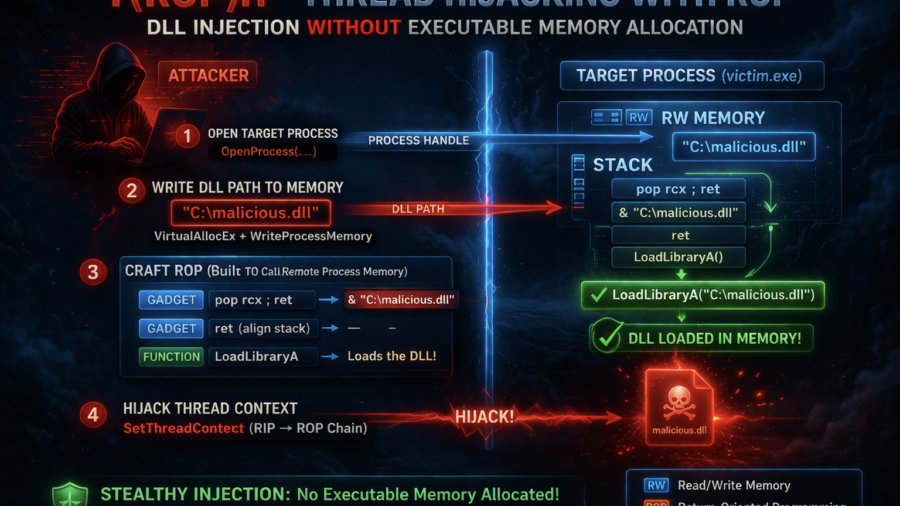
The article presents T(ROP)H, a process injection technique that hijacks threads and uses a ROP chain to load a DLL without allocating executable memory, reducing common detection indicators used by EDR systems.
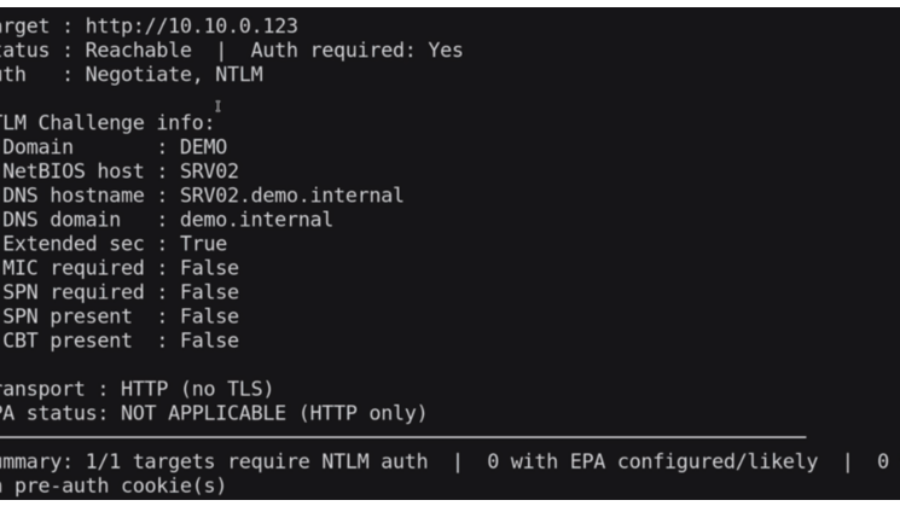
Relaying Trust: Exploiting NTLM Authentication to Compromise Active Directory
he article demonstrates an NTLM relay attack against Active Directory using tools like ntlmrelayx and PetitPotam. By relaying authentication to LDAP, attackers can create accounts, abuse delegation, and gain administrative access.
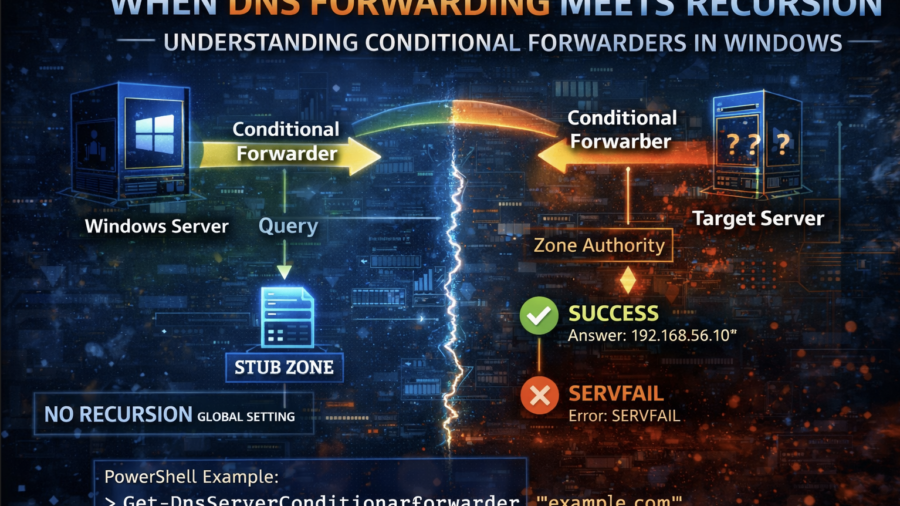
When DNS Forwarding Meets Recursion: Understanding Conditional Forwarders in Windows
The article explains how Windows DNS conditional forwarders interact with recursion. It shows that recursion settings can be overridden per zone and demonstrates how different DNS configurations affect query resolution.
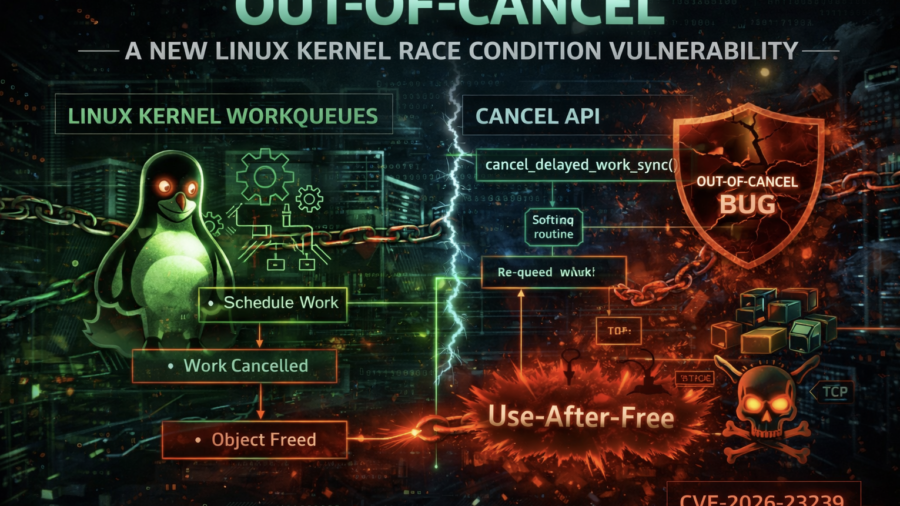
Out-of-Cancel: A New Linux Kernel Race Condition Bug Class
The article introduces the Out-of-Cancel vulnerability class in the Linux kernel, where workqueue cancellation APIs fail to guarantee object lifetime. This race can lead to Use-After-Free bugs, demonstrated using espintcp (CVE-2026-23239).
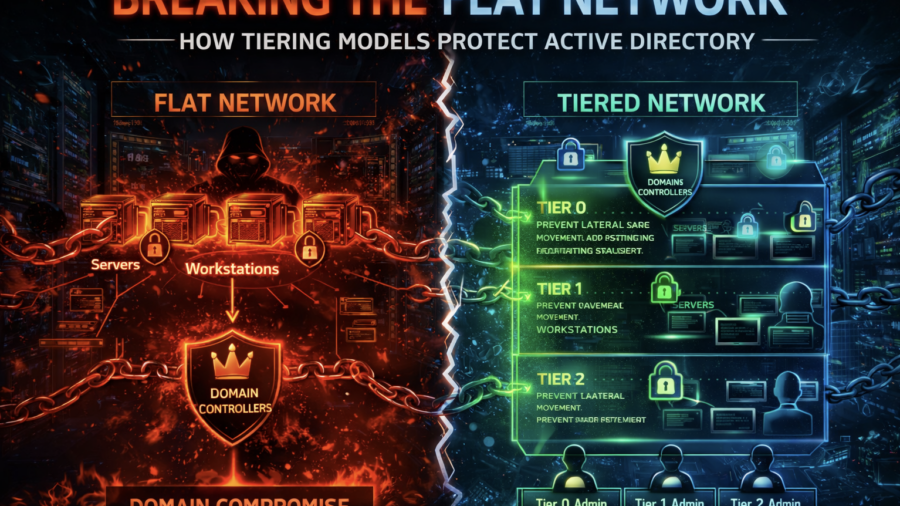
Breaking the Flat Network: How Tiering Models Protect Active Directory
The article explains how flat enterprise networks enable easy lateral movement and domain compromise. It shows how Active Directory tiering models segment privileges and systems to prevent attackers from escalating access.
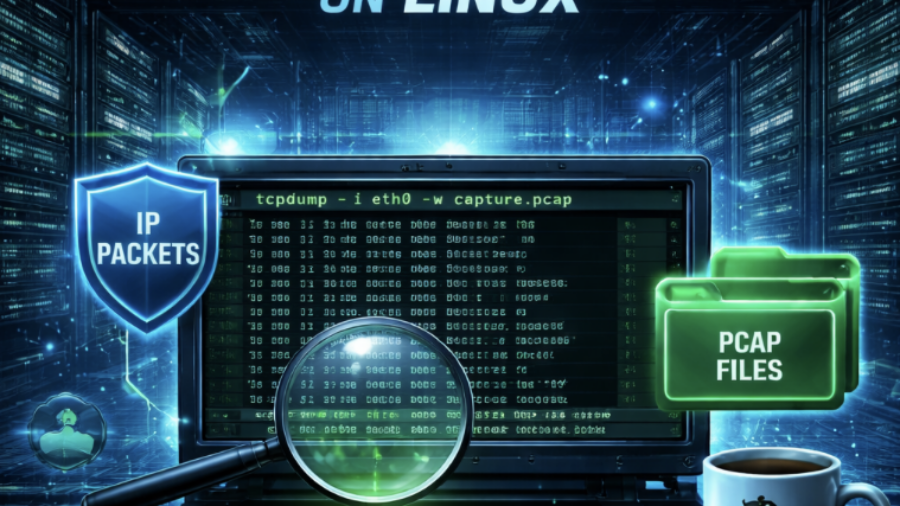
From PCAP to Passwords: Automating Kerberos Roast Extraction
Krb5RoastParser is a Python tool that extracts Kerberos authentication hashes from PCAP traffic and converts them into Hashcat-compatible formats, simplifying Kerberoasting and Kerberos password-cracking workflows.
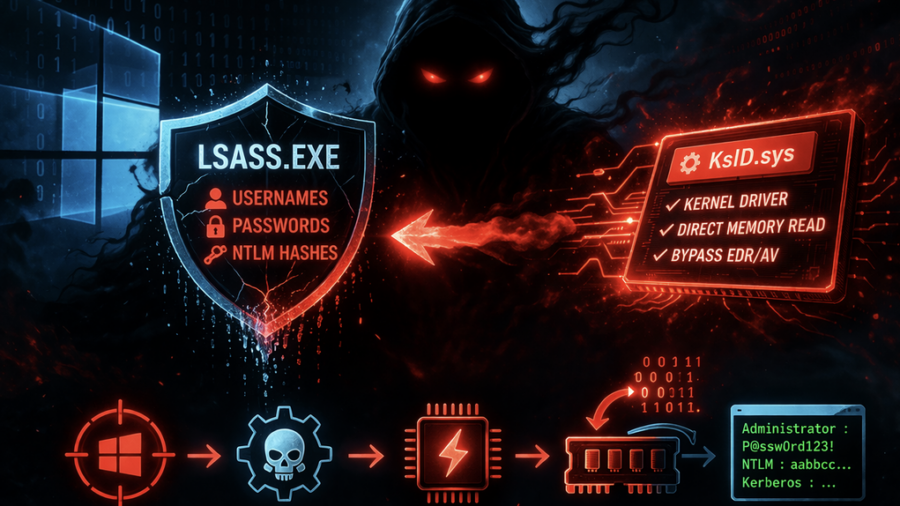
Ghost in LSASS: Inside the KslKatz Credential Dumping Framework
KslKatz is a Windows credential-dumping tool that reads LSASS memory using a kernel driver to bypass user-mode protections. It merges techniques from KslDump and GhostKatz to extract authentication secrets with improved stealth.
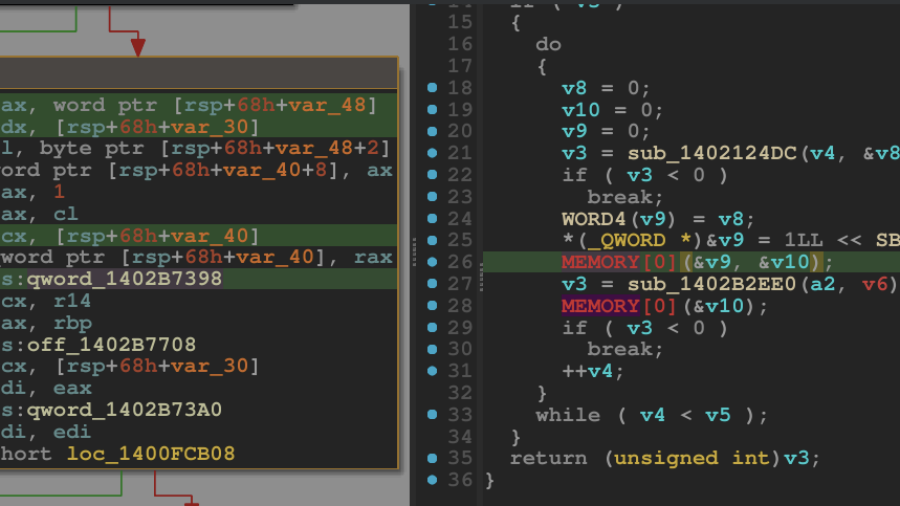
Breaking the Shield: Unpacking a VMProtected Windows Kernel Driver
A technical walkthrough showing how to unpack a VMProtected Windows kernel driver using WinDbg and dynamic analysis. The guide demonstrates restoring the hidden Import Address Table and dumping a clean driver for reverse engineering.
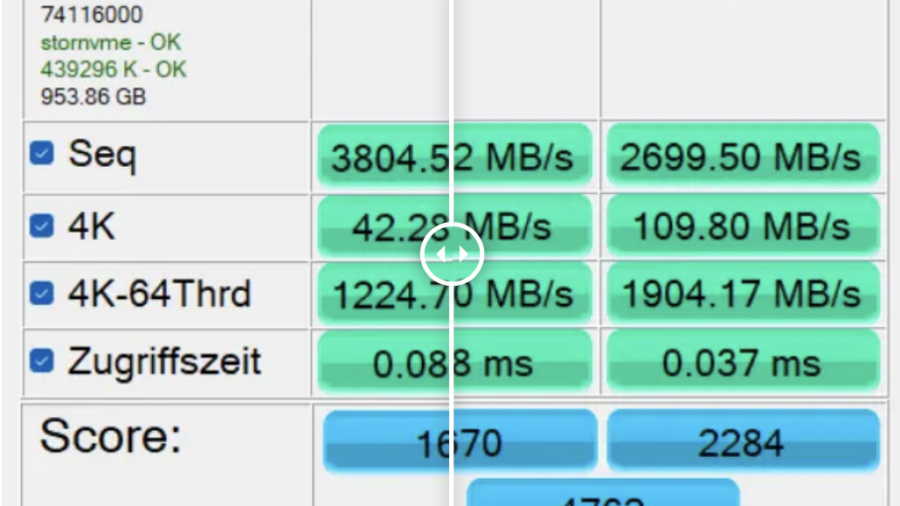
Report: Microsoft quietly blocks Windows 11 25H2, 24H2 performance boost hack for SSDs
Microsoft has disabled a registry hack that enabled a hidden native NVMe driver in Windows 11 24H2/25H2. The tweak previously delivered major SSD performance gains but was likely blocked due to stability and compatibility concerns.
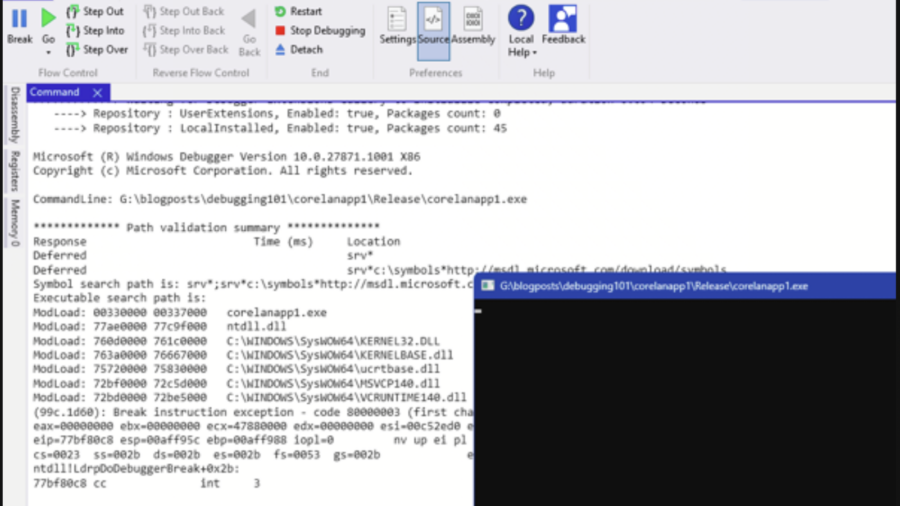
Debugging – WinDBG & WinDBGX Fundamentals
A beginner-friendly guide to debugging Windows programs using WinDbg and WinDbgX. It explains debugger basics, breakpoints, symbols, memory inspection, and execution control—key skills for reverse engineering and vulnerability research.