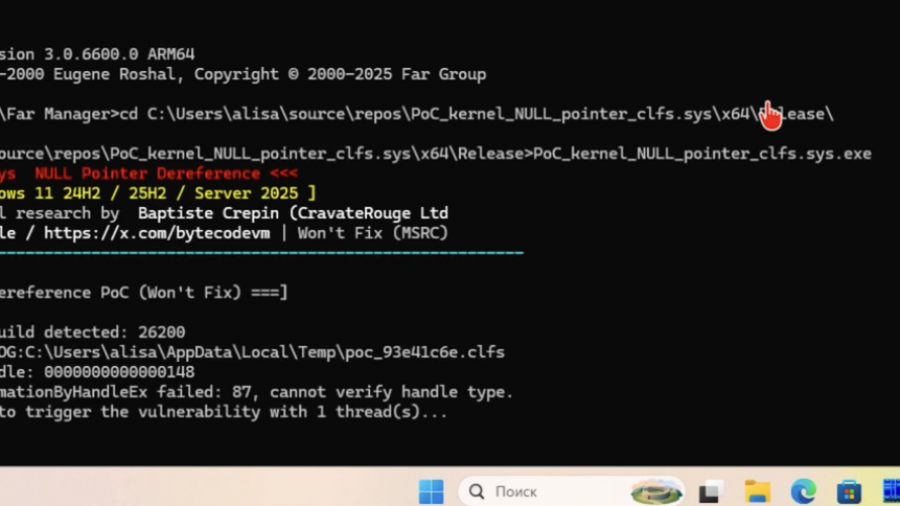
Won’t Fix: Kernel DoS in clfs.sys via NULL FastMutex Dereference
The article examines a Windows kernel bug in clfs.sys where a NULL pointer is dereferenced during fast mutex acquisition, causing a kernel crash and denial of service due to improper validation of a FAST_MUTEX pointer.
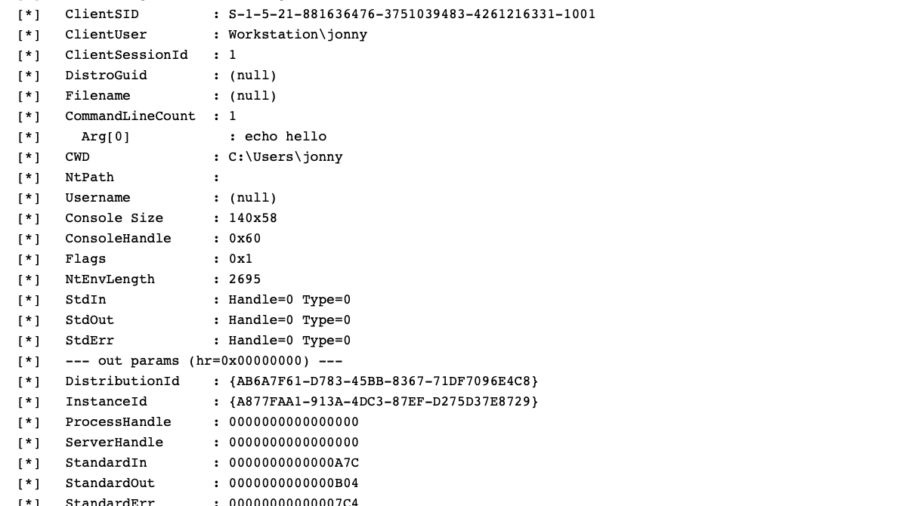
WSL, COM Hooking, & RTTI
The article demonstrates how to hook COM methods in Windows Subsystem for Linux by leveraging C++ RTTI metadata to reconstruct class layouts and locate virtual methods, enabling precise COM instrumentation without symbols.
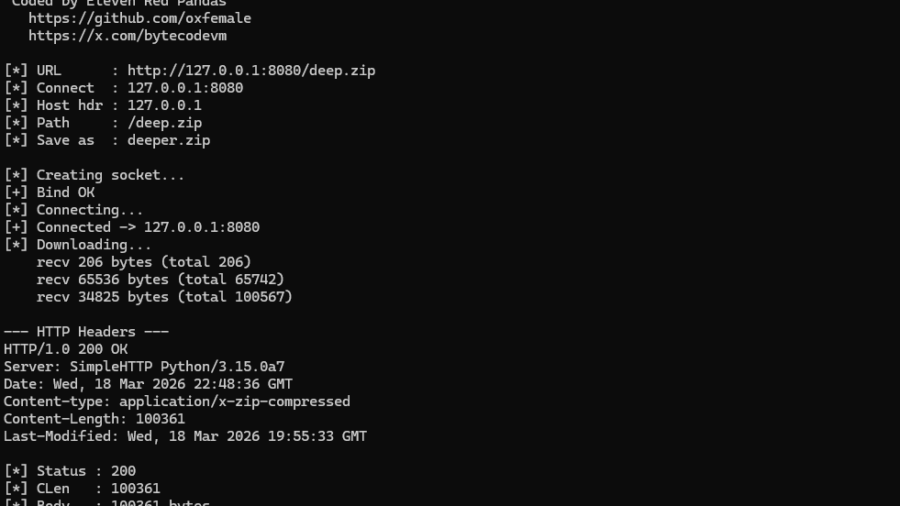
Peeling Back the Socket Layer: Reverse Engineering Windows AFD.sys
The research reverse-engineers Windows AFD.sys, showing how TCP sockets can be created, connected, and used by sending handcrafted IOCTL requests directly to the kernel driver—completely bypassing the Winsock networking API.
LOLExfil: Stealthy Data Exfiltration Using Living-Off-the-Land Techniques
The article introduces LOLExfil, a Living-Off-the-Land data exfiltration technique that abuses legitimate system tools and trusted services to stealthily extract data, blending malicious activity with normal system behavior.
Decrypting and Abusing Predefined BIOCs in Palo Alto Cortex XDR
Research shows how Palo Alto Cortex XDR predefined BIOC behavioral rules can be decrypted and analyzed. By understanding rule logic and built-in exceptions, attackers can adapt techniques to evade detection and bypass behavioral protections.
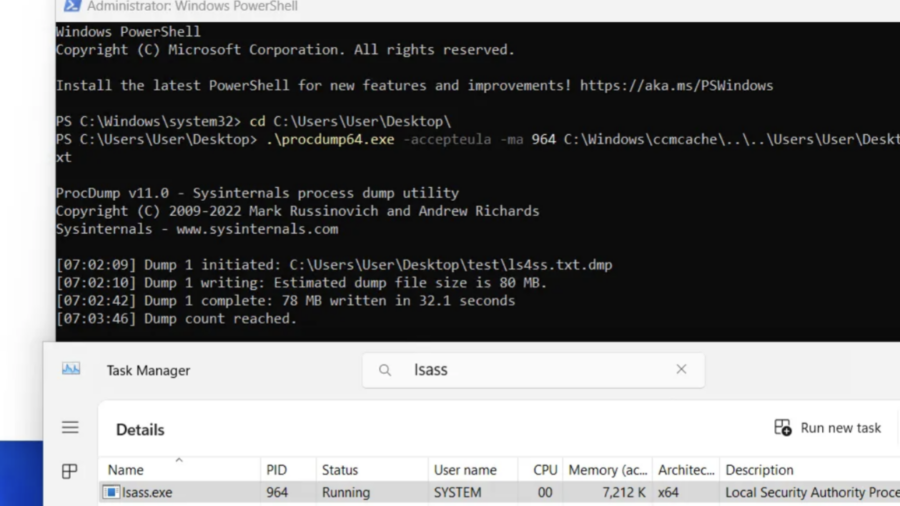
Ghost in the PPL – LSASS Memory Dump
The article explains a technique for dumping memory from the protected LSASS process (PPL). It analyzes limitations of PPL protection and demonstrates how MiniDumpWriteDump and existing process handles can be used to extract credential data.
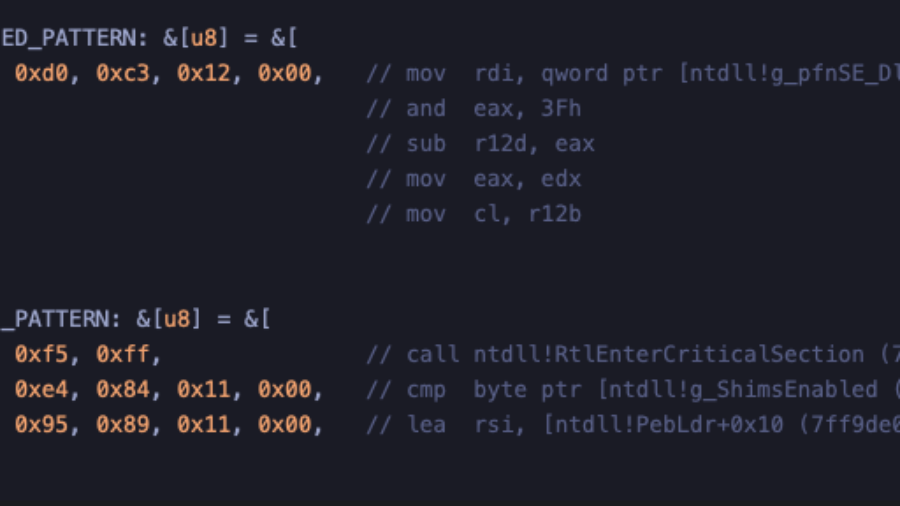
Crimes against NTDLL – Implementing Early Cascade Injection
How to implement Early Cascade Injection in Rust, a stealthy Windows process injection technique that hijacks shim engine callbacks in ntdll to execute shellcode during early process initialization, before many EDR hooks activate.