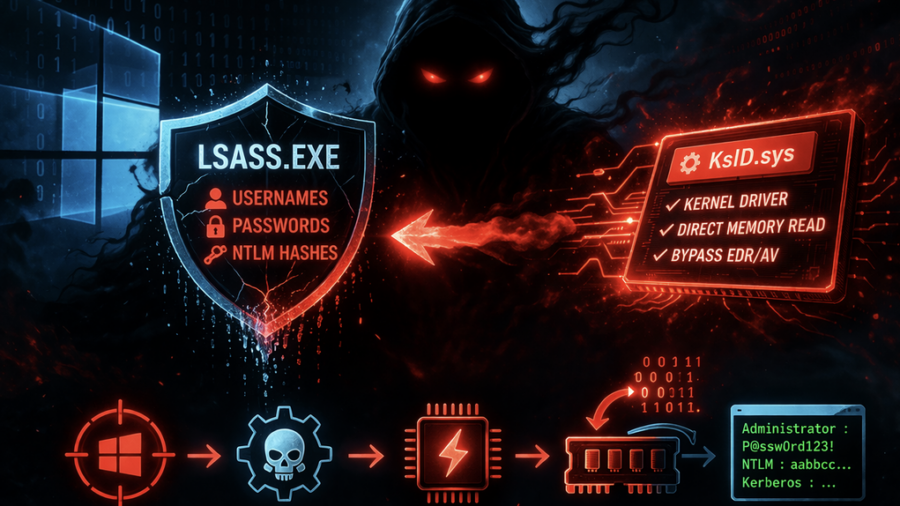
The article explains how attackers dump credentials from the Windows LSASS process using tools like Mimikatz and ProcDump, extracting password hashes and Kerberos tickets that enable privilege escalation and lateral movement.
Ghost in LSASS: Inside the KslKatz Credential Dumping Framework
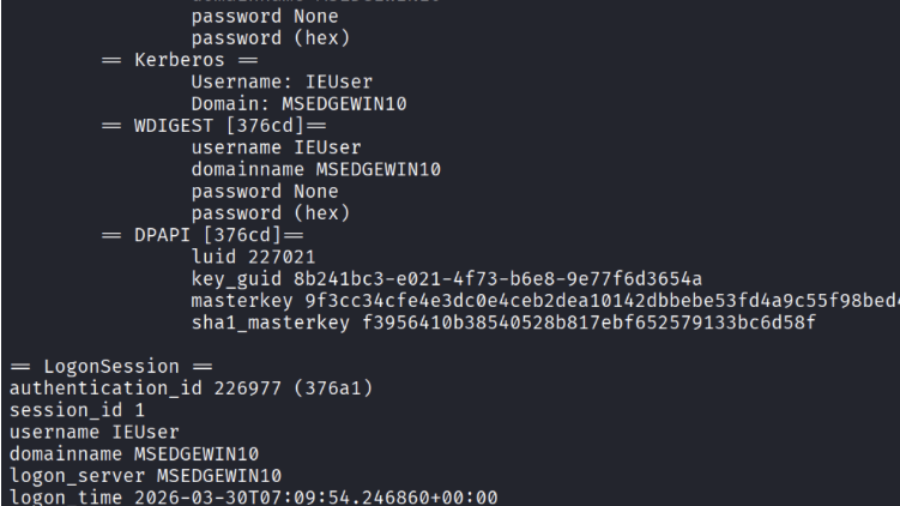
KslKatz is a Windows credential-dumping tool that reads LSASS memory using a kernel driver to bypass user-mode protections. It merges techniques from KslDump and GhostKatz to extract authentication secrets with improved stealth.
Ghost in the PPL – LSASS Memory Dump
The article explains a technique for dumping memory from the protected LSASS process (PPL). It analyzes limitations of PPL protection and demonstrates how MiniDumpWriteDump and existing process handles can be used to extract credential data.