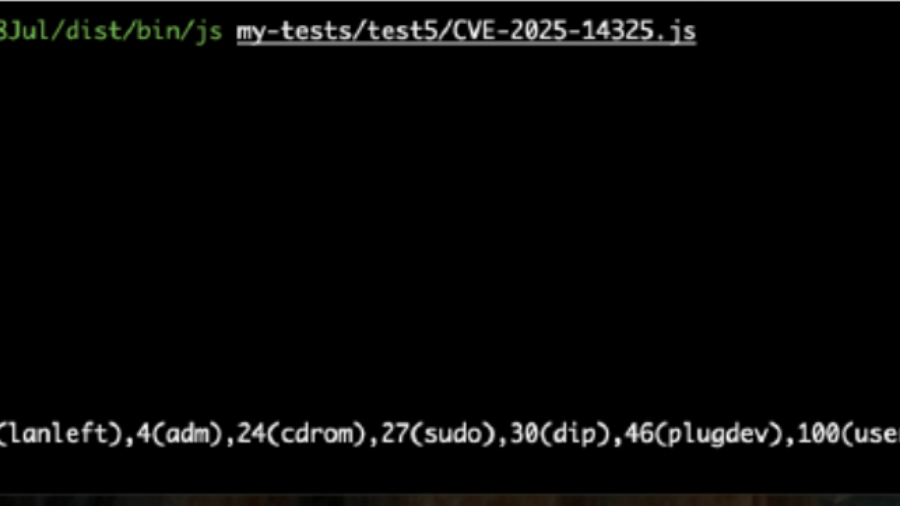
The article analyzes CVE-2025-14325, a SpiderMonkey Baseline JIT bug causing type confusion in inline caches. Incorrect assumptions about object shapes can lead to memory corruption and possible code execution in Firefox.
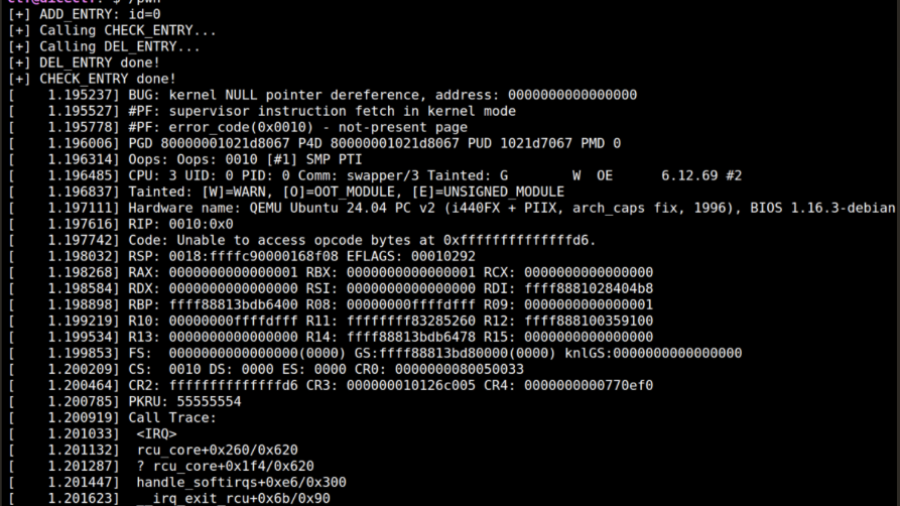
From RCU Double Free to Root: Exploiting a Linux Kernel Race in cornelslop
A DiceCTF write-up showing how an RCU double-free race in a Linux kernel module can be turned into a cross-cache exploit by manipulating SLUB allocator behavior and overlapping page-table entries.
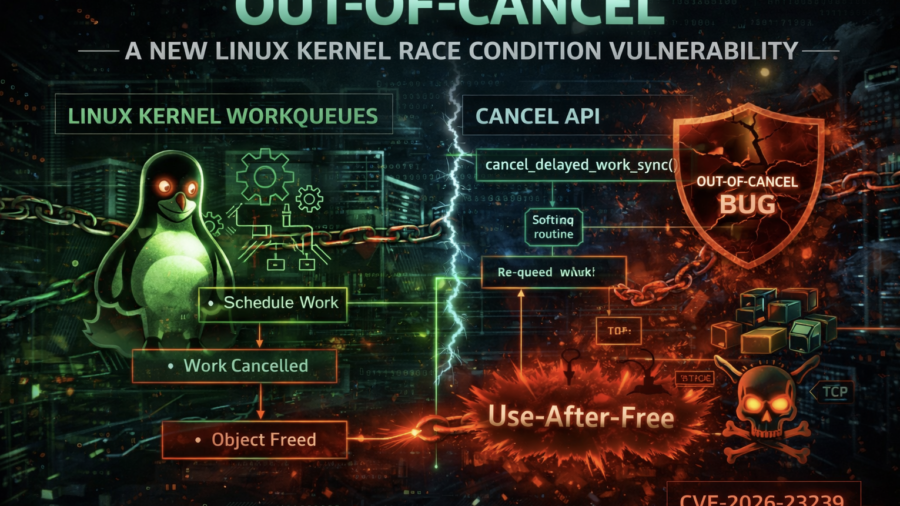
Out-of-Cancel: A New Linux Kernel Race Condition Bug Class
The article introduces the Out-of-Cancel vulnerability class in the Linux kernel, where workqueue cancellation APIs fail to guarantee object lifetime. This race can lead to Use-After-Free bugs, demonstrated using espintcp (CVE-2026-23239).
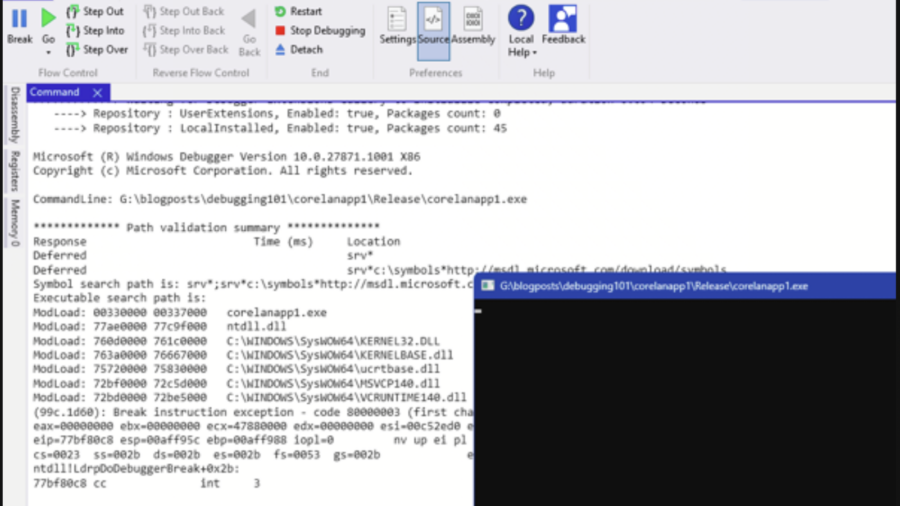
Debugging – WinDBG & WinDBGX Fundamentals
A beginner-friendly guide to debugging Windows programs using WinDbg and WinDbgX. It explains debugger basics, breakpoints, symbols, memory inspection, and execution control—key skills for reverse engineering and vulnerability research.
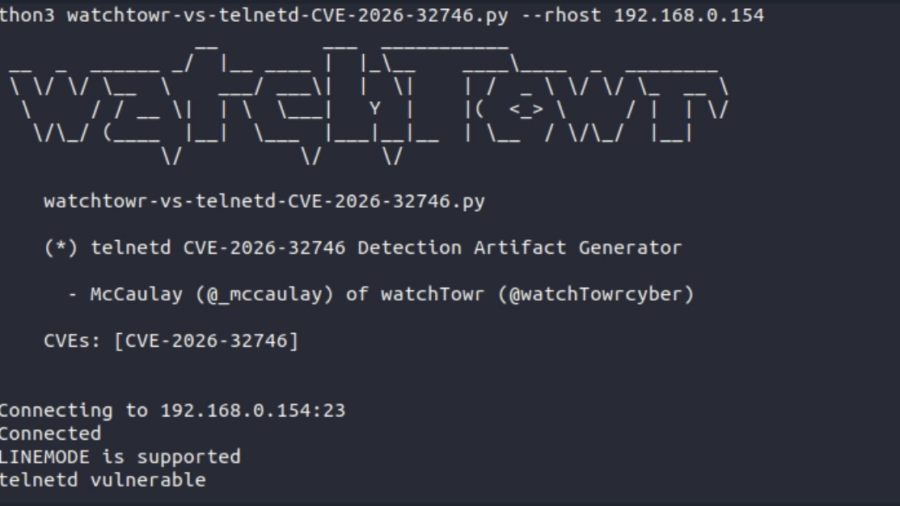
A 32-Year-Old Bug Walks Into A Telnet Server (GNU inetutils Telnetd CVE-2026-32746 Pre-Auth RCE)
The article analyzes CVE-2026-32746, a decades-old vulnerability in GNU Inetutils telnetd where a malformed LINEMODE SLC option triggers an out-of-bounds write, enabling unauthenticated remote exploitation.
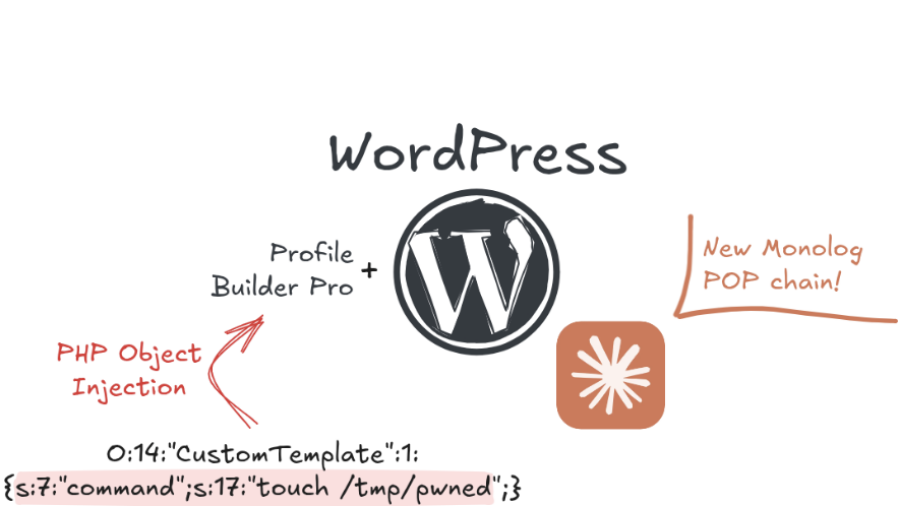
Exploiting a PHP Object Injection in Profile Builder Pro in the era of AI
The article explains how researchers exploited an unauthenticated PHP Object Injection in the WordPress plugin Profile Builder Pro, showing how AI tools can accelerate vulnerability discovery and exploit development in modern web applications.
TP-Link Tapo C200: Hardcoded Keys, Buffer Overflows and Privacy in the Era of AI Assisted Reverse Engineering
The article shows how AI-assisted reverse engineering of the TP-Link Tapo C200 firmware uncovered hardcoded keys, buffer overflows, and insecure APIs, demonstrating how IoT devices can expose users to remote compromise and privacy risks.
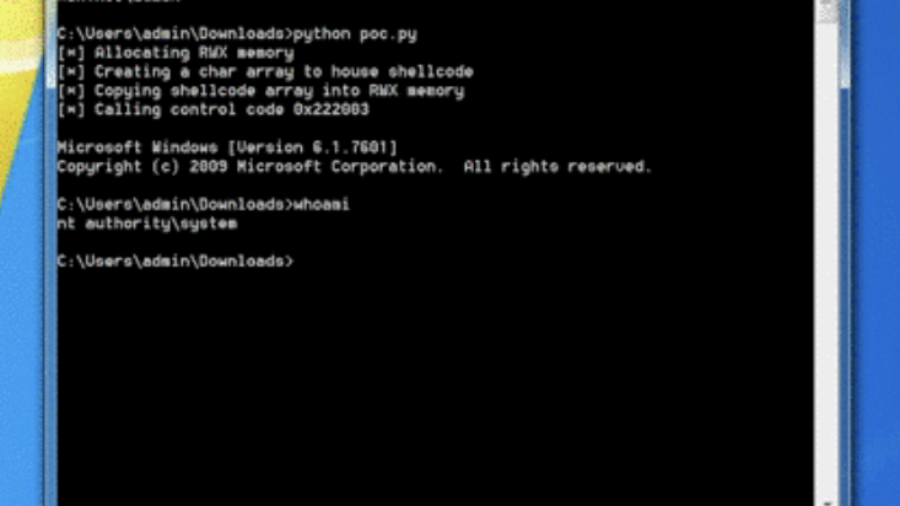
0x00 – Introduction to Windows Kernel Exploitation
The article introduces Windows kernel exploitation and explains how to build a research lab using tools like WinDbg and the HackSys Extreme Vulnerable Driver (HEVD) to study kernel vulnerabilities and exploit development.
Ghost in the PPL – LSASS Memory Dump
The article explains a technique for dumping memory from the protected LSASS process (PPL). It analyzes limitations of PPL protection and demonstrates how MiniDumpWriteDump and existing process handles can be used to extract credential data.
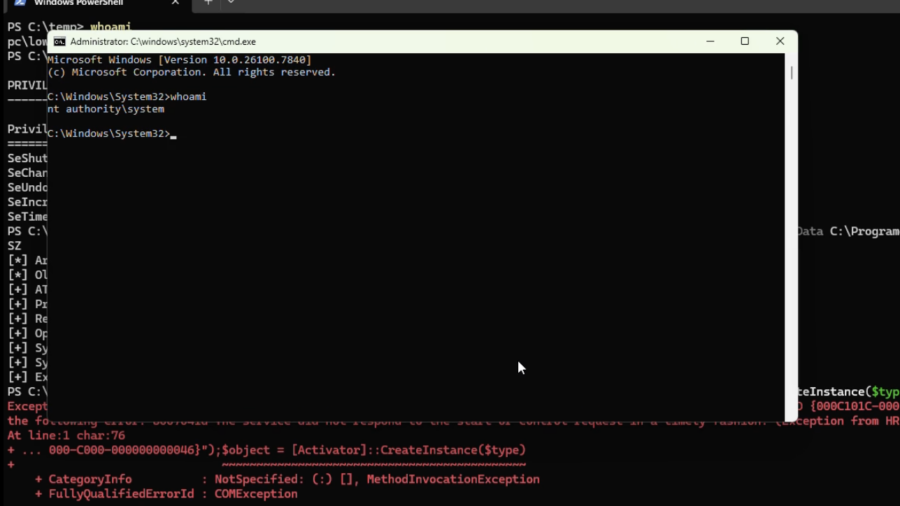
RIP RegPwn: The Rise and Fall of a Windows Registry Exploitation Technique
The article explores a red-team research project called “RegPwn,” showing how weaknesses in Windows registry handling can be abused to achieve privilege escalation or persistence, and discusses why the technique has now been mitigated or rendered ineffective.