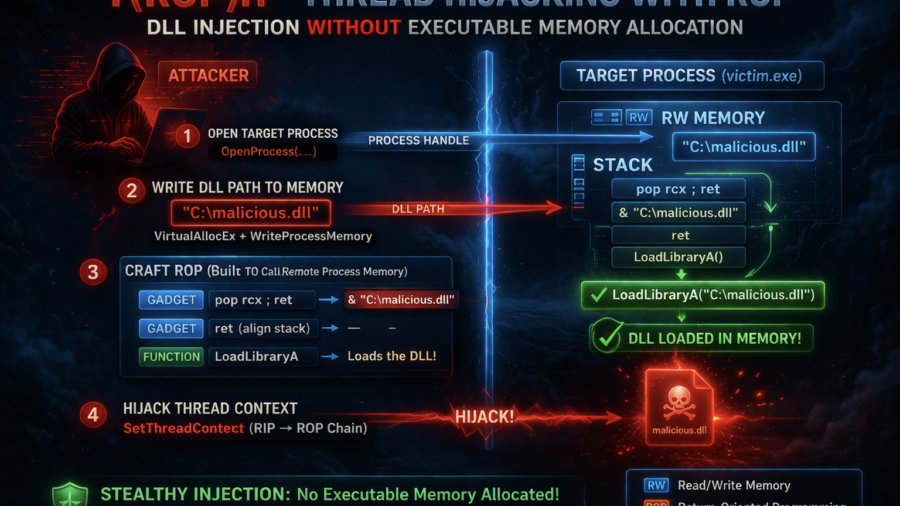
The article presents T(ROP)H, a process injection technique that hijacks threads and uses a ROP chain to load a DLL without allocating executable memory, reducing common detection indicators used by EDR systems.
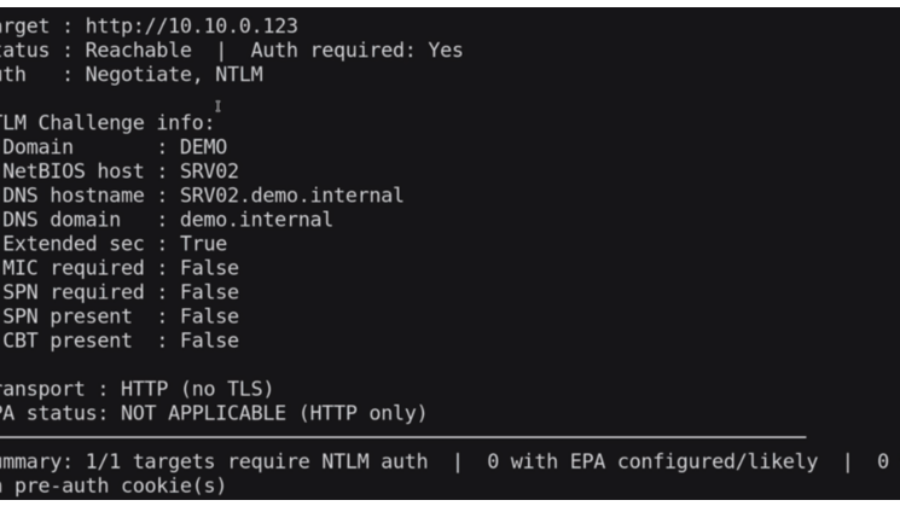
Relaying Trust: Exploiting NTLM Authentication to Compromise Active Directory
he article demonstrates an NTLM relay attack against Active Directory using tools like ntlmrelayx and PetitPotam. By relaying authentication to LDAP, attackers can create accounts, abuse delegation, and gain administrative access.
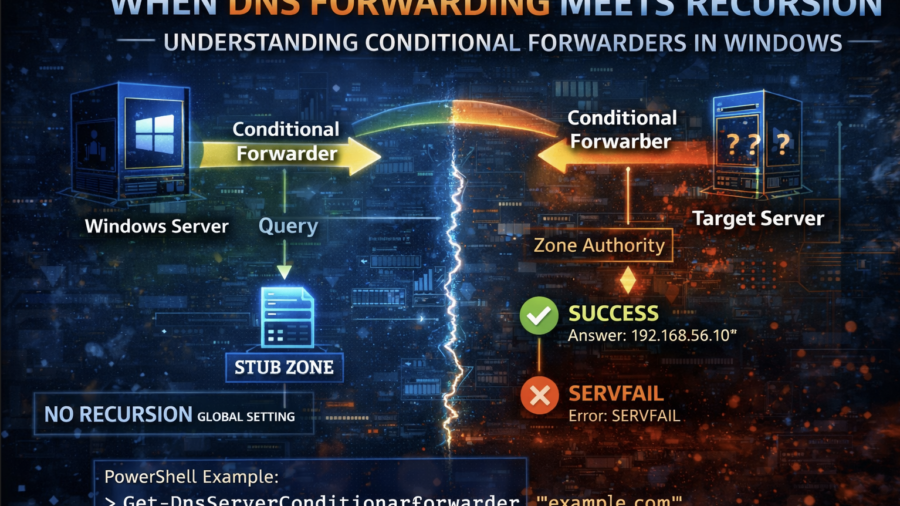
When DNS Forwarding Meets Recursion: Understanding Conditional Forwarders in Windows
The article explains how Windows DNS conditional forwarders interact with recursion. It shows that recursion settings can be overridden per zone and demonstrates how different DNS configurations affect query resolution.
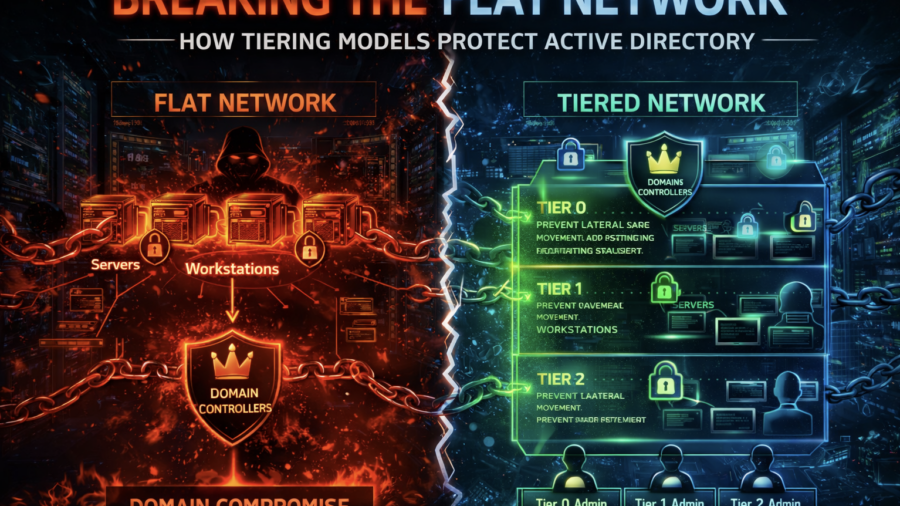
Breaking the Flat Network: How Tiering Models Protect Active Directory
The article explains how flat enterprise networks enable easy lateral movement and domain compromise. It shows how Active Directory tiering models segment privileges and systems to prevent attackers from escalating access.
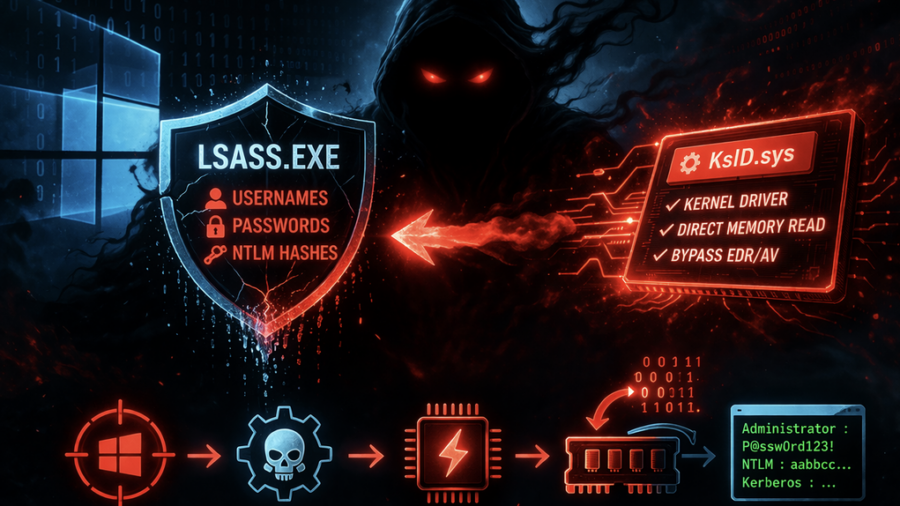
Ghost in LSASS: Inside the KslKatz Credential Dumping Framework
KslKatz is a Windows credential-dumping tool that reads LSASS memory using a kernel driver to bypass user-mode protections. It merges techniques from KslDump and GhostKatz to extract authentication secrets with improved stealth.
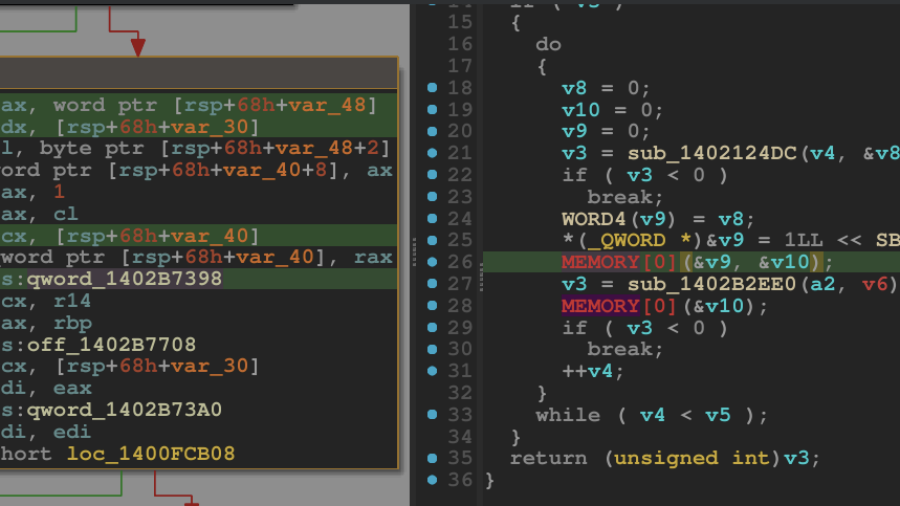
Breaking the Shield: Unpacking a VMProtected Windows Kernel Driver
A technical walkthrough showing how to unpack a VMProtected Windows kernel driver using WinDbg and dynamic analysis. The guide demonstrates restoring the hidden Import Address Table and dumping a clean driver for reverse engineering.
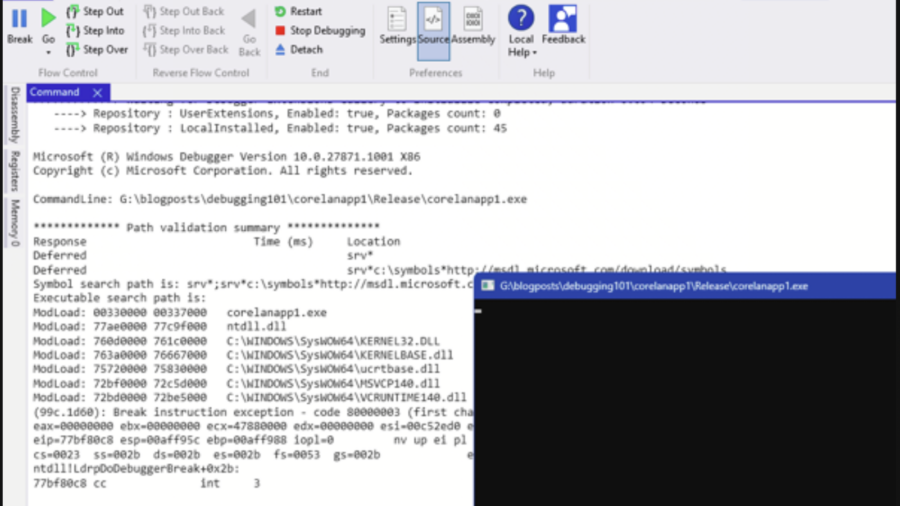
Debugging – WinDBG & WinDBGX Fundamentals
A beginner-friendly guide to debugging Windows programs using WinDbg and WinDbgX. It explains debugger basics, breakpoints, symbols, memory inspection, and execution control—key skills for reverse engineering and vulnerability research.
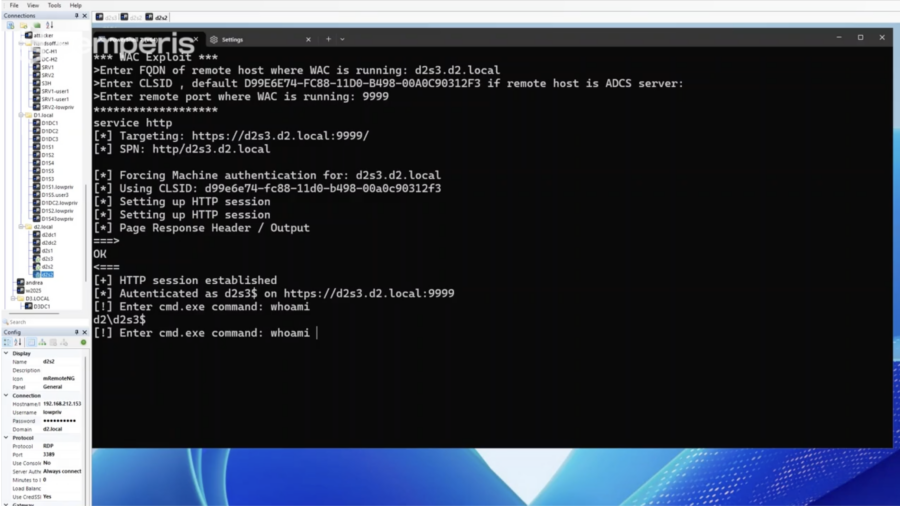
What You Need to Know: Windows Admin Center Remote Privilege Escalation (CVE-2026-26119)
CVE-2026-26119 is a high-severity privilege-escalation flaw in Windows Admin Center caused by improper authentication. Attackers with low-privileged access could gain admin rights and potentially compromise entire domains.
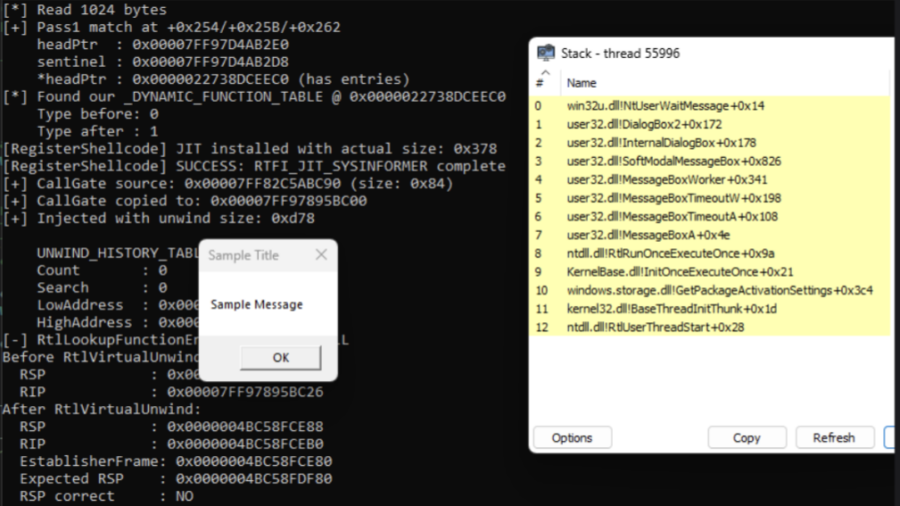
Invisible Execution: Hiding Malware with Unwind Metadata Manipulation
The article introduces BYOUD, a Windows evasion technique that manipulates unwind metadata to spoof call stacks without altering return addresses, allowing malware to bypass EDR stack inspection and appear as legitimate execution.
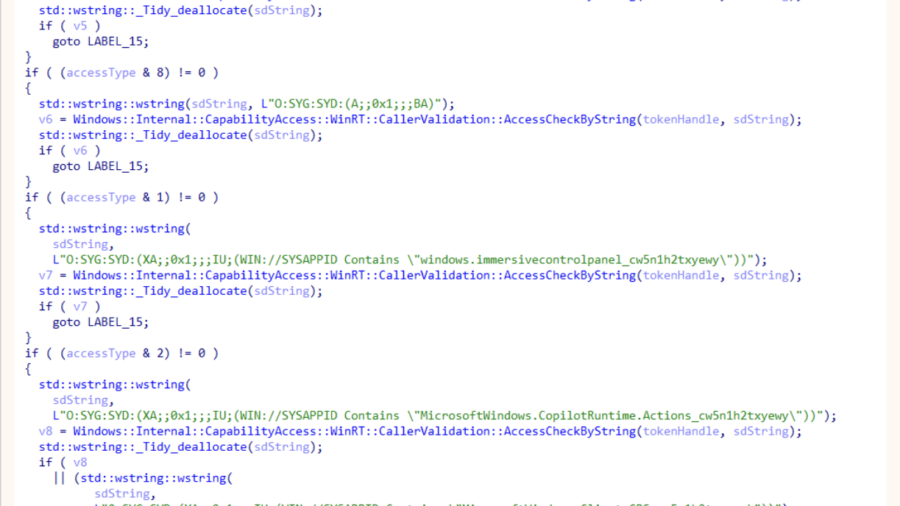
ODR: Internals of Microsoft’s New Native MCP Registration
The article explains Microsoft’s ODR mechanism for native MCP registration, enabling AI agents to discover and invoke system tools through the Model Context Protocol, preparing Windows for secure agent-driven workflows and integrations.