It’s great to see that our website now has its own Telegram channel! Follow us at @core-jmp.org to stay updated with the latest posts, security research, and new articles published on core-jmp.org.
Hacking a Bluetooth Printer Server: GATT to UART Adapter?
Reverse engineering a Bluetooth printer server reveals multiple security flaws, including exposed debug interfaces and insecure GATT services, enabling unauthenticated remote code execution with root privileges via Bluetooth or network access.
Blinkenlights 2.0: Reverse Engineering a Smartwatch via Screen Signals
Reverse engineering a cheap smartwatch and reviving the classic “blinkenlights” attack to extract firmware through screen update patterns, revealing weaknesses in OTA update mechanisms, BLE communication, and embedded device security design.
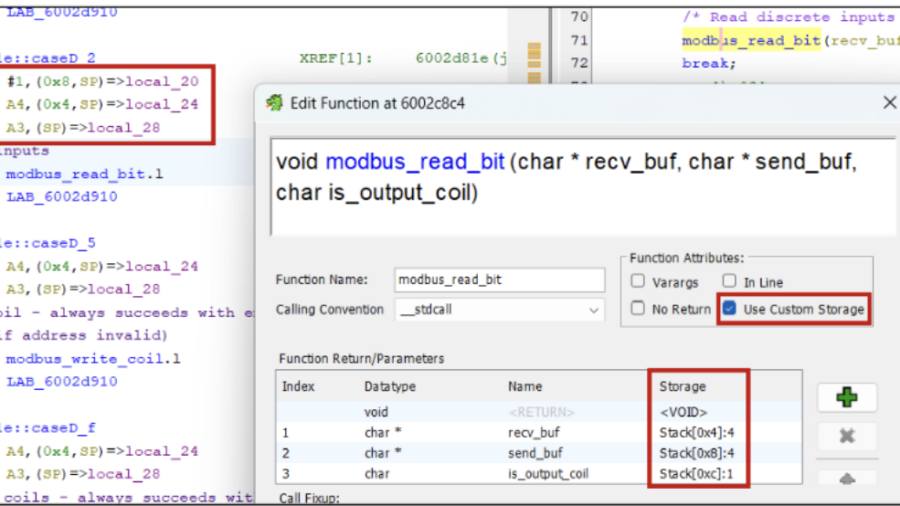
Taming the dragon: reverse engineering firmware with Ghidra
The article explains how to reverse engineer embedded firmware using Ghidra, covering techniques for loading firmware, identifying CPU architectures, analyzing functions, and using scripts/plugins to understand device logic and discover vulnerabilities.
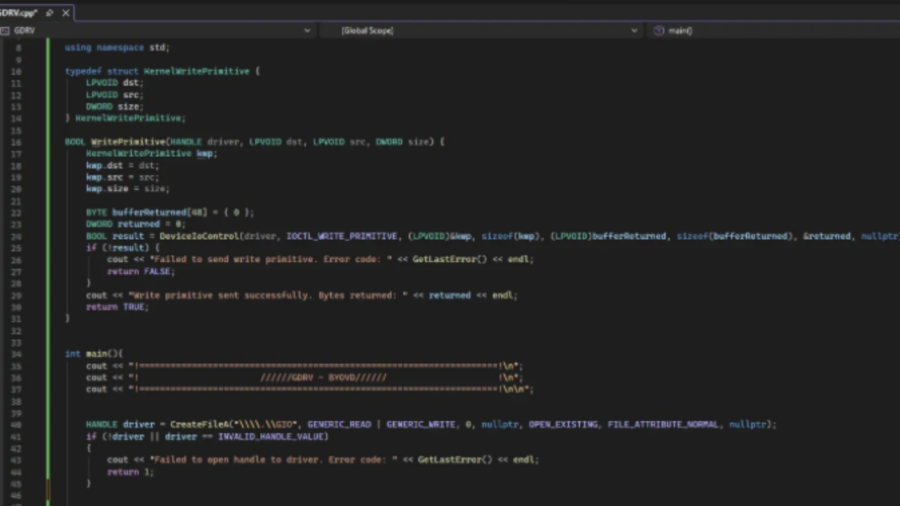
Exploiting a Kernel Read/Write Primitive using BYOVD
The article explains how attackers exploit a vulnerable signed driver (BYOVD) to obtain a kernel read/write primitive. It shows how unsafe IOCTL handlers allow manipulating kernel memory and abusing driver functionality for offensive operations.
Physical Network Sniffing: Capturing Ethernet Traffic with Simple Alligator Clips
The article demonstrates how Ethernet traffic can be passively intercepted at the physical layer using simple tools like alligator clips attached to network cables. It highlights risks of exposed wiring and shows how attackers can capture unencrypted traffic.
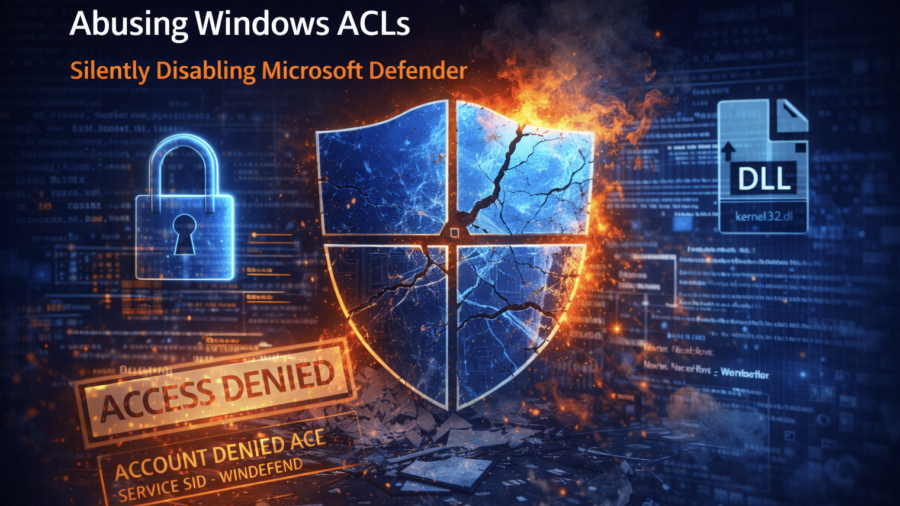
Windows Defender ACL Blocking: A Silent Technique With Serious Impact
The article analyzes a technique that disables Microsoft Defender by modifying file ACLs to block security services from accessing critical system DLLs. This silent method prevents Defender from starting without triggering obvious alerts.
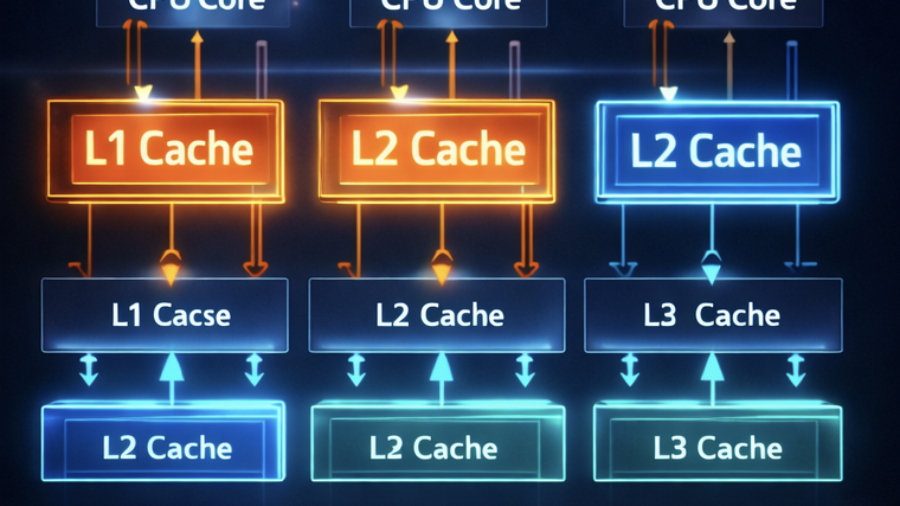
Understanding CPU Cache Hierarchy: Why Modern Processors Use Multiple Cache Levels
The article explains why modern CPUs use multiple cache levels (L1, L2, L3) instead of a single large cache. It discusses the trade-off between cache size and latency and shows how a cache hierarchy balances speed, capacity, and efficiency.
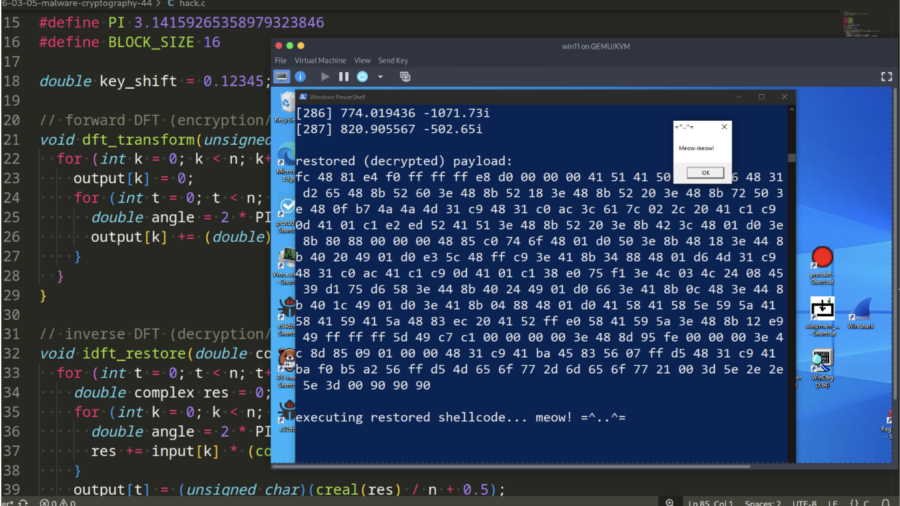
Malware and cryptography 44 – encrypt/decrypt payload via Discrete Fourier Transform. Simple C example.
Demonstration how malware can encrypt and decrypt payloads using the Discrete Fourier Transform (DFT). It provides a simple C example showing how mathematical transforms can hide shellcode and help evade static signature-based detection.
Defeating a 40-year-old copy protection dongle
Reverse engineering a vintage hardware copy-protection dongle used by 1980s enterprise software. By analyzing the DOS program and emulator environment, the author discovered the dongle check and bypassed it with a tiny patch.