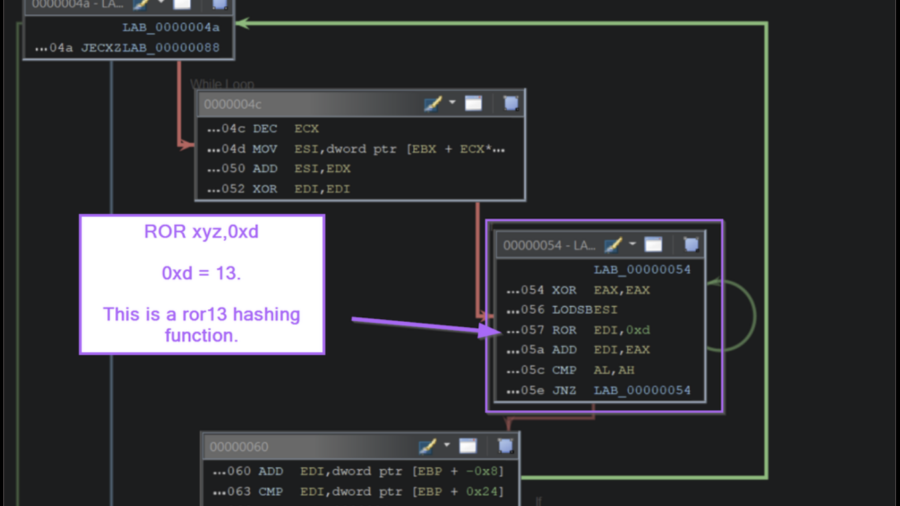
The article demonstrates how to analyze Windows shellcode in Ghidra by identifying API-hashing routines, resolving hidden Windows API calls, and extracting C2 infrastructure without relying on automated emulation tools.
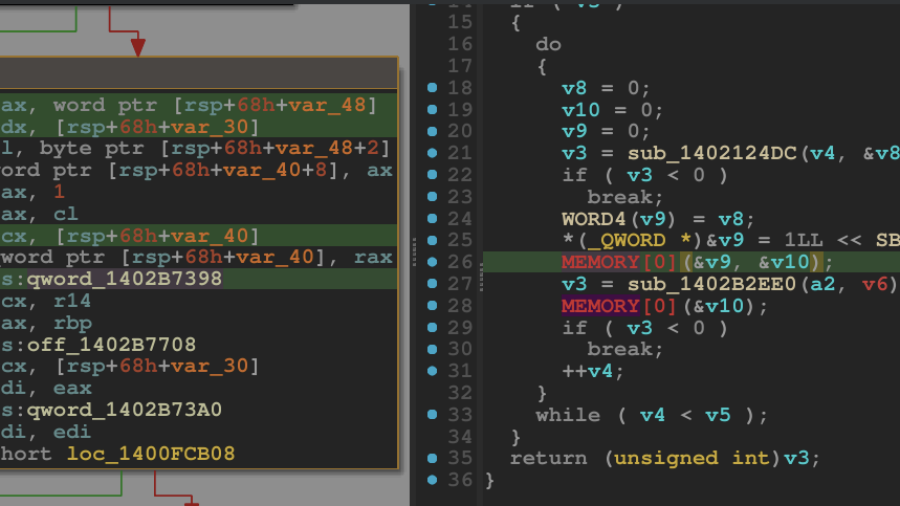
Breaking the Shield: Unpacking a VMProtected Windows Kernel Driver
A technical walkthrough showing how to unpack a VMProtected Windows kernel driver using WinDbg and dynamic analysis. The guide demonstrates restoring the hidden Import Address Table and dumping a clean driver for reverse engineering.
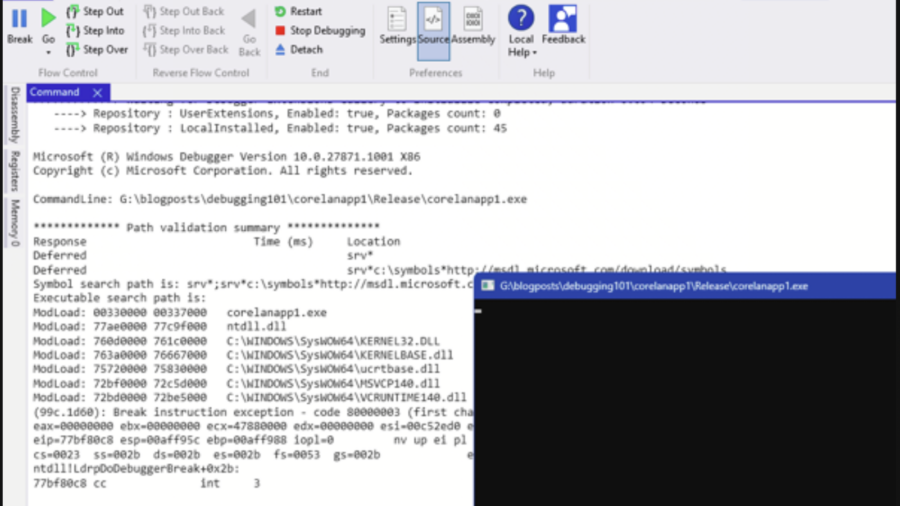
Debugging – WinDBG & WinDBGX Fundamentals
A beginner-friendly guide to debugging Windows programs using WinDbg and WinDbgX. It explains debugger basics, breakpoints, symbols, memory inspection, and execution control—key skills for reverse engineering and vulnerability research.
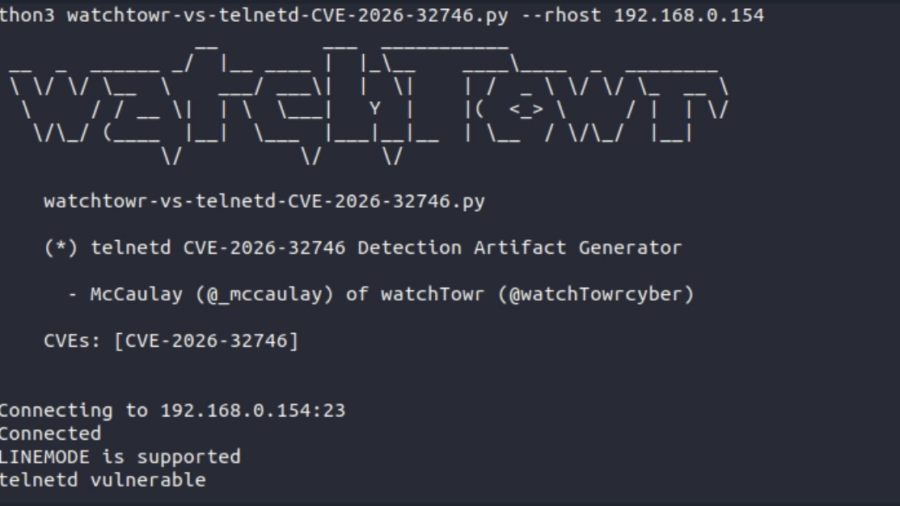
A 32-Year-Old Bug Walks Into A Telnet Server (GNU inetutils Telnetd CVE-2026-32746 Pre-Auth RCE)
The article analyzes CVE-2026-32746, a decades-old vulnerability in GNU Inetutils telnetd where a malformed LINEMODE SLC option triggers an out-of-bounds write, enabling unauthenticated remote exploitation.
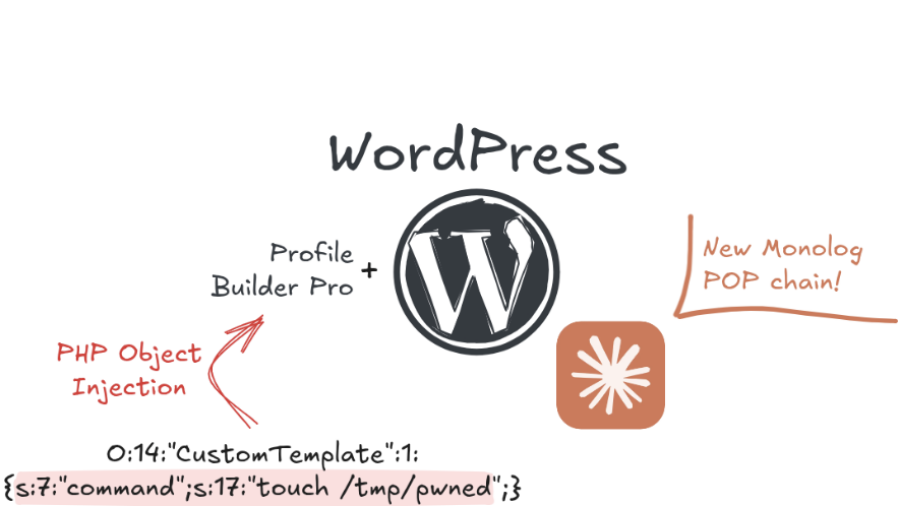
Exploiting a PHP Object Injection in Profile Builder Pro in the era of AI
The article explains how researchers exploited an unauthenticated PHP Object Injection in the WordPress plugin Profile Builder Pro, showing how AI tools can accelerate vulnerability discovery and exploit development in modern web applications.
TP-Link Tapo C200: Hardcoded Keys, Buffer Overflows and Privacy in the Era of AI Assisted Reverse Engineering
The article shows how AI-assisted reverse engineering of the TP-Link Tapo C200 firmware uncovered hardcoded keys, buffer overflows, and insecure APIs, demonstrating how IoT devices can expose users to remote compromise and privacy risks.
Booting into Trust: Reverse Engineering macOS Secure Boot Internals
The article analyzes the macOS secure boot chain on Apple Silicon, showing how Boot ROM, cryptographic verification, Secure Enclave, and staged bootloaders create a hardware-anchored chain-of-trust that protects the OS from power-on to kernel startup.
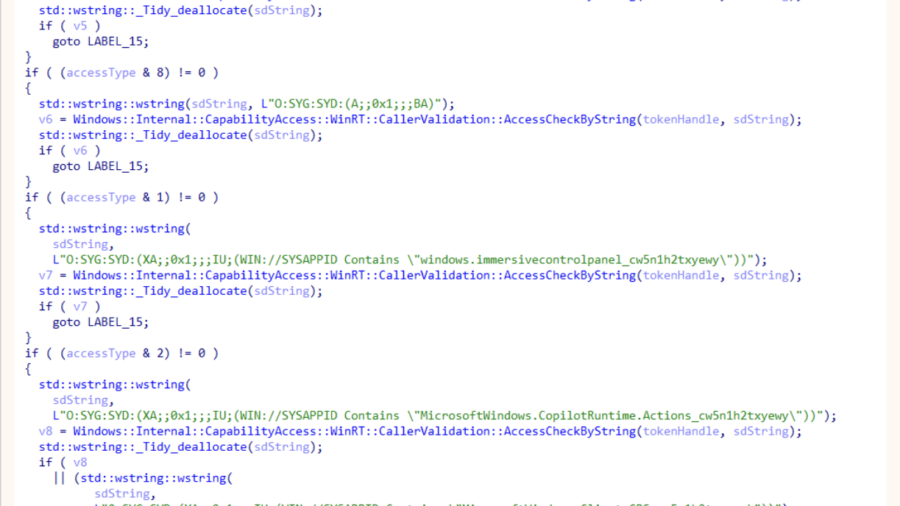
ODR: Internals of Microsoft’s New Native MCP Registration
The article explains Microsoft’s ODR mechanism for native MCP registration, enabling AI agents to discover and invoke system tools through the Model Context Protocol, preparing Windows for secure agent-driven workflows and integrations.
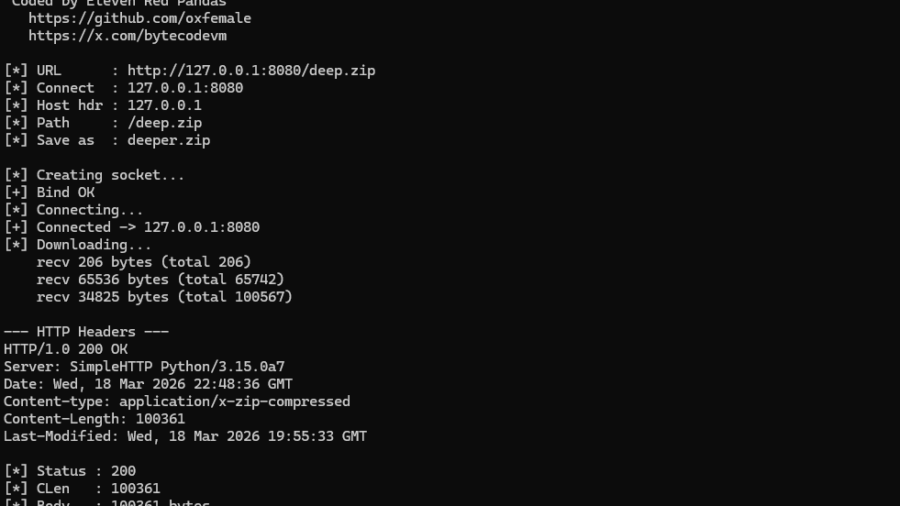
NT AFD.SYS HTTP Downloader: From First Syscall to bypass the majority of usermode EDR hooks
The article demonstrates how to bypass the Winsock layer by communicating directly with the Windows AFD driver using Native API calls. It explains how socket operations can be replicated via IOCTLs and how this reduces reliance on standard networking APIs.
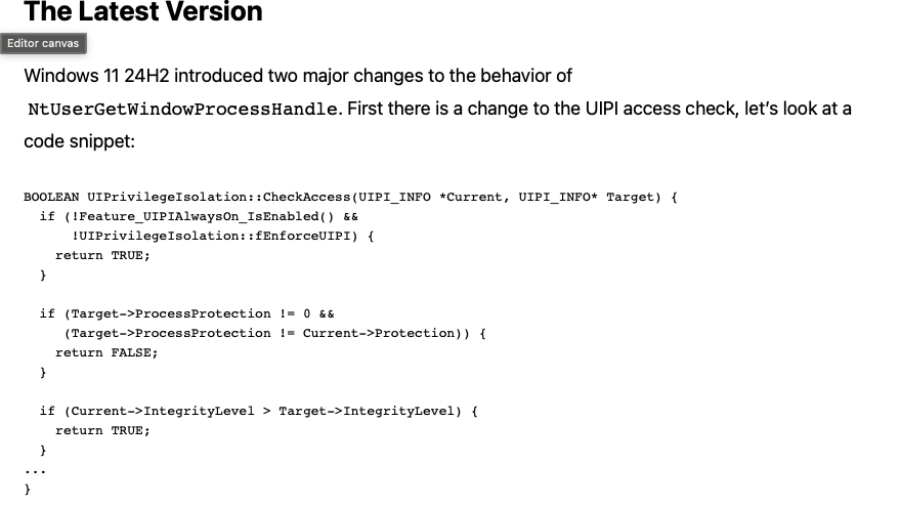
A Deep Dive into the GetProcessHandleFromHwnd API
The article analyzes the Windows GetProcessHandleFromHwnd API and its evolution from a hook-based implementation to a kernel Win32k function that could open powerful process handles, enabling security bypasses such as CVE-2023-41772.